Download PDF
GlobalProtect
Enable Two-Factor Authentication Using a Software Token Application
Table of Contents
Expand All
|
Collapse All
GlobalProtect Docs
-
-
-
-
- 6.3
- 6.2
- 6.1
- 6.0
-
- 6.3
- 6.2
- 6.1
- 6.0
Enable Two-Factor Authentication Using a Software Token Application
Use a software token application for two-factor authentication
for GlobalProtect.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
If your organization uses a software token
(soft token) application, such as RSA SecurID, to implement two-factor
authentication, users are required to first open their software
token app and enter their PIN to obtain a passcode, then enter the
passcode in their GlobalProtect app in the Password field.
This two-step process complicates the login process.
To simplify
the login process and improve the users’ experience, GlobalProtect offers
seamless soft-token authentication. The user enters the RSA PIN
in the GlobalProtect Password field, and
GlobalProtect retrieves the passcode from RSA and proceeds with
the connection without the user taking the extra step of opening
the RSA application.
This feature is supported for all three
RSA modes: PinPad Style (PIN integrated with token code), Fob Style
(PIN followed by token code) and Pinless mode. For PinPad and Fob
Style, the user enters the PIN in the Password field
and GlobalProtect retrieves the passcode. In Pinless mode, the Password
field is grayed out and users enter their username.
- Change the registry keys on the client Windows devices to enable seamless soft-token authentication.You must change the Windows registry on the clients’ Windows devices before you can enable seamless soft-token authentication. GlobalProtect retrieves this registry entry only once, when the GlobalProtect app initializes.
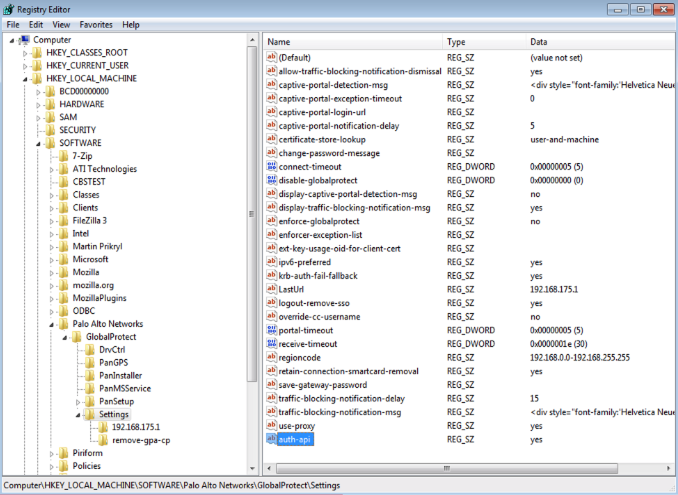
- Open the Windows Registry Editor and select HKEY_LOCAL_MACHINESOFTWAREPalo Alto NetworksGlobalProtectSettings.Change the auth-api value to yes.Because auth-api is set as yes in the client machine, you should configure the portal and gateways with RSA-based authentication. No other authentication profile is supported because GlobalProtect will attempt to retrieve the passcode.Because the portal and gateway use RSA Authentication, we recommend that you enable cookie-based authentication on gateways. The token that is retrieved for the portal may still be active when GlobalProtect tries to get passcode for the gateway, and authentication may fail because the passcode was already used. Therefore, we suggest that you generate an Authentication Override cookie on the portal and Accept the cookie on the gateway.
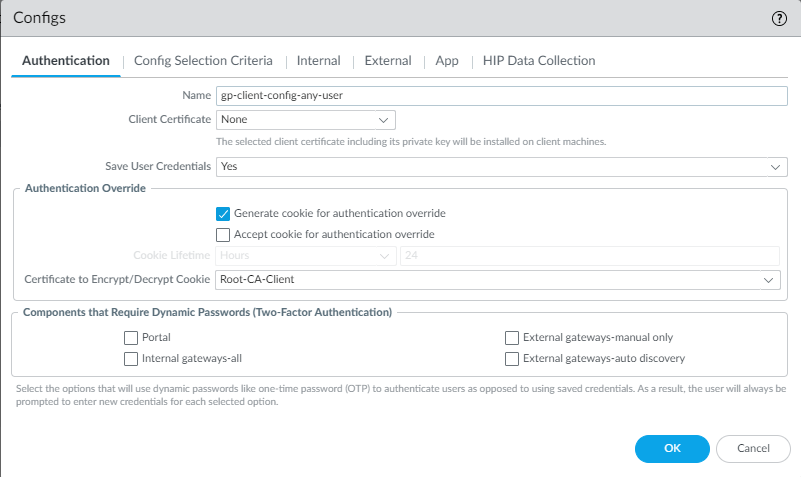
![]() Configure the portal and gateway with RSA-based authentication.Enable cookie-based authentication on the GlobalProtect portal.Specifying GlobalProtect to override an existing authentication allows GlobalProtect to overwrite an existing passcode with a newly-created passcode.
Configure the portal and gateway with RSA-based authentication.Enable cookie-based authentication on the GlobalProtect portal.Specifying GlobalProtect to override an existing authentication allows GlobalProtect to overwrite an existing passcode with a newly-created passcode.- Do one of the following.
- Follow the steps below for Panorama Managed NGFW.
- Select Select NetworkGlobalProtectPortals<portal-config>; then select the Agent tab.
- Click OK.
- Follow the step below for Panorama Managed Prisma Access.
- Select NetworkGlobalProtectPortalsGlobalProtect_PortalAgentDefaultApp.
- Follow the step below for Strata Cloud Managed Managed NGFW and Prisma Access.
- Select WorkflowsPrisma Access SetupGlobalProtectGlobalProtect App.
- Select Generate cookie for authentication override.The authentication cookie includes the following fields:
- user—Username that is used to authenticate the user.
- domain—Domain name of the user.
- os—Application name that is used on the device.
- hostID—Unique ID that is assigned by GlobalProtect to identify the host.
- gen time—Date and time that the authentication cookie was generated.
- ip—IP address of the device that is used to successfully authenticate to GlobalProtect and to obtain the cookie.
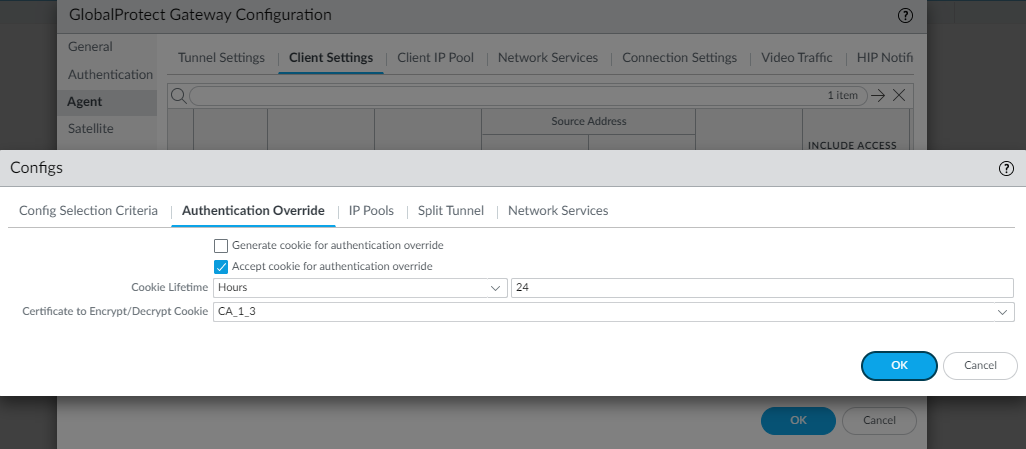
![]() Enable the GlobalProtect gateway to accept cookies for authentication overrides.
Enable the GlobalProtect gateway to accept cookies for authentication overrides.- On your gateway select the Agent tab.Select Client Settings, then select the GlobalProtect client config or add a new one.Select Authentication Override; then, select Accept cookie for authentication override.The authentication cookie includes the following fields:
- user—Username that is used to authenticate the user.
- domain—Domain name of the user.
- os—Application name that is used on the device.
- hostID—Unique ID that is assigned by GlobalProtect to identify the host.
- gen time—Date and time that the authentication cookie was generated.
- ip—IP address of the device that is used to successfully authenticate to GlobalProtect and to obtain the cookie.
![]() On your portal, select the Authentication tab.Add a new client authentication profile or select an existing one; then, select Automatically retrieve passcode from SoftToken application.
On your portal, select the Authentication tab.Add a new client authentication profile or select an existing one; then, select Automatically retrieve passcode from SoftToken application.