Advanced WildFire Powered by Precision AI™
View WildFire Logs and Analysis Reports (PAN-OS & Panorama)
Table of Contents
View WildFire Logs and Analysis Reports (PAN-OS & Panorama)
Samples that firewalls submit for WildFire
analysis are displayed as entries in the WildFire Submissions log
on the firewall web interface. For each WildFire entry, you can
open an expanded log view which displays log details and the WildFire
analysis report for the sample.
Mozilla Firefox users:
The WildFire Analysis Report displays correctly only in Firefox
v54 and earlier releases. If you experience issues viewing the report,
consider using a different web browser such as Google Chrome. Alternatively,
you can download and open the PDF version or view the report through
the WildFire portal.
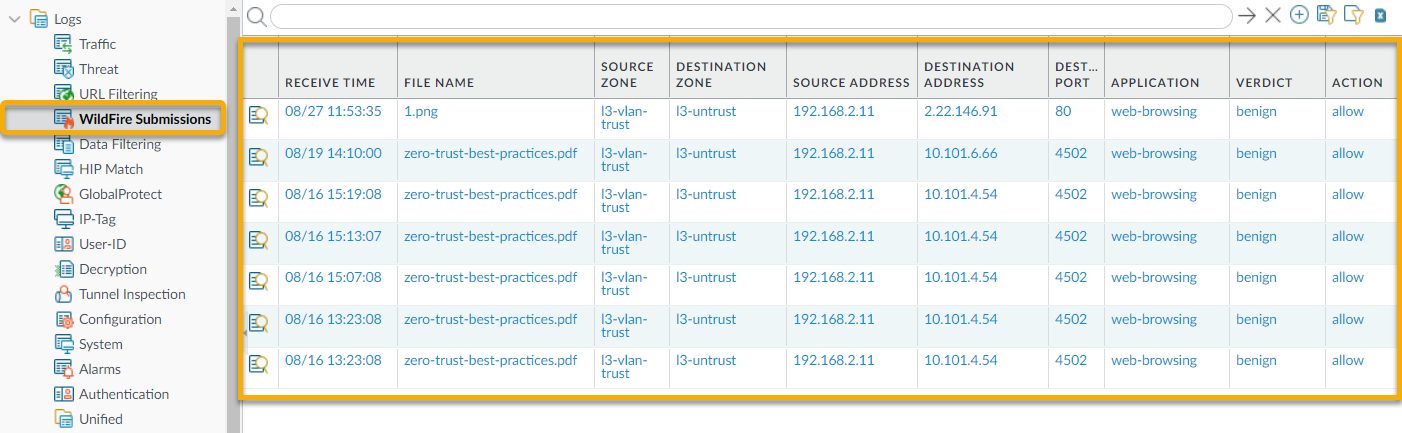
- Forward Files for Advanced WildFire Analysis.Configure WildFire Submissions Log Settings.To view samples submitted by a firewall to a WildFire public, private, or hybrid cloud, select MonitorLogsWildFire Submissions. When WildFire analysis of a sample is complete, the results are sent back to the firewall that submitted the sample and are accessible in the WildFire Submissions logs. The submission logs include details about a given sample, including the following information:
- The Verdict column indicates whether the sample is benign, malicious, phishing, or grayware.
- The Action column indicates whether the firewall allowed or blocked the sample.
- The Severity column indicates how much of a threat a sample poses to an organization using the following values: critical, high, medium, low, and informational.The values for the following severity levels are determined by a combination of verdict and action values.
- Low—Grayware samples with the action set to allow.
- High—Malicious samples with the action set to allow.
- Informational:
- Benign samples with the action set to allow.
- Samples with any verdict with the action set to block.
![]() For any entry, select the Log Details icon to open a detailed log view for each entry:
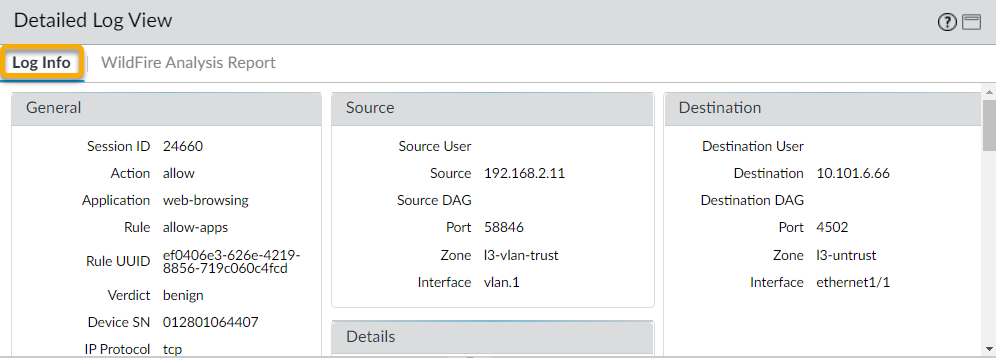
For any entry, select the Log Details icon to open a detailed log view for each entry:![]() The detailed log view displays Log Info and the WildFire Analysis Report for the entry. If the firewall has packet captures (PCAPs) enabled, the sample PCAPs are also displayed.
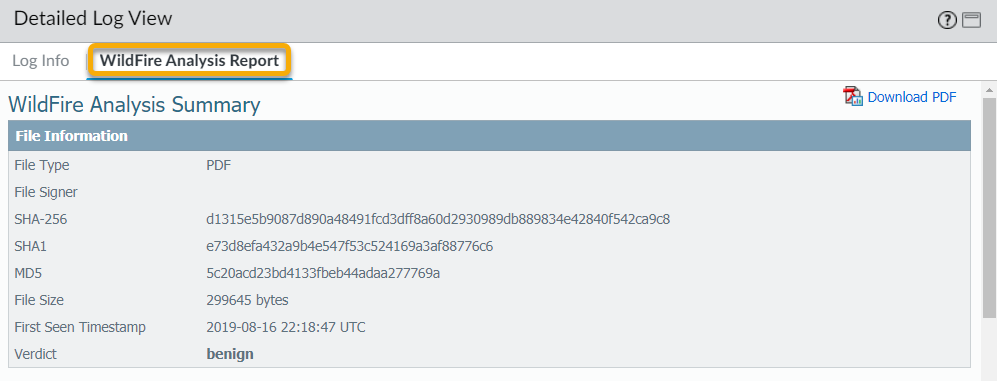
The detailed log view displays Log Info and the WildFire Analysis Report for the entry. If the firewall has packet captures (PCAPs) enabled, the sample PCAPs are also displayed.![]() For all samples, the WildFire analysis report displays file and session details. For malware samples, the WildFire analysis report is extended to include details on the file attributes and behavior that indicated the file was malicious.
For all samples, the WildFire analysis report displays file and session details. For malware samples, the WildFire analysis report is extended to include details on the file attributes and behavior that indicated the file was malicious.![]() (Optional) Download PDF of the WildFire Analysis Report.
(Optional) Download PDF of the WildFire Analysis Report.