Upgrade Firewalls When Panorama Is Internet-Connected
Table of Contents
Expand all | Collapse all
-
-
- Upgrade Panorama with an Internet Connection
- Upgrade Panorama Without an Internet Connection
- Install Content Updates Automatically for Panorama without an Internet Connection
- Upgrade Panorama in an HA Configuration
- Migrate Panorama Logs to the New Log Format
- Upgrade Panorama for Increased Device Management Capacity
- Upgrade Panorama and Managed Devices in FIPS-CC Mode
- Downgrade from Panorama 10.2
- Troubleshoot Your Panorama Upgrade
-
- What Updates Can Panorama Push to Other Devices?
- Schedule a Content Update Using Panorama
- Panorama, Log Collector, Firewall, and WildFire Version Compatibility
- Upgrade Log Collectors When Panorama Is Internet-Connected
- Upgrade Log Collectors When Panorama Is Not Internet-Connected
- Upgrade a WildFire Cluster from Panorama with an Internet Connection
- Upgrade a WildFire Cluster from Panorama without an Internet Connection
- Upgrade Firewalls When Panorama Is Internet-Connected
- Upgrade Firewalls When Panorama Is Not Internet-Connected
- Upgrade a ZTP Firewall
- Revert Content Updates from Panorama
-
Upgrade Firewalls When Panorama Is Internet-Connected
Procedure to upgrade managed firewalls when Panorama
is Internet connected.
Review the PAN-OS 10.2 Release Notes and then
use the following procedure to upgrade firewalls that you manage
with Panorama. This procedure applies to standalone firewalls and
firewalls deployed in a high availability (HA) configuration.
When upgrading HA firewalls across multiple feature PAN-OS releases, you must upgrade each HA
peer to the same feature PAN-OS release on your upgrade path before continuing. For
example, you are upgrading HA peers from PAN-OS 10.0 to PAN-OS 10.2. You must
upgrade both HA peers to PAN-OS 10.1 before you can continue upgrading to the target
PAN-OS 10.2 release. When HA peers are two or more feature releases apart, the
firewall with the older release installed enters a
suspended state with the message Peer
version too old.
If Panorama is unable to connect directly
to the updates server, follow the Upgrade
Firewalls When Panorama Is Not Internet-Connected procedure
so that you can manually download images to Panorama and then distribute
the images to firewalls.
Before you can upgrade firewalls
from Panorama, you must:
- Upgrade Panorama and its Log Collectors to 10.2 before upgrading the managed firewalls to this version. In addition, when upgrading Log Collectors to 10.2, you must upgrade all Log Collectors at the same time due to changes in the logging infrastructure.(PAN-OS 10.2.6 and earlier releases) Make sure Panorama is running the same or a later PAN-OS version than you are upgrading to.(PAN-OS 10.2.7 and later releases) Panorama can manage a firewall running a higher version of PAN-OS within the same release train. For more information, see Changes to Default Behavior in PAN-OS 10.2
- Ensure that firewalls are connected to a reliable power source. A loss of power during an upgrade can make a firewall unusable.
- Review the Ports Used by Panorama to ensure all required ports are open on your network.
- Decide whether to stay in Legacy mode if the Panorama virtual appliance is in Legacy mode on upgrade to PAN-OS 10.2. Legacy mode is not supported for a new Panorama virtual appliance deployment running PAN-OS 9.1 or later release. If you upgrade the Panorama virtual appliance from PAN-OS 9.0 or earlier release to PAN-OS 10.2, Palo Alto Networks recommends reviewing the Setup Prerequisites for the Panorama Virtual Appliance and changing to Panorama mode or Management Only mode based on your needs.If you want to keep the Panorama virtual appliance in Legacy mode, increase CPUs and memory allocated to the Panorama virtual appliance to a minimum 16 CPUs and 32GB memory to successfully upgrade to PAN-OS 10.2. See the Setup Prerequisites for the Panorama Virtual Appliance for more information.
- (Recommended for multi-vsys managed firewalls) Transition all vsys of a multi-vsys managed firewall to Panorama.This is recommended to avoid commit issues on the multi-vsys managed firewall and allows you to take advantage of optimized shared object pushes from Panorama.
- (Multi-vsys managed firewalls) Delete or rename any locally configured Shared object that has an identical name to an object in the Panorama Shared configuration. Otherwise, configuration pushes from Panorama fail after the upgrade and display the error <object-name> is already in use.
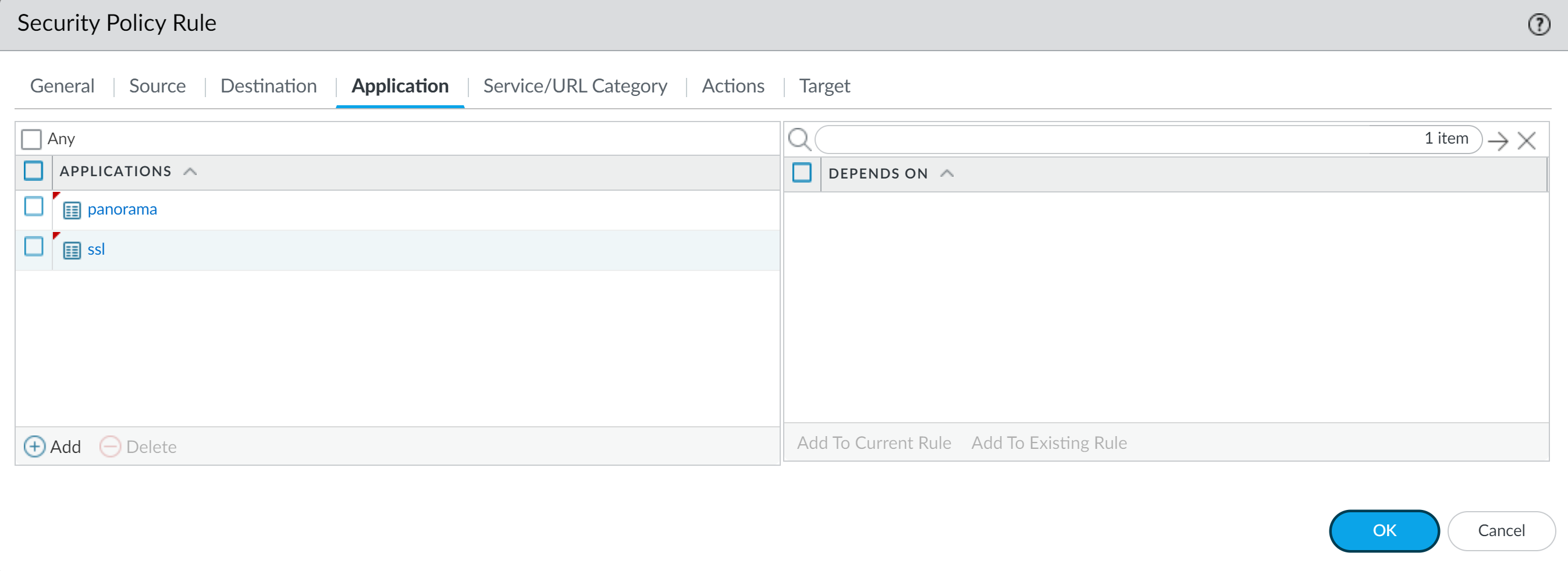
- Log in to the Panorama web interface.Modified your Security policy rule to allow ssl application traffic.This is required to prevent managed devices disconnecting from Panorama after upgrade to PAN-OS 10.2 if traffic between Panorama and managed devices is controlled using the panorama App-ID. Managed devices will disconnect from Panorama if the ssl application is not allowed before you upgrade.PAN-OS 10.2 uses TLS version 1.3 to encrypt the service certificate and handshake messages between Panorama and managed firewalls. As a result, the App-ID for traffic from managed firewalls to Panorama is reclassified from panorama to ssl. To continue communication between Panorama and managed devices, you must modify the Security policy rule controlling traffic between Panorama and managed devices to also allow the ssl application.Skip this step if the Security policy rule controlling traffic between Panorama and managed devices allows Any application or if you already modified your Security policy rule controlling traffic between Panorama and managed devices.
- Select PoliciesSecurityPre Rules.Select Device Group containing the Security policy rule controlling traffic between Panorama and managed firewalls.Select the Security policy rule.Select Application and Add the ssl.Do not delete the panorama application. This will cause all managed firewalls to disconnect from Panorama after you push the changes.
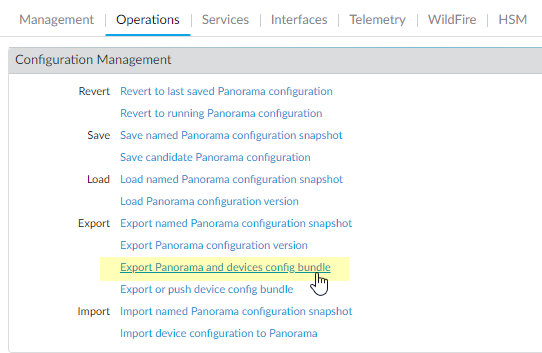
![]() Click OK.Select CommitCommit and Push and Commit and Push your configuration changes.Save a backup of the current configuration file on each managed firewall you plan to upgrade.Although the firewall automatically creates a configuration backup, it is a best practice to create and externally store a backup before you upgrade.
Click OK.Select CommitCommit and Push and Commit and Push your configuration changes.Save a backup of the current configuration file on each managed firewall you plan to upgrade.Although the firewall automatically creates a configuration backup, it is a best practice to create and externally store a backup before you upgrade.- Select PanoramaSetupOperations and click Export Panorama and devices config bundle to generate and export the latest configuration backup of Panorama and of each managed appliance.
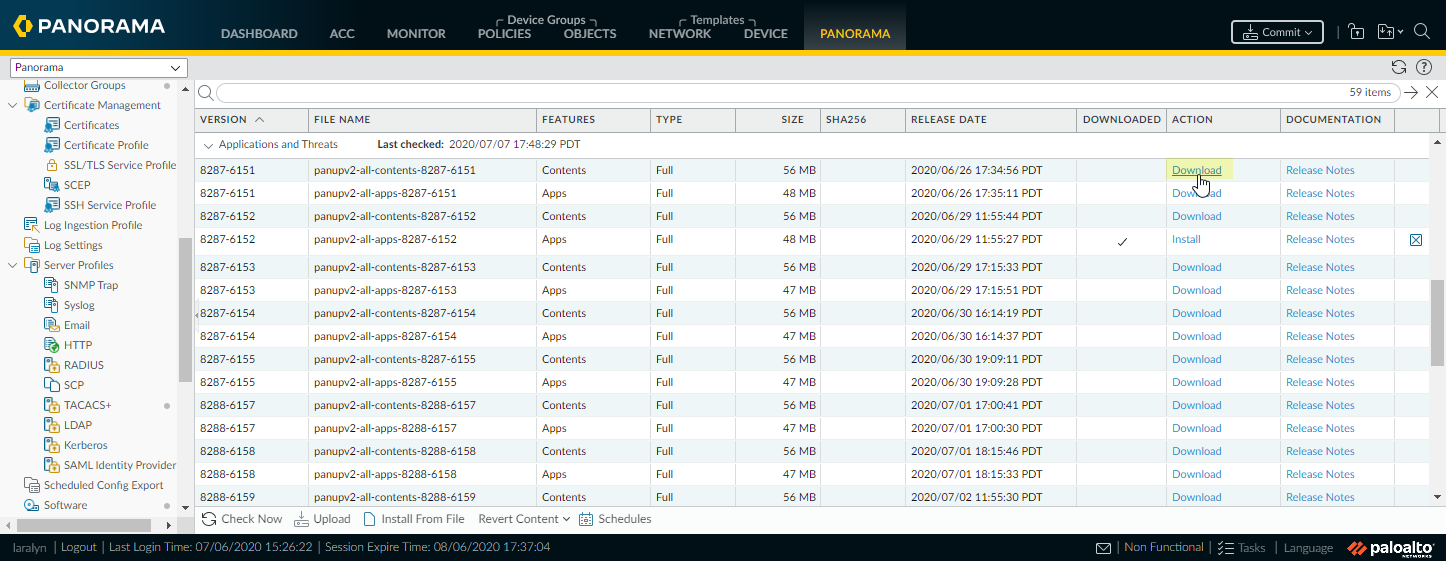
![]() Save the exported file to a location external to the firewall. You can use this backup to restore the configuration if you have problems with the upgrade.Update the content release version on the firewalls you plan to upgrade.Refer to the Release Notes for the minimum content release version required for PAN-OS 10.2. Make sure to follow the Best Practices for Applications and Threats Content Updates when deploying content updates to Panorama and managed firewalls.
Save the exported file to a location external to the firewall. You can use this backup to restore the configuration if you have problems with the upgrade.Update the content release version on the firewalls you plan to upgrade.Refer to the Release Notes for the minimum content release version required for PAN-OS 10.2. Make sure to follow the Best Practices for Applications and Threats Content Updates when deploying content updates to Panorama and managed firewalls.- Select PanoramaDevice DeploymentDynamic Updates and Check Now for the latest updates. If an update is available, the Action column displays a Download link.
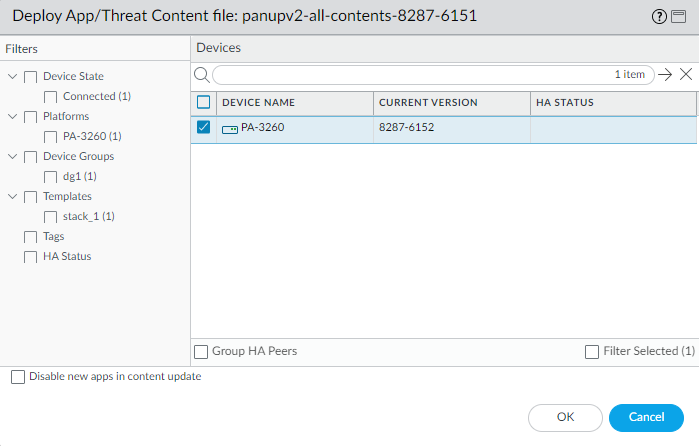
![]() If not already installed, Download the latest content release version.Click Install, select the firewalls on which you want to install the update, and click OK. If you are upgrading HA firewalls, you must update content on both peers.
If not already installed, Download the latest content release version.Click Install, select the firewalls on which you want to install the update, and click OK. If you are upgrading HA firewalls, you must update content on both peers.![]() By default, you can upload a maximum of two software or content updates of each type to a Panorama appliance and if you download a third update of the same type, Panorama will delete the update for the earliest version of that type. If you need to upload more than two software updates or content updates of a single type, use the setmax-num-images count <number> CLI command to increase the maximum.Determine the Upgrade Path to PAN-OS 10.2.You cannot skip installation of any feature release versions in the path from the currently running PAN-OS version to PAN-OS 10.2.0.Review the PAN-OS Upgrade Checklist, the known issues and changes to default behavior in the Release Notes and upgrade/downgrade considerations for each release through which you pass as part of your upgrade path.If upgrading more than one firewall, streamline the process by determining upgrade paths for all firewalls before you start downloading images.(Best Practices) If you are leveraging Strata Logging Service, install the device certificate.The firewall automatically switches to using the device certificate for authentication with Strata Logging Service ingestion and query endpoints on upgrade to PAN-OS 10.2.If you do not install the device certificate prior to upgrade to PAN-OS 10.2, the firewall continues to use the existing logging service certificates for authentication.(HA firewall upgrades only) If you will be upgrading firewalls that are part of an HA pair, disable preemption. You need only disable this setting on one firewall in each HA pair.
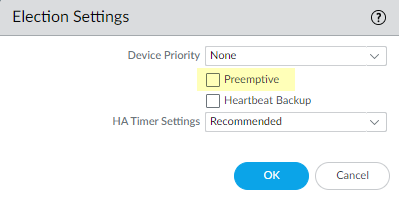
By default, you can upload a maximum of two software or content updates of each type to a Panorama appliance and if you download a third update of the same type, Panorama will delete the update for the earliest version of that type. If you need to upload more than two software updates or content updates of a single type, use the setmax-num-images count <number> CLI command to increase the maximum.Determine the Upgrade Path to PAN-OS 10.2.You cannot skip installation of any feature release versions in the path from the currently running PAN-OS version to PAN-OS 10.2.0.Review the PAN-OS Upgrade Checklist, the known issues and changes to default behavior in the Release Notes and upgrade/downgrade considerations for each release through which you pass as part of your upgrade path.If upgrading more than one firewall, streamline the process by determining upgrade paths for all firewalls before you start downloading images.(Best Practices) If you are leveraging Strata Logging Service, install the device certificate.The firewall automatically switches to using the device certificate for authentication with Strata Logging Service ingestion and query endpoints on upgrade to PAN-OS 10.2.If you do not install the device certificate prior to upgrade to PAN-OS 10.2, the firewall continues to use the existing logging service certificates for authentication.(HA firewall upgrades only) If you will be upgrading firewalls that are part of an HA pair, disable preemption. You need only disable this setting on one firewall in each HA pair.- Log in to the firewall web interface of one of the firewall HA peers.Select DeviceHigh Availability and edit the Election Settings.If enabled, disable (clear) the Preemptive setting and click OK.
![]() Commit your change. Make sure the commit is successful before you proceed with the upgrade.(HA firewall upgrades only) Suspend the primary HA peer to force a failover.(Active/passive firewalls) For firewalls in an active/passive HA configuration, suspend and upgrade the active HA peer first.(Active/active firewalls) For firewalls in an active/active HA configuration, suspend and upgrade the active-primary HA peer first.
Commit your change. Make sure the commit is successful before you proceed with the upgrade.(HA firewall upgrades only) Suspend the primary HA peer to force a failover.(Active/passive firewalls) For firewalls in an active/passive HA configuration, suspend and upgrade the active HA peer first.(Active/active firewalls) For firewalls in an active/active HA configuration, suspend and upgrade the active-primary HA peer first.- Log in to the firewall web interface of active primary firewall HA peer.Select DeviceHigh AvailabilityOperational Commands and Suspend local device for high availability.In the bottom-right corner, verify that the state is suspended.The resulting failover should cause the secondary passive HA peer to transition to active state.The resulting failover verifies that HA failover is functioning properly before you upgrade.Download the target PAN-OS 10.2.0 release image.
- Select PanoramaDevice DeploymentSoftware and Check Now for the latest release versions.Download the firewall-specific file (or files) for the release version to which you are upgrading. You must download a separate installation file for each firewall model (or firewall series) that you intend to upgrade.For example, to upgrade your PA-220 and PA-5250 firewalls to PAN-OS 10.2.0, download the PanOS_220-10.2.0, PanOS_3000-10.2.0, and PanOS_5200-10.2.0 images. After you successfully download an image, the Action column changes to Install for that image.Install the PAN-OS 10.2 software update on the firewalls.(SD-WAN only) To preserve an accurate status for your SD-WAN links, you must upgrade your hub firewalls to PAN-OS 10.2 before you upgrade your branch firewalls. Upgrading branch firewalls before hub firewalls may result in incorrect monitoring data (PanoramaSD-WANMonitoring) and for SD-WAN links to erroneously display as down.
- Click Install in the Action column that corresponds to the firewall models you want to upgrade. For example, if you want to upgrade your PA-220 firewalls, click Install in the row that corresponds to PanOS_220-10.2.0.In the Deploy Software file dialog, select all firewalls that you want to upgrade.(HA firewall upgrades only) To reduce downtime, select only one peer in each HA pair. For active/passive pairs, select the passive peer; for active/active pairs, select the active-secondary peer.(HA firewall upgrades only) Make sure Group HA Peers is not selected.Select Reboot device after install.To begin the upgrade, click OK.After the installation completes successfully, reboot using one of the following methods:
- If you are prompted to reboot, click Yes.
- If you are not prompted to reboot, select DeviceSetupOperations and Reboot Device.
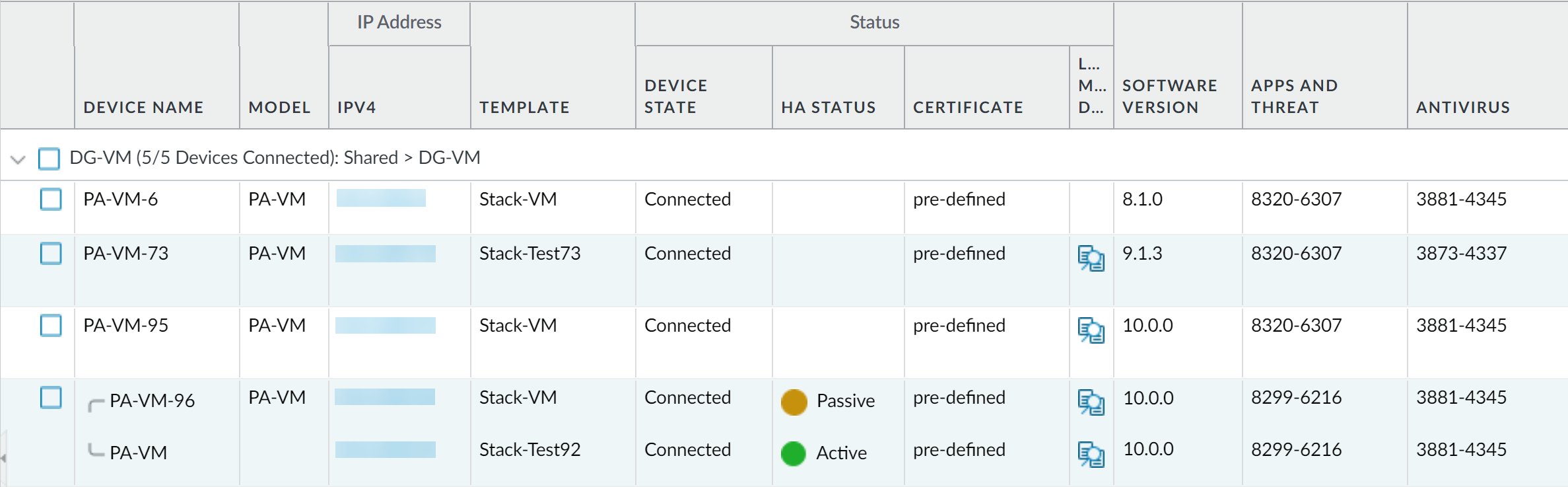
After the firewalls finish rebooting, select PanoramaManaged Devices and verify the Software Version is 10.2.0 for the firewalls you upgraded. Also verify that the HA status of any passive firewalls you upgraded is still passive.(HA firewall upgrades only) Restore HA functionality to the primary HA peer.- Log in to the firewall web interface of suspended primary firewall HA peer.Select DeviceHigh AvailabilityOperational Commands and Make local device functional for high availability.In the bottom-right corner, verify that the state is Passive. For firewalls in an active/active configuration, verify that the state is Active.Wait for the HA peer running configuration to synchronize.In the Dashboard, monitor the Running Config status in the High Availability widget.(HA firewall upgrades only) Suspend the secondary HA peer to force a failover back to the primary HA peer.
- Log in to the firewall web interface of active secondary firewall HA peer.Select DeviceHigh AvailabilityOperational Commands and Suspend local device for high availability.In the bottom-right corner, verify that the state is suspended.The resulting failover should cause the primary passive HA peer to transition to active state.The resulting failover verifies that HA failover is functioning properly before you upgrade.(HA firewall upgrades only) Upgrade the second HA peer in each HA pair.
- In the Panorama web interface, select PanoramaDevice DeploymentSoftware.Click Install in the Action column that corresponds to the firewall models of the HA pairs you are upgrading.In the Deploy Software file dialog, select all firewalls that you want to upgrade. This time, select only the peers of the HA firewalls you just upgraded.Make sure Group HA Peers is not selected.Select Reboot device after install.To begin the upgrade, click OK.After the installation completes successfully, reboot using one of the following methods:
- If you are prompted to reboot, click Yes.
- If you are not prompted to reboot, select DeviceSetupOperations and Reboot Device.
(HA firewall upgrades only) Restore HA functionality to the secondary HA peer.- Log in to the firewall web interface of suspended secondary firewall HA peer.Select DeviceHigh AvailabilityOperational Commands and Make local device functional for high availability.In the bottom-right corner, verify that the state is Passive. For firewalls in an active/active configuration, verify that the state is Active.Wait for the HA peer running configuration to synchronize.In the Dashboard, monitor the Running Config status in the High Availability widget.(FIPS-CC mode only) Upgrade Panorama and Managed Devices in FIPS-CC Mode.Upgrading a managed firewall in FIPS-CC mode requires you to reset the secure connection status if you added the Dedicated Log Collector to Panorama management while the managed firewall was running a PAN-OS 10.2 release.You do not need to re-onboard the managed firewall added to Panorama management while the managed firewall was running a PAN-OS 10.0 or earlier release.Verify the software and content release version running on each managed firewall.
- On Panorama, select PanoramaManaged Devices.Locate the firewalls and review the content and software versions in the table.For HA firewalls, you can also verify that the HA Status of each peer is as expected.
![]() (HA firewall upgrades only) If you disabled preemption on one of your HA firewalls before you upgraded, then edit the Election Settings (DeviceHigh Availability) and re-enable the Preemptive setting for that firewall and then Commit the change.On the Panorama web interface, perform a full configuration push to your managed firewalls.This step is required to enable selective commit and push of device group and template stack configuration changes from Panorama to your managed firewalls.This is required to successfully push configuration changes to multi-vsys firewalls managed by Panorama after successful upgrade to PAN-OS 10.2. For more information, see the change to default behavior for shared configuration objects for multi-vsys firewalls managed by Panorama.
(HA firewall upgrades only) If you disabled preemption on one of your HA firewalls before you upgraded, then edit the Election Settings (DeviceHigh Availability) and re-enable the Preemptive setting for that firewall and then Commit the change.On the Panorama web interface, perform a full configuration push to your managed firewalls.This step is required to enable selective commit and push of device group and template stack configuration changes from Panorama to your managed firewalls.This is required to successfully push configuration changes to multi-vsys firewalls managed by Panorama after successful upgrade to PAN-OS 10.2. For more information, see the change to default behavior for shared configuration objects for multi-vsys firewalls managed by Panorama.- Select CommitPush to Devices.Push.