SaaS Security
Microsoft Purview Information Protection Labeling for Office 365
Table of Contents
Expand All
|
Collapse All
SaaS Security Docs
Microsoft Purview Information Protection Labeling for Office 365
Learn how to configure Microsoft Purview Information Protection labels for Office 365
in Data Security.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Data Security license:
|
Data Security supports Microsoft Purview Information Protection
Labeling for Office 365 connectors. As an Administrator you can define
rules and Data Security applies labels to your files accordingly, thus
classifying and protecting your sensitive information. Labeling is supported for the
following file types:
- .docs
- .docm
- .xlsx
- .xlsm
- .xlsb
- .pptx
- .ppsx
- .pdf (enable now)
Configure Microsoft Purview Information Protection Labeling
Prerequisite: Create and Publish Sensitivity
Labels
Data Security will need permissions to fetch the labels
available in the M365 instance and their priorities. To grant permissions,
perform the following steps.
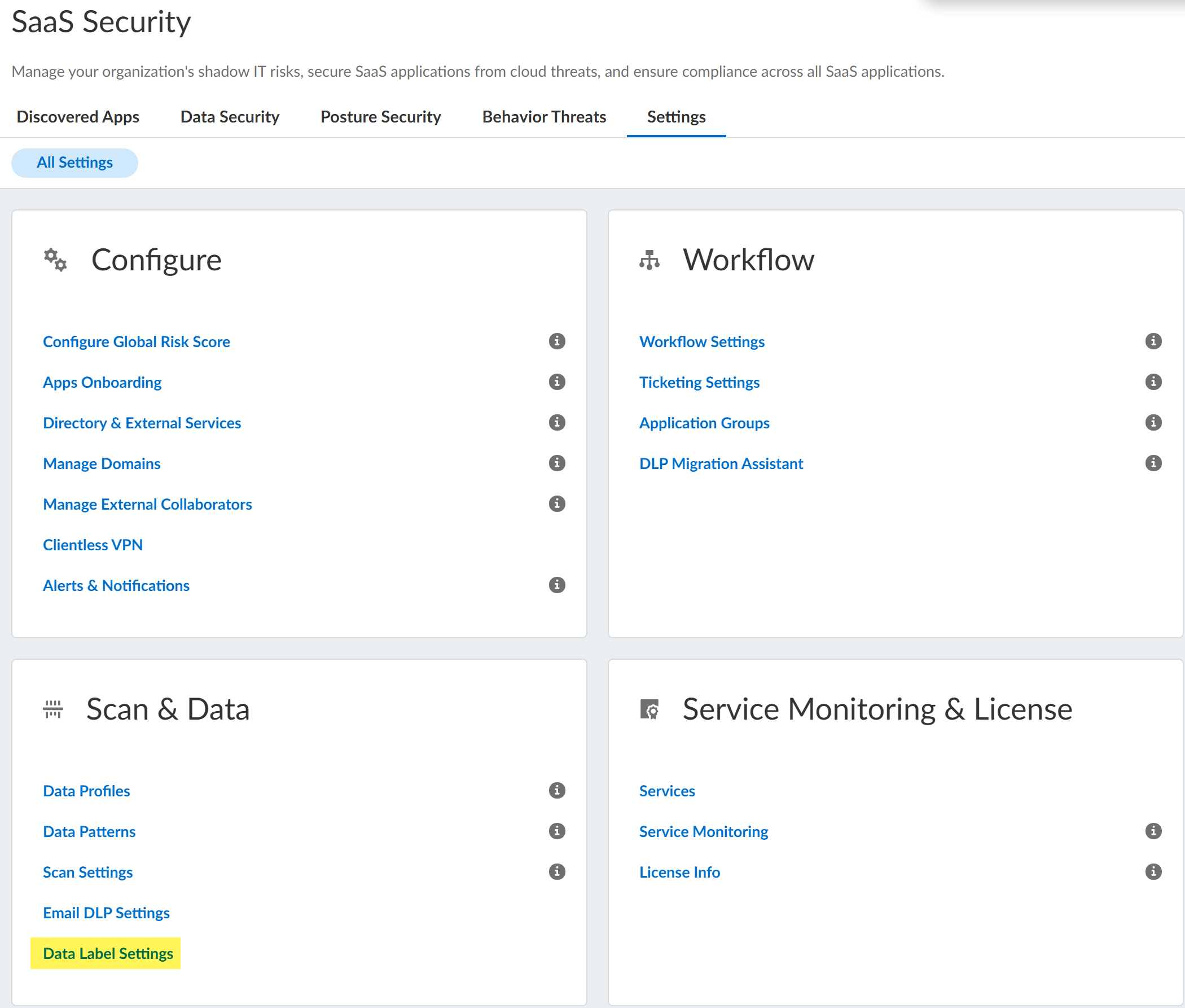
- Log in to Strata Cloud Manager.Select ConfigurationSaaS SecuritySaaS SecuritySettingsData Label Settings. The Office 365 instances which support data labeling are listed.
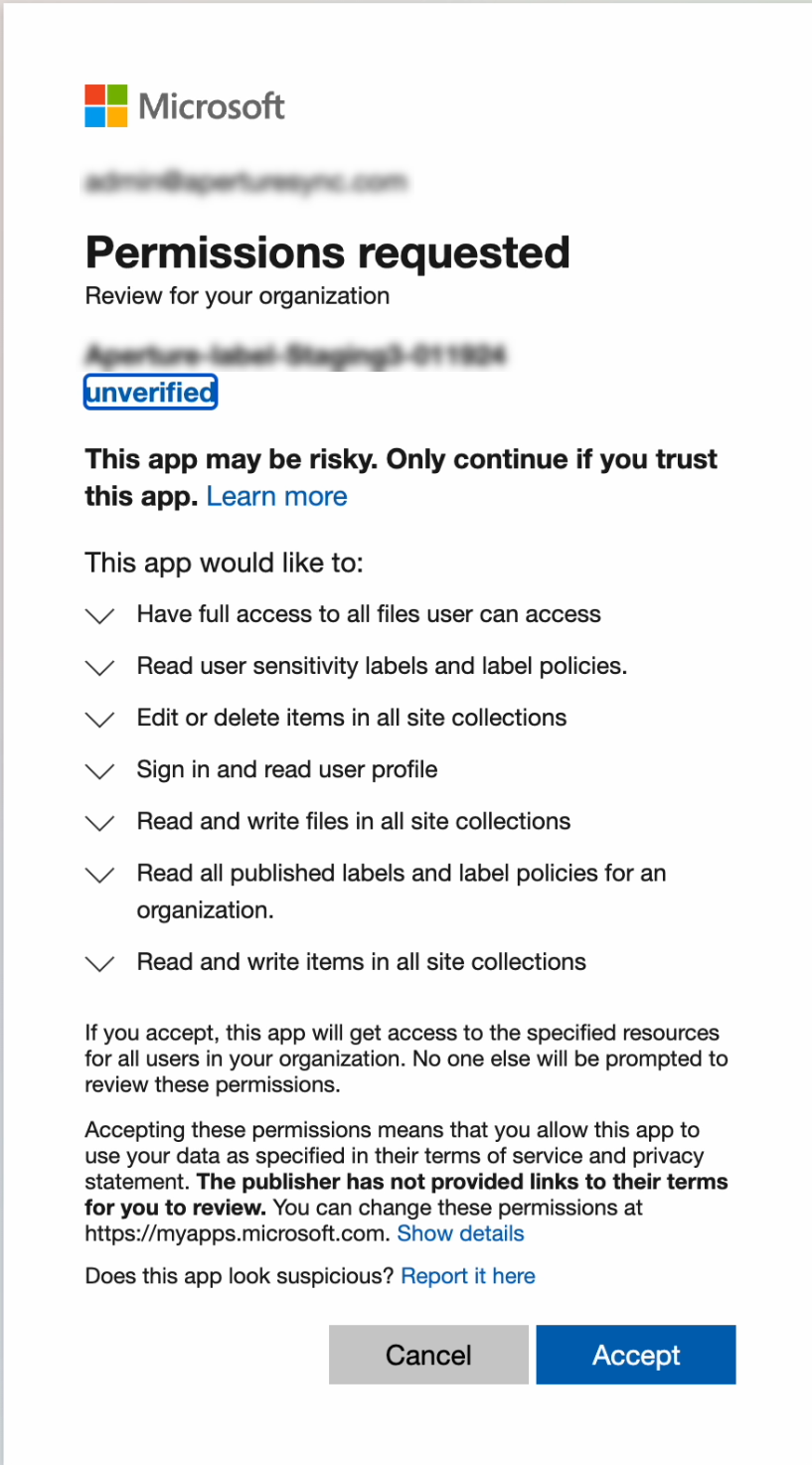
![]() If you have not fetched data labels for an existing onboarded Office 365 connector, choose your Office 365 connector instance and Authorize to fetch their labels.
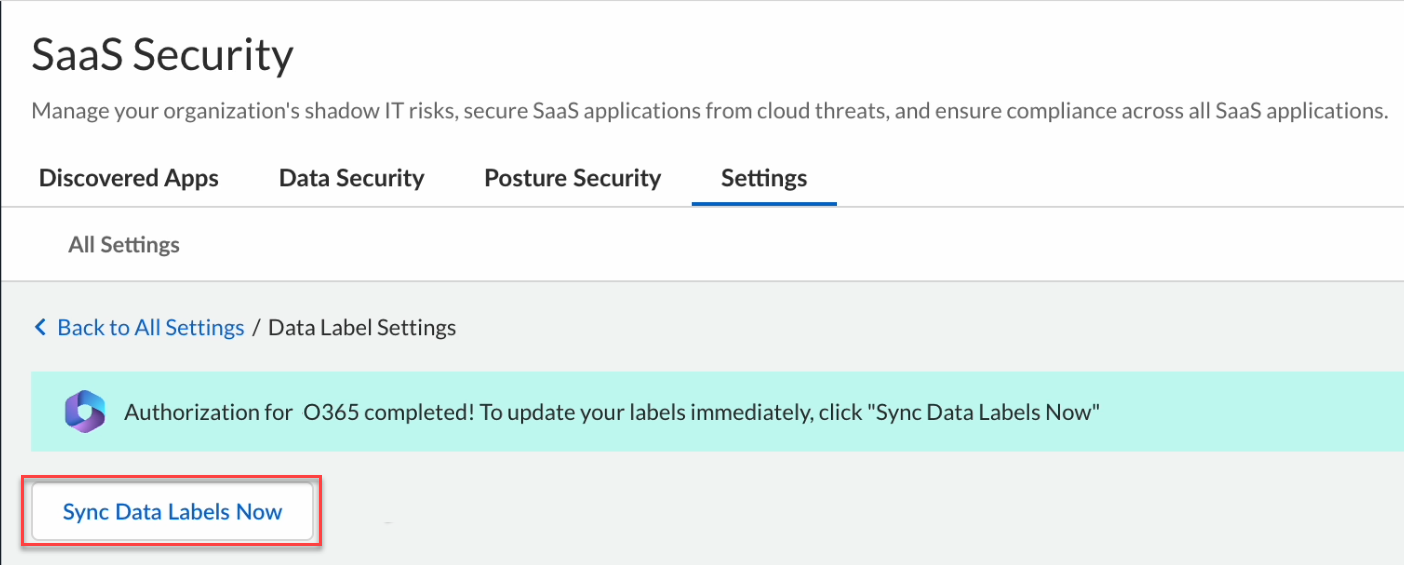
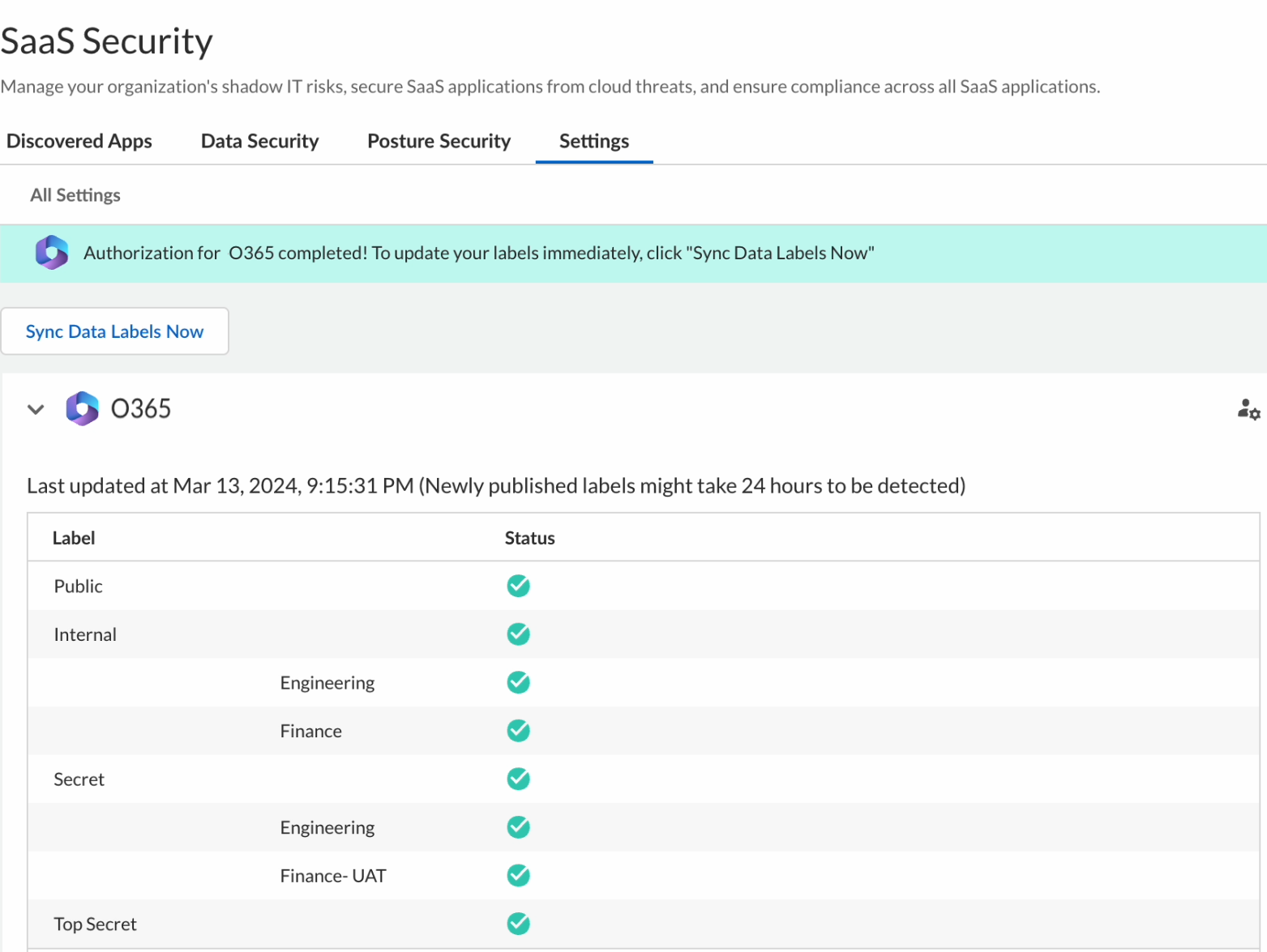
If you have not fetched data labels for an existing onboarded Office 365 connector, choose your Office 365 connector instance and Authorize to fetch their labels.![]() After authorization, the labels are fetched for the Office 365 connector immediately. Labels are refreshed every 24 hours. To fetch labels at any point in time, click Sync Data Labels Now.
After authorization, the labels are fetched for the Office 365 connector immediately. Labels are refreshed every 24 hours. To fetch labels at any point in time, click Sync Data Labels Now.![]()
![]()
Apply Labeling with Data Asset Policies
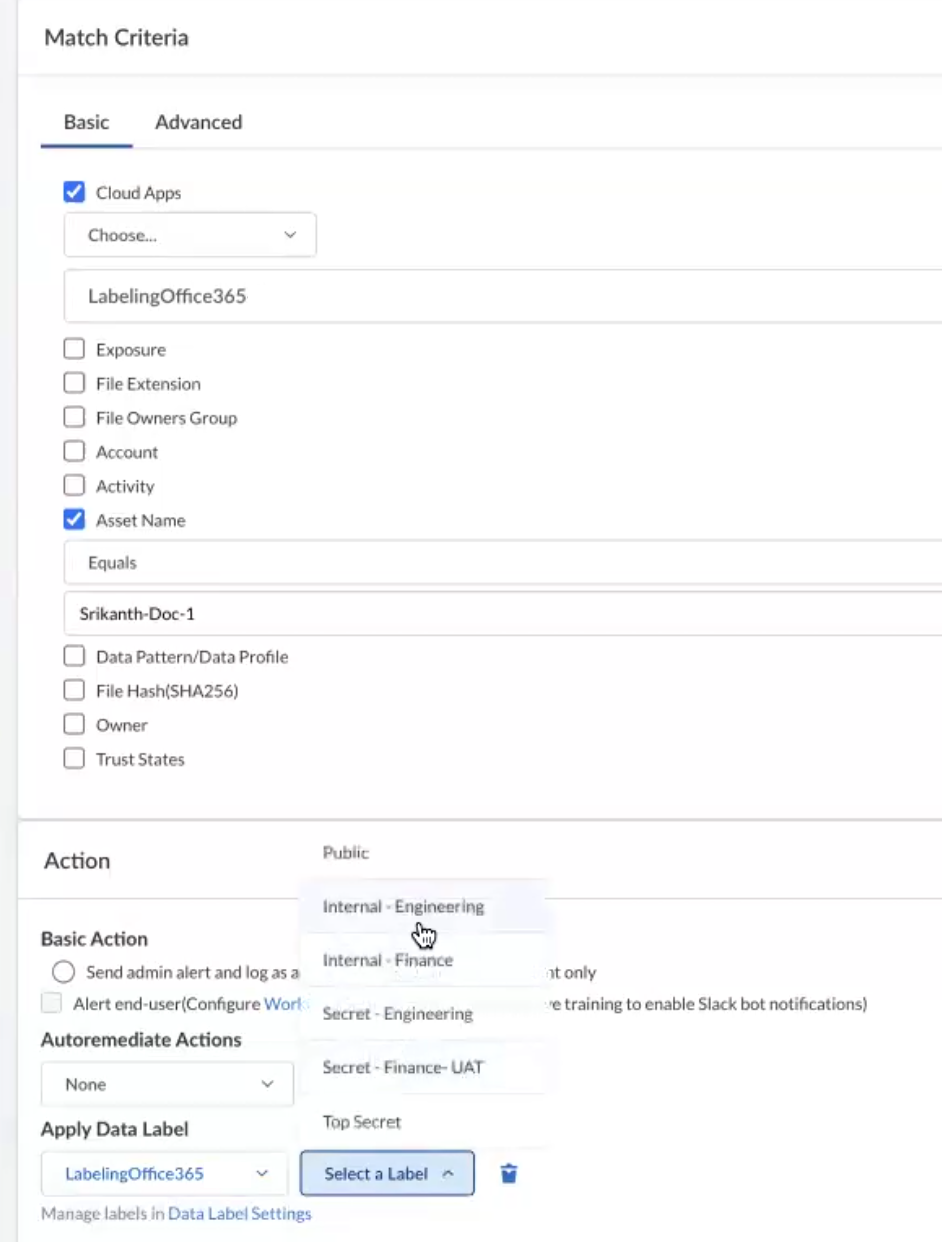
Perform the following steps to apply labeling with Data Asset Policies.- Select ConfigurationSaaS SecurityData SecurityPoliciesAdd Policy. In the Add Data Asset Policies page, scroll down to Apply Data Label under the Action section.Choose the Office 365 connector instance and the required label from the drop-down list.
![]()
- When a sensitive label has encryption settings enabled, you cannot apply that specific sensitivity label through APIs. Learn more about how to apply sensitivity labels to your files.
- When you configure a policy, you cannot choose to quarantine and label at the same time.
How Policy Driven Labeling Applies Labels
Once data asset policies are created to apply labels, Data Security will regularly scan assets (of the right file types) that match the policy’s criterion and attempt to apply the label. Labels are only applied if the policy driven label has a higher priority than the label currently on the asset.For example, if an asset has the Top Secret (the highest priority) label and a matching policy needs to apply the Confidential (which has lower priority than Top Secret) label, the policy will not attempt to apply the label. This will also apply when multiple policies match the asset. Eventually, the rule with the highest priority label will get applied.Data Security applies labels by invoking Microsoft Graph API. This applies the label asynchronously on the asset. So, there might be a lag between the moment Data Security applying the label and the label actually reflecting on the file in Office 365.View and Override Labels
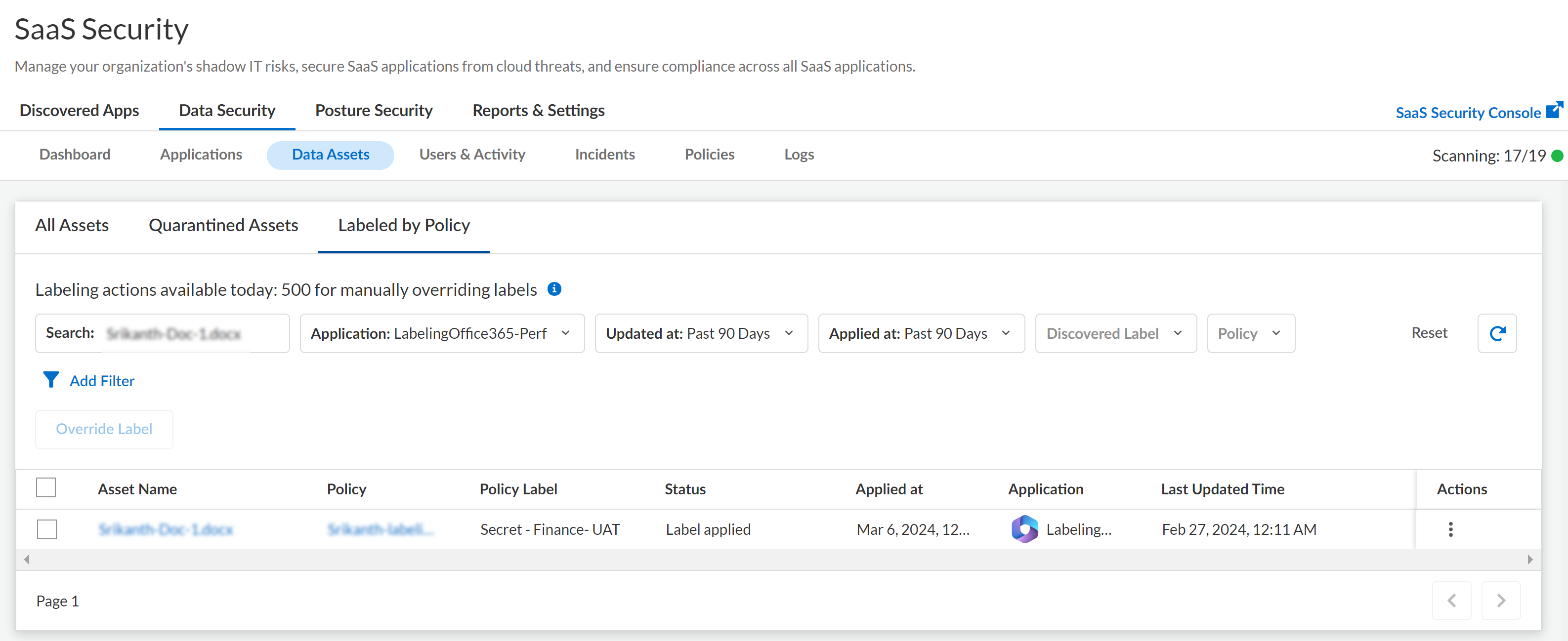
- Select ConfigurationSaaS SecurityData SecurityData AssetsLabeled by Policy. Use the various filters available at the top of the table to filter your results. As an example, the following screen shot shows a specific asset in a specific instance of Office 365.
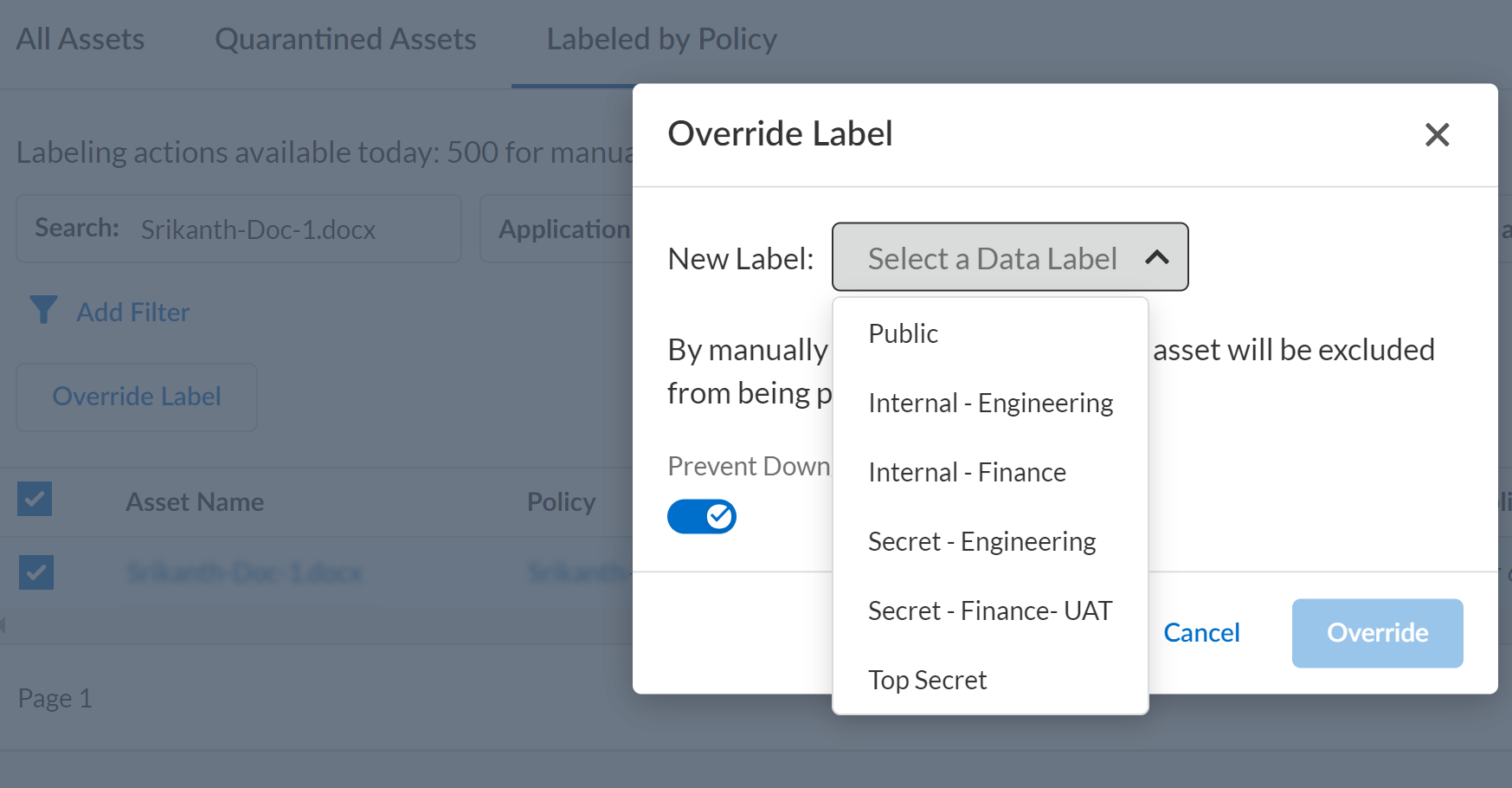
![]() To override an existing label, select the asset and override with a different label.
To override an existing label, select the asset and override with a different label.![]()
- If you override the labels manually for an asset, those assets will not be labeled by Data Asset Policies in the future.
- Select the Prevent Downgrade option to prevent users from downgrading the asset to a lower priority labeling.
Quotas for Labeling
LicensesRecent Files (< 24 Hours)Older Files (> 24 hours)All customers25000 labels per day5000 labels per dayImportant Things to Remember- Labels are available only for Office 365 connectors which have been onboarded.
- Manual overriding of labeling is limited to 500 per day.
- Files less than 24 hours old (file content change or label change) are prioritized and allocated to the Recent Files quota while files older than 24 hours are allocated to the Older Files quota.
- If the number of files to be labeled are more than your daily quota, those extra files are added to the backlog. However, these extra files are allocated to the Older Files category.