SaaS Security
User Activity Policies
Table of Contents
Expand All
|
Collapse All
SaaS Security Docs
User Activity Policies
Learn about the benefits of user activity policies on Data Security.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Data Security license:
|
In addition to data patterns, you can add user activity policies on Data Security for comprehensive coverage. Similar to data asset policies, user activity policies
include a robust set of match criteria that enable you to precisely define which user
activities are threats to your organization. Data Security also provides
predefined user activity policies for detecting suspicious user activity.
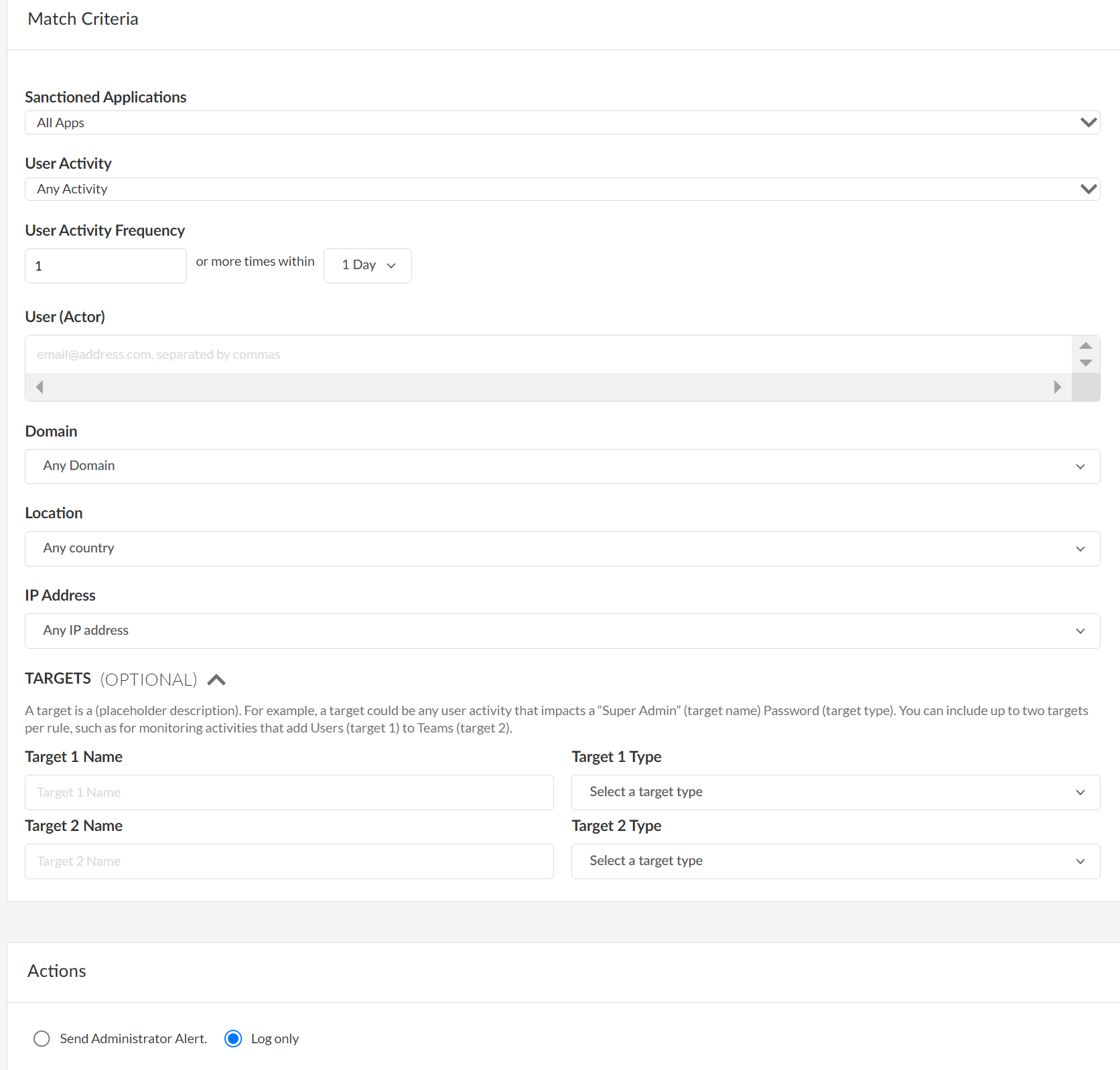
Match Criteria for User Activity Policies
Learn about the match criteria available for user activity policies on Data Security.
When you create a user activity policy, you need to specify match
criteria. The following table lists the match criteria for user activity policies on Data Security.
Match Criteria | Description |
|---|---|
|
Sanctioned Applications
|
List of accessible applications to scan. By default, all cloud apps
you added to Data Security are scanned, but you can
restrict scans to specific apps.
|
|
User Activity
|
List of activities to monitor. For example, activities can include
Create,
Download,Edit,
Delete, Authorize,
Upload, Join, or
more. You can include multiple activities in a policy.
|
User Activity Frequency | The count and frequency of the activity
that will trigger a policy violation. For example, ten (or more)
times a week, or two (or more) times per day. |
User (Actor) | Users whose perform the activities. By default,
all users in all domains are included. Alternatively, you can:
|
|
Domain
|
The domain where the activity occurs. Choices include:
|
Location | The location where the activity occurs.
Choices include:
You can choose a maximum of 28 countries
from the given list. |
IP Address | The IP address where the activity was initiated.
Choices include:
Use
commas to separate multiple IP addresses. |
|
TARGETS (OPTIONAL)
|
The Name and Type of
target for the user activity. For example, a target could be any
user activity that impacts a Super Admin
(target name) Password (target type). Or, any
user activity associated with a Client List
(target name) Report (target type).
You can Add a Target to include multiple
targets in a policy. For example, activities that add
Users (target) to
Teams (target), or activities that share
Links (target) with
Users (target) would include two targets
in the policy.
Folder alerts you
when the user activity occurs on any file contained in the folder.
Folder File alerts you when there is user
activity on the specific file defined in the
Name. The targets available depend on your SaaS
app. If a specific target does not display in
Explore >
Activities, then the event isn't
supported for your SaaS app and, therefore, you can't define it in a
policy. |
Predefined Policies to Detect Suspicious User Activity
Learn about the predefined policies that you can use
to detect suspicious user activities.
Policies for detecting suspicious user activity are now
included in the Behavior Threats feature of SaaS
Security. Specifically, the predefined policies in Data Security are now
available as static policies in Behavior Threats. The
following predefined policies mentioned in this section will not be available for newly
provisioned tenants from May 30, 2025. By transitioning to the new Behavior Threats
policies, you ensure continued functionality and access to the latest features. See the
LIVEcommunity blog for a detailed explanation
of this transition.
Data Security provides predefined policies
for detecting suspicious user activity. These activities might indicate
attempts to steal or destroy data, or might indicate attempts to
breach a user's account. These predefined policies are Disabled by
default, but you can Enable them from the
User Activities Policies page ( Data SecurityPoliciesUser Activity Policies).
If a Suspicious User Activity policy is enabled, violations of
the policy are logged as incidents.
From the User Activity Policies page, you can edit the severity
of a policy, but you cannot edit its match criteria. If you want
to trigger policy violations based on different criteria, such as
a different event count or frequency, contact customer support.
The following predefined policies are available.
| Predefined Policy Name | Description |
|---|---|
| Bulk Deletion | Detects that a user deleted a large number
of files or folders within a short time frame. Bulk deletion might
be a malicious attempt to cause data loss. Data Security
triggers a violation of this policy if a user deletes more than
20 unique files or folders within an hour. |
| Bulk Download | Detects that a user downloaded a large number
of distinct files or folders within a short time frame. Bulk downloads
might be an attempt to compromise your organization’s sensitive
data. Data Security triggers a violation of this policy
if a user downloads more than 20 unique files or folders within
an hour. |
| Bulk Sharing | Detects that a user shared a large number
of distinct files or folders within a short time frame. Bulk sharing
might be an attempt to compromise your organization’s sensitive data. Data Security triggers a violation of this policy if a user shares
more than 20 unique files or folders within an hour. |
| Bulk Upload | Detects that a user uploaded a large number
of distinct files or folders within a short time frame. Bulk uploads
might be an attempt to compromise your organization’s sensitive data. Data Security triggers a violation of this policy if a user uploads
more than 20 unique files or folders within an hour. |
| Impossible Traveler | Detects that a user accessed an application
from different locations within a time frame that could not accommodate
travel between the locations. The locations are determined by IP
addresses. This impossible travel might indicate that the user’s
account is compromised. |
| Inactive Account Access | Detects that a user accessed an application
by using an inactive account. An account is considered inactive
if it was not accessed in over 30 days. Inactive account access
might indicate that the user’s account was breached. |
| Login Failure | Detects multiple failed login attempts to an
application by a user. Multiple login failures might indicate an
attempt to breach the user account. Data Security triggers
a violation of this policy if there are more than 5 consecutive failed
login attempts within 30 minutes. |
| Malware | Detects user activity on a file that contains
malware. This activity might identify a malicious user and is a
threat to your organization. |
| Risky IPs | Detects that a user accessed an application
from a suspicious IP address. Suspicious IP addresses include malicious
IP addresses identified by Unit 42, the Palo Alto Networks threat
intelligence team. Suspicious IP addresses also include IP addresses
of known Tor exit nodes and IP addresses belonging to Bulletproof
Hosting Providers (BHPs). Access from a risky IP address likely indicates
that the user’s account was breached. |
| Unsafe Location | Detects that a user accessed an application
from a country that the United States Department of the Treasury
considers unsafe. These countries are considered unsafe because
they are known origins of cyberattacks. User access from an unsafe location
likely indicates that the user’s account was breached. |
| Unsafe VPN | Detects that a user accessed an application
from an unauthorized or unsanctioned VPN. These unsafe VPNs include personal
VPNs and known consumer VPNs. The use of an unsafe VPN might indicate
that the user is hiding their IP address to avoid auditing and tracking.
The use of an unsafe VPN might also indicate that a malicious actor
is attempting to decrypt traffic to steal user credentials. |
Examples of User Activity Policies
Examples of user activity policies on Data Security.
The following are some examples of how to configure user activity rules.
Objective | Criteria | Value |
|---|---|---|
Send an alert if any user downloads more
than 500 files in a day. | Activity Count or Frequency Target
Type Action | Download 500, 1 day File Send
Admin Alert |
Send an alert for failed logins on Salesforce. | Activity Cloud Apps Action | Failed Login Salesforce Send
Admin Alert |
Log any activity from a malicious IP address. | Activity IP Address Action | Any Activity 127.31.52.12 Log
only |
Send an alert if a user outside of paloaltonetworks.com
uploads an executable file. | Activity Domain Target Name Target Type Action | Upload Any Domain Except paloaltonetworks.com *.exe File Send
Admin Alert |
Log an activity when users change their
passwords. | Activity Target Type Action | Edit Password Log only |
Add a New User Activity Policy
Learn how to create a new user activity policy to monitor user and administrator
activity.
User activity policies enable activity logging and activity alerting, depending on
the user activity support for the specific SaaS app. You can track user activities that
compromise your organization. You can create a policy that sends email alerts or
creates an activity monitoring log entry when a user downloads a large
number of reports, or when a user tries to access a SaaS app from a malicious IP
address. There are numerous other examples that warrant activity
monitoring.
- Log in to Strata Cloud Manager.Select ConfigurationSaaS SecurityData SecurityPoliciesUser Activity PoliciesAdd Policy.Define the basic settings.
- Enter a Name for the policy.(Optional) Enter a Description for the policy.Specify a Severity for the policy ranging from Very Low, Low, Medium, High, and Critical..Verify that the Status is Enabled. A policy can be in the enabled or disabled state. After you add a new policy, you must enable the policy.Specify the Items to Detect.
- Select one of the following:
- Users—Applies the policy to users.
- Assets—Applies the policy to assets such as files or folders.
(Optional) Manage Exceptions for the policy. Enter the users or assets you want to exclude from the policy. For example, you might want to exclude Data Security administrators from user activity monitoring.Specify the match criteria for the activity.Specify the Action that you want Data Security to take:- Log Only (default)—For activity logging purposes, log the policy violation.
- Log and Send administrator alert—For activity alerting purposes, send an email for policy violations that require immediate action by one or more administrators. Data Security can send up to five emails per hour on matches against each policy.
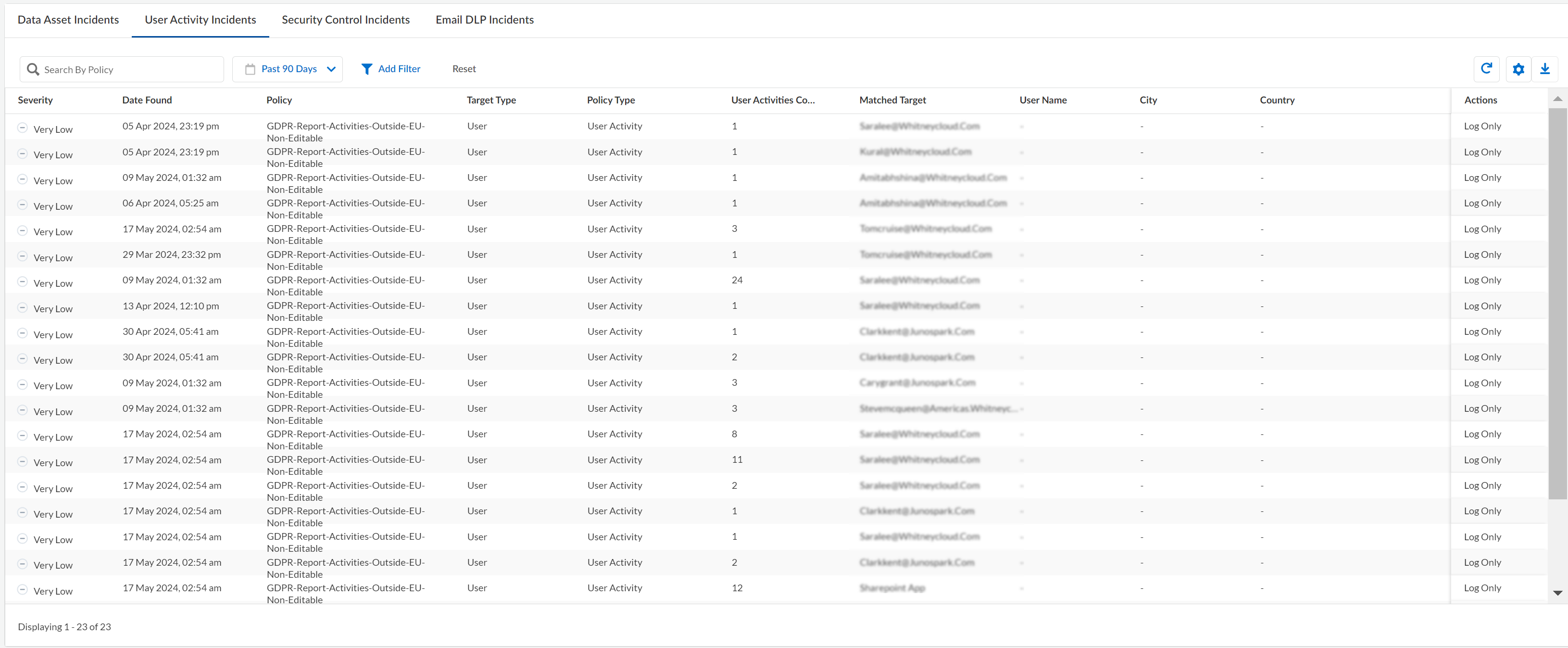
Save your new policy.Save Policy to create your new User Activity policy.Data Security starts scanning files against the policy as soon as you save the changes. After the scan starts, you can start View Policy Violations for User Activity.View Policy Violations for User Activity
Learn how to view policy violations for user and administrator activities on Data Security.Data Security starts scanning files and matching them against enabled user activity rules as soon as you save a new policy or modify an existing policy. The default action is to generate a log when a policy violation occurs but if you enabled email alerts for high-risk issues, you will also receive an automatic email notification. To view policy violations for user activities, select ConfigurationSaaS SecurityData SecurityIncidentsUser Activity Incidents. If no known violations for user activity policies display, consider that activity monitoring for some cloud apps depends on user activity requirements.![]()