Prisma Access
Enable Multitenancy and Migrate the First Tenant
Table of Contents
Expand All
|
Collapse All
Prisma Access Docs
-
- 6.1 Preferred and Innovation
- 6.0 Preferred and Innovation
- 5.2 Preferred and Innovation
- 5.1 Preferred and Innovation
- 5.0 Preferred and Innovation
- 4.2 Preferred
- 4.1 Preferred
- 4.0 Preferred
- 3.2 Preferred and Innovation
-
-
- 4.0 & Later
- Prisma Access China
-
-
Enable Multitenancy and Migrate the First Tenant
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
Use the following workflow to enable multitenancy and migrate your existing configuration to the
first tenant you create. If you don’t have any existing configuration, you can
enable multitenancy and add your tenants; then configure them.
When you enable multitenancy,
Prisma Access migrates the following components of your configuration:
- All service connection and remote network tunnel onboarding information, including tunnel configuration.
- Existing mobile users onboarding information.
- Strata Logging Service information.
- Existing Autonomous DEM (ADEM) configuration
- The templates, template stacks, and device groups for service connections, remote networks, and mobile users.
You need to specify the number of users (for a mobile user deployment), bandwidth (for a remote
networks deployment), and Autonomous DEM (ADEM) to allocate for each
deployment (if you have purchased an ADEM license).
Because
of these device group changes, you create an access domain and add
the migrated device groups, templates, and template stacks, as shown
in the following workflow.
If you don’t have an existing
Prisma Access configuration, and you are creating an all-new multitenant
deployment, do not use this workflow; instead, complete the steps
in Add Tenants to Prisma Access to create the
first tenant.
- Determine the number of licensed units you want to allocate to this deployment.While Prisma Access migrates your configuration to the first tenant, you need to specify:
- The Bandwidth to allocate for the tenant’s remote users deployment (if applicable).
- The Users to allocate for the tenant’s mobile users deployment (if applicable).
- The number of ADEM units to allocate for mobile uses and remote networks (if applicable).
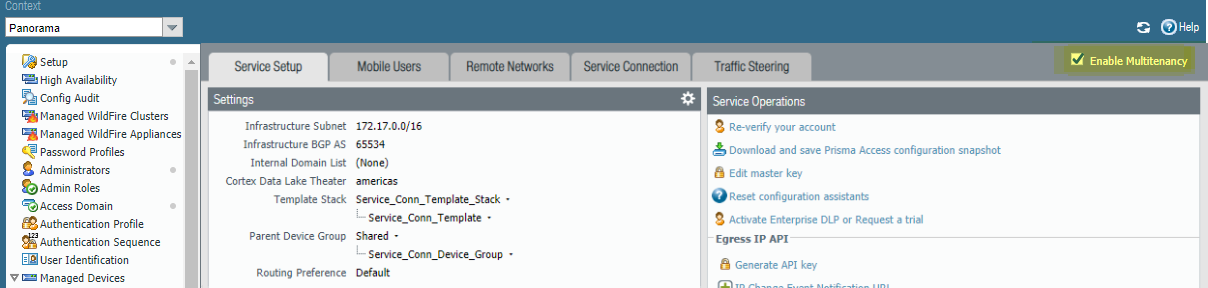
Select PanoramaCloud ServicesConfiguration.Select Enable Multitenancy (located on the upper right of the page).![]() After you enable multitenancy, Panorama displays a notification informing you that the existing Prisma Access configuration move to the first tenant.After you enable multitenancy, your deployment permanently changes to a multitenant deployment, and you cannot revert to single tenant mode.Click OK to migrate the existing configuration to the first tenant.The Tenants page displays, and pie charts in the center of the window display.
After you enable multitenancy, Panorama displays a notification informing you that the existing Prisma Access configuration move to the first tenant.After you enable multitenancy, your deployment permanently changes to a multitenant deployment, and you cannot revert to single tenant mode.Click OK to migrate the existing configuration to the first tenant.The Tenants page displays, and pie charts in the center of the window display.- If you have a remote networks or mobile users license, the available amount of licensed remote network bandwidth and mobile users display.
- (Remote Networks and Mobile User Deployments Only) If you have purchased an Autonomous DEM license, the available number of units for ADEM uses displays.
- If you have a Clean Pipe deployment, the amount of bandwidth for the tenant displays.
Choose the type of deployment you want to use for the tenant.- For a remote network, mobile user deployment, or to configure both deployment types for a tenant, select Remote Networks/Mobile Users.
- For a clean pipe deployment, select Clean Pipe.This section only describes how to configure tenants for remote network, mobile user, or both remote network and mobile user deployment types. To configure the clean pipe service, see Prisma Access for Clean Pipe.
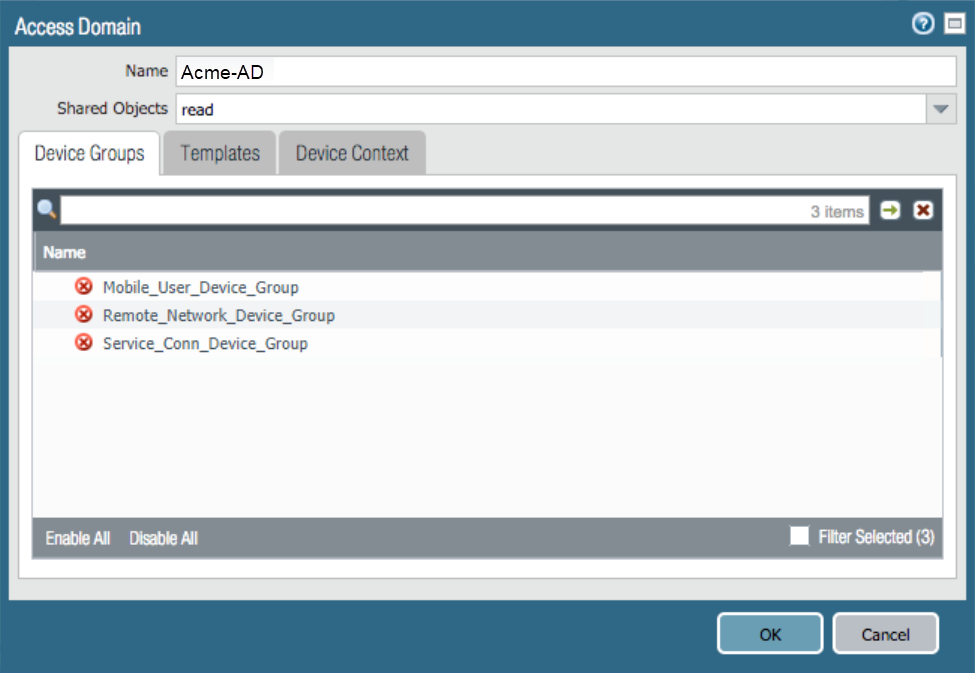
Migrate the existing configuration to the first tenant.The first migrated sub-tenant's name is auto-populated from the tenant you are migrating and cannot be edited.- Create a new Access Domain by clicking the down arrow selecting New Access Domain.Enter a Name for the access domain and click OK.Prisma Access adds the Mobile_User_Device_Group, Remote_Network_Device_Group, and Service_Conn_Device_Group Device Groups to the new access domain.Do not associate the default Device Groups and Templates to other sub-tenants other than the first migrated sub-tenant.
![]() (Optional) Click Templates to verify that Prisma Access added the following templates and template stacks:
(Optional) Click Templates to verify that Prisma Access added the following templates and template stacks:- Explicit_Proxy_Template
- Explicit_Proxy_Template_Stack
- Mobile_User_Template
- Mobile_User_Template_Stack
- Remote_Network_Template
- Remote_Network_Template_Stack
- Service_Conn_Template
- Service_Conn_Template_StackThese are the default template stacks and templates for a standard Prisma Access deployment; if you added other templates, be sure that Prisma Access added them.
![]() (Optional) If you have other templates associated with this configuration, select them.Click OK to close the Access Domain page and return to the Tenants page.Enter the values in Bandwidth (Mbps) for remote networks, Users for mobile users, and the number of Autonomous DEM Users you want to allocate for each deployment type.Use the following guidelines when allocating ADEM units for a tenant:
(Optional) If you have other templates associated with this configuration, select them.Click OK to close the Access Domain page and return to the Tenants page.Enter the values in Bandwidth (Mbps) for remote networks, Users for mobile users, and the number of Autonomous DEM Users you want to allocate for each deployment type.Use the following guidelines when allocating ADEM units for a tenant:- The number of ADEM units you can allocate for mobile users and remote networks can be only equal to or less than base license.
- The minimum number of units you can allocate is 200.
- After you allocate the ADEM units for a tenant, you can edit or remove those units.
- If you did not purchase an ADEM license for your deployment type (Mobile Users or Remote Networks), that choice is grayed out.
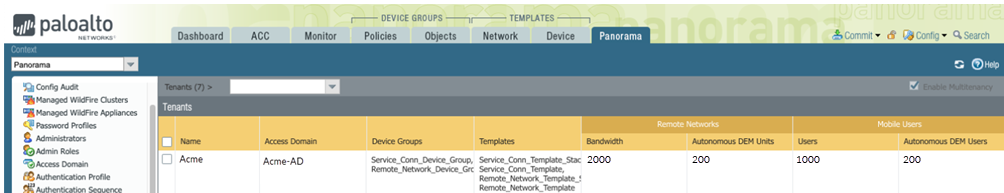
![]() Click OK.The PanoramaCloud ServicesConfiguration page shows the first tenant successfully migrated, and a Tenants drop-down is added above the Tenants area.
Click OK.The PanoramaCloud ServicesConfiguration page shows the first tenant successfully migrated, and a Tenants drop-down is added above the Tenants area.![]() Make sure that all the templates and device groups were populated to the tenant.
Make sure that all the templates and device groups were populated to the tenant.- Select the tenant from the drop-down list.Go to PanoramaCloud ServicesConfiguration.Select Service Setup.Click the gear to edit the Settings.Make sure that the correct template stack, template, and device group (Service_Conn_Template_Stack, Service_Conn_Template, and Service_Conn_Device_Group, respectively) were populated to the settings.Go to oither tabs for which you have existing configuration (for example, Mobile Users—GlobalProtect, Mobile Users—Explicit Proxy, Remote Networks, or Service Connection), click the gear to edit the Settings, and make sure that the correct template stack, template, and device group were populated to the settings.Commit your changes locally to Panorama (CommitCommit to Panorama.Select CommitCommit to Panoramato save your changes locally on the Panorama that manages Prisma Access.If you do not perform a local commit, Prisma Access components do not display in the Push Scope when you Commit and Push your changes.Commit and push your changes to make them active in Prisma Access.
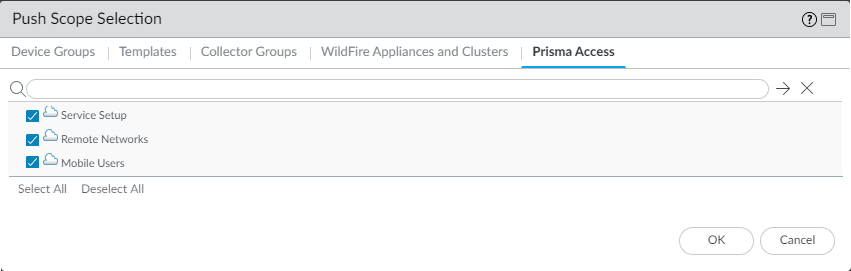
- Select CommitCommit and Push and Edit Selections in the Push Scope.Select Prisma Access, then select the tenant you created, Service Setup, Remote Networks, and Mobile Users.
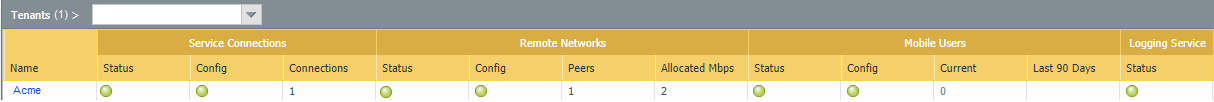
![]() Click OK to save your changes to the Push Scope.Commit and Push your changes.Select PanoramaCloud ServicesStatus.The status page shows the status of all tenants. Because you have created only one tenant, that tenant is the only one that displays. If you select that tenant from the drop-down, you show a detailed status of that tenant.
Click OK to save your changes to the Push Scope.Commit and Push your changes.Select PanoramaCloud ServicesStatus.The status page shows the status of all tenants. Because you have created only one tenant, that tenant is the only one that displays. If you select that tenant from the drop-down, you show a detailed status of that tenant.![]() Selecting a tenant from the drop-down returns you to the Status page for that tenant.Continue to add more tenants to Prisma Access.
Selecting a tenant from the drop-down returns you to the Status page for that tenant.Continue to add more tenants to Prisma Access.