Next-Generation Firewall
Enable and Monitor App-ID TSIDs
Table of Contents
Expand All
|
Collapse All
Next-Generation Firewall Docs
-
-
-
-
-
-
-
- PAN-OS 12.1
- PAN-OS 11.2
- PAN-OS 11.1
- PAN-OS 11.0 (EoL)
- PAN-OS 10.2
- PAN-OS 10.1
- PAN-OS 10.0 (EoL)
- PAN-OS 9.1 (EoL)
- PAN-OS 9.0 (EoL)
- PAN-OS 8.1 (EoL)
-
- PAN-OS 12.1
- PAN-OS 11.2
- PAN-OS 11.1
- PAN-OS 10.2
- PAN-OS 10.1
Enable and Monitor App-ID TSIDs
App-ID TSIDs provide previews to App-IDs and can be used to preview future App-IDs
before introducing them into your production network environment.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
This is a core Network Security feature for NGFWs and Prisma
Access; no prerequisites needed.
|
Palo Alto Networks provides a preview version of App-IDs to allow users to test and
validate modified and new App-IDs in the form of Threat Signature Indicators
(TSIDs). These TSIDs are delivered as vulnerability signatures using the category:
app-id-change and are, by default, configured on the
firewall with a severity level of Informational and an action
of Allow. The non-invasive setting provides monitoring
capabilities while preventing unwanted changes from blocking access to key
applications in a production environment.
The App-ID TSIDs are packaged with Applications and Threats content updates
and include TSID entries for App-IDs that are slated for official release one month
later. For example, an App-ID TSID released in the first week of March will include
TSIDs for App-IDs that are scheduled for release in the first week of April. This
one month probationary period is to allow time for testing/validation and updates to
any security policies. You can refer to the Notices section of the Applications
and Threats Content Release Notes for more details about the nature of the
TSIDs.
The name of the App-ID TSID (contained in the Threat ID/name field) correlates to the
name of the upcoming App-ID to
- Log in to the PAN-OS web interface.Verify that you have an active Advanced Threat Prevention / Threat Prevention subscription. To verify subscriptions for which you have currently-active licenses, select DeviceLicenses and verify that the appropriate licenses are available and have not expired.
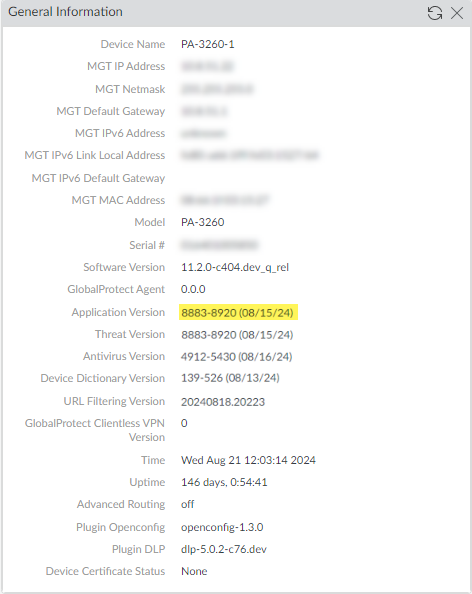
![]() Verify that Applications and Threats content update 8783 or later is installed on your firewall to access the new Vulnerability Signature category. To view the currently installed Application and Threats content version, select Dashboard and refer to the Application Version entry located in the Generation Information pane.
Verify that Applications and Threats content update 8783 or later is installed on your firewall to access the new Vulnerability Signature category. To view the currently installed Application and Threats content version, select Dashboard and refer to the Application Version entry located in the Generation Information pane.![]() Enable App-ID TSID visibility by adding a Vulnerability Protection Rule in your Vulnerability Protection security profile.
Enable App-ID TSID visibility by adding a Vulnerability Protection Rule in your Vulnerability Protection security profile.- Update or create a new Vulnerability Protection security profile (ObjectsSecurity ProfilesVulnerability Protection).If you want to update an existing Vulnerability Security Profile, select one from the list of available profiles. If you want to Add a new one, refer to Security Profile: Vulnerability Protection.
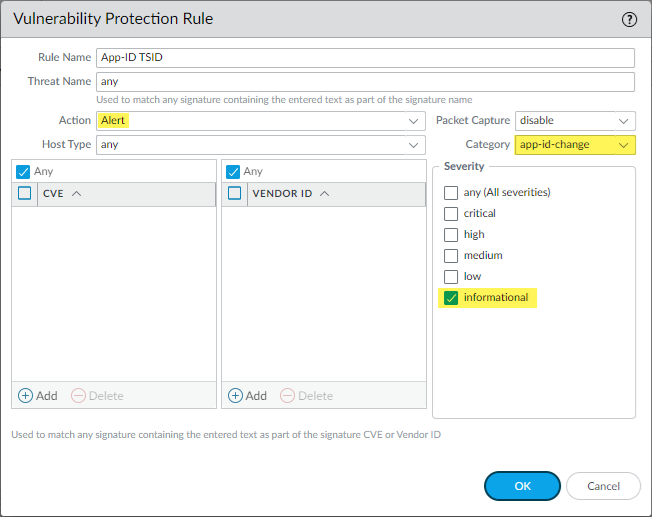
- Add a new Vulnerability Protection Rule and configure it using the following settings:Palo Alto Networks recommends using the following settings to enable matching App-ID TSIDs in order to generate corresponding Threat Logs for future App-ID changes.
![]()
- Click OK to exit the Vulnerability Protection Rule configuration dialog.
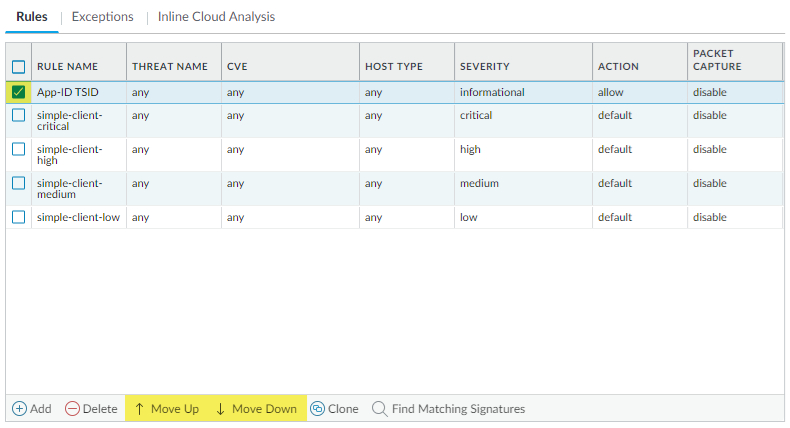
Change the Vulnerability Protection rule precedence using the controls at the bottom of the Vulnerability Protection profile configuration page so that the new rule is at the top.![]() Test the new rule by selecting the rule and Find Matching Signatures. This will return currently available App-ID TSIDs. If you do not see any results or the results do not appear to indicate App-ID TSIDs, verify that app-id-change has been selected in the Vulnerability Protection Rule.
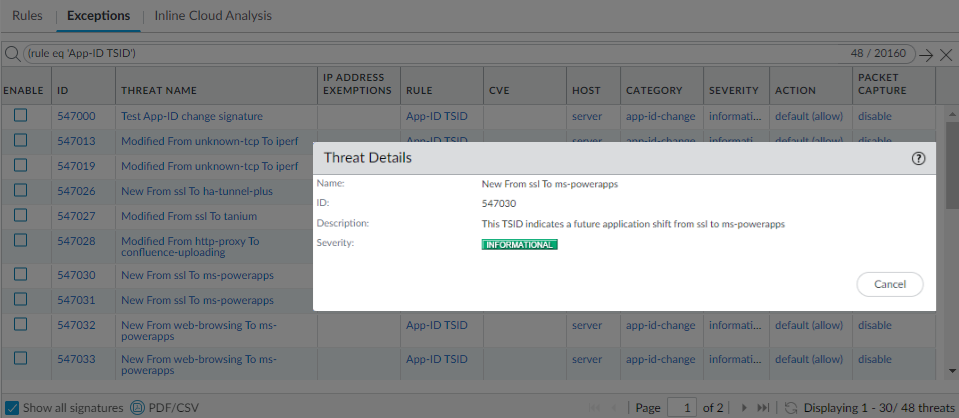
Test the new rule by selecting the rule and Find Matching Signatures. This will return currently available App-ID TSIDs. If you do not see any results or the results do not appear to indicate App-ID TSIDs, verify that app-id-change has been selected in the Vulnerability Protection Rule.![]() Click on the Threat Name of one of the results for more details about the App-ID TSID.
Click on the Threat Name of one of the results for more details about the App-ID TSID.![]() Click OK to save your Vulnerability Protection profile.Configure your Vulnerability Protection profile to the Security Policy rule(s) you want to monitor for potential App-ID changes. This can be done by applying the specific Vulnerability Protection profile in the Security Policy rule(s) or in a Security Profile Group and using that group in the Security Policy rule(s), based on how your policies are constructed.
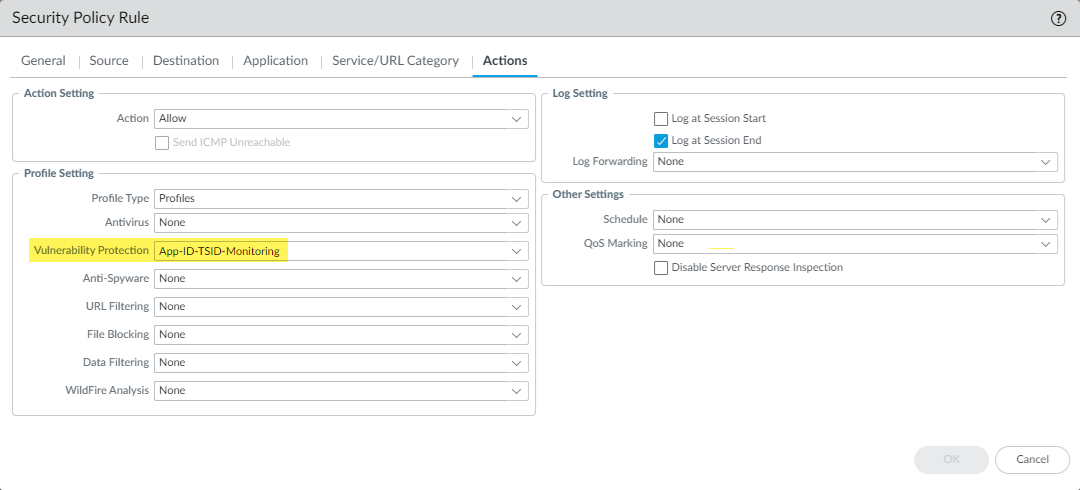
Click OK to save your Vulnerability Protection profile.Configure your Vulnerability Protection profile to the Security Policy rule(s) you want to monitor for potential App-ID changes. This can be done by applying the specific Vulnerability Protection profile in the Security Policy rule(s) or in a Security Profile Group and using that group in the Security Policy rule(s), based on how your policies are constructed.- Vulnerability Profile applied directly to a Security Policy rule:
- Go to PoliciesSecurity and select a security policy rule that you want monitored for App-ID changes.
- Navigate to the Actions tab and select Profiles from the Profile Type drop down.
- In the Vulnerability Protection drop down, select the updated or newly created Vulnerability Protection profile created in step 4.
![]()
- Click OK to save the changes.
- Repeat the above process for other security policy rules that you want monitored for App-ID changes.
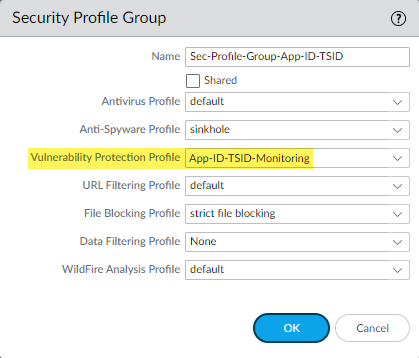
- Vulnerability Profile applied to a Security Profile Group that is referenced by a Security Policy rule
- Go to ObjectsSecurity Profile Groups and select an existing security profile group or Add a new one.
- In the Vulnerability Protection Profile drop down, select the updated or newly created Vulnerability Protection profile created in step 4 and then click OK to save the changes.
![]()
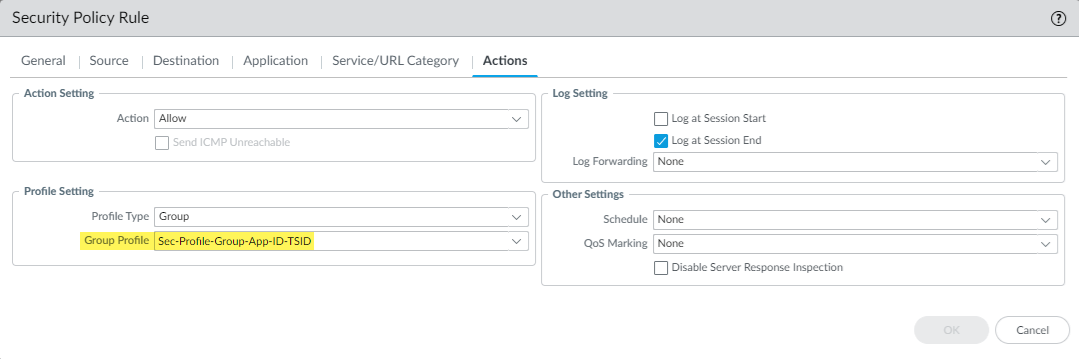
- Go to PoliciesSecurity and select a security policy rule that you want monitored for App-ID changes.
- Navigate to the Actions tab and select Group from the Profile Type drop down.
- In the Group Profile drop down, select the newly updated security profile group.
![]()
- Click OK to save the changes.
- Repeat the above process for other security policy rules that you want monitored for App-ID changes.
Search for activity on the firewall for queries that match against the App-ID TSID criteria. You can manually peruse through the logs or you can create a custom report using the same Query Builder attributes used for activity searches. You can then use the custom report / threat log results to modify your existing Security policy rules in preparation for the new and updated App-IDs scheduled for inclusion in the following month's release of the Applications and Threats content update. You can track affected rules by cross referencing the Rule with the detected App-ID TSIDs in your network. If you use Panorama to manage your firewalls, you can use the global search functionality (located in the top-right) to find the affected rule(s). Selecting the resulting Security Rule will bring you to that policy rule for configuration.You can cross reference affected rules by populating the threat logs and custom reports with the Rule and Rule UUID data columns.- Monitor activity on the firewall:If you are using the Strata Cloud Manager Log Viewer to review your firewall logs, you can use the following search query: Threat Category = 'app-id-change'
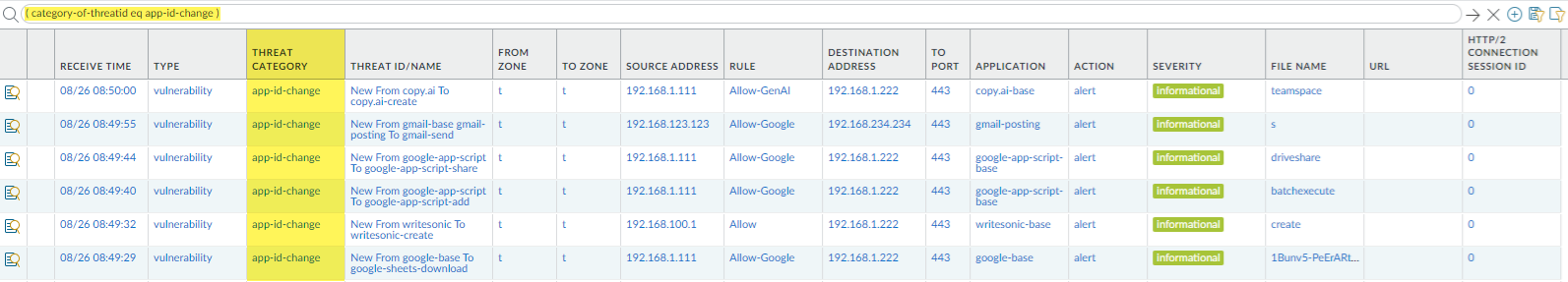
- Select MonitorLogsThreat.
- Use the log query builder to create a filter with the Attribute Threat Category and in the Value field, enter the Threat Category: app-id-change. For example: ( category-of-threatid eq app-id-change ) to view logs that have triggered a matching App-ID TSID, which can be identified by the Threat Category: app-id-change.
![]()
- Create a custom report on the firewall:Palo Alto Networks recommends using the following configuration for the custom report to view information relevant to the App-ID TSIDs.
![]()
- Configure a custom report from MonitorManage Custom Reports. For more information about creating custom reports, refer to Generate Custom Reports.
- When configuring the Report Settings, make sure to specify the Database type: Threat, which is listed under the Summary Databases group. If you are using Panorama, the Threat type to be used is listed under Remote Device Data.
- Use the Query Builder to add the following filter: category-of-threatid eq app-id-change.
- (Optional) Group the report by the Rule.
- At a minimum, populate the report with the following columns:
- Rule
- Rule UUID
- Application
- Threat ID/Name
- Define the Time Frame for the report (Last 7 Days is generally recommended; however, also consider using a time frame most relevant since you downloaded and installed the latest Application and Threats content update, which contain TSIDs).
- (Optional) Select the Scheduled option to run the report on a nightly basis. The report is then available for viewing in the Reports column on the side.
- Click Run Now to generate the custom report or OK to save the changes.
- If you generate a custom report, you can immediately view the results of the report. Alternatively, you can output the report into the following formats: PDF, CSV, and XML.
![]()
Next Steps:- The Threat ID/Name value in the App-ID TSID match results describe the nature of the updated App-ID entry after you install the upcoming Applications and Threats content update. Depending on the type of the update, this could be a Modified or New App-ID, as indicated by the description. After reviewing the information, you can update your security policies to include these modified or new App-IDs, as appropriate for your organization's network usage policies. Refer to Manage New and Modified App-IDs for more information.