Data Center Best Practice Security Policy
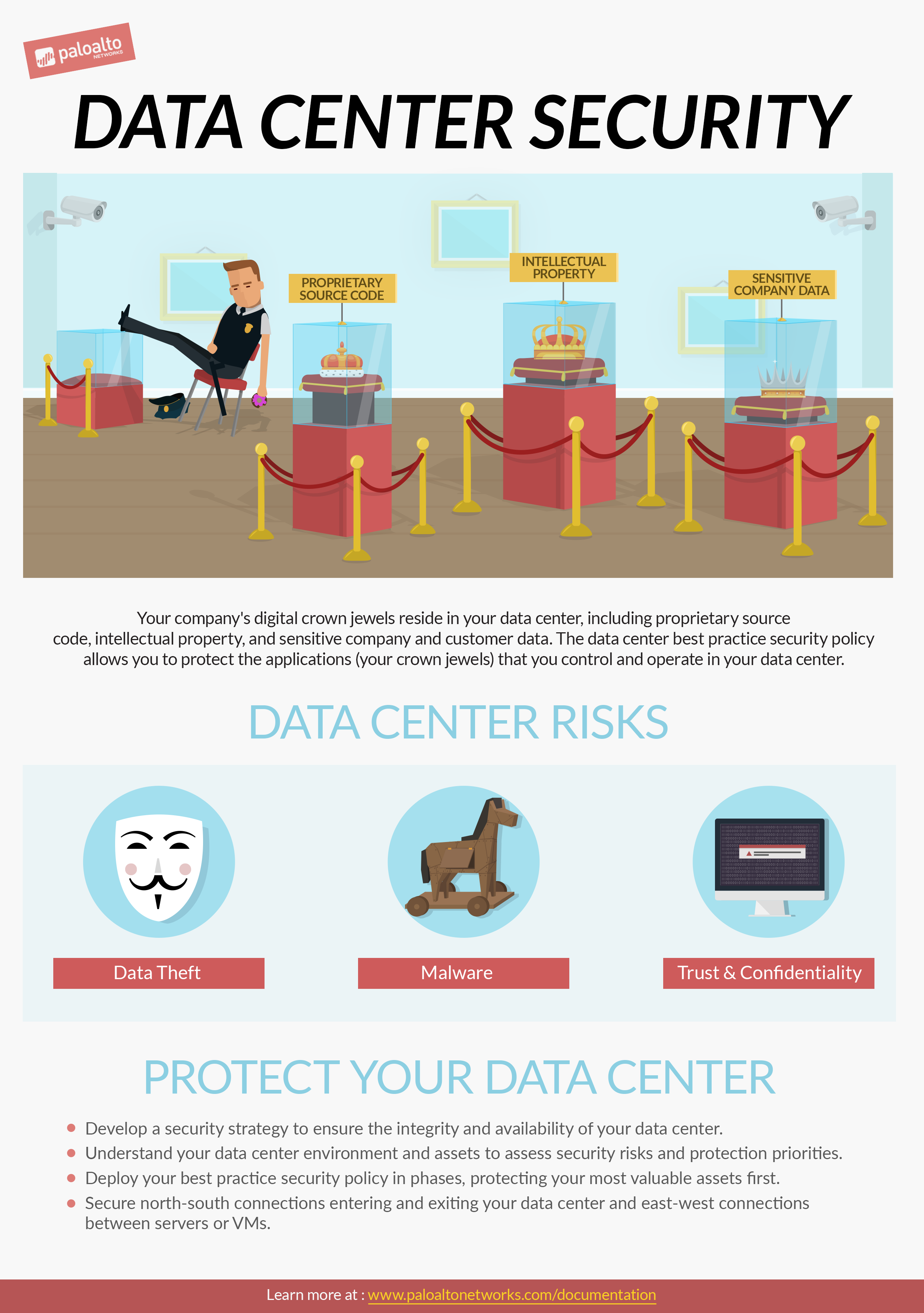
Your enterprise's most valuable assets reside in your data center, including proprietary source code, intellectual property, and sensitive company and customer data. Your customers and employees trust you to maintain the confidentiality and integrity of their data and expect that data to be always available, so it's important to implement a data center best practice security policy that safeguards your data and prevents successful attacks. Use the guidelines in this site to plan, deploy, and maintain your data center best practice security policy.
What Do You Want To Do?
Featured Topics
Recommended Topics
What Is a Data Center Best Practice Security Policy?
Protect all north-south and east-west traffic flows and prevent attackers from getting into your data center and executing malware or exfiltrating data.
Create Data-Center-to-Internet Decryption Policy Rules
Updated with recommendations for using the new decryption features introduced in PAN-OS 10.0, including TLS 1.3 support and enhancements for simplifying troubleshooting of decryption issues.
Block QUIC Traffic
Our recommended block rules have been updated with recommendations for blocking the Quick UDP Internet Connections (QUIC) protocol to prevent potentially dangerous encrypted traffic from entering the network.
Videos
DNS Sinkhole Best Practice Settings Check
Antivirus Profile Decoder Actions Best Practice Settings Check
Interzone Deny Rule Logging Best Practice Settings Check
Antivirus Profile WildFire Decoder Actions Best Practice Settings Check
Intrazone Allow Rule Logging Best Practice Settings Check
BPA+ YouTube Channel
Click "View BPA+ Playlist" to access all of the BPA+ videos, including best practice network security checks and a demo.