Advanced URL Filtering
Configure Inline Categorization (PAN-OS 10.1)
Table of Contents
Configure Inline Categorization (PAN-OS 10.1)
Configure URL Filtering Inline ML in PAN-OS 10.1.
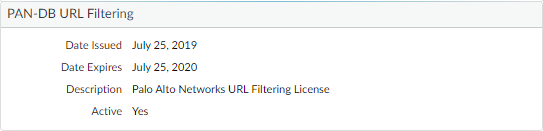
- Log in to the PAN-OS web interface.Verify that you have an active legacy URL filtering or Advanced URL Filtering subscription.Select DeviceLicenses and confirm that a URL filtering license is available and has not expired.
![]() Configure the URL Filtering Inline ML settings in a URL Filtering profile.
Configure the URL Filtering Inline ML settings in a URL Filtering profile.- Select ObjectsSecurity ProfilesURL Filtering, then Add or select a URL Filtering profile.Select Inline ML and define an Action for each inline ML model.There are two classification engines available for each type of malicious webpage content: Phishing and JavaScript Exploit.
- Block—When the firewall detects a website with phishing content, the firewall generates a URL Filtering log entry.
- Alert—The firewall allows access to the website and generates a URL Filtering log entry.
- Allow—The firewall allows access to the website but does not generate a URL Filtering log entry.
![]() Click OK to save your changes.Commit your changes.(Optional) Add URL exceptions to your URL Filtering profile if you encounter false-positives.You can add exceptions by specifying an external dynamic list in the URL Filtering profile or by adding a web page entry from the URL Filtering logs to a custom URL category.
Click OK to save your changes.Commit your changes.(Optional) Add URL exceptions to your URL Filtering profile if you encounter false-positives.You can add exceptions by specifying an external dynamic list in the URL Filtering profile or by adding a web page entry from the URL Filtering logs to a custom URL category.- Select Objects > Security Profiles > URL Filtering.Select a URL Filtering profile for which you want to exclude specific URLs, then select Inline ML.Add a pre-existing external dynamic list of URL type. If none is available, create a new external dynamic list.Click OK to save your changes.Commit your changes.Add file exceptions from URL Filtering log entries.
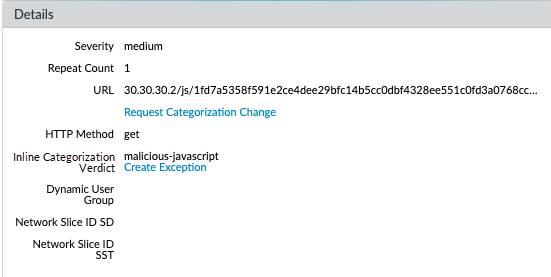
- Select Monitor > Logs > URL Filtering and filter the logs for URL entries with an Inline ML Verdict of malicious-javascript or phishing. Select a URL Filtering log for a URL that you wish to create an exception for.Go to the Detailed Log View and scroll down to the Details pane, then select Create Exception located next to the Inline ML Verdict.
![]() Select a custom category for the URL exception, then click OK.The new URL exception can be found in the list to which it was added, under Objects > Custom Objects > URL Category.(Optional) Verify the status of your firewall’s connectivity to the inline ML cloud service.Use the following CLI command on the firewall to view the connection status.
Select a custom category for the URL exception, then click OK.The new URL exception can be found in the list to which it was added, under Objects > Custom Objects > URL Category.(Optional) Verify the status of your firewall’s connectivity to the inline ML cloud service.Use the following CLI command on the firewall to view the connection status.show mlav cloud-statusFor example:show mlav cloud-status MLAV cloud Current cloud server: ml.service.paloaltonetworks.com Cloud connection: connected
If you are unable to connect to the inline ML cloud service, verify that the ML domain ml.service.paloaltonetworks.com is not blocked.Test your URL filtering deployment.To view information about web pages that have been processed using URL Filtering inline ML, filter the logs (Monitor > Logs > URL Filtering) based on Inline ML Verdict. Web pages that have been determined to contain threats are categorized with verdicts of either phishing or malicious-javascript. For example: ![]()