Convert Simple Rules with Well-Known Apps After One Week
Table of Contents
9.1
Expand all | Collapse all
Convert Simple Rules with Well-Known Apps After One Week
Convert legacy port-based security policy rules that
control a small number of well-known applications after one week
of monitoring production traffic.
After a week of monitoring
production traffic, you can safely begin to convert simple port-based
rules to App-ID based rules. Good candidates include rules for which
only one or a small number of well-known applications should legitimately
use the port because it’s fairly easy to determine which applications
you want to allow on a simple rule. Examples include port 21 (FTP),
port 22 (SSH), and port 53 (DNS).
Install the latest Content Updates before
you begin converting rules to ensure you have the latest application
signatures on your PAN-OS appliance. This example shows you how
to sort port-based rules to find candidates for safe conversion
and the options for converting those port-based rules directly to
App-ID based rules.
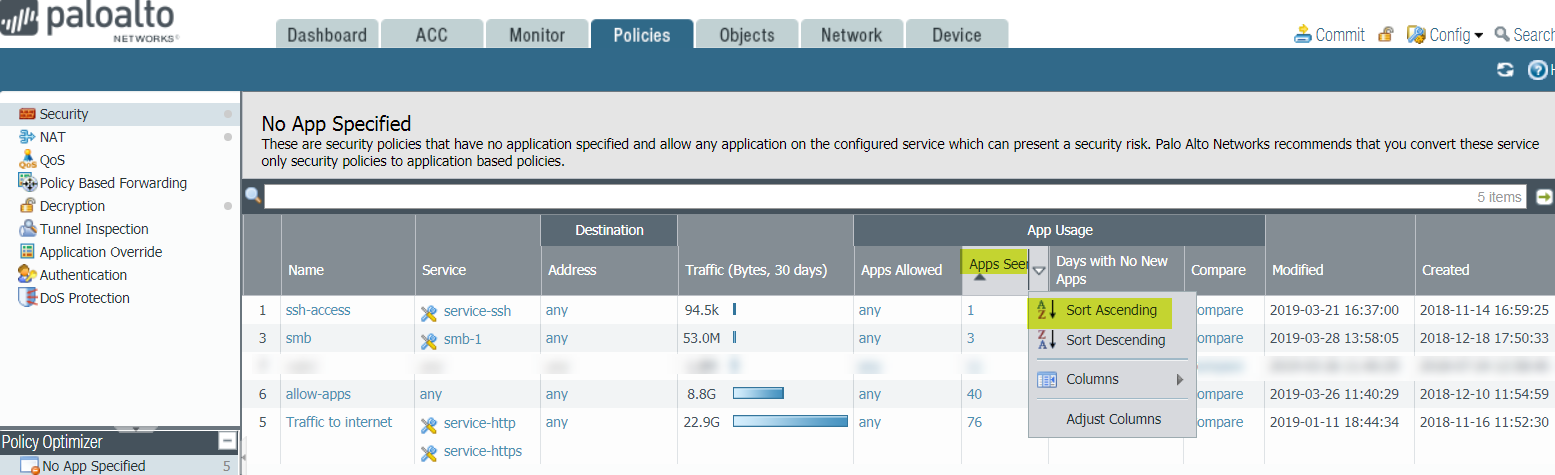
- In, selectPoliciesSecurityPolicy OptimizerNo App SpecifiedApps SeenandSort Ascendingto find the port-based rules that have seen the fewest applications.
![]() The port-based rules that have seen the fewest applications are at the top of theNo App Specifieddisplay. You can safely convert rules for specific services, such as SSH, directly to application-based rules and you can examine rules that have seen few applications to see if you can safely convert them.The port-based rule intended to allow Server Message Block (SMB) traffic has seen only three applications since migrating the configuration to the PAN-OS appliance and therefore is a candidate for conversion.
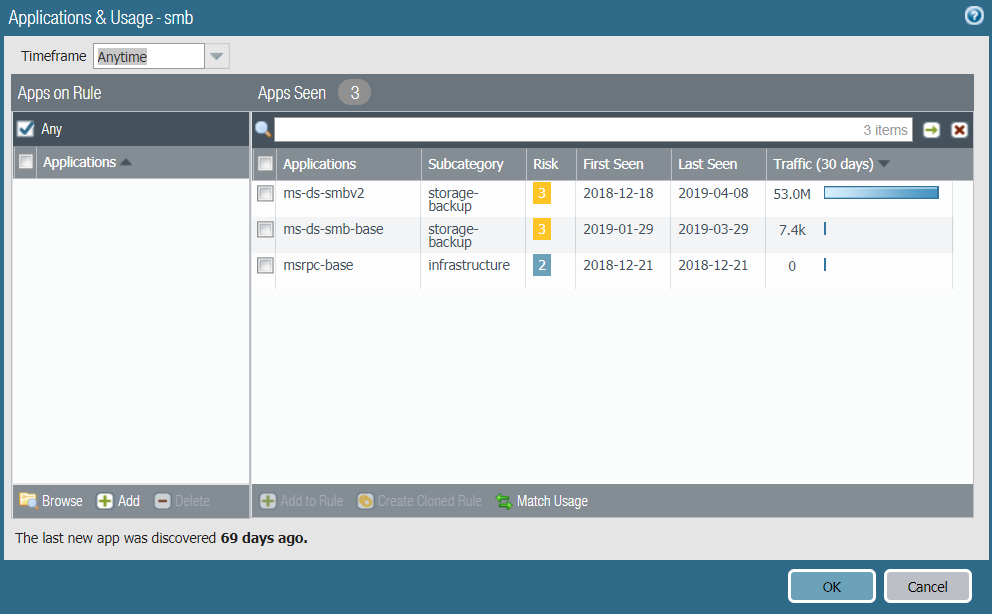
The port-based rules that have seen the fewest applications are at the top of theNo App Specifieddisplay. You can safely convert rules for specific services, such as SSH, directly to application-based rules and you can examine rules that have seen few applications to see if you can safely convert them.The port-based rule intended to allow Server Message Block (SMB) traffic has seen only three applications since migrating the configuration to the PAN-OS appliance and therefore is a candidate for conversion. - Click theApps Seennumber orCompareto examine the applications seen on the rule.Applications & Usageshows the applications actually seen in the traffic that match the rule.
![]()
- Evaluate whether you want to allow all, some, or none of the applications seen on the rule and select the applications you want to allow.You can match the exact usage of the rule, future-proof the rule by adding the container apps, or select individual applications to add to the rule.
- If you want the rule to allow all applications exactly as matched on the rule:
- Select allApplicationsinApps Seen).
- ClickMatch Usage.
- ClickOKto convert the port-based rule to an App-ID based rule.
- Set theServicetoapplication-defaultso that no evasive, malicious applications can use the port.
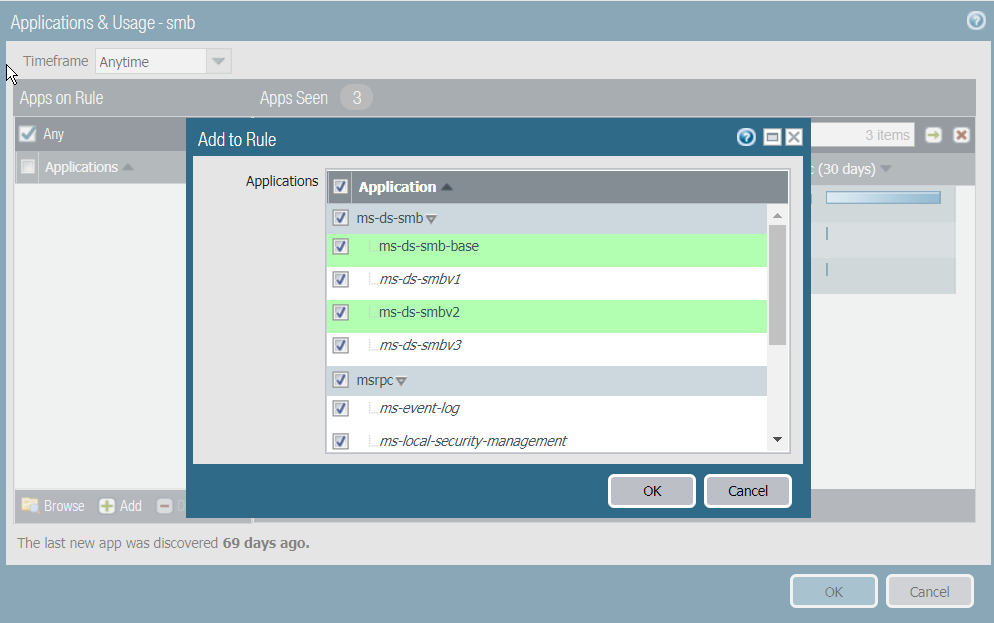
- If you want to allow all of the applications seen on the rule and future-proof the rule by adding their container applications (so all applications within each container are allowed and applications added to the container app later are automatically allowed):
- Leave all the applications selected andAdd to Rule.
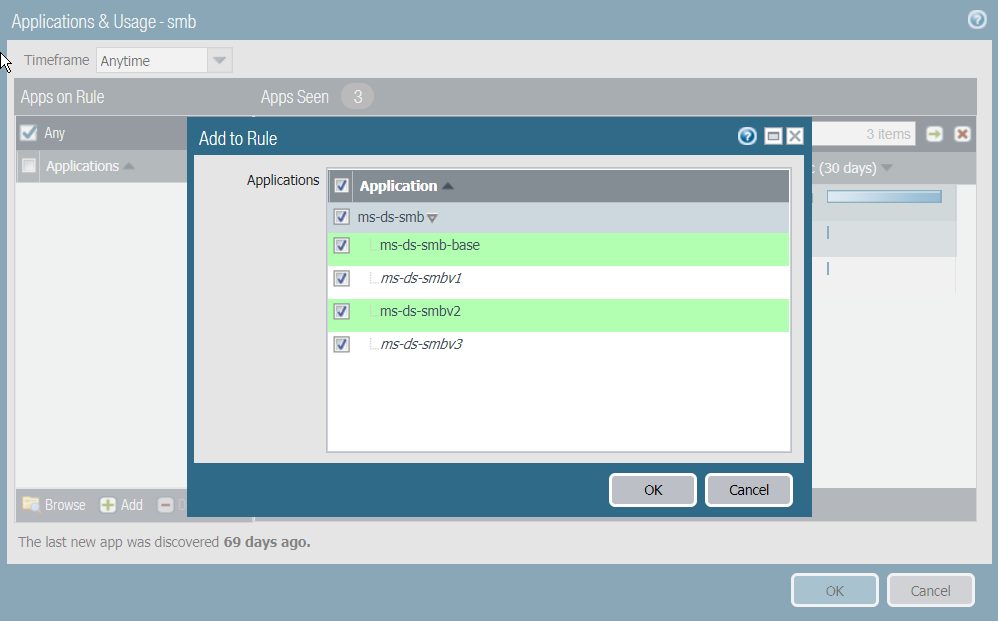
![]() The gray-shaded applications are the container apps. The green-shaded applications are the applications seen on the rule. The unshaded applications belong to the same container app but have not been seen on the rule.
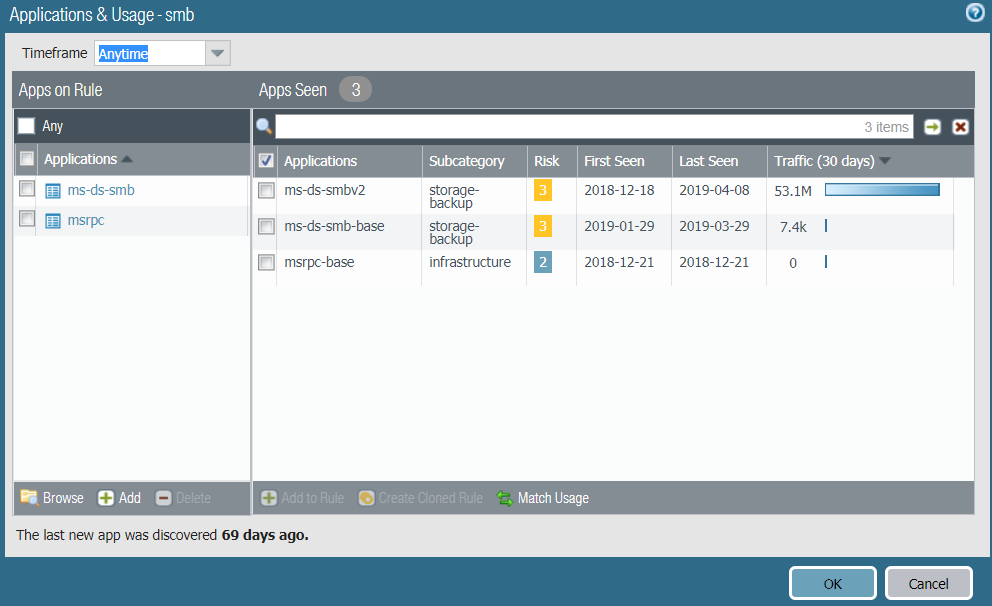
The gray-shaded applications are the container apps. The green-shaded applications are the applications seen on the rule. The unshaded applications belong to the same container app but have not been seen on the rule. - ClickOK. Only the container apps appear inApps on Rulebecause they include (allow) all of the applications they contain:
![]()
- ClickOKto convert the rule.
- Set theServicetoapplication-defaultso that no evasive, malicious applications can use the port.
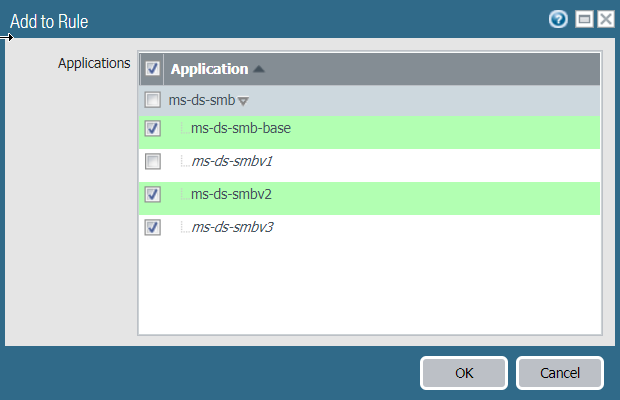
- If you want to allow only some of the applications or if you want to select the applications to allow within a container app, select those applications and then clickAdd to Rule. For example, if you decide not to allow msrpc-base and select only ms-ds-smbv2 and ms-ds-smb-base andAdd to Rule, Policy Optimizer shows you the related applications in the container app (ms-ds-smb, shaded gray) and provides the opportunity to future-proof the rule by adding those applications:
- Select the applications you want to allow and then clickAdd to Rule.For example, if you decide not to allow msrpc-base and select only ms-ds-smbv2 and ms-ds-smb-base andAdd to Rule, Policy Optimizer shows you the related applications in the container app (ms-ds-smb, shaded gray) and provides the opportunity to future-proof the rule by adding those applications:
![]() The green-shaded applications are the applications seen on the rule. The unshaded applications belong to the same container app but have not been seen on the rule. In this case, you may choose to allow ms-ds-smbv3 to future-proof the rule but not to allow ms-ds-smbv1 because it’s an older protocol.
The green-shaded applications are the applications seen on the rule. The unshaded applications belong to the same container app but have not been seen on the rule. In this case, you may choose to allow ms-ds-smbv3 to future-proof the rule but not to allow ms-ds-smbv1 because it’s an older protocol. - You can allow all of the applications or select which applications to allow.To allow all of the applications, clickOK.Apps on Ruleshows the selected applications. ClickOKto convert the rule.To allow only selected applications, deselect the undesired applications. If you deselect an application in a container, the container app is also deselected so it doesn’t automatically allow its child apps.
![]()
- ClickOK.Apps on Ruleshows the selected applications.
- ClickOKto convert the rule.
- Set theServicetoapplication-defaultso that no evasive, malicious applications can use the port.