Create an External Dynamic List Using the EDL Hosting Service
Table of Contents
End-of-Life (EoL)
Create an External Dynamic List Using the EDL Hosting Service
Configure an External Dynamic List (EDL) for Software-as-a-Service
(SaaS) applications.
Some Software-as-a-Service (SaaS)
providers publish lists of IP addresses and URLs as destination endpoints for their
SaaS applications. SaaS providers frequently update the SaaS applications
destination endpoint lists as support grows and the service expands. This requires
you to manually monitor the SaaS application endpoints for changes and manually
update your policy configuration to ensure connectivity to these critical SaaS
applications or set up an external tool to monitor and update your EDLs.
Configure an EDL using the EDL Hosting Service maintained by Palo
Alto Networks to ease the operational burden of maintaining an EDL for a SaaS
application. The EDL Hosting Service provides publicly available Feed URLs for SaaS
application endpoints published by the SaaS application provider. Leveraging a Feed
URL as the source in an EDL allows for dynamic enforcement of SaaS application
traffic without the need for you to host and maintain your own EDL source.
Palo Alto Networks checks the application Feed URLs published by SaaS providers on a
daily basis and optimizes the IP address information received from SaaS application
providers in order to reduce the number of IP addresses that are published in each
EDL. This optimization includes identifying and removing duplicate IP addresses and
then aggregating the remaining IP addresses into a smaller number of contiguous
address ranges.
Microsoft updates all Microsoft 365 Feed URLs at the end of each calendar month and
provides a 30 day advanced notice prior to update. See the official Microsoft 365 Web Services page
for more information. Additionally, the endpoints for the Microsoft 365 Common and
Office Online SaaS application are always added to every Feed URL in the EDL Hosting
Service.
The EDL Hosting Service availability status and updates are posted to the Palo
Alto Networks Cloud Services Status page.
- Visit the EDL Hosting Service and identify the Feed URL for your SaaS application.Review the Microsoft 365 documentation for more information which Feed URL is best for your use case. Additionally, consider the SaaS application and location of users accessing the SaaS application when identifying a Feed URL to. For example, if you have a branch in Germany that only needs to access Exchange Online, select a Feed URL from the Service Area: Exchange Online for Germany.For a policy-based forwarding policy rule, use an IP-based Feed URL.(Best Practices) Create a certificate profile to authenticate the EDL Hosting Service.
- Download the GlobalSign Root R1 certificate.Convert the GlobalSign Root R1 Certificate to PEM Format.Launch the firewall web interface.Import the GlobalSign Root R1 certificate.
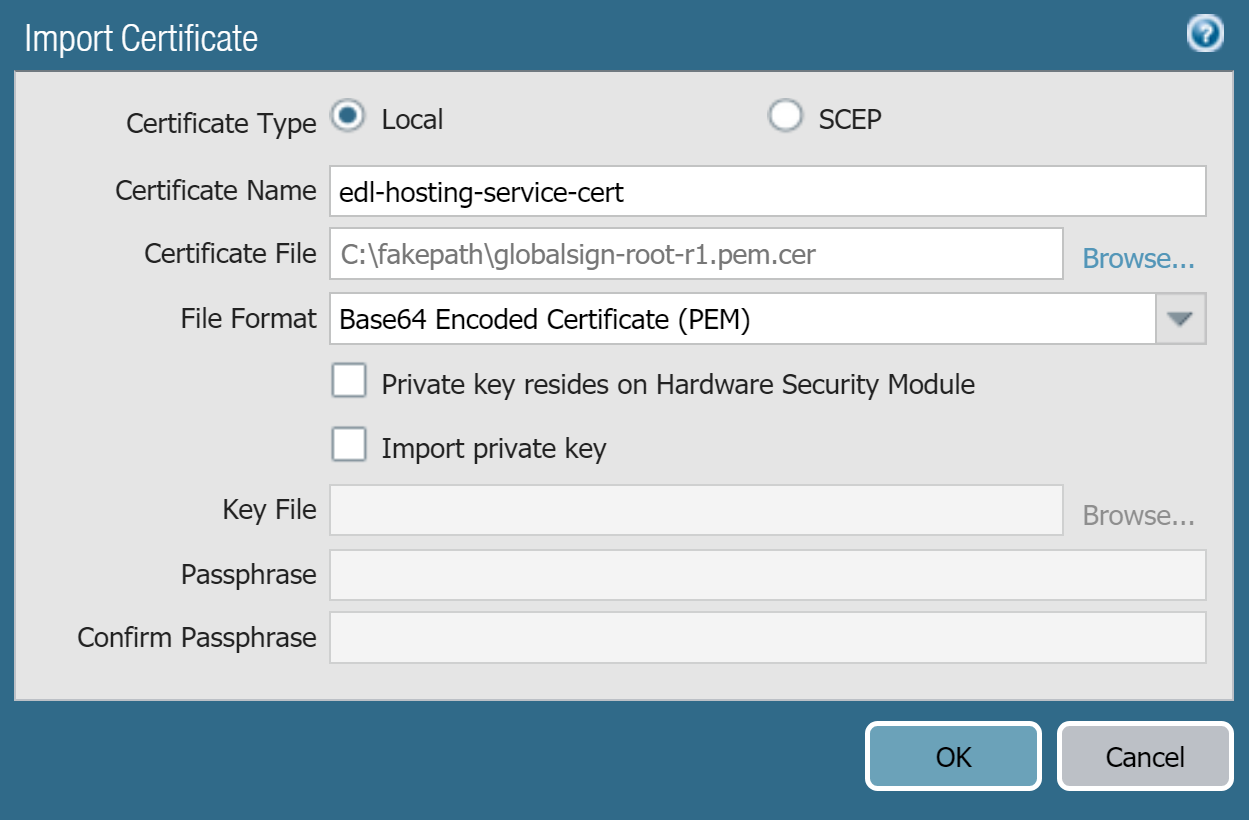
- Select DeviceCertificate ManagementCertificates and Import a new certificate.
- For Certificate Type, select Local.
- Enter a descriptive Certificate Name.
- For the Certificate File, select Browse and select the certificate you downloaded in the previous step.
- For the File Format, select Base64 Encoded Certificate (PEM).
- Click OK.
![]() Create a certificate authority (CA) certificate profile.
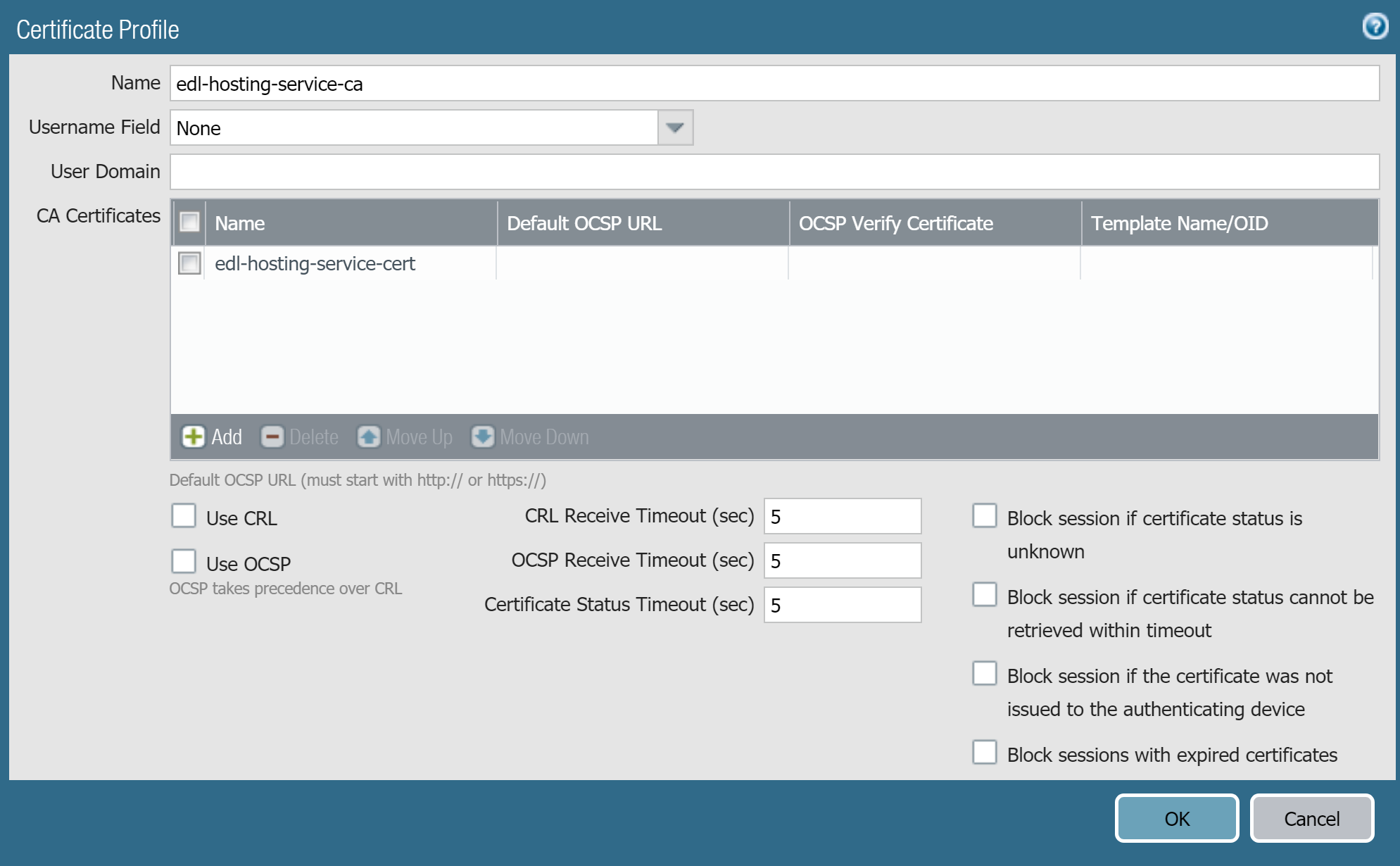
Create a certificate authority (CA) certificate profile.- Select DeviceCertificate ManagementCertificate Profile and Add a new certificate profile.
- Enter a descriptive Name.
- For the CA Certificates, Add the certificate you imported in the previous step.
- Click OK.
![]() Commit.Create an EDL using a Feed URL from the EDL Hosting Service.
Commit.Create an EDL using a Feed URL from the EDL Hosting Service.- Select ObjectsExternal Dynamic Lists and Add a new EDL.Enter a descriptive Name for the EDL.Select the EDL Type.
- For an IP-based EDL, select IP List.
- For a URL-based EDL, select URL List.
(Optional) Enter a Description for the EDLEnter the Feed URL as the EDL Source.Enforce all endpoints within a specific Feed URL. Adding an excluding a specific endpoint from a Feed URL can cause connectivity issues to the SaaS application.(Best Practices) Select the Certificate Profile you created in the previous step.Specify the frequency the firewall should Check for updates to match the update frequency of the Feed URL.For example, if the Feed URL is updated daily by Palo Alto Networks then configure the EDL to check for updates Daily.Palo Alto Networks displays the update frequency for each Feed URL in the EDL Hosting Service. Feed URLs are automatically updated with any new endpoints.Click Test Source URL to verify that the firewall can access the Feed URL from the EDL Hosting Service.Click OK.![]() Enforce Policy on an External Dynamic List.When you enforce policy on an EDL from the EDL Hosting Service where the EDL is the source, be specific when configuring which users have access to the SaaS application to avoid over-provisioning access to the application.Leverage App-ID alongside EDLs in a policy rule for additional strict enforcement of SaaS application traffic.
Enforce Policy on an External Dynamic List.When you enforce policy on an EDL from the EDL Hosting Service where the EDL is the source, be specific when configuring which users have access to the SaaS application to avoid over-provisioning access to the application.Leverage App-ID alongside EDLs in a policy rule for additional strict enforcement of SaaS application traffic.