Enterprise DLP
Strata Cloud Manager
Table of Contents
Expand All
|
Collapse All
Enterprise DLP Docs
Strata Cloud Manager
Create a security policy rule to prevent exfiltration of sensitive data to ChatGPT
for Prisma Access (Managed by Strata Cloud Manager) on Strata Cloud Manager.
- Log into Strata Cloud Manager.Enable Non-File Inspection.Select ConfigurationNGFW and Prisma AccessSecurity ServicesDecryption and create the decryption profile and policy rule required to enable Enterprise DLP on Strata Cloud Manager.Do not enable Strip ALPN in the decryption profile. Enterprise DLP cannot inspect egress traffic to ChatGPT if you remove application-layer protocol negotiation (ALPN) headers from decrypted traffic.(Optional) Create a data pattern.Create a custom regex data pattern to define your own match criteria. You can skip this step if you plan to use predefined or existing data patterns to define match criteria in your data filtering profile.Create a data profile or use an existing data profile.Select ConfigurationData Loss PreventionDLP Rules and in the Actions column, Edit the DLP rule.
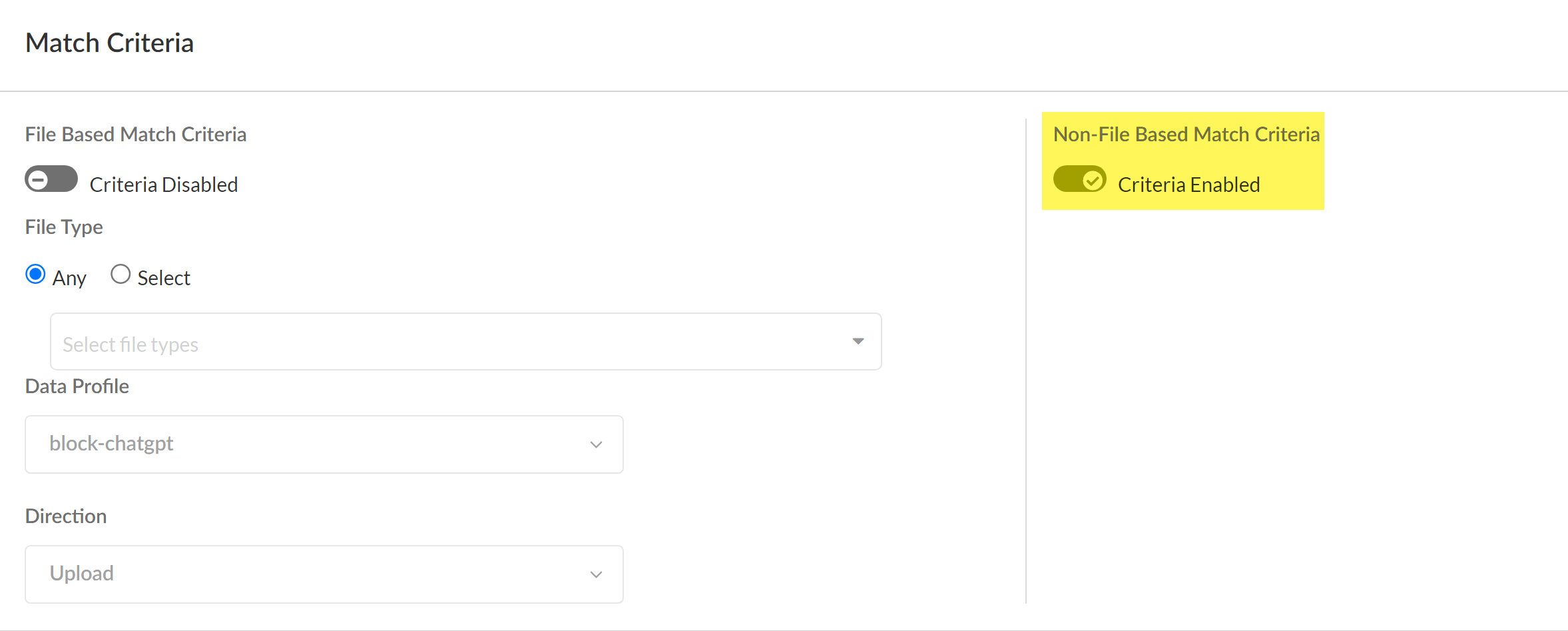
- Enable Non-File Based Match Criteria.DLP rules configured for non-file detection are required to prevent exfiltration of sensitive data to ChatGPT. You can further modify the DLP rule to enforce your organization’s data security standards. The DLP rule has an identical name as the data profile from which it was automatically created.You can keep File Based Matched Criteria enabled or disable as needed. Enabling this setting has no impact on detection of egress traffic to ChatGPT as long as Non-File Based Match Criteria is enabled.
![]() Modify the Action and Log Severity.Modify the rest of the DLP rule as needed.Save.Create a Shared Profile Group for the Enterprise DLP data filtering profile.
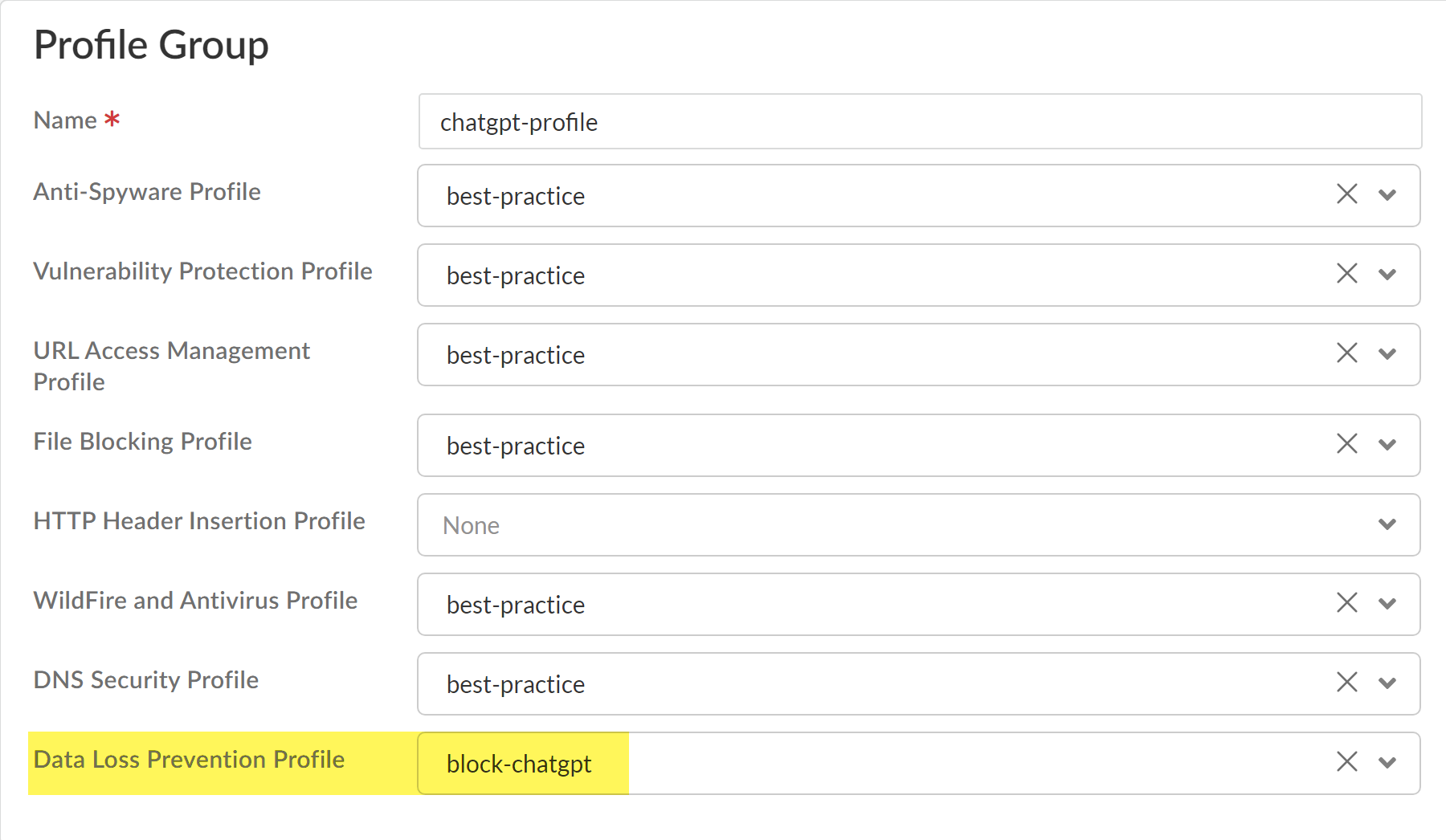
Modify the Action and Log Severity.Modify the rest of the DLP rule as needed.Save.Create a Shared Profile Group for the Enterprise DLP data filtering profile.- Select ConfigurationNGFW and Prisma AccessSecurity ServicesProfile Groups and Add Profile Group.Enter a descriptive Name for the Profile Group.For the Data Loss Prevention Profile, select the Enterprise DLP data profile.Add any other additional profiles as needed.Save the profile group.
![]() Create a Security policy and attach the Profile Group.Alternatively, you can create or add ChatGPT to an Internet Access policy rule. You can skip this step if you create a Internet Access policy rule for ChatGPT.
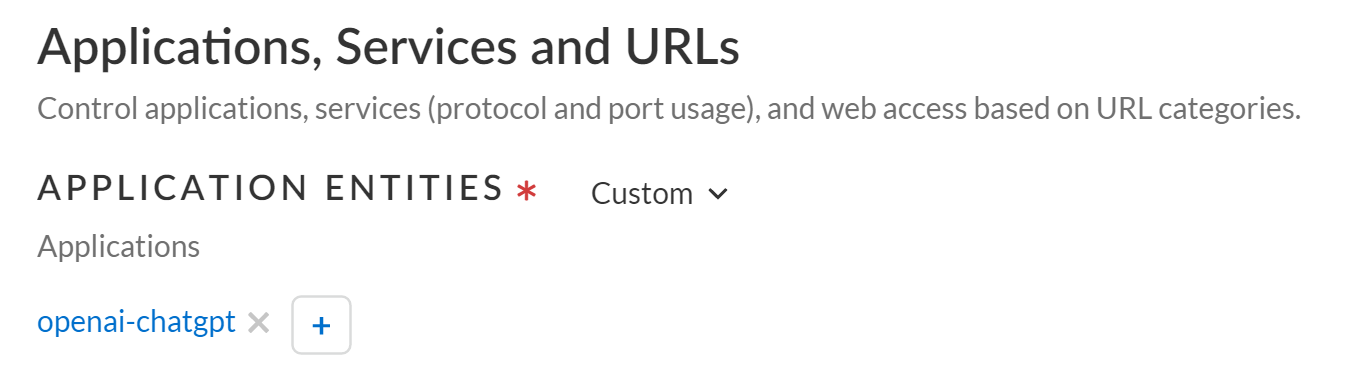
Create a Security policy and attach the Profile Group.Alternatively, you can create or add ChatGPT to an Internet Access policy rule. You can skip this step if you create a Internet Access policy rule for ChatGPT.- Select ConfigurationSecurity ServicesSecurity Policy and Add Rule.You can also update an existing Security policy to attach a Profile Group for Enterprise DLP filtering.In the Applications, Services, and URLs section, Add Applications to search for and select openai-chatgpt.
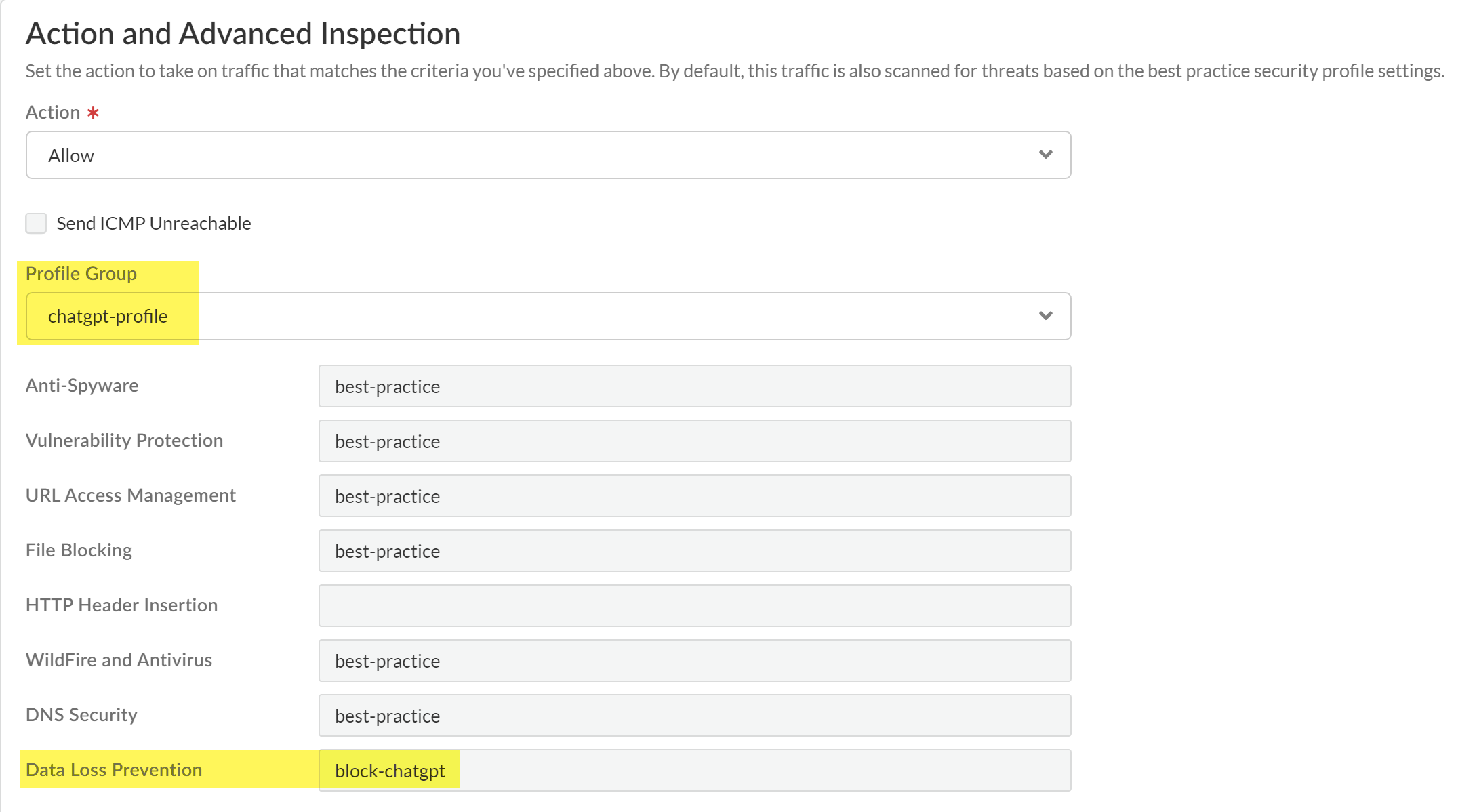
![]() Navigate to the Action and Advanced Inspection section, and select the Profile Group you created in the previous step.
Navigate to the Action and Advanced Inspection section, and select the Profile Group you created in the previous step.![]() Configure the Security policy as needed.The Action you specify in the data profile determines whether egress traffic to ChatGPT is blocked. The Security policy rule Action does not impact whether matched traffic is blocked.For example, you configured the data filtering profile to Block matching egress traffic but configure the Security policy rule Action to Allow. In this scenario, the matching egress traffic to ChatGPT is blocked.Save the Security policy.Push your Security policy rule.
Configure the Security policy as needed.The Action you specify in the data profile determines whether egress traffic to ChatGPT is blocked. The Security policy rule Action does not impact whether matched traffic is blocked.For example, you configured the data filtering profile to Block matching egress traffic but configure the Security policy rule Action to Allow. In this scenario, the matching egress traffic to ChatGPT is blocked.Save the Security policy.Push your Security policy rule.- Push Config and Push.Select (enable) Remote Networks and Mobile Users.Push.