Redistribute User-ID Information From an On-Premises Firewall to Prisma Access
Table of Contents
Expand All
|
Collapse All
Prisma Access Docs
-
-
- Prisma Access China
- 4.0 & Later
- 3.2 Preferred and Innovation
- 3.1 Preferred and Innovation
- 3.0 Preferred and Innovation
- 2.2 Preferred
-
-
-
- 5.2 Preferred and Innovation
- 5.1 Preferred and Innovation
- 5.0 Preferred and Innovation
- 4.2 Preferred
- 4.1 Preferred
- 4.0 Preferred
- 3.2 Preferred and Innovation
- 3.1 Preferred and Innovation
- 3.0 Preferred and Innovation
- 2.2 Preferred
Redistribute User-ID Information From an On-Premises Firewall to Prisma Access
Shows the steps you use to redistribute User-ID information
from an on-premises firewall to Prisma Access.
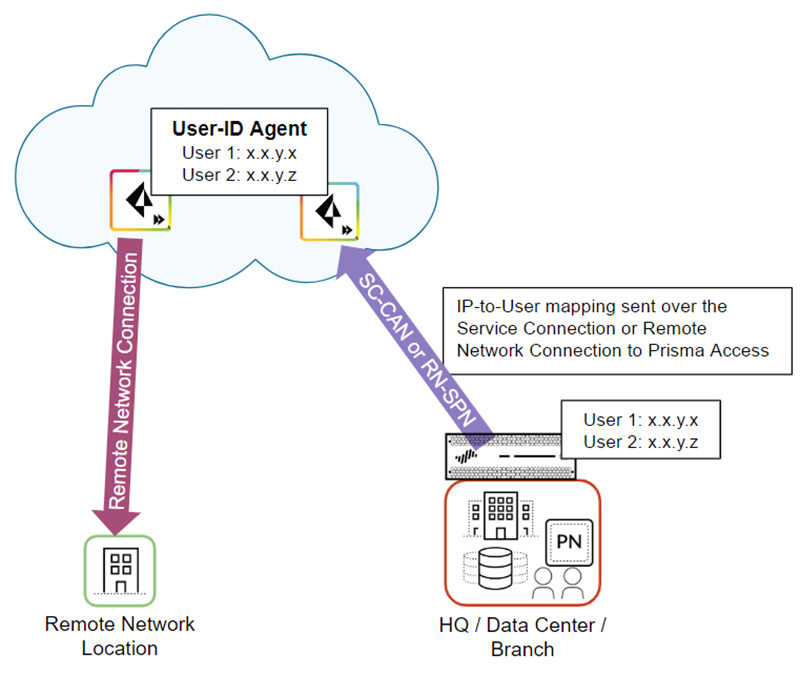
In cases where users are at a branch location
or HQ that is secured by an on-premises next-generation firewall
with user-based policies, and they need to access resources at another
branch location that you have secured with Prisma Access, you must redistribute IP address-to-user
name mappings from the on-premises firewall to Prisma Access.
The
following figure shows an HQ/Data center with an on-premises next-generation
firewall with existing IP address-to-username mapping. Prisma Access connects
to the firewall with either a service connection (SC-CAN) or remote
network connection (RN-SPN), and the on-premises firewall redistributes
the mapping to Prisma Access.
The following figure shows a
Prisma Access service connection or remote network connection being
used to redistribute the mapping. You can use any route path over
an IPSec trusted tunnel for privately addressed destinations to
redistribute this mapping.
To redistribute
User-ID mappings from an on-premises firewall to Prisma Access,
complete the following steps.
- Configure the on-premises firewall to redistribute User-ID information to Prisma Access.
- From the on-premises firewall, select DeviceData RedistributionCollector Settings.Click the gear icon to edit the settings.Provide a Collector Name and a Collector Pre-Shared Key to identify the on-premises firewall as a User-ID agent.Click OK to save your changes.Configure Prisma Access to collect the User-ID mapping from the on-premises firewall.
- From the Panorama that manages Prisma Access, select DeviceData RedistributionAgents.Make sure that you have selected the Service_Conn_Template (for service connections) or the Remote_Network_Template (for remote network connections) in the Templates drop-down at the top of the page.Add a User-ID Agent and give it a Name.Select Host and Port.Enter the IP address of the MGT interface or service route that the firewall uses to send user mappings in the Host field.For the MGT interface, you can enter a hostname instead of the IP address.Enter the Collector Name and Collector Pre-Shared Key, using the values for the collector you used for the on-premises firewall in Step 1.Select IP User Mappings.Click OK.
