Configure SAML Authentication
Table of Contents
End-of-Life (EoL)
Configure SAML Authentication
To configure SAML single
sign-on (SSO) and single logout (SLO), you must register the firewall
and the IdP with each other to enable communication between them.
If the IdP provides a metadata file containing registration information,
you can import it onto the firewall to register the IdP and to create
an IdP server profile. The server profile defines how to connect
to the IdP and specifies the certificate that the IdP uses to sign
SAML messages. You can also use a certificate for the firewall to
sign SAML messages. Using certificates is a requirement to secure
communications between the firewall and the IdP.
Palo Alto
Networks requires HTTPS to ensure the confidentiality of all SAML
transactions instead of alternative approaches such as encrypted
SAML assertions. To ensure the integrity of all messages processed
in a SAML transaction, Palo Alto Networks requires digital certificates
to cryptographically sign all messages.
The following procedure
describes how to configure SAML authentication for end users and
firewall administrators. You can also configure SAML authentication for Panorama administrators.
SSO
is available to administrators and to GlobalProtect and Authentication
Portal end users. SLO is available to administrators and GlobalProtect
end users, but not to Authentication Portal end users.
Administrators
can use SAML to authenticate to the firewall web interface, but
not to the CLI.
- Obtain the certificates that the IdP and firewall will use to sign SAML messages.If the certificates don’t specify key usage attributes, all usages are allowed by default, including signing messages. In this case, you can Obtain Certificates by any method.If the certificates do specify key usage attributes, one of the attributes must be Digital Signature, which is not available on certificates that you generate on the firewall or Panorama. In this case, you must import the certificates:
- Certificate the firewall uses to sign SAML messages—Import the certificate from your enterprise certificate authority (CA) or a third-party CA.
- Certificate the IdP uses to sign SAML messages (Required
for all deployments)—Import a metadata file containing the
certificate from the IdP (see the next step). The IdP certificate
is limited to the following algorithms:Public key algorithms—RSA (1,024 bits or larger) and ECDSA (all sizes). A firewall in FIPS/CC mode supports RSA (2,048 bits or larger) and ECDSA (all sizes).Signature algorithms—SHA1, SHA256, SHA384, and SHA512. A firewall in FIPS/CC mode supports SHA256, SHA384, and SHA512.
Add a SAML IdP server profile.The server profile registers the IdP with the firewall and defines how they connect.In this example, you import a SAML metadata file from the IdP so that the firewall can automatically create a server profile and populate the connection, registration, and IdP certificate information.If the IdP doesn’t provide a metadata file, select DeviceServer ProfilesSAML Identity Provider, Add the server profile, and manually enter the information (consult your IdP administrator for the values).- Export the SAML metadata file from the IdP to a client system from which you can upload the metadata to the firewall.The certificate specified in the file must meet the requirements listed in the preceding step. Refer to your IdP documentation for instructions on exporting the file.Select DeviceServer ProfilesSAML Identity Provider or PanoramaServer ProfilesSAML Identity Provider on Panorama™ and Import the metadata file onto the firewall.Enter a Profile Name to identify the server profile.Browse to the Identity Provider Metadata file.Select Validate Identity Provider Certificate (default) to validate the chain of trust and optionally the revocation status of the IdP certificate.To enable this option, a Certificate Authority (CA) must issue your IdP’s signing certificate. You must create a Certificate Profile that has the CA that issued the IdP’s signing certificate. In the Authentication Profile, select the SAML Server profile and Certificate Profile to validate the IdP certificate.If your IdP signing certificate is a self-signed certificate, there is no chain of trust; as a result, you cannot enable this option. The firewall always validates the signature of the SAML Responses or Assertions against the Identity Provider certificate that you configure whether or not you enable the Validate Identity Provider Certificate option. If your IdP provides a self-signed certificate, ensure that you are using PAN-OS 10.0 to mitigate exposure to CVE-2020-2021.Validate the certificate to ensure it hasn’t been compromised and to improve security.Enter the Maximum Clock Skew, which is the allowed difference in seconds between the system times of the IdP and the firewall at the moment when the firewall validates IdP messages (default is 60; range is 1 to 900). If the difference exceeds this value, authentication fails.Click OK to save the server profile.Click the server profile Name to display the profile settings. Verify that the imported information is correct and edit it if necessary.Whether you import the IdP metadata or manually enter the IdP information, always ensure that the signing certificate of your SAML identity provider is the Identity Provider Certificate for your server profile and your IdP sends signed SAML Responses, Assertions, or both.Configure an authentication profile.The profile defines authentication settings that are common to a set of users.
- Select DeviceAuthentication Profile and Add a profile.Enter a Name to identify the profile.Set the Type to SAML.Select the IdP Server Profile you configured.Select the Certificate for Signing Requests.The firewall uses this certificate to sign messages it sends to the IdP. You can import a certificate generated by your enterprise CA or you can generate a certificate using the root CA that was generated on the firewall or Panorama.(Optional) Enable Single Logout (disabled by default).Select the Certificate Profile that the firewall will use to validate the Identity Provider Certificate.Enter the Username Attribute that IdP messages use to identify users (default username).When you predefine dynamic administrator roles for users, use lower-case to specify the role (for example, enter superreader, not SuperReader). If you manage administrator authorization in the IdP identity store, specify the Admin Role Attribute and Access Domain Attribute also.Select Advanced and Add the users and user groups that are allowed to authenticate with this authentication profile.Click OK to save the authentication profile.Assign the authentication profile to firewall applications that require authentication.
- Assign the authentication profile to:
- Administrator accounts that you manage locally on the firewall. In this example, Configure a Firewall Administrator Account before you verify the SAML configuration later in this procedure.
- Administrator accounts that you manage externally in the IdP identity store. Select DeviceSetupManagement, edit the Authentication Settings, and select the Authentication Profile you configured.
- Authentication policy rules that secure the services and applications that end users access through Authentication Portal. See Configure Authentication Policy.
- GlobalProtect portals and gateways that end users access.
Commit your changes.The firewall validates the Identity Provider Certificate that you assigned to the SAML IdP server profile.Create a SAML metadata file to register the firewall application (management access, Authentication Portal, or GlobalProtect) on the IdP.- Select DeviceAuthentication Profile and, in the Authentication column for the authentication profile you configured, click Metadata.In the Service drop-down, select the application you want to register:
- management (default)—Administrative access to the web interface.
- authentication-portal—End user access to services and applications through Authentication Portal.
- global-protect—End user access to services and applications through GlobalProtect.
(Authentication Portal or GlobalProtect only) for the Vsysname Combo, select the virtual system in which the Authentication Portal settings or GlobalProtect portal are defined.Enter the interface, IP address, or hostname based on the application you will register:- management—For the Management Choice, select Interface (default) and select an interface that is enabled for management access to the web interface. The default selection is the IP address of the MGT interface.
- authentication-portal—For the IP Hostname, enter the IP address or hostname of the Redirect Host (see DeviceUser IdentificationAuthentication Portal Settings).
- global-protect—For the IP Hostname, enter the hostname or IP address of the GlobalProtect portal or gateway.
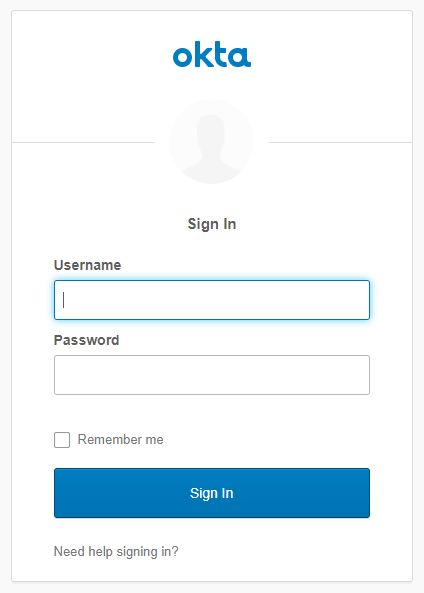
Click OK and save the metadata file to your client system.Import the metadata file into the IdP server to register the firewall application. Refer to your IdP documentation for instructions.Verify that users can authenticate using SAML SSO.For example, to verify that SAML is working for access to the web interface using a local administrator account:- Go to the URL of the firewall web interface.Click Use Single Sign-On.Enter the username of the administrator.Click Continue.The firewall redirects you to authenticate to the IdP, which displays a login page. For example:
![]() Log in using your SSO username and password.After you successfully authenticate on the IdP, it redirects you back to the firewall, which displays the web interface.Use your firewall administrator account to request access to another SSO application.Successful access indicates SAML SSO authentication succeeded.
Log in using your SSO username and password.After you successfully authenticate on the IdP, it redirects you back to the firewall, which displays the web interface.Use your firewall administrator account to request access to another SSO application.Successful access indicates SAML SSO authentication succeeded.