Network Security
Exclude Traffic from Decryption for Business, Legal, or Regulatory Reasons
Table of Contents
Expand All
|
Collapse All
Network Security Docs
Exclude Traffic from Decryption for Business, Legal, or Regulatory Reasons
Exclude traffic for legal, privacy, or business reasons from decryption to comply
with those policies while still applying SSL/TLS protections with a decryption
profile.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
No separate license required for decryption when using NGFWs or
Prisma Access.
Note: The features and capabilities available to you in
Strata Cloud Manager depend on your active license(s).
|
Policy-based decryption exclusions are for excluding traffic that you choose
not to decrypt. You can create a policy-based decryption exclusion based on any
combination of the traffic’s source, destination, service, or URL category. Examples of traffic you may
intentionally not decrypt, or reasons not to decrypt this traffic:
- Traffic that contains personally identifiable information (PII) or other sensitive information, such as traffic to the financial-services, health-and-medicine, and government URL categories.
- Traffic that originates or is destined for executives or other users whose traffic shouldn’t be decrypted.
- Traffic to devices such as finance servers.
- Applications where privacy and the user experience are prioritized over security.
- Decryption of the traffic is prohibited by laws or local regulation. An example of not decrypting traffic for regulatory and legal compliance is the European Union (EU) General Data Protection Regulation (GDPR). The EU GDPR will require strong protection of all personal data for all individuals. The GDPR affects all companies, including foreign companies, that collect or process the personal data of EU residents.Different regulations and compliance rules may mean that you treat the same data differently in different countries or regions. Businesses usually can decrypt personal information in their corporate data centers because the business owns the information. The best practice is to decrypt as much traffic as possible so that you can see it and apply security protection to it.
You can specify websites to exclude from decryption using a predefined URL category, a custom URL category (URL
List type), or an external dynamic list, which define a
dynamic, custom list of URLs. Custom URL categories are ideal for static,
infrequently changing lists of URLs. In environments with dynamically changing IP
addresses, such as Office 365, or where you make frequent changes to the URL list,
it’s often preferable to use an external dynamic list. Changes to external dynamic
lists are less disruptive because changes are applied dynamically; a configuration
commit is not necessary. In contrast, custom URL categories require a commit for any
changes to take effect.
Create an external dynamic list or a custom URL category that contains all the
categories you choose not to decrypt so that one decryption policy rule governs
the encrypted traffic you choose to allow. Apply a no-decryption profile to the
rule. The ability to add categories to an external dynamic list or a custom URL
category makes it easy to exclude traffic from decryption and helps keep the
rulebase clean.
The Next-Generation Firewall (NGFW) compares incoming traffic to
decryption policy rules in the order they are placed in the decryption rulebase. As
such, best practice is to place the following exclusion rules at the top of the
decryption rulebase, in the following order:
- IP address-based exceptions for sensitive destination servers.
- Source-user based exceptions for executives and other users or groups.
- Custom URL or external dynamic list-based exceptions for destination URLs.
- Sensitive predefined URL category-based exceptions for destination URLs of entire categories such as financial-services, health-and-medicine, and government.
Placing exclusions at the top of the rulebase prevents inadvertent decryption of
sensitive traffic or traffic that laws and regulations prohibit from decryption.
Exclude Traffic from Decryption for Business, Legal, or Regulatory Reasons (Strata Cloud Manager)
- Create a decryption policy rule or modify an existing rule.Fill out basic information and all required fields under the Source, Destination, and Log Settings sections. For source and destination Zones, select Any Zones, so that the no-decrypt rule applies to all SSL traffic destined for an external server.Define match criteria for the traffic you want to exclude from decryption.
- In the Services and URLs section, click Add URL Categories.Select from predefined URL categories or Create New custom URL categories. The NGFW excludes traffic to selected categories from decryption unless you create an exception rule.You can also Add External Dynamic Lists or Add SaaS Application Endpoints.Specify that you don't want to decrypt traffic matching the rule.In the Action and Advanced Inspection section, for Action, select Do Not Decrypt.(Best Practice) Apply a decryption profile that blocks sessions with expired certificates and untrusted issuers.
- Configure or modify a no-decryption profile if you haven't already.
- Select the No Decryption tab.
- For Server Certificate Verification, select Block sessions with expired certificate and Block sessions with untrusted issuer.
- Save the profile.
- In the Action and Advanced Inspection section, select the no-decrypt Decryption Profile.
Save the rule.Move (or drag and drop) the decryption exclusion rule to the top of the rulebase.The NGFW enforces decryption rules against incoming traffic in the rulebase sequence and enforces the first rule that matches the traffic.Save the configuration.Select Push ConfigPush.Exclude Traffic from Decryption for Business, Legal, or Regulatory Reasons (PAN-OS)
The following procedure shows how to exclude financial or health-related traffic from SSL Forward Proxy decryption.- Exclude traffic from decryption based on match criteria.
- Select PoliciesDecryption and Add or modify a decryption policy rule.Define the traffic that you want to exclude from decryption.
- Enter a descriptive Name, such as No-Decrypt-Finance-Health.
- For Source and Destination, select Any.
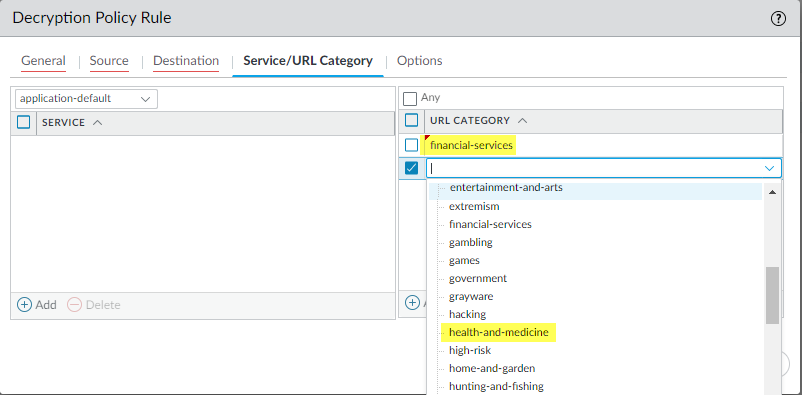
- Select the Service/URL Category tab, and Add the financial-services and health-and-medicine categories.
![]()
Select the Options tab, and for Action, select No Decrypt.(Best Practice) For Decryption Profile, select a no-decryption profile that validates certificates for sessions you don't want to decrypt.Exception: Don’t attach a no-decryption profile to decryption policy rules for TLSv1.3 traffic that you don’t decrypt because NGFWs can’t read the encrypted certificate information so it can’t perform certificate checks. However, you should still create a decryption policy rule for TLSv1.3 traffic that you don’t decrypt because undecrypted traffic isn’t logged unless a decryption policy rule controls that traffic.If you haven't already, configure the decryption profile to Block sessions with expired certificates and Block sessions with untrusted issuers.Click OK.Place your decryption policy rule at the top of the decryption rulebase.The NGFW enforces decryption rules against incoming traffic in the rulebase sequence and enforces the first rule that the traffic matches.Select the No-Decrypt-Finance-Health policy rule (DecryptionPolicies), and click Move Up until it appears at the top of the list, or drag and drop the rule.Save the configuration.Click Commit.