Subscriber ID Security in a 5G Network
Table of Contents
10.0 (EoL)
Expand all | Collapse all
-
- Automatic Content Updates Through Offline Panorama
- Enhanced Authentication for Dedicated Log Collectors and WildFire Appliances
- Syslog Forwarding Using Ethernet Interfaces
- Increased Configuration Size for Panorama
- Access Domain Enhancements for Multi-Tenancy
- Enhanced Performance for Panorama Query and Reporting
- Log Query Debugging
- Configurable Key Limits in Scheduled Reports
- Multiple Plugin Support for Panorama
End-of-Life (EoL)
Subscriber ID Security in a 5G Network
Secure your 5G traffic with Security policy rules that
specify source subscriber identifiers.
Detection of threats in 5G mobile networks
requires identification of compromised subscribers and users. Prevention
requires the ability to apply network security based on subscriber
ID, which is Subscriber Permanent Identifier (SUPI) including
International Mobile Subscriber Identity (IMSI).
You can now
apply network security based on the subscriber identity of subscribers
and users trying to access your 5G network. Security policy rules
and correlation based on 5G SUPI including IMSI are supported on:
- PA-7000 Series firewalls that use the PA-7000-100G-NPC, and the PA-7050-SMC-B card or PA-7080-SMC-B card, and the PA-7000-LFC card (the firewall must use all three cards)
- PA-5200 Series firewalls
- VM-700, VM-500, VM-300, and VM-100 firewalls
When
deciding which firewall model to purchase, consider the total number
of 3G, 4G, and 5G network identifiers (Subscriber IDs and Equipment
IDs) you need to include as external dynamic list (EDL) entries
or static entries. Each firewall model supports a number of EDL entries and static
entries.
- Enable GTP Security, commit, and reboot the firewall.Enable inspection of 5G HTTP/2 control packets and content inspection of GTP-U packets; create a Mobile Network Protection profile.Create address objects for the IP addresses assigned to the network elements in your topology, such as the AMF on the N11 interface, the gNB on the N3 interface, the SMF on the N11 interface, and the UPF on the N3 interface.(Optional) Create an External Dynamic List (EDL) of Type Subscriber Identity List; the Source of the list provides access to a server that provides identifiers of subscribers connected to the 5G network, for which you want to allow (or deny) traffic.Create a Security policy rule that applies your Mobile Network Protection profile to application traffic.
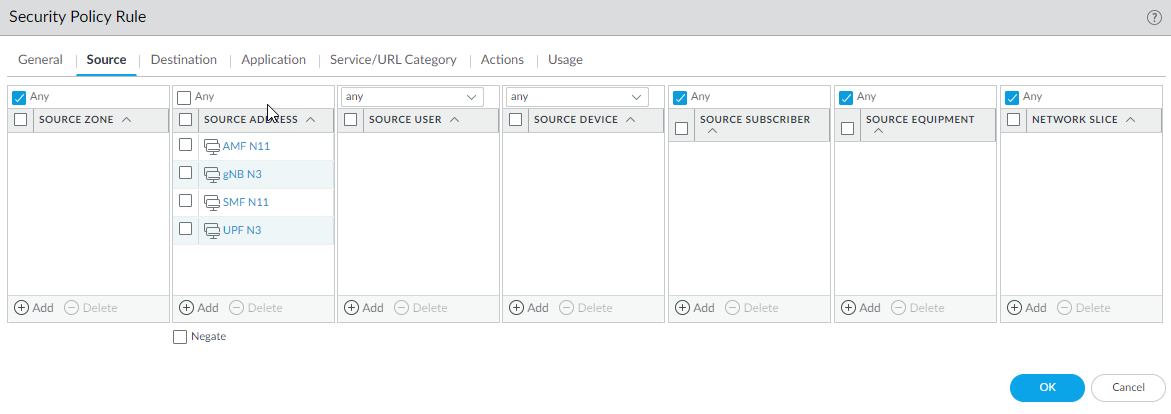
- Select PoliciesSecurity and Add a Security policy rule by Name.For Source Address, Add the address objects for the 5G element endpoints on the N3 and N11 interfaces that you want to allow.
![]() For Destination, Add the Destination Address address objects for the 5G element endpoints on the N3 and N11 interfaces that you want to allow.Add the Applications to allow, such as gtp-u for the user plane and web-browsing, which has HTTP/2.On the Actions tab, select the Action, such as Allow, and select the Mobile Network Protection profile you created.Click OK.Create another Security policy rule based on Subscriber ID.
For Destination, Add the Destination Address address objects for the 5G element endpoints on the N3 and N11 interfaces that you want to allow.Add the Applications to allow, such as gtp-u for the user plane and web-browsing, which has HTTP/2.On the Actions tab, select the Action, such as Allow, and select the Mobile Network Protection profile you created.Click OK.Create another Security policy rule based on Subscriber ID.- Select PoliciesSecurity and Add a Security policy rule by Name, for example, 5G Subscriber ID Security.Select Source tab and Add a Source Zone or select Any.Add one or more Source Subscriber IDs (if you configured an EDL, specify that EDL.
- 5G Subscriber Permanent Identifier (SUPI) including IMSI
- IMSI (14 or 15 digits)
- Range of IMSI values separated by a hyphen. In a range, only the 11th digit through the 15th digit of the IMSI can change from the start of the range to the end of the range; for example, 111111111111122-111111111119999.
- IMSI prefix of six digits with an asterisk (*) as the wildcard after the prefix; for example, 926789*.
- EDL that specifies IMSIs
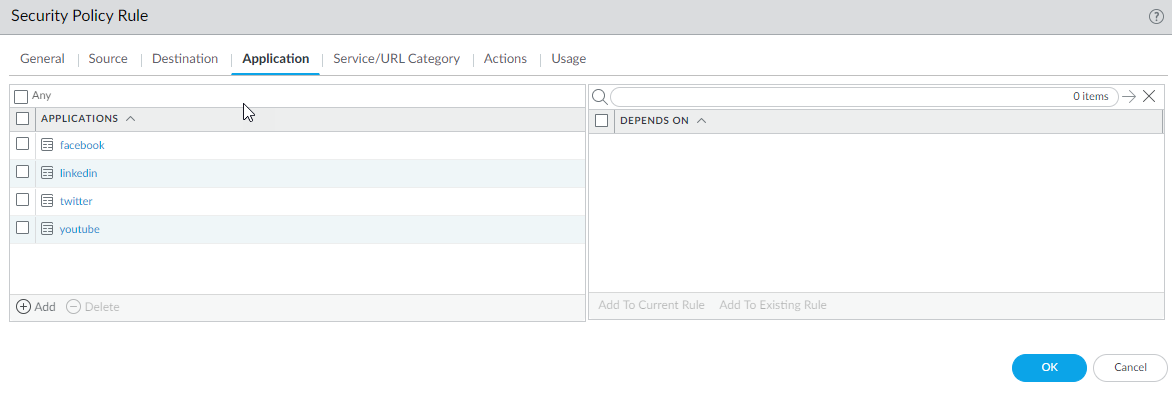
Specify Destination Zone, Destination Address, and Destination Device as Any.Add the Applications to allow, for example, youtube, facebook, linkedin, and twitter.![]() On the Actions tab, select the Action, such as Allow.Click OK.Commit.
On the Actions tab, select the Action, such as Allow.Click OK.Commit.