Decryption Best Practices
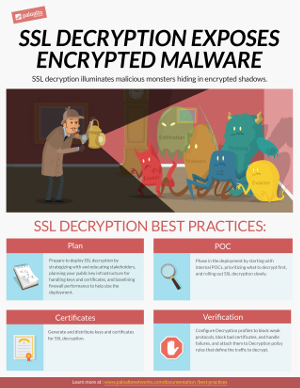
You can't defend against threats you can’t see. By enabling decryption on your next-gen firewalls you can inspect and control SSL/TLS and SSH traffic so that you can detect and prevent threats that would otherwise remain hidden in encrypted traffic. Use the best practice guidelines in this site to learn how to plan for and deploy decryption in your organization.
What Do You Want To Do?
Featured Topics
Digital Learning: Decryption
Learn how to prevent malicious content from entering your network and concealed sensitive content from leaving.
Recommended Topics
Prepare to Deploy Decryption
Proper preparation makes deploying decryption much easier and smoother because everyone from IT to executives to the user base is educated and ready for the changes.
Size the Decryption Firewall Deployment
Decryption consumes firewall CPU resources, so it’s important to evaluate the amount of SSL decryption your firewall deployment can support and decide what to do if you need more power to support your desired decryption deployment.
Decryption Broker