Download PDF
Use Case: Monitor Applications Using Panorama
Table of Contents
11.0 (EoL)
Expand all | Collapse all
-
- Determine Panorama Log Storage Requirements
-
- Setup Prerequisites for the Panorama Virtual Appliance
- Perform Initial Configuration of the Panorama Virtual Appliance
- Set Up The Panorama Virtual Appliance as a Log Collector
- Set Up the Panorama Virtual Appliance with Local Log Collector
- Set up a Panorama Virtual Appliance in Panorama Mode
- Set up a Panorama Virtual Appliance in Management Only Mode
-
- Preserve Existing Logs When Adding Storage on Panorama Virtual Appliance in Legacy Mode
- Add a Virtual Disk to Panorama on an ESXi Server
- Add a Virtual Disk to Panorama on vCloud Air
- Add a Virtual Disk to Panorama on Alibaba Cloud
- Add a Virtual Disk to Panorama on AWS
- Add a Virtual Disk to Panorama on Azure
- Add a Virtual Disk to Panorama on Google Cloud Platform
- Add a Virtual Disk to Panorama on KVM
- Add a Virtual Disk to Panorama on Hyper-V
- Add a Virtual Disk to Panorama on Oracle Cloud Infrastructure (OCI)
- Mount the Panorama ESXi Server to an NFS Datastore
-
- Increase CPUs and Memory for Panorama on an ESXi Server
- Increase CPUs and Memory for Panorama on vCloud Air
- Increase CPUs and Memory for Panorama on Alibaba Cloud
- Increase CPUs and Memory for Panorama on AWS
- Increase CPUs and Memory for Panorama on Azure
- Increase CPUs and Memory for Panorama on Google Cloud Platform
- Increase CPUs and Memory for Panorama on KVM
- Increase CPUs and Memory for Panorama on Hyper-V
- Increase the CPUs and Memory for Panorama on Oracle Cloud Infrastructure (OCI)
- Complete the Panorama Virtual Appliance Setup
-
- Convert Your Evaluation Panorama to a Production Panorama with Local Log Collector
- Convert Your Evaluation Panorama to a Production Panorama without Local Log Collector
- Convert Your Evaluation Panorama to VM-Flex Licensing with Local Log Collector
- Convert Your Evaluation Panorama to VM-Flex Licensing without Local Log Collector
- Convert Your Production Panorama to an ELA Panorama
-
- Register Panorama
- Activate a Panorama Support License
- Activate/Retrieve a Firewall Management License when the Panorama Virtual Appliance is Internet-connected
- Activate/Retrieve a Firewall Management License when the Panorama Virtual Appliance is not Internet-connected
- Activate/Retrieve a Firewall Management License on the M-Series Appliance
- Install the Panorama Device Certificate
- Install the Device Certificate for a Dedicated Log Collector
-
- Migrate from a Panorama Virtual Appliance to an M-Series Appliance
- Migrate a Panorama Virtual Appliance to a Different Hypervisor
- Migrate from an M-Series Appliance to a Panorama Virtual Appliance
- Migrate from an M-500 Appliance to an M-700 Appliance
- Migrate from an M-600 Appliance to an M-700 Appliance
- Migrate from an M-100 Appliance to an M-500 Appliance
- Migrate from an M-100 or M-500 Appliance to an M-200 or M-600 Appliance
-
- Configure an Admin Role Profile
- Configure an Admin Role Profile for Selective Push to Managed Firewalls
- Configure an Access Domain
-
- Configure a Panorama Administrator Account
- Configure Local or External Authentication for Panorama Administrators
- Configure a Panorama Administrator with Certificate-Based Authentication for the Web Interface
- Configure an Administrator with SSH Key-Based Authentication for the CLI
- Configure RADIUS Authentication for Panorama Administrators
- Configure TACACS+ Authentication for Panorama Administrators
- Configure SAML Authentication for Panorama Administrators
- Configure Tracking of Administrator Activity
-
- Add a Firewall as a Managed Device
- Change Between Panorama Management and Cloud Management
-
- Add a Device Group
- Create a Device Group Hierarchy
- Create Objects for Use in Shared or Device Group Policy
- Revert to Inherited Object Values
- Manage Unused Shared Objects
- Manage Precedence of Inherited Objects
- Move or Clone a Policy Rule or Object to a Different Device Group
- Push a Policy Rule to a Subset of Firewalls
- Device Group Push to a Multi-VSYS Firewall
- Manage the Rule Hierarchy
- Manage the Master Key from Panorama
- Schedule a Configuration Push to Managed Firewalls
- Redistribute Data to Managed Firewalls
-
- Plan the Transition to Panorama Management
- Migrate a Firewall to Panorama Management and Reuse Existing Configuration
- Migrate a Firewall to Panorama Management and Push a New Configuration
- Migrate a Firewall HA Pair to Panorama Management and Reuse Existing Configuration
- Migrate a Firewall HA Pair to Panorama Management and Push a New Configuration
- Load a Partial Firewall Configuration into Panorama
- Localize a Panorama Pushed Configuration on a Managed Firewall
-
- Configure a Managed Collector
- Monitor Managed Collector Health Status
- Configure Log Forwarding to Panorama
- Configure Syslog Forwarding to External Destinations
- Forward Logs to Strata Logging Service
- Verify Log Forwarding to Panorama
- Modify Log Forwarding and Buffering Defaults
- Configure Log Forwarding from Panorama to External Destinations
-
- Add Standalone WildFire Appliances to Manage with Panorama
- Remove a WildFire Appliance from Panorama Management
-
-
- Configure a Cluster and Add Nodes on Panorama
- Configure General Cluster Settings on Panorama
- Remove a Cluster from Panorama Management
- Configure Appliance-to-Appliance Encryption Using Predefined Certificates Centrally on Panorama
- Configure Appliance-to-Appliance Encryption Using Custom Certificates Centrally on Panorama
- View WildFire Cluster Status Using Panorama
-
-
- Preview, Validate, or Commit Configuration Changes
- Commit Selective Configuration Changes for Managed Devices
- Push Selective Configuration Changes to Managed Devices
- Enable Automated Commit Recovery
- Compare Changes in Panorama Configurations
- Manage Locks for Restricting Configuration Changes
- Add Custom Logos to Panorama
- Use the Panorama Task Manager
- Reboot or Shut Down Panorama
- Configure Panorama Password Profiles and Complexity
-
-
- Verify Panorama Port Usage
- Resolve Zero Log Storage for a Collector Group
- Replace a Failed Disk on an M-Series Appliance
- Replace the Virtual Disk on an ESXi Server
- Replace the Virtual Disk on vCloud Air
- Migrate Logs to a New M-Series Appliance in Log Collector Mode
- Migrate Logs to a New M-Series Appliance in Panorama Mode
- Migrate Logs to a New M-Series Appliance Model in Panorama Mode in High Availability
- Migrate Logs to the Same M-Series Appliance Model in Panorama Mode in High Availability
- Migrate Log Collectors after Failure/RMA of Non-HA Panorama
- Regenerate Metadata for M-Series Appliance RAID Pairs
- View Log Query Jobs
- Troubleshoot Registration or Serial Number Errors
- Troubleshoot Reporting Errors
- Troubleshoot Device Management License Errors
- Troubleshoot Automatically Reverted Firewall Configurations
- View Task Success or Failure Status
- Generate a Stats Dump File for a Managed Firewall
- Recover Managed Device Connectivity to Panorama
- Restore an Expired Device Certificate
End-of-Life (EoL)
Use Case: Monitor Applications Using Panorama
This example takes you through the process of assessing
the efficiency of your current policies and determining where you
need to adjust them to fortify the acceptable use policies for your
network.
When you log in to Panorama, the Top Applications widget
on the Dashboard gives a preview of the most
used applications over the last hour. To display the widget, select WidgetsApplicationTop Applications in the toolbar.
You can either glance over the list of top applications and mouse
over each application block for which you want to review the details,
or you can select the ACC tab to view the
same information as an ordered list. The following image is a view
of the Top Applications widget on the Dashboard.
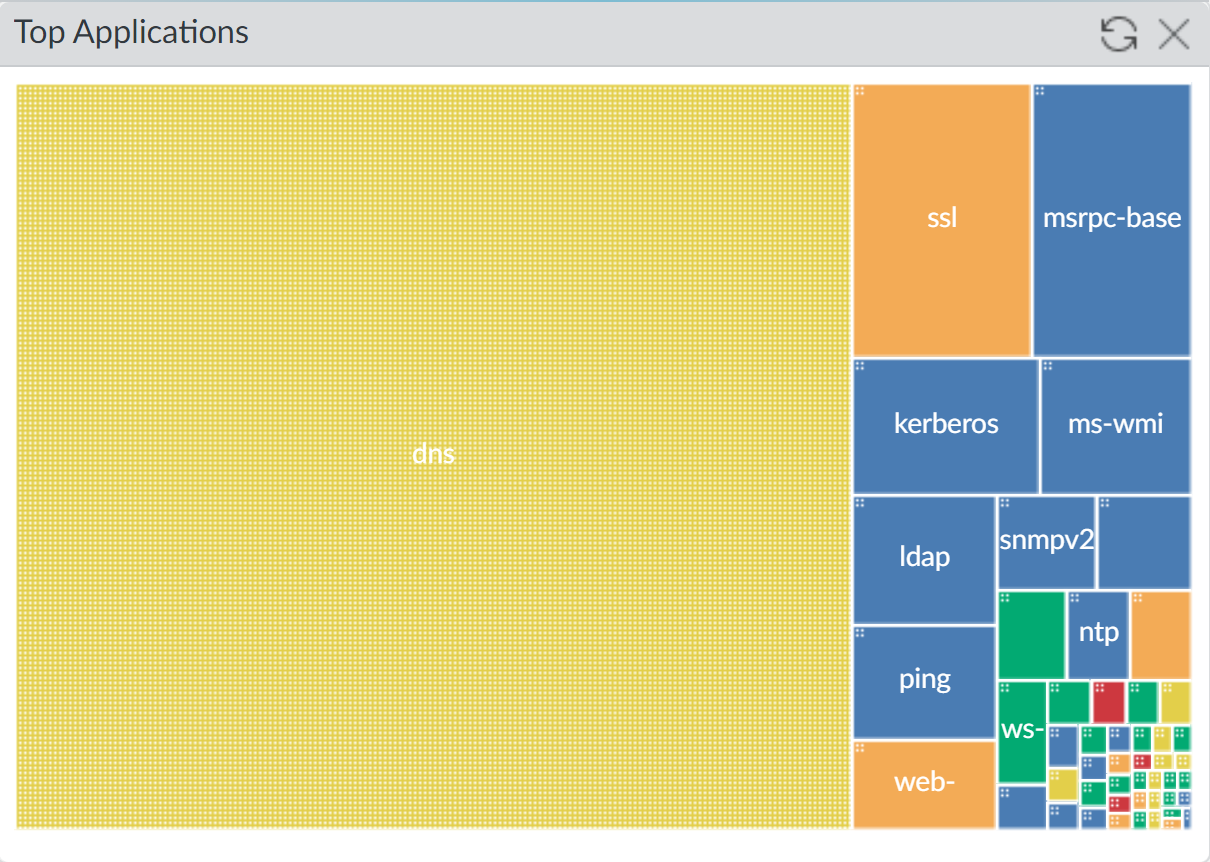
The data source for this display is the application statistics
database; it does not use the Traffic logs and is generated whether
or not you have enabled logging for security rules. This view into
the traffic on your network depicts everything that is allowed on
your network and is flowing through unblocked by any policy rules
that you have defined.
In the ACC tab, you can select and toggle
the Data Source to be local on Panorama or
you can query the managed firewalls (Remote Device Data)
for the data; Panorama automatically aggregates and displays the
information. For a speedier flow, consider using Panorama as the
data source (with log forwarding to Panorama enabled) because the
time to load data from the managed firewalls varies by the time
period for which you choose to view data and the volume of traffic
that is generated on your network. If your managed firewalls have
a combination of PAN-OS 7.0 and earlier versions, Remote
Device Data is not available.
The Dashboard example in Figure 1 shows
DNS as a popular application. If you click the DNS application block,
Panorama opens the ACCNetwork
Activity tab with DNS applied as a global filter
and shows information on the application, users who accessed the
application, and the details on the risk level and characteristics
of the application.
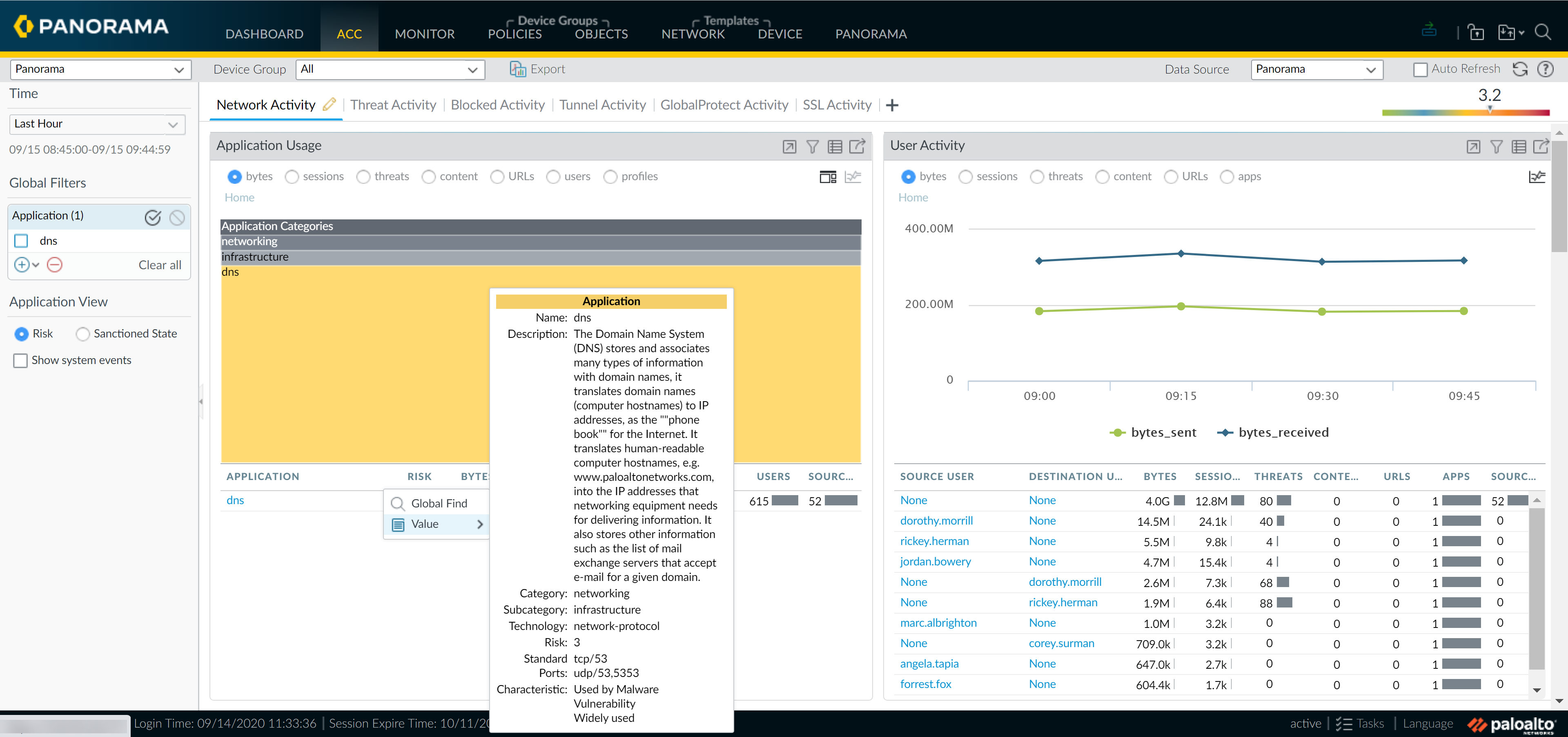
In the User Activity widget, you can see
how many users are using DNS and the volume of traffic being generated.
If you have enabled User-ID, you can view the names of the users
who are generating this traffic, and drill in to review all the
sessions, content or threats associated with each user.
In the Threat Activity tab, view the Compromised
Hosts widget to see what correlation objects were matched
on, and view the match evidence associated with the user and application.
You can also view the threat name, category and ID in the Threat
Activity widget.
With DNS set as a global filter, use the Destination
IP Activity and the Destination Regions widgets to
verify where the traffic was destined. You can also view the ingress
and egress zones and the security rule that is letting this connection
through.
For more detailed information, jump into the Traffic logs
![]() for a filtered view
and review each log entry for ports used, packets sent, bytes sent
and received. Adjust the columns to view more information or less information
based on your needs.
for a filtered view
and review each log entry for ports used, packets sent, bytes sent
and received. Adjust the columns to view more information or less information
based on your needs.
The MonitorApp-Scope >
Traffic Map tab displays a geographical map of the traffic
flow and provides a view of incoming versus outgoing traffic. You
can also use the MonitorApp-ScopeChange Monitor tab to view
changes in traffic patterns. For example, compare the top applications
used over this hour to the last week or month to determine if there
is a pattern or trend.
With all the information you have now uncovered, you can evaluate
what changes to make to your policy configurations. Here are some
suggestions to consider:
- Be restrictive and create a pre-rule on Panorama to block or allow all DNS traffic. Then use Panorama device groups to create and push this policy rule to one or more firewalls.
- Enforce bandwidth use limits and create a QoS profile and policy rule that de-prioritizes non-business traffic. Use Panorama device groups and templates to configure QoS and then push rules to one or more firewalls.
- Schedule a custom report group that pulls together the activity for the specific user and that of top applications used on your network to observe that pattern for another week or two before taking action.
Besides checking for a specific application, you can also check
for any unknown applications in the list of top applications. These
are applications that did not match a defined App-ID™ signature
and display as unknown-udp and unknown-tcp. To delve into these
unknown applications, click on the name to drill down to the details
for the unclassified traffic.
Use the same process to investigate the top source IP addresses
of the hosts that initiated the unknown traffic along with the IP
address of the destination host to which the session was established.
For unknown traffic, the traffic logs, by default, perform a packet
capture (pcap) when an unknown application is detected. The green
arrow in the left column represents the packet capture snippet of
the application data. Clicking on the green arrow displays the pcap
in the browser.
Having the IP addresses of the servers (destination IP), the
destination port, and the packet captures, you will be better positioned
to identify the application and make a decision on how you would
like to take action on your network. For example, you can create
a custom application that identifies this traffic instead of labeling
it as unknown TCP or UDP traffic. Refer to the article Identifying Unknown Applications for
more information on identifying unknown application and Custom Application Signatures for
information on developing custom signatures to discern the application.
