Download PDF
GlobalProtect
GlobalProtect for Internal HIP Checking and User-Based Access
Table of Contents
Expand All
|
Collapse All
GlobalProtect Docs
-
-
-
-
- 6.3
- 6.2
- 6.1
- 6.0
-
- 6.3
- 6.2
- 6.1
- 6.0
GlobalProtect for Internal HIP Checking and User-Based Access
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
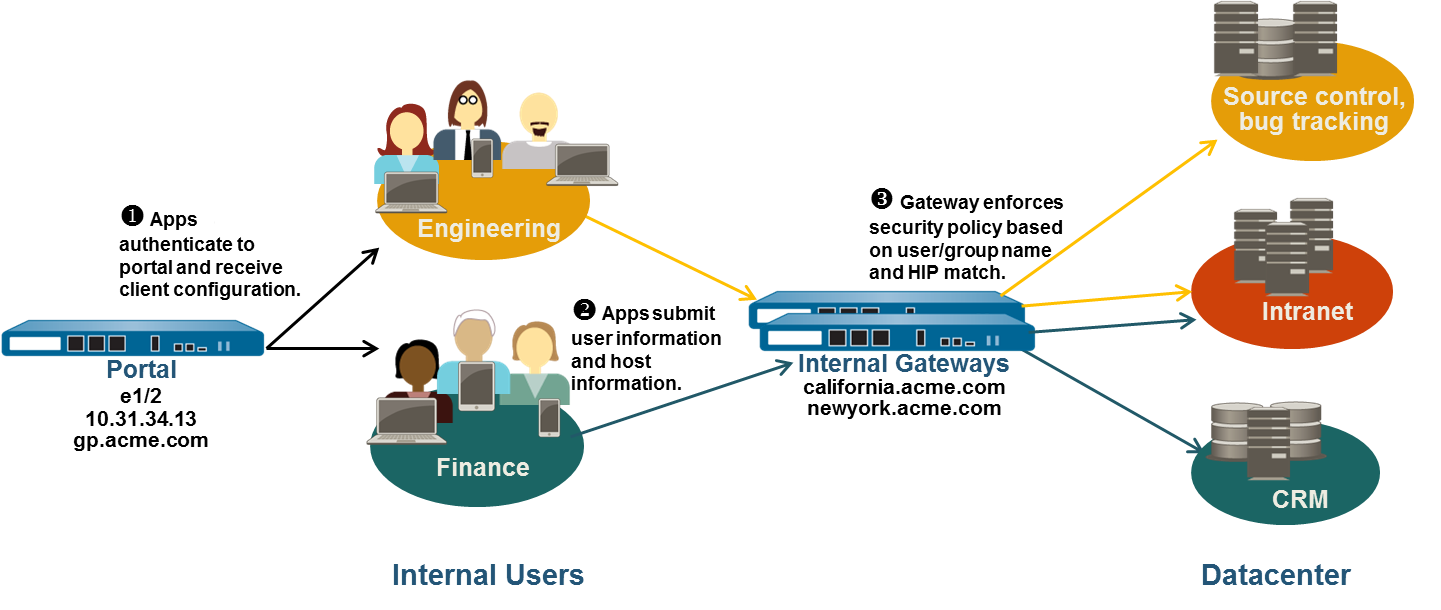
When used in conjunction with User-ID and/or
HIP checks, an internal gateway provides a secure, accurate method
of identifying and controlling traffic by user and/or device state,
replacing other network access control (NAC) services. Internal
gateways are useful in sensitive environments that require authenticated
access to critical resources.
In a configuration with only
internal gateways, all endpoints must be configured with User-Logon
(Always On); On-Demand mode is not supported. It is also recommended
that you configure all client configurations to use single sign-on
(SSO). In addition, since internal hosts do not need to establish
a tunnel connection with the gateway, the IP address of the physical
network adapter on the endpoint is used.
In this quick config,
the internal gateways enforce group-based policies that allow users
in the Engineering group access to the internal source control and
bug databases and users in the Finance group access to the CRM applications.
All authenticated users have access to internal web resources. In
addition, HIP profiles configured on the gateway check each host
to ensure compliance with internal maintenance requirements, such
as whether the latest security patches are installed, whether disk
encryption is enabled, or whether the required software is installed.
Use
the following steps to configure a GlobalProtect internal gateway.
- (Required only on NGFW managed by Panorama or Strata Cloud Manager)Create Interfaces and Zones for GlobalProtect.In this configuration, you must set up interfaces on each firewall hosting a portal and/or a gateway. Because this configuration uses internal gateways only, you must configure the portal and gateways on interfaces in the internal network.Use the default virtual router for all interface configurations to avoid creating inter-zone routing.On each firewall hosting a portal/gateway:
- Select an Ethernet port to host the portal/gateway, and then configure a Layer3 interface with an IP address in the l3-trust Security Zone (NetworkInterfacesEthernet).Enable User Identification on the l3-trust zone.If any of your end users will be accessing the GlobalProtect app on their mobile devices, or if you plan on using HIP-enabled security policy, purchase and install a GlobalProtect subscription for each firewall hosting an internal gateway.
![]() After you purchase the GlobalProtect subscriptions and receive your activation code, install the GlobalProtect subscriptions on the firewalls hosting your gateways.Contact your Palo Alto Networks Sales Engineer or Reseller if you do not have the required licenses.Obtain server certificates for the GlobalProtect portal and each GlobalProtect gateway.In order to connect to the portal for the first time, the endpoints must trust the root CA certificate used to issue the portal server certificate. You can either use a self-signed certificate on the portal and deploy the root CA certificate to the endpoints before the first portal connection, or obtain a server certificate for the portal from a trusted CA.You can use self-signed certificates on the gateways.The recommended workflow is as follows:
After you purchase the GlobalProtect subscriptions and receive your activation code, install the GlobalProtect subscriptions on the firewalls hosting your gateways.Contact your Palo Alto Networks Sales Engineer or Reseller if you do not have the required licenses.Obtain server certificates for the GlobalProtect portal and each GlobalProtect gateway.In order to connect to the portal for the first time, the endpoints must trust the root CA certificate used to issue the portal server certificate. You can either use a self-signed certificate on the portal and deploy the root CA certificate to the endpoints before the first portal connection, or obtain a server certificate for the portal from a trusted CA.You can use self-signed certificates on the gateways.The recommended workflow is as follows:- On the firewall hosting the portal:
- Use the root CA on the portal to generate a self-signed server certificate. Repeat this step for each gateway.
On each firewall hosting an internal gateway, Deploy the self-signed server certificates.Define how you will authenticate users to the portal and gateways.You can use any combination of certificate profiles and/or authentication profiles as necessary to ensure the security of your portal and gateways. Portals and individual gateways can also use different authentication schemes. See the following sections for step-by-step instructions:- Set Up External Authentication (authentication profile)
- Set Up Client Certificate Authentication (certificate profile)
- Set Up Two-Factor Authentication (token- or OTP-based)
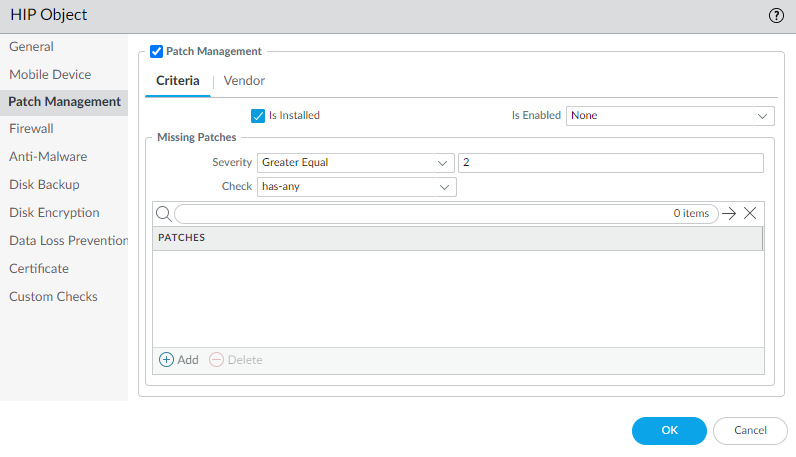
You must then reference the certificate profile and/or authentication profiles that you defined in the portal and gateway configurations.Create the HIP profiles you need to enforce security policies on gateway access.See Host Information for more information on HIP matching.- Create the HIP objects to filter the raw host data collected by the app. For example, if you want to prevent users that are not up-to-date with required patches from connecting, you might create a HIP object to match on whether the patch management software is installed and that all patches with a given severity are up-to-date.
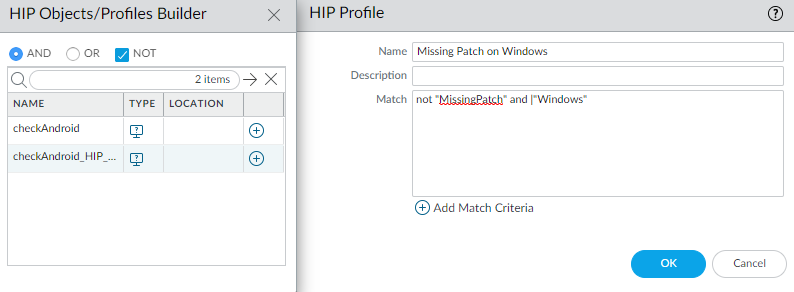
![]() Create the HIP profiles that you plan to use in your policies.For example, if you want to ensure that only Windows users with up-to-date patches can access your internal applications, you might attach the following HIP profile that will match hosts that do NOT have a missing patch:
Create the HIP profiles that you plan to use in your policies.For example, if you want to ensure that only Windows users with up-to-date patches can access your internal applications, you might attach the following HIP profile that will match hosts that do NOT have a missing patch:![]() Configure the internal gateways with the following settings.
Configure the internal gateways with the following settings.- Interface
- IP Address
- Server Certificate
- Authentication Profile and/or Configuration Profile
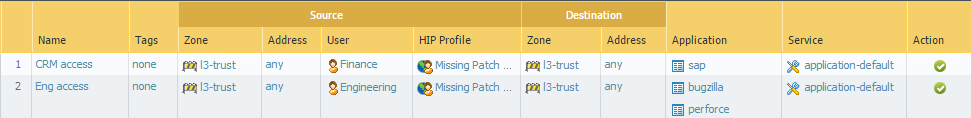
Note that it is not necessary to configure the client settings in the gateway configurations (unless you want to set up HIP notifications) because tunnel connections are not required. See Configure a GlobalProtect Gateway for step-by-step instructions on creating the gateway configurations.Configure the GlobalProtect Portals.Although all of the previous configurations can use the User-logon (Always On) or On-demand (Manual user initiated connection) connect methods, an internal gateway configuration must always be on, and therefore requires the User-logon (Always On) connect method.Configure the portal as follows:- Set Up Access to the GlobalProtect Portal:Interface—ethernet1/2IP Address—10.31.34.13Server Certificate—GP-server-cert.pem issued by GoDaddy with CN=gp.acme.comDefine the GlobalProtect Client Authentication Configurations:Use single sign-on—enabledConnect Method—User-logon (Always On)Internal Gateway Address—california.acme.com, newyork.acme.comUser/User Group—anyCommit the portal configuration.Deploy the GlobalProtect App Software.Select DeviceGlobalProtect Client.In this example, use the procedure to Host App Updates on the Portal.Create the HIP-enabled and/or user/group-based security rules on your gateway(s).Add the following security rules for this example:
- Do one of the following:
- On Panorama, select PoliciesSecurity, and then Add a new rule.
- On Strata Cloud Manager, select ManageConfigurationNGFW and Prisma AccessSecurity Services and then Add a new rule.
On the Source tab, set the Source Zone to l3-trust.On the User tab, add the HIP profile and user/group to match.- Click Add in the HIP Profiles area, and select the MissingPatch HIP profile.
- Add the Source User group (Finance or Engineering depending on which rule you are creating).
Click OK to save the rule.Commit the gateway configuration.![]()