Convert Internet Access Rules
Table of Contents
9.1
Expand all | Collapse all
Convert Internet Access Rules
Convert legacy port-based HTTP/HTTPS (port 80/443) internet
access rules to application-based rules.
An internet access rule controls traffic on
port 80 (HTTP) and port 443 (HTTPS). This rule usually sees the
largest number of applications and the greatest amount of traffic
in bytes. A port-based internet access rule could allow applications
you don’t want on your network and expose it to attacks, so you
need to control and safely enable the applications you allow on
those ports.
When you convert internet access rules from
port-based rules to application-based rules, you need to understand
which applications your company sanctions for business use and which
applications your company tolerates for other purposes.
A
good method of converting an internet access rule is to group applications that
require similar treatment in the same rule instead of creating separate
rules for each application to help prevent rulebase bloat. Use Policy
Optimizer to sort the applications seen on a rule by application
subcategory so you can see all the applications on a rule for a
particular subcategory, select the applications your business uses,
and then clone a rule to control those applications. Policy Optimizer
offers many sorting and filtering options to
organize and analyze applications seen on a rule.
Clone the
rule instead of directly converting it to ensure application availability. Cloning
a rule retains the original port-based rule and places the cloned
application-based rule directly above the port-based rule in the
Security rulebase. This enables you to create different internet
access rules from the original port-based rule for groups of applications
you want to treat differently, without risking application availability.
You can easily see which applications match the cloned rule and
which applications filter through to the original port-based rule
and adjust the rules as needed. When no applications you want to
allow match the port-based rule for a long enough period of time
to be confident you’ve accounted for all the applications the business
requires, you can disable (or delete) the port-based rule, which
finishes the conversion without risking application availability.
You
can use the same method to convert other rules that have seen more
than a few well-known applications. Use information
to help you prioritize which rules to convert after you convert
the internet access rules. For example, you could prioritize by
a combination of most
Policies
Security
Policy Optimizer
No App Specified
Apps Seen
and most
traffic over the last 30 days (Traffic (Bytes, 30 days)
)
to convert the most-used rules, or you could look at Days
with No New Apps
and the Modified
date
to find rules that have seen many applications but are also more
stable.This example shows you how to clone an application-based
rule that controls email applications from a port-based internet
access rule. You can use the same cloning process to create application-based
rules safely for different subcatgories and individual applications
seen on any port-based rule.
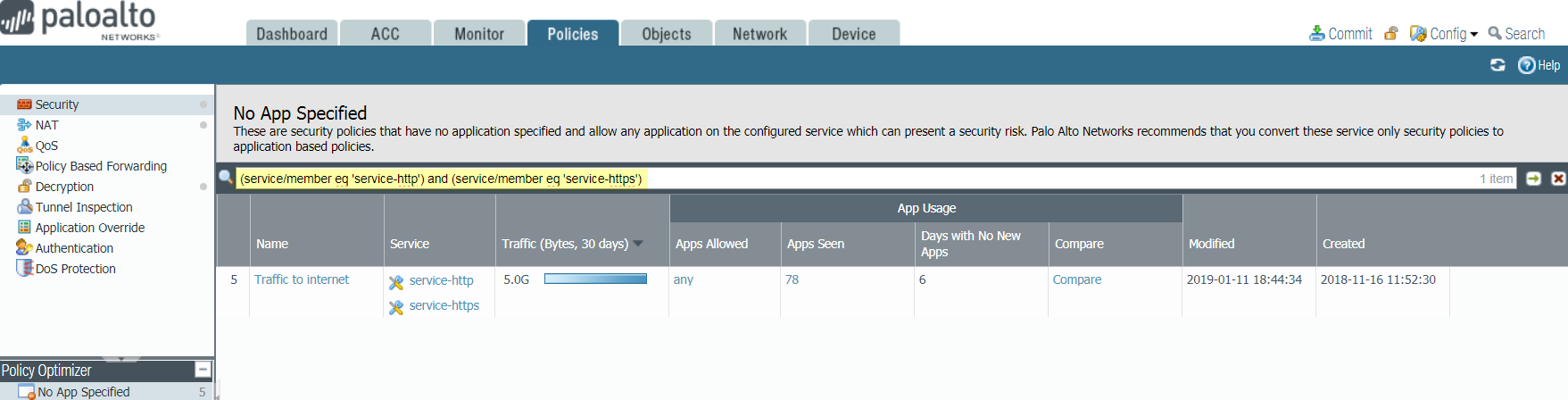
- Navigate toand find the port-based rule(s) that control internet access.PoliciesSecurityPolicy OptimizerNo App SpecfiedUse the filter(service/member eq ‘service-http’) and (service/member eq ‘service-https’)to find the port-based rule(s) configured withservice-httpandservice-https, which are the internet access rule(s).
![]()
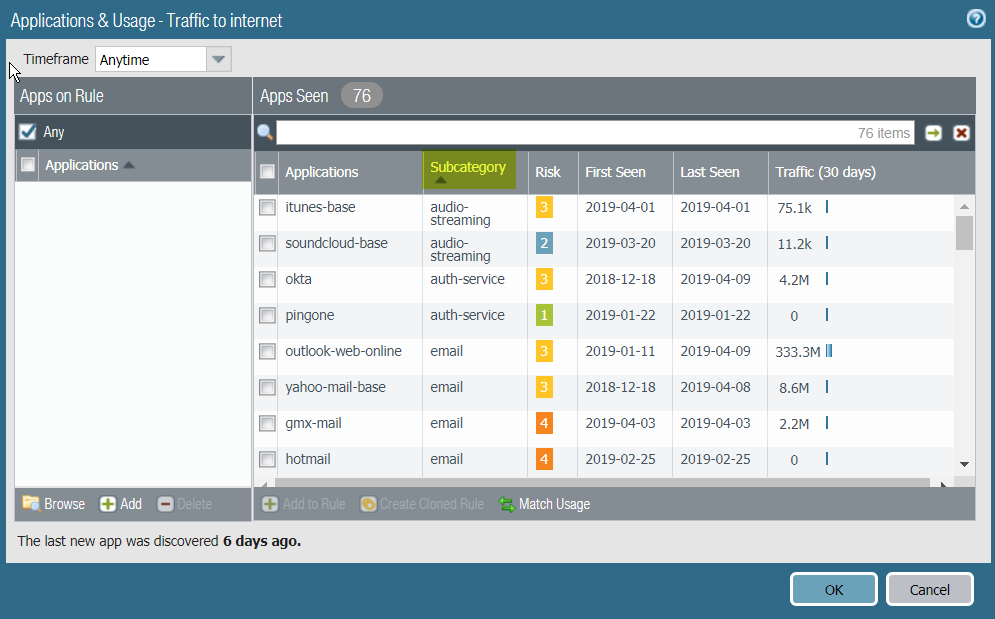
- ClickCompareor the number ofApps Seento open theApplications & Usagedialog.
- SortApps Seenby application subcategory to group similar applications that may be appropriate to control in the same Security policy rule.Sort bySubcategoryto group the applications seen on the rule:
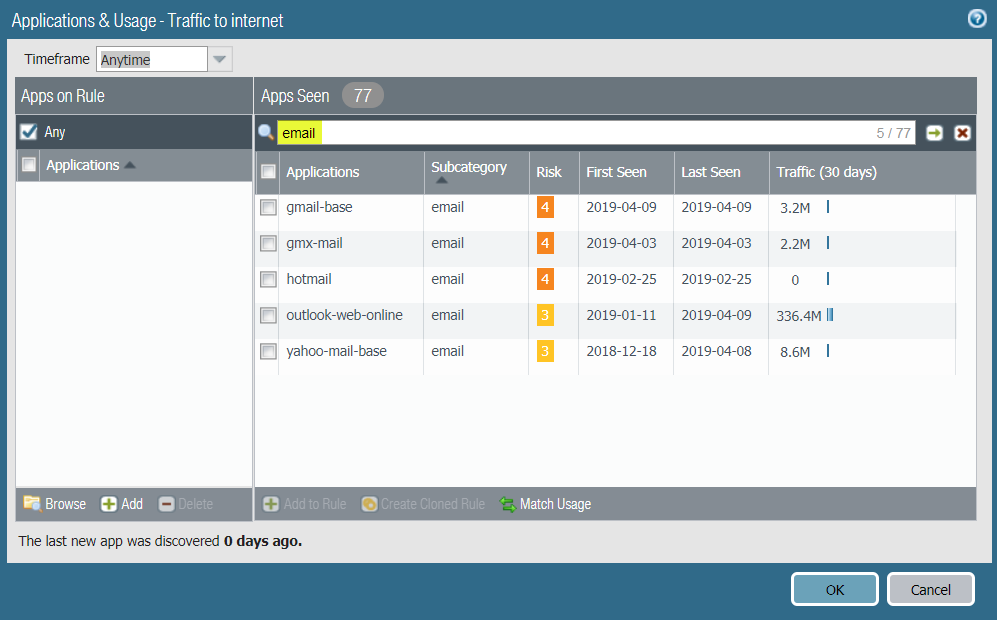
![]() You can also filter by a particular subcategory to see only the applications that belong to that subcategory. In this example, to create an App-ID based rule to control email applications, filter to view only the email applications seen on the rule:
You can also filter by a particular subcategory to see only the applications that belong to that subcategory. In this example, to create an App-ID based rule to control email applications, filter to view only the email applications seen on the rule:![]()
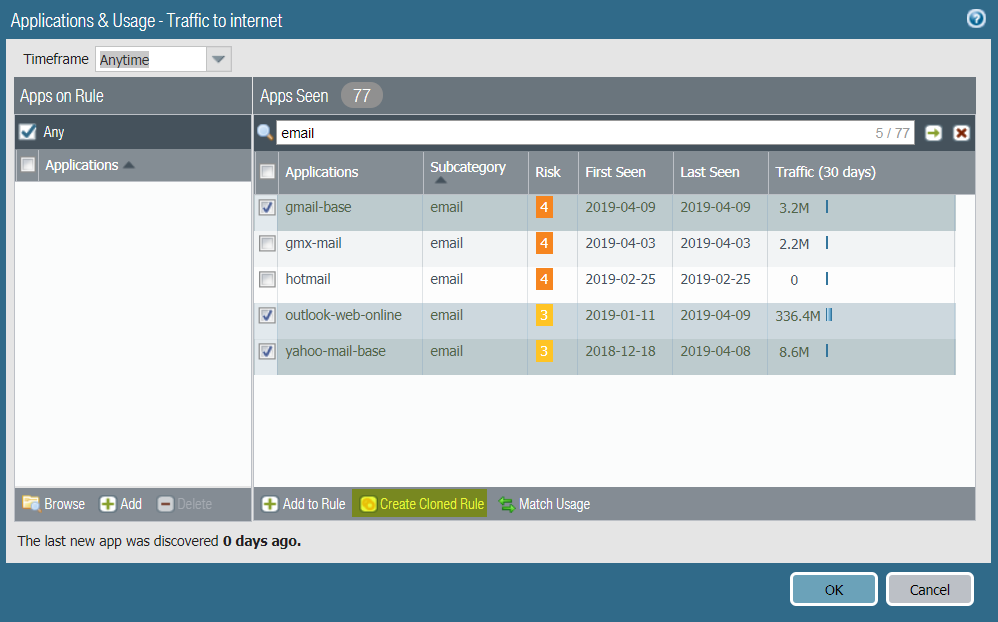
- Select the applications you want to allow and thenCreate Cloned Ruleto clone the new application-based rule from the port-based rule.For example, if your company sanctions Gmail and Outlook for corporate use and tolerates Yahoo email for personal use, but chooses not to allow GMX mail or Hotmail:
![]()
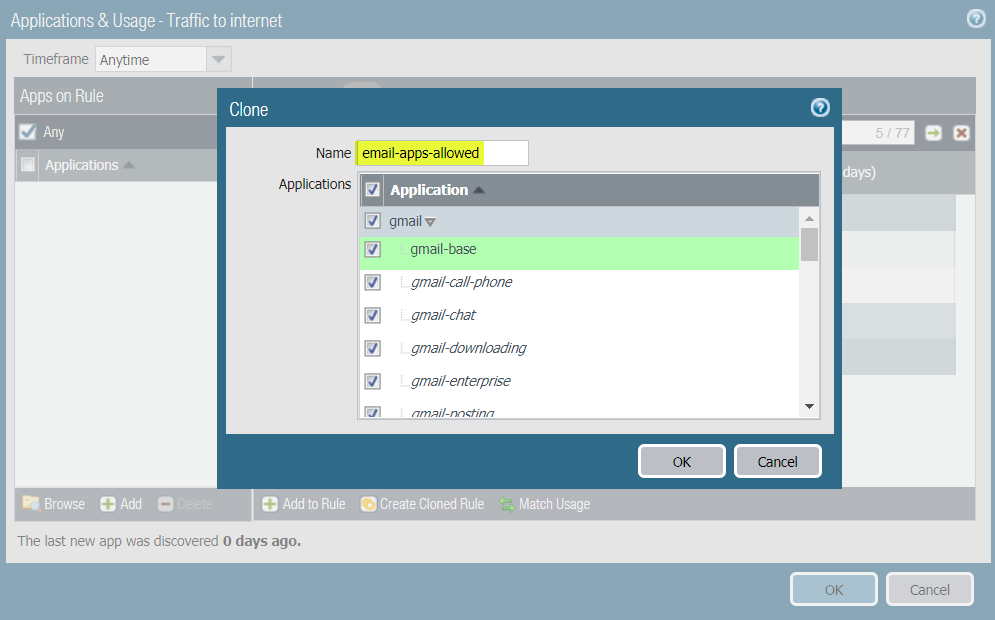
- In theClonedialog, select the applications associated with each application that you want to allow.
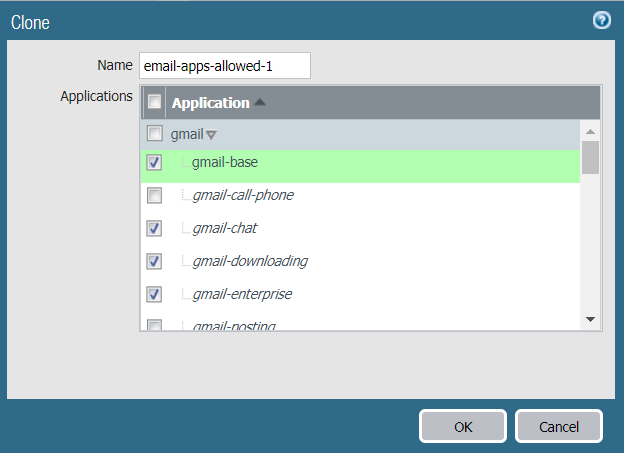
![]() Give the new rule aNamethat describes its purpose. Decide if you want to allow only specific capabilities for each email application or if you want to allow the container app. If you allow the container app, you allow all of the applications in the container. This future-proofs the rule by automatically allowing new applications if they are added to the container app and helps ensure application availability. By default, all of the applications are selected. The container app for each application is shaded gray, applications that have been seen on the rule are shaded green, and applications in the container app that haven’t been seen on the rule are italicized and not shaded.If you choose not to allow some applications in a container app, the container app is also deselected and the rule only includes the specific applications you select.
Give the new rule aNamethat describes its purpose. Decide if you want to allow only specific capabilities for each email application or if you want to allow the container app. If you allow the container app, you allow all of the applications in the container. This future-proofs the rule by automatically allowing new applications if they are added to the container app and helps ensure application availability. By default, all of the applications are selected. The container app for each application is shaded gray, applications that have been seen on the rule are shaded green, and applications in the container app that haven’t been seen on the rule are italicized and not shaded.If you choose not to allow some applications in a container app, the container app is also deselected and the rule only includes the specific applications you select.![]() Deselecting the gmail-call-phone and gmail-posting applications also deselected the gmail container app.
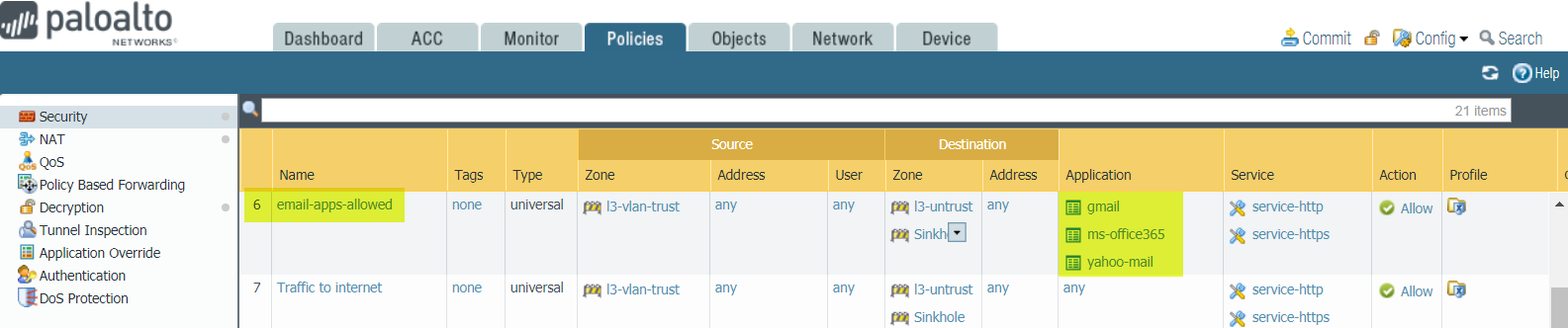
Deselecting the gmail-call-phone and gmail-posting applications also deselected the gmail container app. - ClickOKto create the rule, which is placed above the port-based rule in the Security policy rulebase ().PoliciesSecurityIf you select the container apps, Policy Optimizer adds only the container apps to the rule because they include all of the applications.
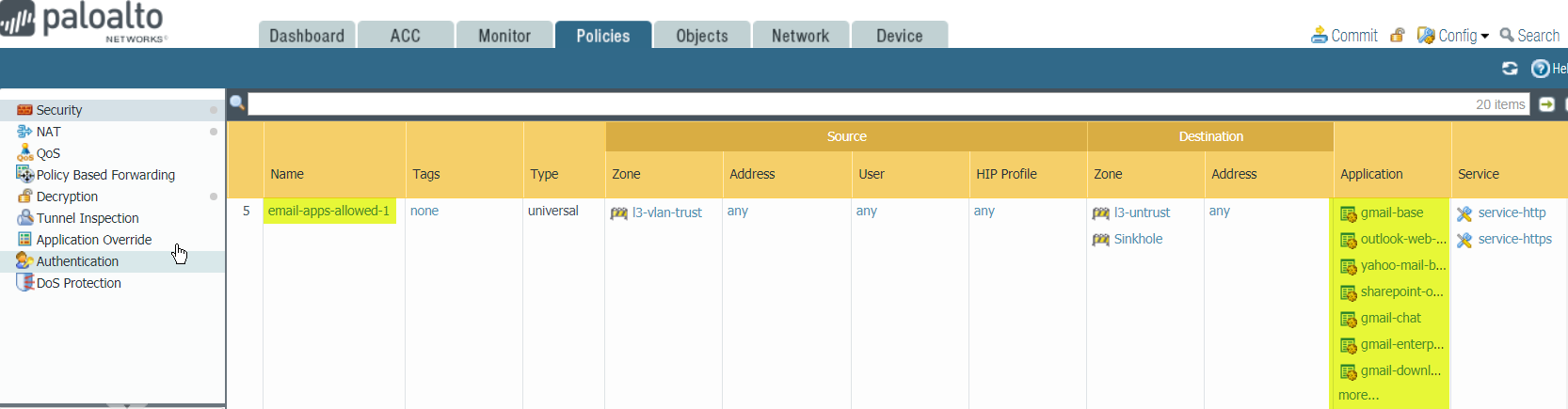
![]() If you select individual applications from theClonedialog instead of the container apps, Policy Optimizer adds only the selected applications to the new App-ID based rule.
If you select individual applications from theClonedialog instead of the container apps, Policy Optimizer adds only the selected applications to the new App-ID based rule.![]()
- Click the ruleNameor aServiceand change theServicetoapplication-defaultto prevent evasive applications from gaining access on a non-standard port.