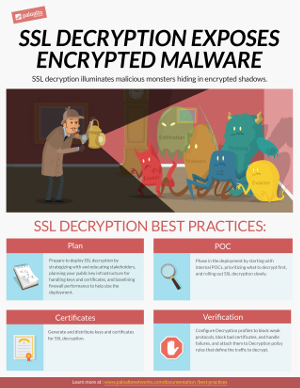
Decryption Best Practices
You can't defend against threats you can’t see. By enabling decryption on your next-gen firewalls you can inspect and control SSL/TLS and SSH traffic so that you can detect and prevent threats that would otherwise remain hidden in encrypted traffic. Use the best practice guidelines in this site to learn how to plan for and deploy decryption in your organization.
What Do You Want To Do?
Featured Topics
Best Practice Decryption Profile: Data Center
Decryption Profiles define the cipher suite settings the firewall accepts so you can protect against vulnerable, weak protocols and algorithms.
Recommended Topics
Best Practice Decryption: Internet Gateway
You can't protect against threats you can't see. Decrypt as much traffic as local regulations and business requirements allow so you can inspect the traffic and block threats.