Get a Packet Capture of a GTP Event
Table of Contents
10.1 (EoL)
Expand all | Collapse all
End-of-Life (EoL)
Get a Packet Capture of a GTP Event
Get a packet capture of a GTP event, such as GTP-in-GTP,
to troubleshoot an abnormal GTP packet.
To make it easier to troubleshoot an erroneous
General Packet Radio Service (GPRS) tunneling protocol (GTP) packet,
you can capture a single GTP packet that triggered any of the following
GTP events:
- GTP-in-GTP
- End-user IP address spoofing
- Abnormal GTPv1-C, GTPv2-C, and GTP-U messages that have a missing mandatory Information Element (IE), invalid IE, out-of-order IE, invalid header, or unsupported message type
- Other abnormal GTPv1-C, GTPv2-C, or GTP-U messages
- Enable GTP or confirm that it is already enabled.Enable packet capture in a Mobile Network Protection Profile.
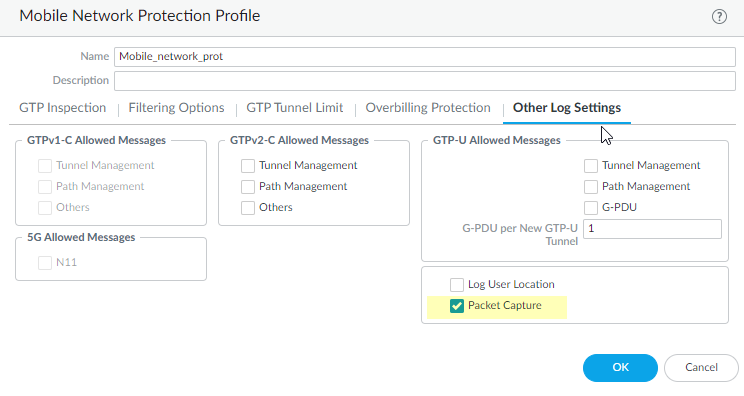
- Select ObjectsSecurity ProfilesMobile Network Protection and select an existing profile or Add a new profile.Select GTP InspectionGTP-C and enable either GTPv2-C Stateful Inspection or GTPv1-C Stateful Inspection to enable the Mobile Network Protection profile.Select Other Log Settings and enable Packet Capture.
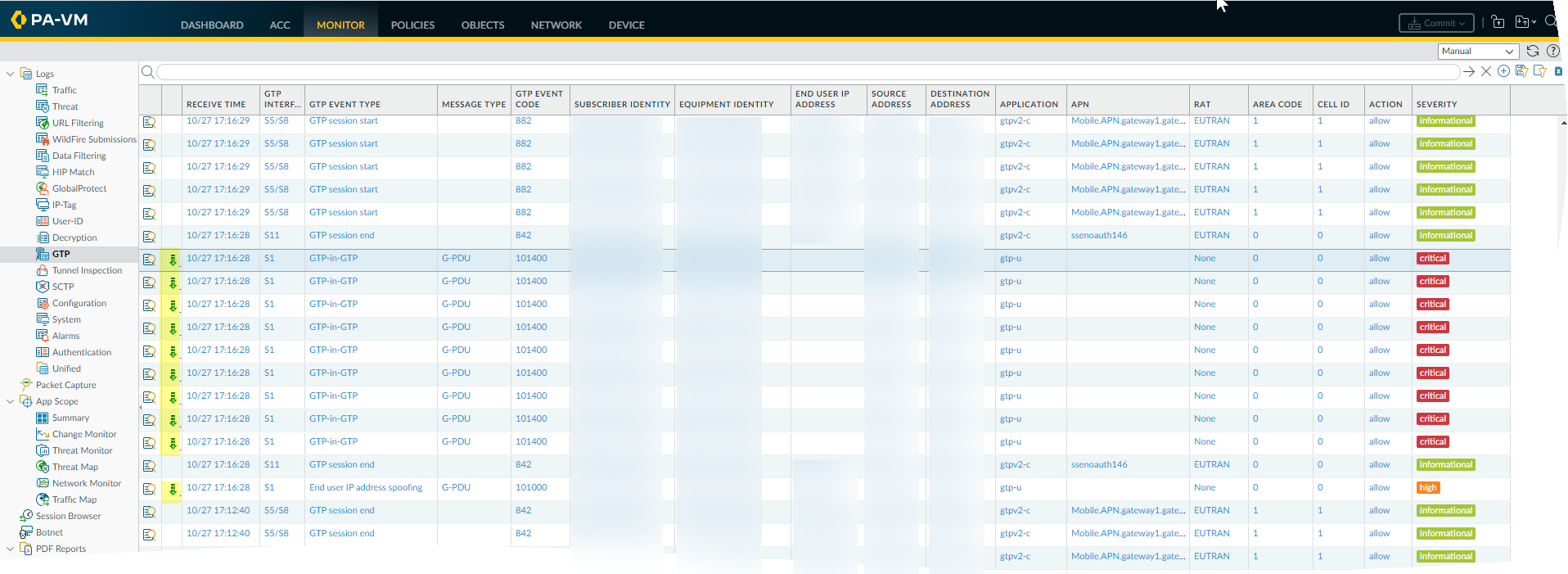
![]() Click OK.Apply the Mobile Network Protection profile to a Security policy rule that applies to the zone you are protecting.Commit your changes.If the Application Command Center (ACC) on your firewall indicates a GTP problem that you want to troubleshoot, select MonitorLogsGTP and look for the GTP packet capture icon () at the beginning of rows that capture troublesome GTP packets. In those rows you’ll see the GTP Event Type (such as Abnormal GTPv2-C message with missing mandatory IE), the Subscriber Identity (IMSI), source and destination IP address of the packet, and other information.
Click OK.Apply the Mobile Network Protection profile to a Security policy rule that applies to the zone you are protecting.Commit your changes.If the Application Command Center (ACC) on your firewall indicates a GTP problem that you want to troubleshoot, select MonitorLogsGTP and look for the GTP packet capture icon () at the beginning of rows that capture troublesome GTP packets. In those rows you’ll see the GTP Event Type (such as Abnormal GTPv2-C message with missing mandatory IE), the Subscriber Identity (IMSI), source and destination IP address of the packet, and other information.![]()
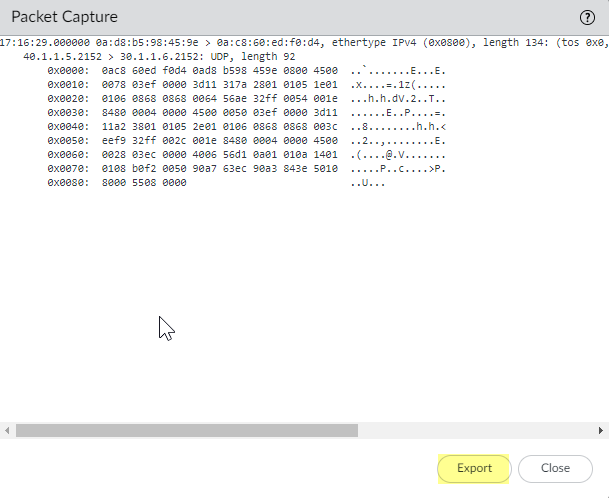
![]() If you want more details to verify the event, click the download icon () to download a packet capture file.
If you want more details to verify the event, click the download icon () to download a packet capture file.![]()
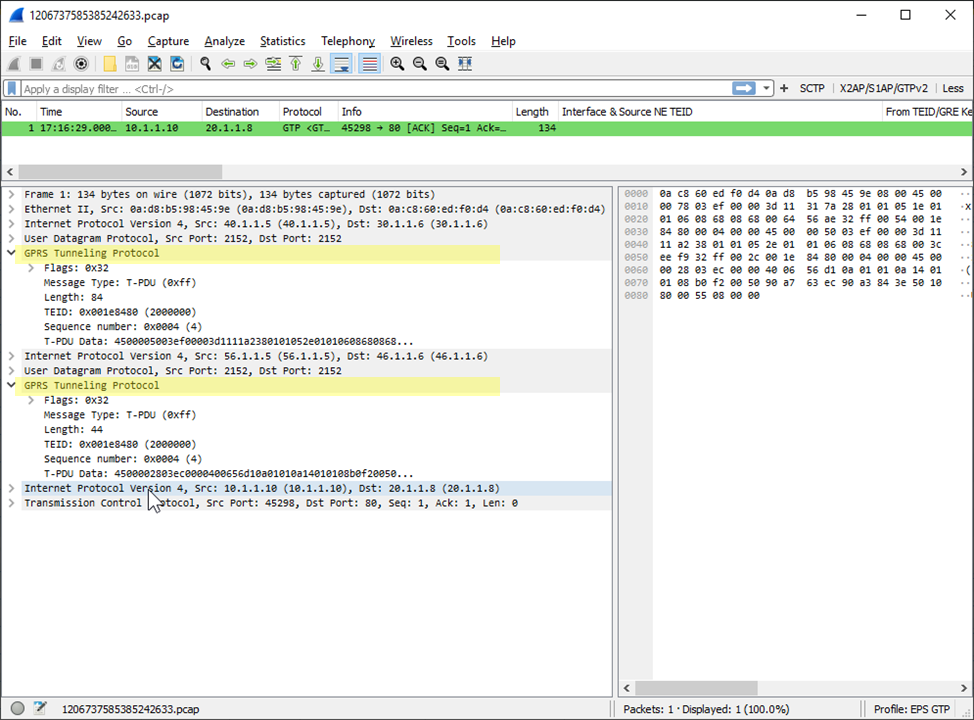
![]() Export the file to readable format and verify that the details support the GTP event type.In this packet capture example, the packet has two headers titled GPRS Tunneling Protocol; a GTP header inside another GTP header verifies that the GTP-in-GTP event is not a false positive; it’s identified as a GTP-in-GTP attack.
Export the file to readable format and verify that the details support the GTP event type.In this packet capture example, the packet has two headers titled GPRS Tunneling Protocol; a GTP header inside another GTP header verifies that the GTP-in-GTP event is not a false positive; it’s identified as a GTP-in-GTP attack.![]()