Support for Custom Layer 3 and Layer 4 Threat Signatures
Table of Contents
Expand all | Collapse all
Support for Custom Layer 3 and Layer 4 Threat Signatures
As part of zone security enhancements, you
can now write custom threat (vulnerability) signatures based on
Layer 3 and Layer 4 header fields (such as IP flags, acknowledgment numbers,
etc). This enables you to provide improved vulnerability signature
coverage resulting from old and deprecated TCP/IP stacks used in
embedded / IoT devices.
Custom L3 & L4 vulnerability signatures
are expressed through your Zone and Zone Protection profile configuration.
You must specify how the firewall responds when it detects a threat.
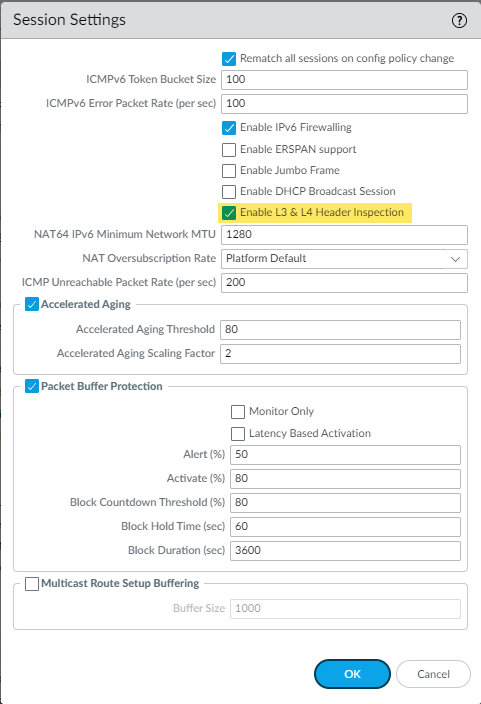
- Selectand enableDeviceSetupSessionL3 & L4 Header Inspectionglobally on the firewall.
![]()
- Create a Zone Protection profile and configure the L3 & L4 header inspection settings.
- Selectand either select an existing profile orNetworkNetwork ProfilesZone ProtectionAdda new profile.
- If you are creating a new zone protection profile, enter aNamefor the profile and an optionalDescription.
- SelectL3 & L4 Header Inspectionto define your custom vulnerability signatures.
- Addnew custom rules by defining the configuration and signature details for each entry, which are performed in their respective tabs:ConfigurationandSignature.
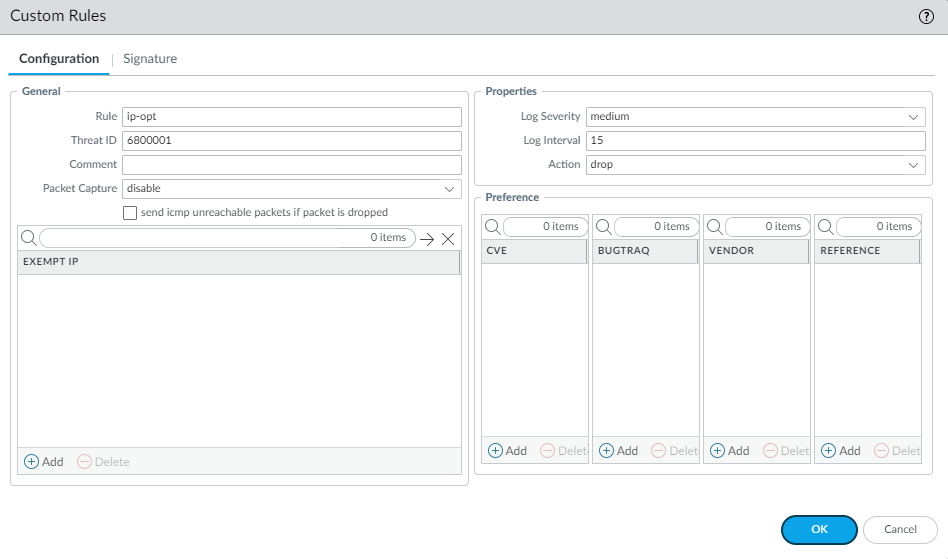
- UnderConfiguration, fill out the following required fields in the General, Properties, and Preference section.
![]()
- Rule—Specify the custom rule name.
- Threat ID—Enter a numeric ID between 41000 and 45000 or 6800001 and 6900000.
- Comment—Optionally, add a description of the custom rule.
- Packet Capture—Select a packet capture setting.Optionally, selectsend icmp unreachable packets if packet is droppedto send an ICMP unreachable response to the client upon packet loss.
- Exempt IP—Enter the IP address(es) for which you do not want the custom rule to apply to.
- Log Severity—Select the severity of the threat.
- Log Interval—Indicates how frequently an event is logged.
- Action—Choose the action to take when there is a custom signatures match. Options include alert, drop, reset-client, reset-server, and reset-both. Refer to Security Policy Actions for more information about these action settings.
- Preference—Add references to provide context or related information about the custom threat signature. You can add CVEs, Bugtraq citations, 3rd party vendor IDs, or reference links to additional analysis or background information.
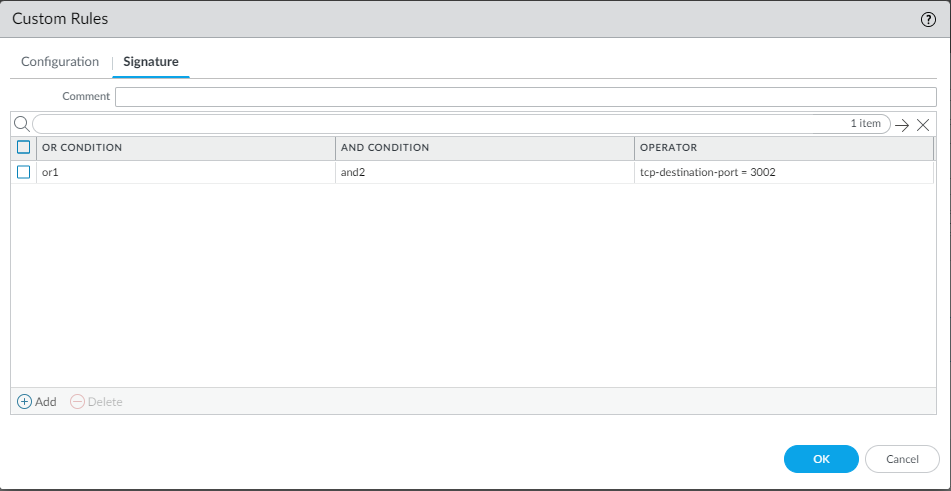
- From theSignaturetab, provide a name or description of the custom vulnerability underComment. After specifying a name, selectAddto provide the custom signature details.
![]()
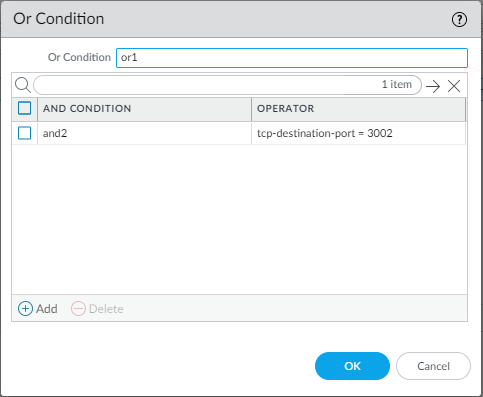
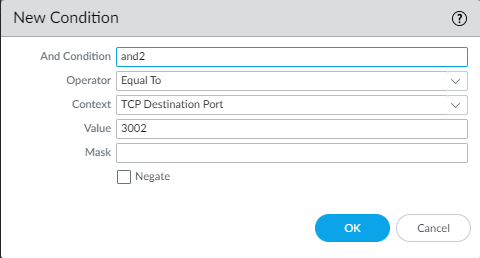
- Specify a matching Or Condition. When finished, selectAddto configure an And Condition and the associated values in a new window.
![]()
- If you select aLess ThanorGreater Thanoperator, specify aContextand aValue. TheEqual Tooperator additionally hasMaskandNegateoptions. Click OK when you have finished configuring the new and condition.
![]()
- Repeat for each matching condition that you want to add.
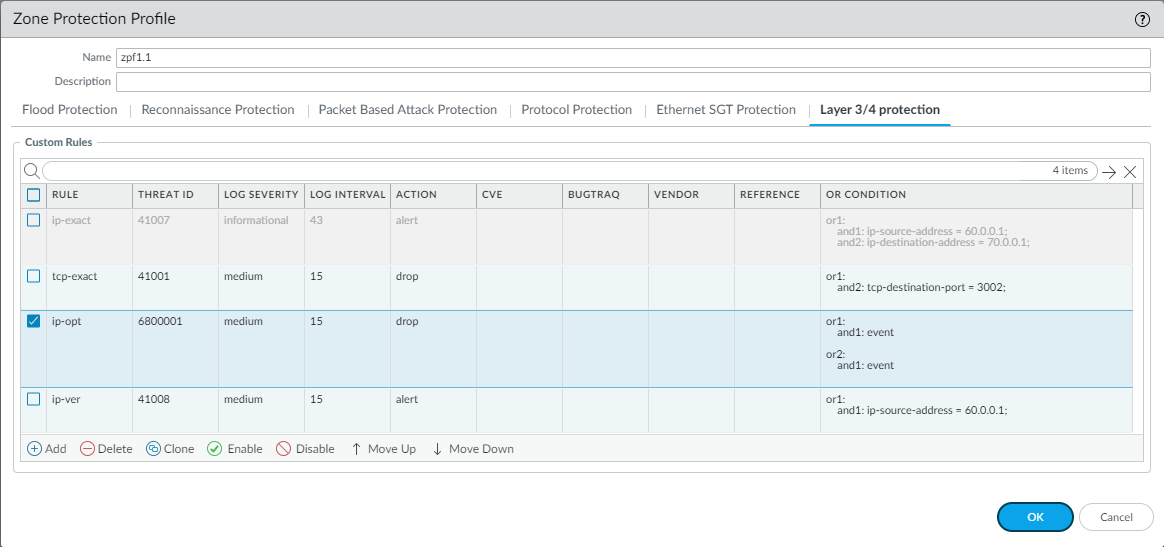
- ClickOKand review your signatures. ClickOKagain to return to the zone protection profile.
- From theL3 & L4 Header Inspectiontab, you can reorder, disable, and clone the custom rule entries as necessary. ClickOKto exit the zone protection profile.
![]()
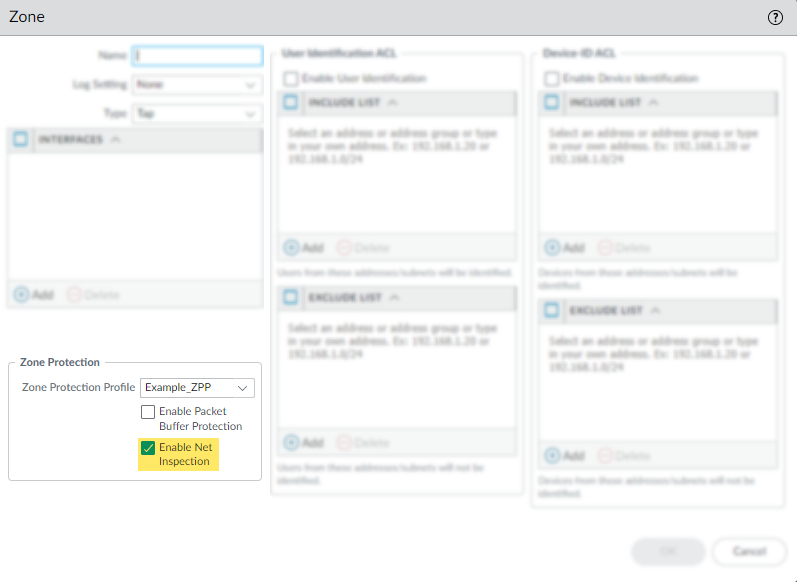
- Apply the Zone Protection profile to a security zone that is assigned to interfaces you want to protect.
- Selectand select the zone where you want to assign the Zone Protection profile.NetworkZones
- AddtheInterfacesbelonging to the zone.
- ForZone Protection Profile, select the profile you just created.
- SelectEnable Net Inspectionto enable the L3 & L4 header inspection configuration settings.
![]()
- ClickOK.
- Commityour changes.