Prisma Access
App Acceleration in Prisma Access
Table of Contents
Expand All
|
Collapse All
Prisma Access Docs
-
- Prisma Access China
- 4.0 & Later
- 3.2 Preferred and Innovation
- 3.1 Preferred and Innovation
- 3.0 Preferred and Innovation
- 2.2 Preferred
-
-
-
- 5.1 Preferred and Innovation
- 5.0 Preferred and Innovation
- 4.2 Preferred
- 4.1 Preferred
- 4.0 Preferred
- 3.2 Preferred and Innovation
- 3.1 Preferred and Innovation
- 3.0 Preferred and Innovation
- 2.2 Preferred
App Acceleration in Prisma Access
Prisma Access
Learn how
Prisma Access
can speed up app performance using App
Acceleration.Where Can I Use
This? | What Do I Need? |
|---|---|
|
|
App Acceleration directly addresses the causes of poor app performance and
acts in real-time to mitigate them, dramatically improving the user experience for
Prisma Access
GlobalProtect and Remote Network users.The primary causes of poor user experience when accessing apps are dynamic content
(content that must be processed for each user individually, on-demand) and network
connectivity issues.
App Acceleration provides you with the following functionality:
Acceleration for top SaaS apps
—App
Acceleration for Prisma SASE accelerates dynamic content to improve the response
time of top SaaS apps. It securely and intelligently prepares the dynamic content
that each user needs, before the user requests it. As a result, App Acceleration dramatically
reduces the response time of applications and the APIs powering them to improve the
user experience and boost productivity.
Accelerated applications are
listed in the Supported Apps section.
Network Acceleration
—When your users access apps, they can experience poor app
performance that is caused by decreased throughput, which could be caused by packet
loss, degraded wireless connectivity, network congestion, and other factors. These
networking issues can adversely affect the employee experience and reduce their
productivity. When the internet was conceived, networks were homogenous and wireless
connectivity was in its infancy. Fundamental protocols like TCP were originally
created for these networks. Today, networks are no longer homogenous and wireless
connectivity creates a highly variable user experience. When users experience
degraded network conditions, TCP can't differentiate if the problem occurred because
of device limitations, network limitations, or physical constraints.
Without requiring any changes to your client configuration or applications, App
Acceleration securely builds an understanding of the:
- Device capability—The type of client endpoint
- Network capability—The type of network
- App Context— The type of app being used
Using its understanding of device, network and application context, App
Acceleration maximizes throughput and adjusts in real-time to account for changing
network conditions.
When compared to direct internet access, App Acceleration offers a marked throughput
improvement for TCP traffic when connecting through
Prisma Access
. You can view throughput improvements from App Acceleration in Prisma SASE
Incidents and Alerts. AI-powered Autonomous DEM (ADEM)
integrates with App Acceleration and provides you with metrics such as the number of
applications that were accelerated and the performance boost gained overall.
App Acceleration Requirements and Guidelines
When configuring App Acceleration, make a note of the
following guidelines and requirements:
- Supported Apps—App Acceleration supports the following apps:
- AWS S3
- Azure Storage
- Box
- Google Drive
- Microsoft OneDrive
- Salesforce
- SAP Ariba
- ServiceNow
- Slack (file downloads)
- Zoom (file downloads from chat, recording downloads)
- Supported Locations—App Acceleration is available for allPrisma Accesslocations except for the following locations:
- Trusted Root CA Upload—You need to set up a trusted Root CA and perform a commit and push operation and then select it during App Acceleration setup, as shown in the following procedures. If usingStrata Cloud Managerto configure App Acceleration, set up the Root CA in thePrisma Accessscope. If you change the certificate you use, you must also commit and push the changed certificate before you select it.
- Forward Trust Certificate and Trusted Root CA—Enable the CA/certificate you uploaded as a forward trust certificate and trusted root CA, as shown in the following procedures. If SSL decryption is applied to any accelerated apps, you must mark the certificate as a forward trust certificate and trusted root CA, or users will encounter SSL errors when trying to access those apps.
- QUIC Protocol Support—Some browsers (such as Google Chrome) may use the Quick UDP Internet Connections (QUIC) protocol by default. Layer 7 app acceleration can't be used on traffic using QUIC. As a workaround, disable the QUIC protocol when you configure App Acceleration.
- —Users connecting to Prisma Access deployments that have App Acceleration enabled for top SaaS apps can expect to see response headers with a name of Zy-*, such as Zy-Server and Zy-Accelerated, and a zy_sid session cookie.SaaS Apps and Zy-* Response HeadersIf the response header is Zy-Accelerated, a value of1indicates that the response was accelerated and a value of0indicates the response was not accelerated.
- Content Localization—If an accelerated SaaS app localizes content based solely on the user's IP address or user ID, when acceleration is enabled for that app, its content will not be localized.
- Unsupported—The following functionality does not support App Acceleration andPrisma AccessFunctionalityPrisma Accessdeployments with these features enabled will not be accelerated:
- Remote Networks that use Overlapped Subnets (supported by default inPrisma Access (Managed by Strata Cloud Manager)deployments, configurable inPrisma Access (Managed by Panorama)deployments.
Configure App Acceleration
To configure App Acceleration in Prisma Access, select one of the following tabs
depending on your deployment (
Prisma Access (Managed by Strata Cloud Manager)
or Prisma Access (Managed by Panorama)
). Configure App Acceleration in Prisma Access (Strata Cloud Manager)
Prisma Access
(Strata Cloud Manager
)Configure App Acceleration in a
Prisma Access (Managed by Strata Cloud Manager)
deployment. To configure App Acceleration in a
Prisma Access (Managed by Strata Cloud Manager)
deployment, complete this
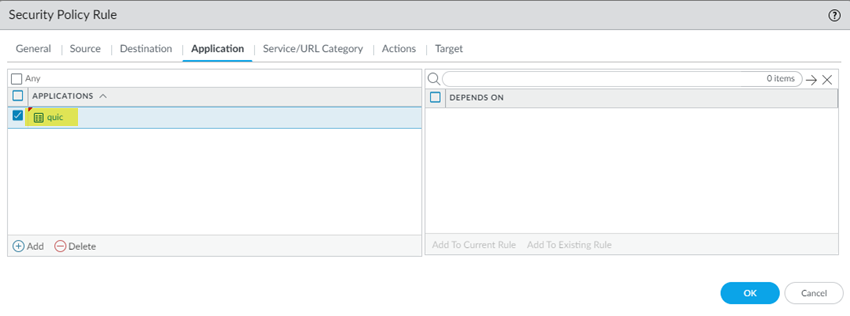
task.- (Optional) Disable the Quick UDP Internet Connections (QUIC) protocol.App Acceleration cannot accelerate apps at Layer 7 without disabling QUIC.
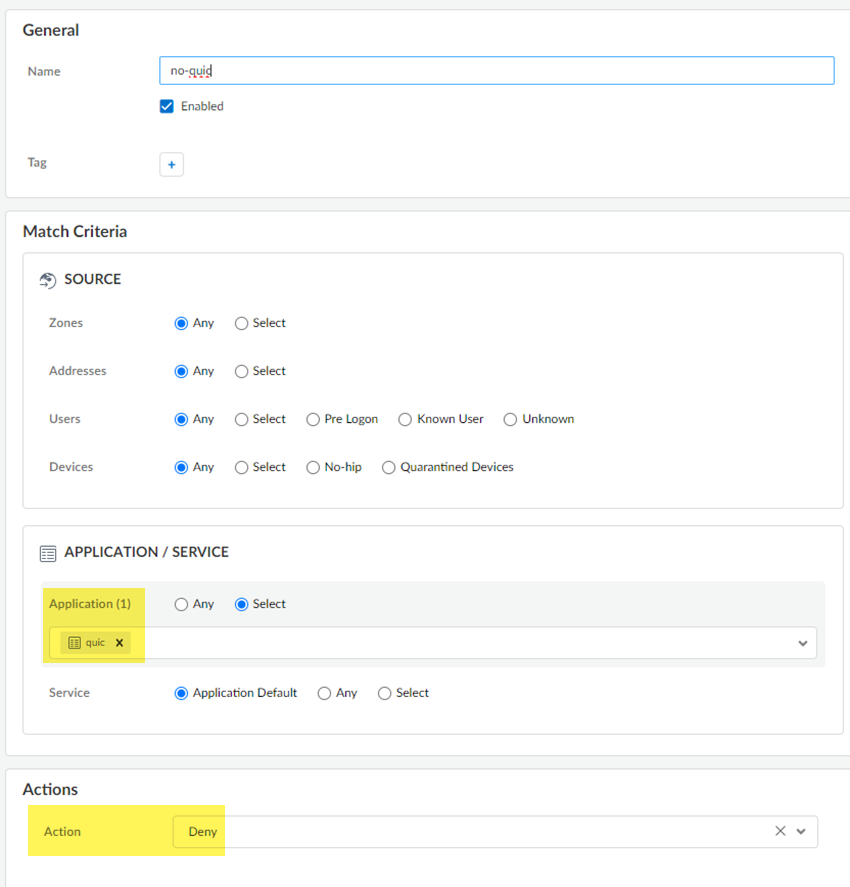
- Go toandManageConfigurationNGFW & Prisma AccessSecurity ServicesSecurity Policy.Add RulePre RulesCreate this Security policy rule in theGlobalconfiguration scope.
- Select anApplication / Serviceofquicand anActionsofDrop.
![]()
- Saveyour changes.
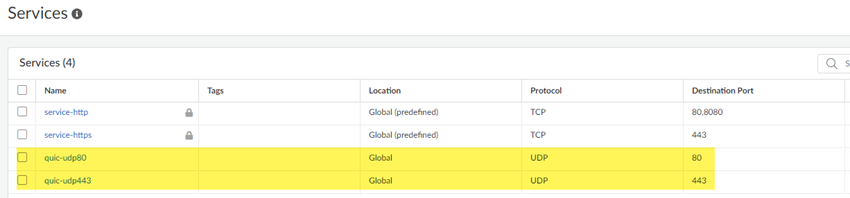
- Go toandManageConfigurationNGFW & Prisma AccessObjectsServicesServiceAddservices for UDP port 80 and UDP port 443.Palo Alto Networks recommends adding services for UDP port 80 and UDP port 443 and creating an additional security policy to block UDP traffic on those ports, because newer versions of QUIC might be misidentified asunknown-udp.
![]()
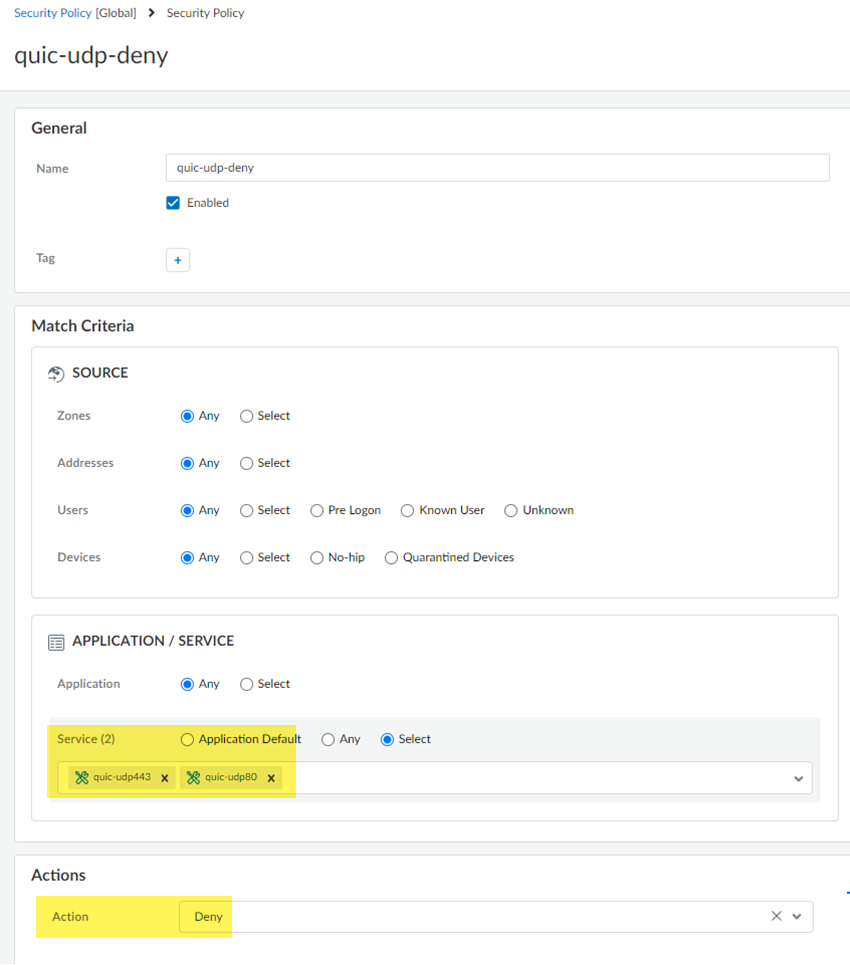
- Return toManageConfigurationNGFW & Prisma AccessSecurity ServicesSecurity PolicyAdd Rulefor a second security policy, specifying the services underApplication / Servicesand anActionofDrop.
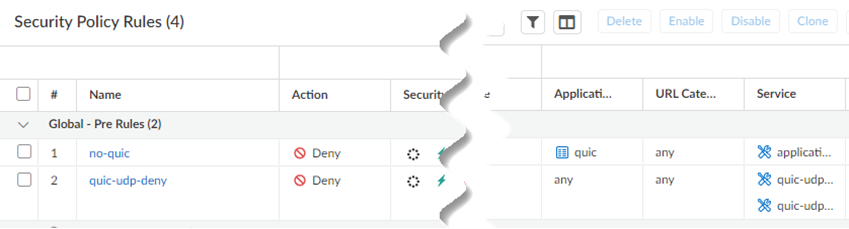
![]() When complete, you will have two security policies: One that blocks the QUIC protocol and one that blocks traffic on UDP ports 80 and 443.
When complete, you will have two security policies: One that blocks the QUIC protocol and one that blocks traffic on UDP ports 80 and 443.![]()
- Import a root certificate authority (CA) certificate and private key inStrata Cloud Managerin thePrisma Accessscope to use with App Acceleration and push your changes.A self-signed root CA/certificate is the top-most certificate in a certificate chain. App Acceleration uses the root CA/certificates to create certificates for the accelerated apps. Push the root CA/certificate in Prisma Access so that App Acceleration can begin creation of the app- specific certificates.The root CA/certificate must have these characteristics: :
- The CA must be a trusted CA.
- (Recommended) The CA should be unique and used for App Acceleration only.
- The CA can't be expired. Make a note of the CA expiration date, and renew the certificate before it expires. If a CA/certificate in use by App Acceleration expires, users will receive an SSL error when trying to access accelerated apps. It is critical to ensure that the CA is valid when App Acceleration is in use by your organization.
- It must include a key.
- It must use a passphrase.
- It must be in thescope.Prisma Access
- (Mobile Users—GlobalProtect Deployments Only) It must be installed in the local root certificate store.You can perform this installation by adding it to the list of trusted certificates as described in this procedure or, if you are using ActiveDirectory, you can distribute the root CA from AD using an Active Directory Group Policy Object (GPO).
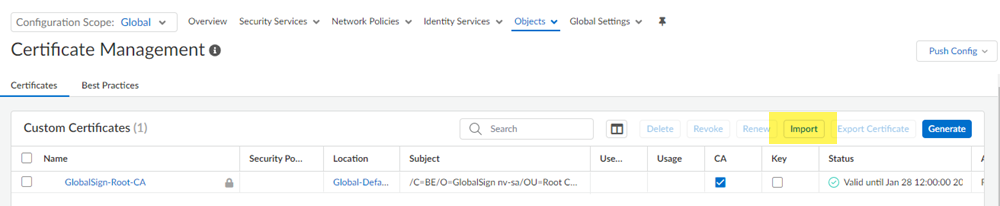
If you ever need to change the root CA/certificate, you must upload it and commit your changes before you can use the changed certificate.- Go to.ManageConfigurationNGFW and Prisma AccessObjectsCertificate Management
- Importa certificate.
![]()
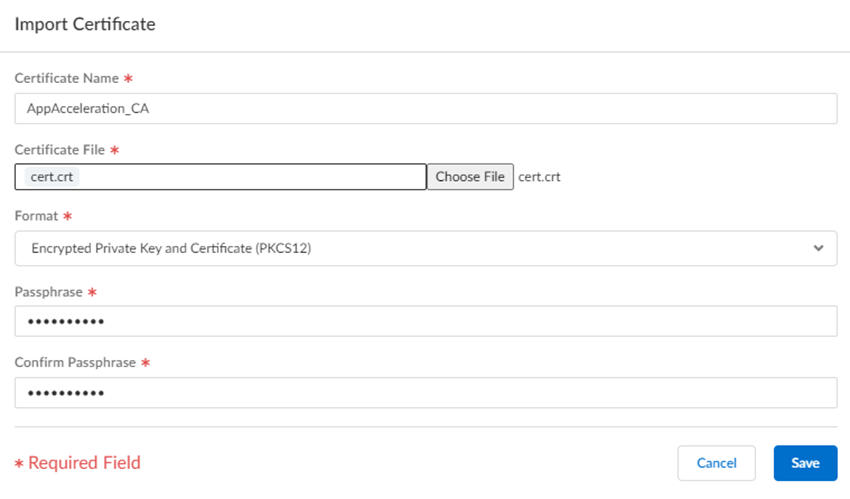
- Select the following parameters:
- Enter a uniqueCertificate Namefor the certificate, such asAppAcceleration_CA.The name is case-sensitive and can be up to 31 characters long. Use only letters, numbers, hyphens, and underscores in the name.
- Choose Fileand browse for theCertificate Filereceived from the CA andOpenit.
- Select aFormat:
- Encrypted Private Key and Certificate (PKCS12)—This is the default and most common format, in which the key and certificate are in a single container (Certificate File).
- Base64 Encoded Certificate (PEM)—You must import the key separately from the certificate. You're required to select aKey Fileif you select this format.
- Enter aPassphraseandConfirm Passphrase.
- Saveyour changes.
![]()
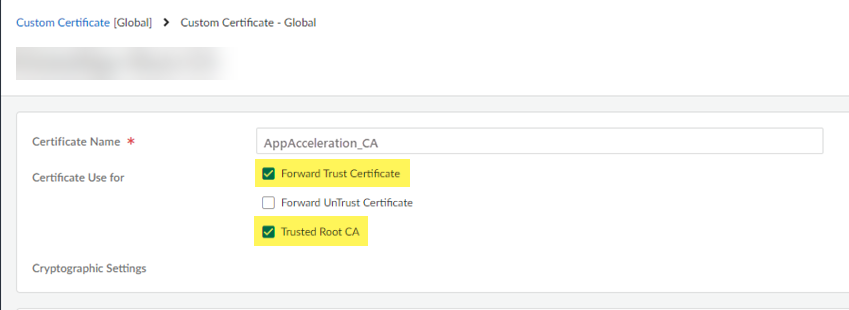
- Mark the root CA/certificate you added as a forward trust certificate and a trusted root CA.If you don't specify the certificate as a forward trust certificate and trusted root CA, users will encounter SSL errors when trying to access accelerated apps when using SSL decryption.
- Select the root CA/certificate you added.
- Select the certificate as aForward Trust CertificateandTrusted Root CA.
![]()
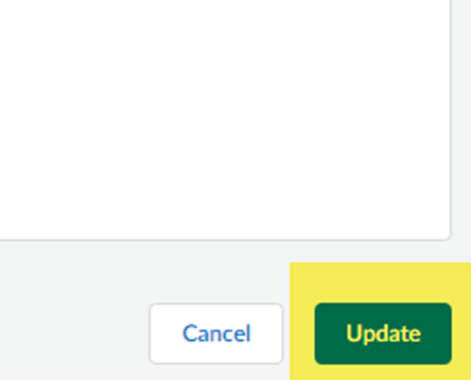
- Updatethe certificate.
![]()
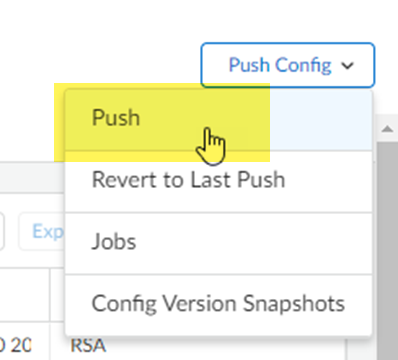
- Pushyour changes.
![]()
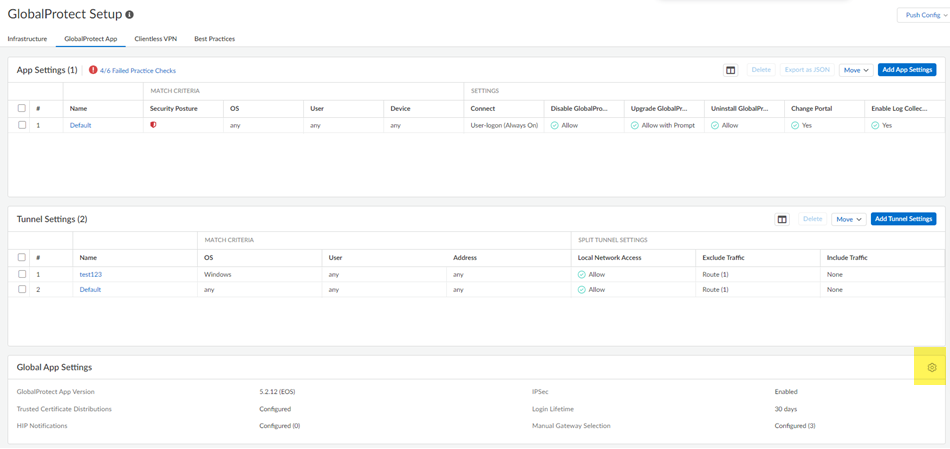
- (Mobile Users—GlobalProtect Deployments Only) Add the root CA/certificate you added to the list of GlobalProtect trusted certificates and install it in the local root certificate store.Alternatively, if you are using ActiveDirectory, you can distribute the root CA from AD using an Active Directory GPO.
- Go to.WorkflowsPrisma Access SetupGlobalProtectGlobalProtect AppGlobal App Settings
- Click the gear to edit theSettings.
![]()
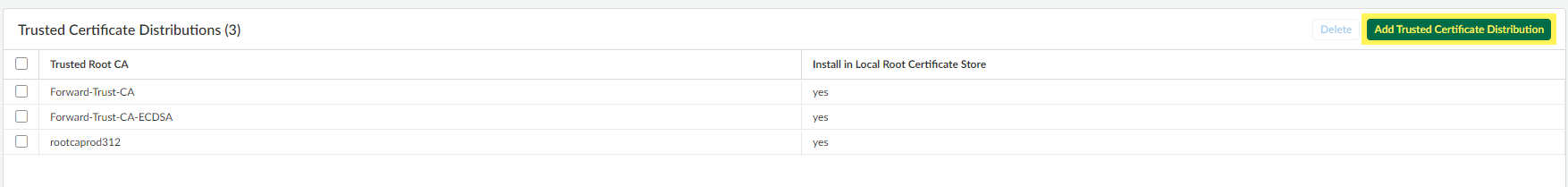
- Add Trusted Certificate Distribution.
![]()
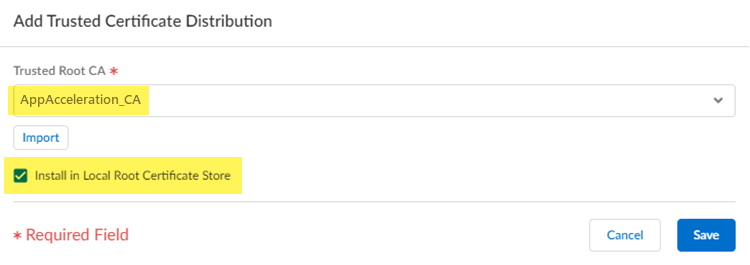
- Select theTrusted Root CAyou created in an earlier step and selectInstall in Local Root Certificate Store.
![]()
- Saveyour changes.
- Pushyour changes.
- Enable App Acceleration and choose the certificate file you created.
- Go tofrom the left navigation bar.WorkflowsApp Acceleration
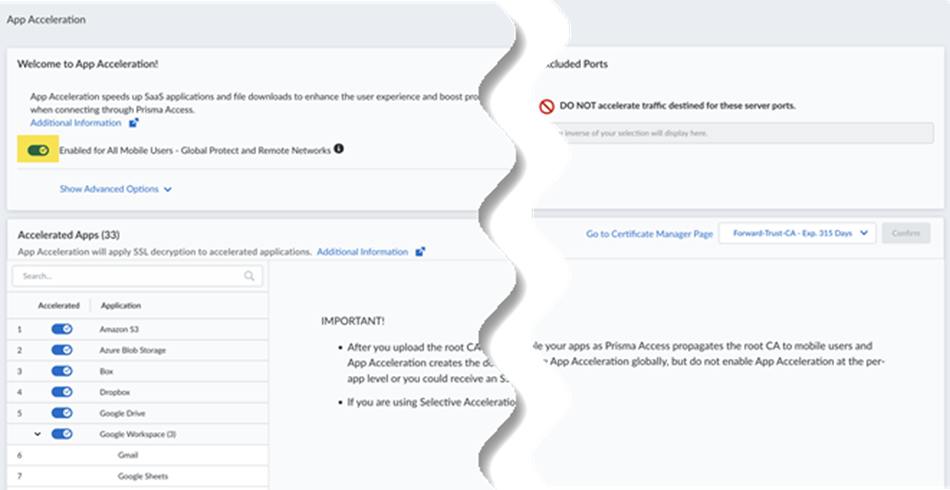
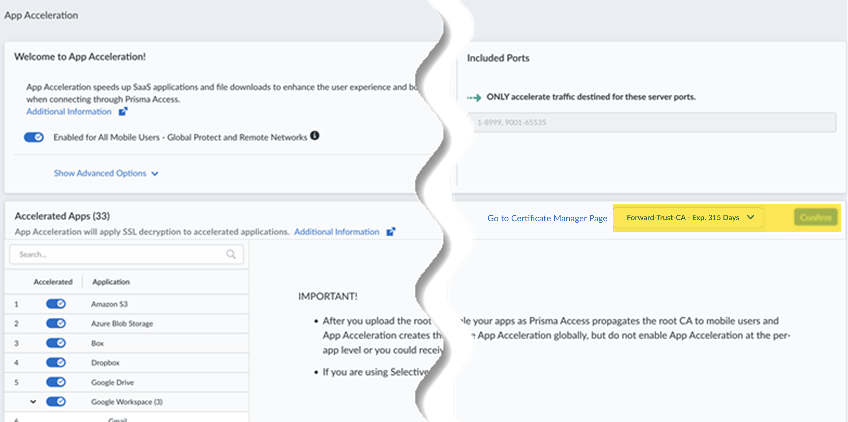
![]() The App Acceleration window displays.
The App Acceleration window displays.![]()
- Move the slider to the right to have App Acceleration beEnabled for all Mobile Users—GlobalProtect and Remote Networks.If commits are ongoing, App Acceleration settings will take effect after all commits complete.
![]() App Acceleration displays as enabled; however, you still need to select a root CA/certificate.
App Acceleration displays as enabled; however, you still need to select a root CA/certificate.![]()
- Select the certificate you created in an earlier step.If you need to change the certificate from an existing one, select it here. You must commit the new certificate before you select it.
![]() After you import the certificate, you must wait until App Acceleration generates domain-specific certificates for each app. This process can take up to one hour. In the meantime, you can move the slider for theAccelerated Appsto the left to temporarily disable App Acceleration and access the apps until the certificates are generated; if you don't, you might receive an SSL error until the certificates are generated.
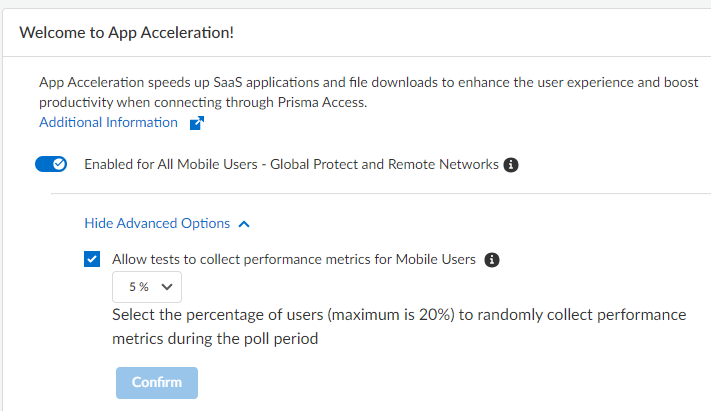
After you import the certificate, you must wait until App Acceleration generates domain-specific certificates for each app. This process can take up to one hour. In the meantime, you can move the slider for theAccelerated Appsto the left to temporarily disable App Acceleration and access the apps until the certificates are generated; if you don't, you might receive an SSL error until the certificates are generated. - (Optional)Show Advanced Optionsand change the metric testing parameters.
- (Optional) To disable the collection of metrics to obtain performance information, deselectAllow tests to collect performance metrics for Mobile Users.Palo Alto Networks recommends that you enable metric collection to view the app performance improvements when using App Acceleration.
- (Optional) To change the percentage of users for which predictive tests are processed from the default of 5%, select another percentage in the drop-down andConfirmthe changes.
![]()
Configure App Acceleration in Prisma Access (Panorama)
Prisma Access
(Panorama
)Configure App Acceleration in a
Prisma Access (Managed by Panorama)
deployment.To configure App Acceleration in a
Prisma Access (Managed by Panorama)
deployment, complete this
task.- (Optional) Disable the Quick UDP Internet Connections (QUIC) protocol.App Acceleration cannot accelerate apps at Layer 7 without disabling QUIC.
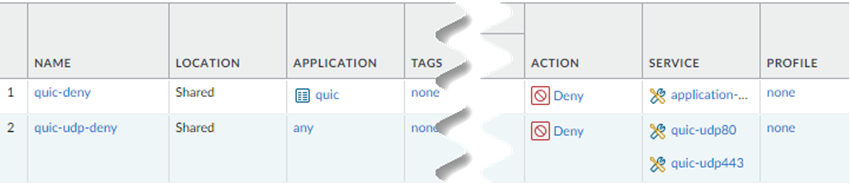
- Go toandPoliciesSecurityPre RulesAdda security policy.Create this Security policy rule in theShareddevice group.
- Select anApplicationofquicand anactionofDeny.
![]()
- Adda second security policy.Newer versions of QUIC might be misidentified asunknown-udp. For this reason, Palo Alto Networks recommends adding services for UDP port 80 and UDP port 443 and creating an additional security policy to block UDP traffic on those ports.
- UnderService/URL Category,Adda new services for UDP port 80 and UDP port 443 and anActionofDeny.When complete, you will have two security policies: One that blocks the QUIC protocol and one that blocks traffic on UDP ports 80 and 443.
![]()
- Import a root certificate authority (CA) certificate and private key in Panorama to use with App Acceleration and commit and push your changes.A self-signed root CA/ certificate is the top-most certificate in a certificate chain. App Acceleration uses the root CA/ certificates to create certificates for the accelerated apps. Push the root CA/ certificate in Prisma Access so that App Acceleration can begin creation of the app-specific certificates.The root CA/ certificate must have these characteristics:
- The CA must be a trusted CA.
- (Recommended) The CA should be unique and used for App Acceleration only.
- The CA can't be expired. Make a note of the CA expiration date, and renew the certificate before it expires. If a CA/certificate in use by App Acceleration expires, users will receive an SSL error when trying to access accelerated apps. It is critical to ensure that the CA is valid when App Acceleration is in use by your organization.
- It must include a key.
- It must use a passphrase.
- (Mobile Users—GlobalProtect Deployments Only) It must be installed in the local root certificate store.You can perform this installation by adding it to the list of trusted certificates as described in this procedure or, if you are using ActiveDirectory, you can distribute the root CA from AD using an Active Directory Group Policy Object (GPO).
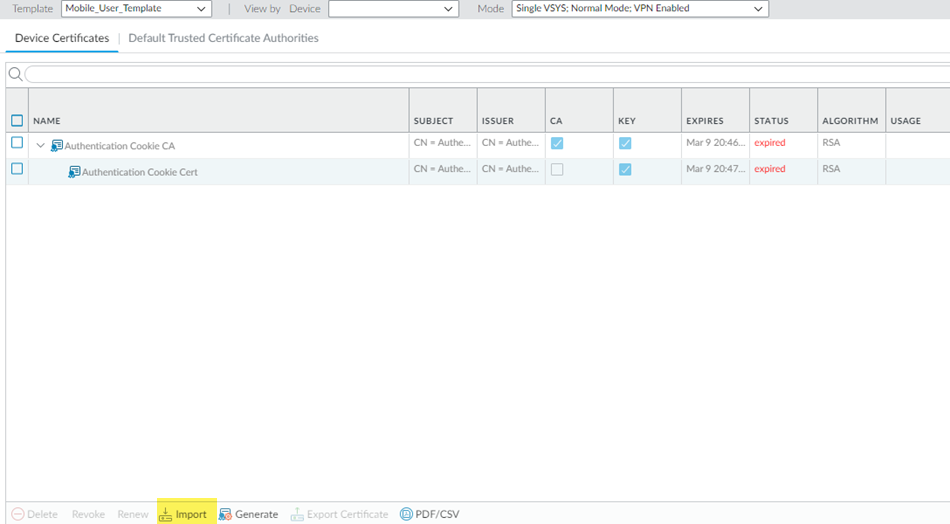
If you ever need to change the root CA/certificate, you must upload it and commit and push your changes before you can use the changed certificate.- Go to.DeviceCertificatesCertificate ManagementBe sure that you are in the Mobile_User_Template.
- Importa certificate.
![]()
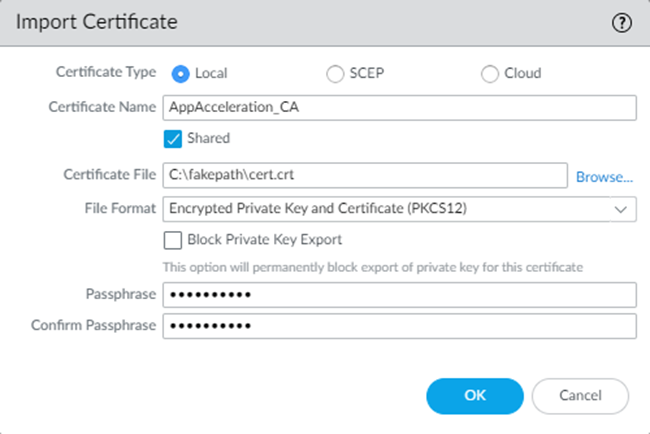
- Select the following parameters:
- Enter a uniqueCertificate Namefor the certificate, such asAppAcceleration_CA.The name is case-sensitive and can be up to 31 characters long. Use only letters, numbers, hyphens, and underscores in the name.
- Browse for theCertificate Filereceived from the CA andOpenit.
- Select aFormat:
- Encrypted Private Key and Certificate (PKCS12)—This is the default and most common format, in which the key and certificate are in a single container (Certificate File).
- Base64 Encoded Certificate (PEM)—You must import the key separately from the certificate. You're required toImport Private Keyand select aKey Fileif you select this format.
- Enter aPassphraseandConfirm Passphrase.
- ClickOK.
![]()
- Repeat these steps, substituting the Remote_Network_Template for the Mobile_User_Template.You must import these certificates in both the Mobile_User_Template and Remote_Network_Template in order to accelerate apps for your mobile users and users at remote network sites.
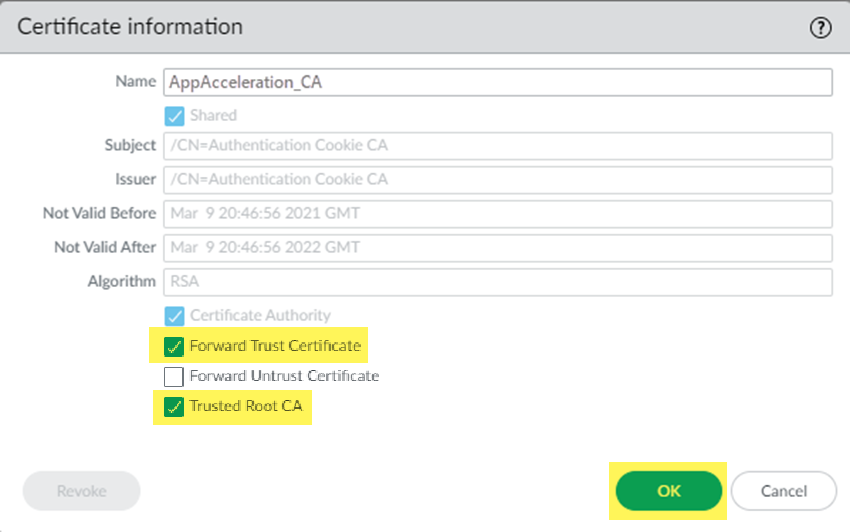
- Mark the root CA/certificate you added as a forward trust certificate and a trusted root CA.If you don't specify the certificate as a forward trust certificate and trusted root CA, users will encounter SSL errors when trying to access accelerated apps when using SSL decryption. If you have certificates in the Mobile_User_Template and Remote_Network_Template, perform this step in both templates.
- Select the root CA/certificate you added.
- Select the certificate as aForward Trust CertificateandTrusted Root CAand clickOK.
![]()
- Commit and Pushyour changes.
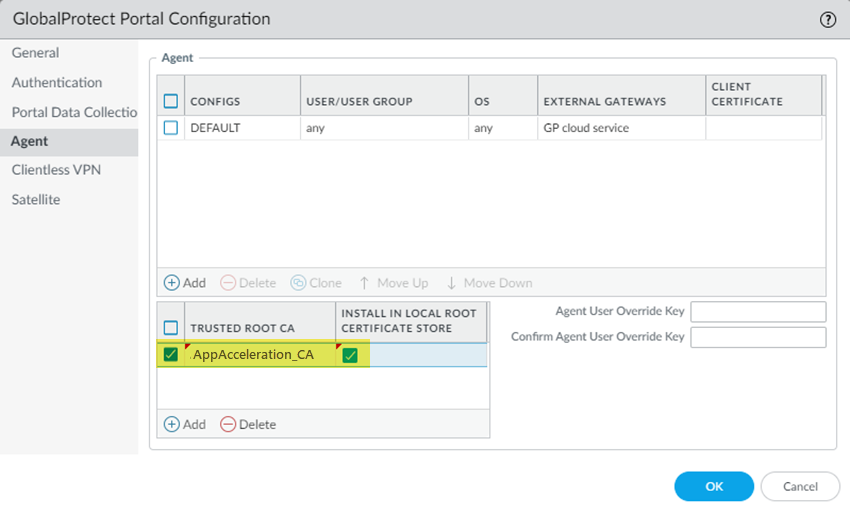
- (Mobile Users—GlobalProtect Deployments Only) Add the root CA/certificate you added to the list of GlobalProtect trusted certificates in the GlobalProtect portal configuration.Alternatively, if you are using ActiveDirectory, you can distribute the root CA from AD using an Active Directory GPO.
- Go to.NetworkGlobalProtectPortalsGlobalProtect_PortalAgentBe sure that you are in the Mobile_User_Template.
- Addthe trusted root CA you created in a previous step.
- SelectInstall in Local Root Certificate Store.
- ClickOK.
![]()
- Commit and Pushyour changes.
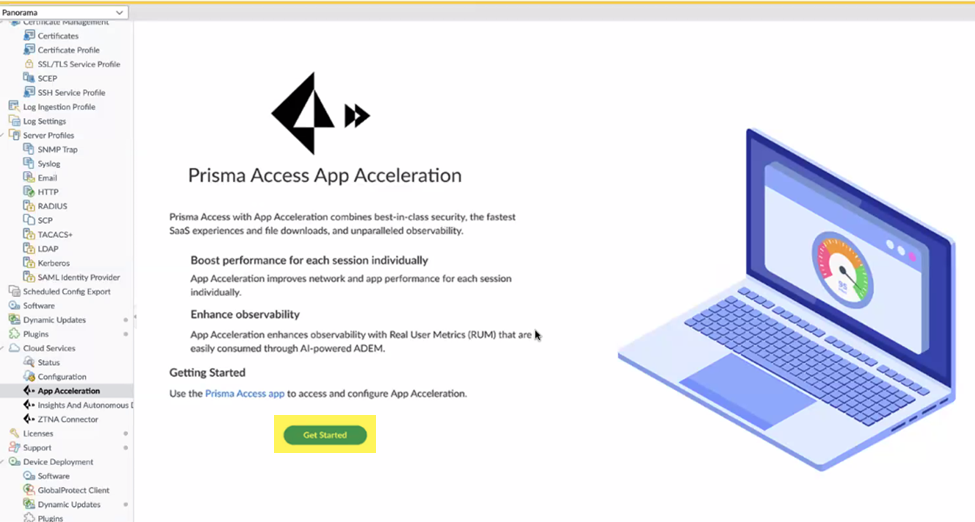
- Enable App Acceleration and choose the certificate file you created.
- Go toandPanoramaCloud ServicesApp AccelerationGet Startedwith App Acceleration.
![]()
- Go tofrom the left navigation bar.WorkflowsApp Acceleration
![]() The App Acceleration window displays.
The App Acceleration window displays.![]()
- Move the slider to the right to have App Acceleration beEnabled for all Mobile Users—GlobalProtect and Remote Networks.If commits are ongoing, App Acceleration settings will take effect after all commits complete.
![]() App Acceleration displays as enabled; however, you still need to select a root CA/ certificate.
App Acceleration displays as enabled; however, you still need to select a root CA/ certificate.![]()
- Select the certificate you created in an earlier step.If you need to change the certificate from an existing one, select it here. You must commit and push the new certificate before you select it.
![]() After you import the certificate, you must wait until App Acceleration generates domain-specific certificates for each app. This process can take up to one hour. In the meantime, you can move the slider for theAccelerated Appsto the left to temporarily disable App Acceleration and access the apps until the certificates are generated; if you don't, you might receive an SSL error until the certificates are generated.
After you import the certificate, you must wait until App Acceleration generates domain-specific certificates for each app. This process can take up to one hour. In the meantime, you can move the slider for theAccelerated Appsto the left to temporarily disable App Acceleration and access the apps until the certificates are generated; if you don't, you might receive an SSL error until the certificates are generated. - (Optional)Show Advanced Optionsand change the metric testing parameters.
- (Optional) To disable the collection of metrics to obtain performance information, deselectAllow tests to collect performance metrics for Mobile Users.Palo Alto Networks recommends that you enable metric collection to view the app performance improvements when using App Acceleration.
- (Optional) To change the percentage of users for which predictive tests are processed from the default of 5%, select another percentage in the drop-down andConfirmthe changes.
![]()