GlobalProtect
Deploy the GlobalProtect Mobile App Using Workspace ONE
Table of Contents
End-of-Life (EoL)
Deploy the GlobalProtect Mobile App Using Workspace ONE
You can deploy the GlobalProtect app to managed endpoints that are enrolled with Workspace ONE.
Endpoints running iOS or Android must download the Workspace ONE agent to enroll
with the Workspace ONE MDM. Windows 10 endpoints do not require the Workspace ONE
agent but require you to configure enrollment on the endpoint. After you deploy the
app, configure and deploy a VPN profile to set up the GlobalProtect app for end
users automatically.
If you want to run the GlobalProtect app for Android on managed Chromebooks, you can Deploy the GlobalProtect App for Android on Managed Chromebooks Using Workspace ONE.
- Before you begin, ensure that the endpoints to which you want to deploy the
GlobalProtect app are enrolled with Workspace ONE:
-
Android and iOS—Download the Workspace ONE agent and follow the prompts to enroll.
-
Windows Phone and Windows 10 UWP—Configure the Windows 10 UWP endpoint to enroll with Workspace ONE (from the endpoint, select SettingsAccountsWork accessConnect).
-
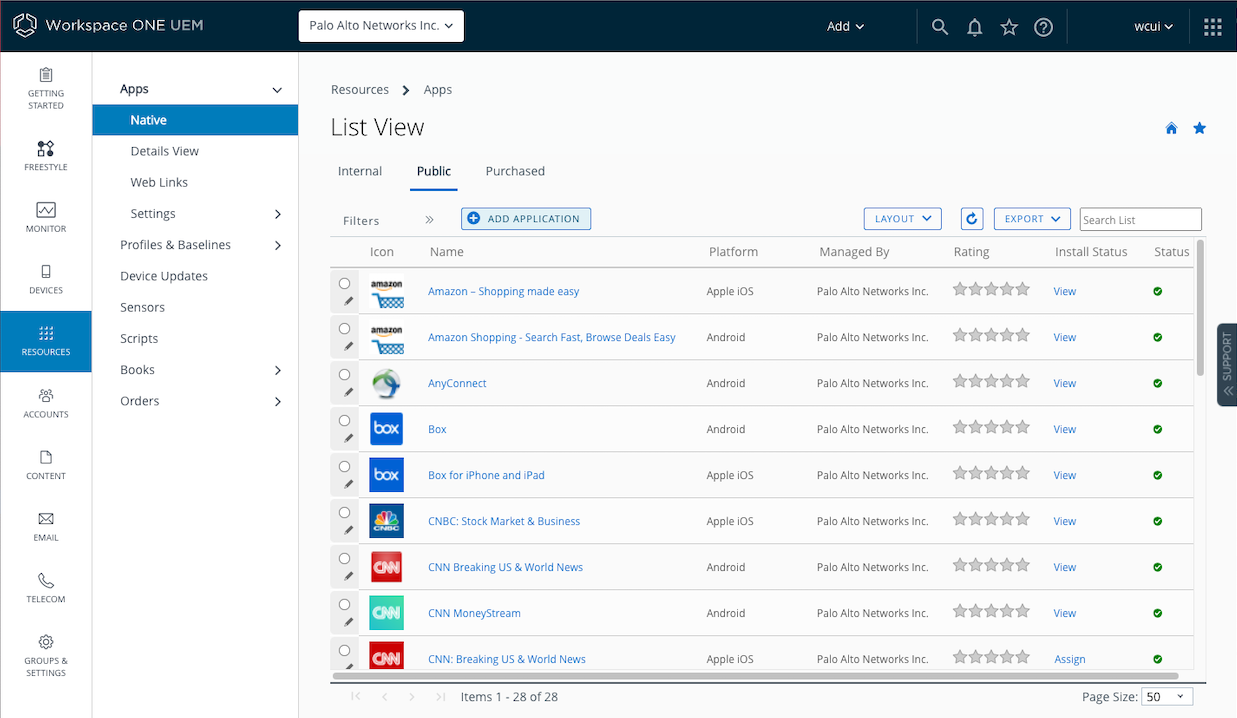
- Add the GlobalProtect app to Workspace ONE:
- From Workspace ONE, select ResourcesApps NativePublicAdd Application.
![]()
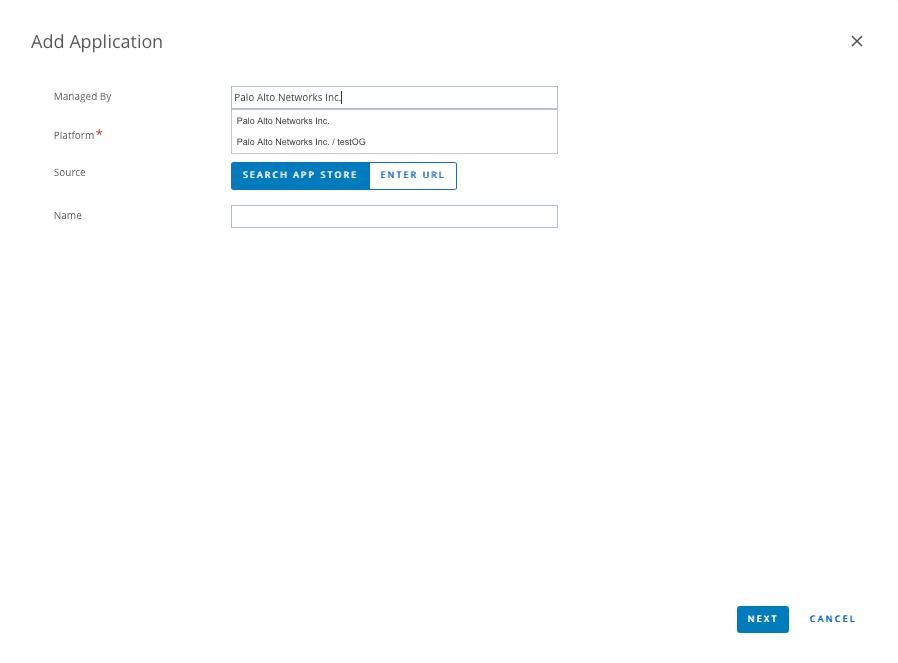
- In the Managed by field, select the organization
group by which this app will be managed.
![]()
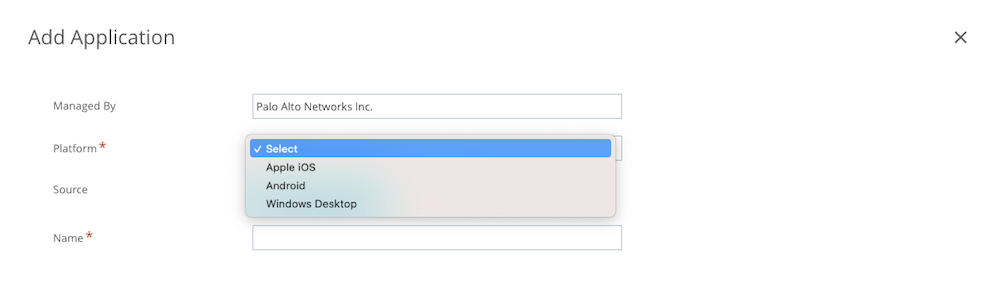
- Select the Platform (Apple
iOS, Android, or
Windows Desktop).
![]()
- Search for the GlobalProtect app in the endpoint app store, or enter
one of the following URLs for the GlobalProtect app page:
-
Windows Phone and Windows 10 UWP—https://www.microsoft.com/en-us/p/globalprotect/9nblggh6bzl3
- Click Next. If you searched for the app in the
endpoint app store, you must also Select the app
from a list of search results, and then SAVE &
ASSIGN to configure deployment options.If you searched for the GlobalProtect app for Android and did not see the app in the list, contact your Android for Work administrator to add GlobalProtect to the list of approved company apps or use the app URL in the Google Play Store.
- From Workspace ONE, select ResourcesApps NativePublicAdd Application.
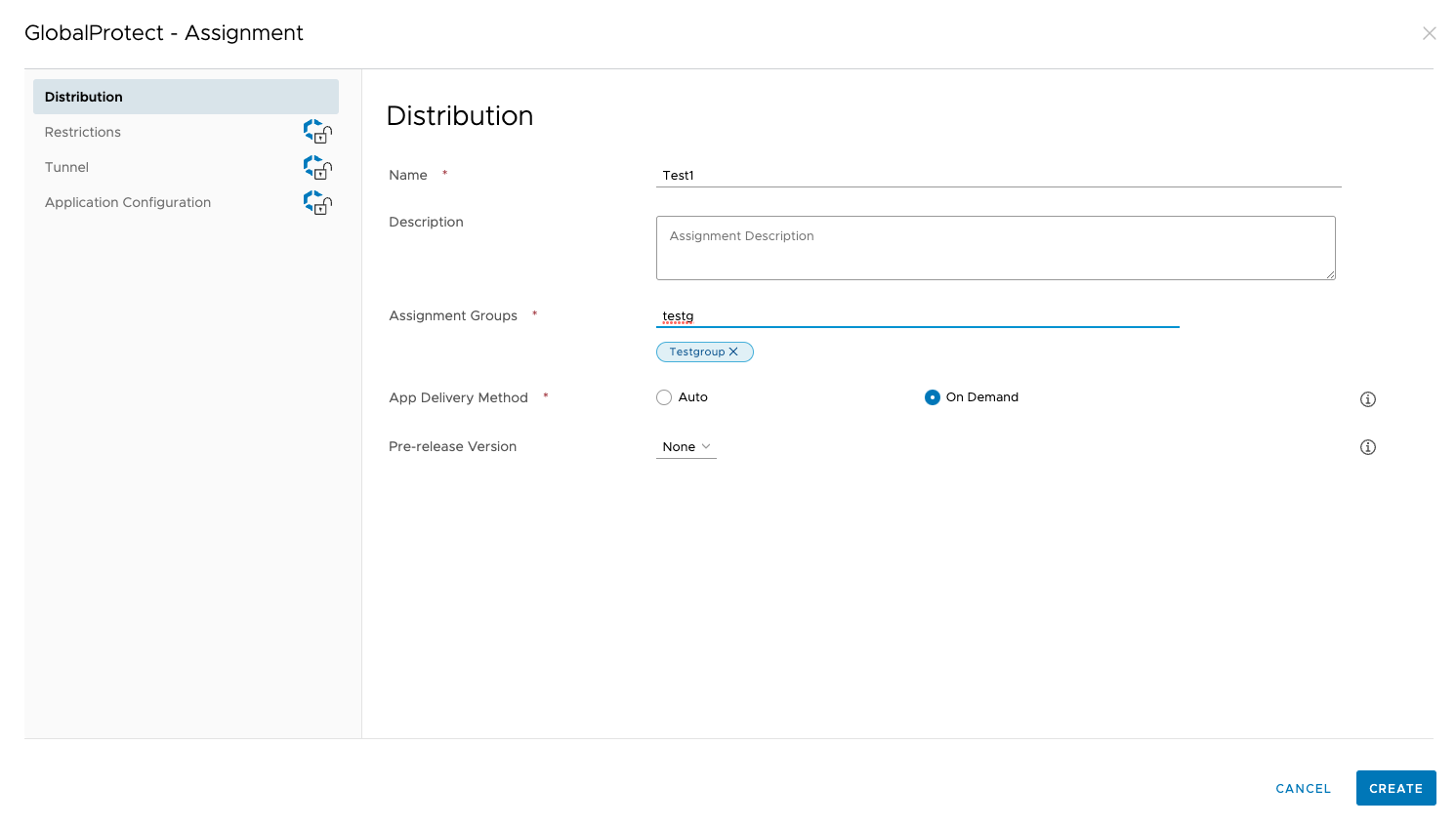
- Configure deployment options for the GlobalProtect app:If you added the app previously but did not assign the app to any Smart Groups, select the GlobalProtect link from the list of apps (ResourcesApps NativePublic). In the Details View, select AssignAdd Assignment.
- On the Distribution tab, specify the following
information:
- Enter a Name for the assignment.
- Select one or more Assignment Groups that will have access to the GlobalProtect app.
- Choose the App Delivery Method, either Auto, which pushes the app to the device automatically, or On Demand, which deploys the app when needed.
![]()
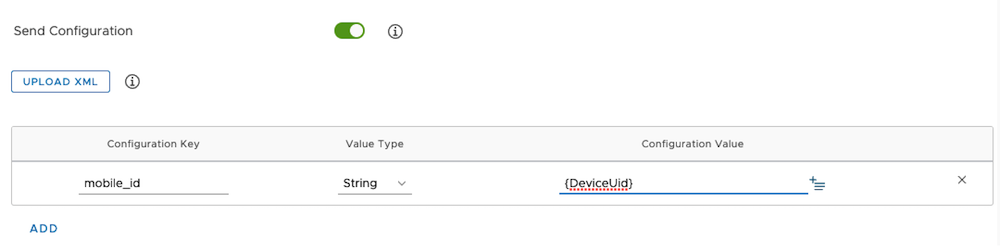
- (GlobalProtect App for iOS or Android only) On the
Application Configuration tab, enable the
application configuration to use the UDID to identify the
endpoint.
-
iOS—To use HIP integration with MDM for your GlobalProtect deployment on iOS devices, you can specify the unique device identifier (UDID) attribute. For details, see Configure an Always On VPN Configuration for iOS Endpoints Using Workspace ONE.Toggle on Send Configuration and add the following key-value pairs:
-
Configuration Key—mobile_id
-
Value Type—String
-
Configuration Value—{DeviceUid}
![]()
-
-
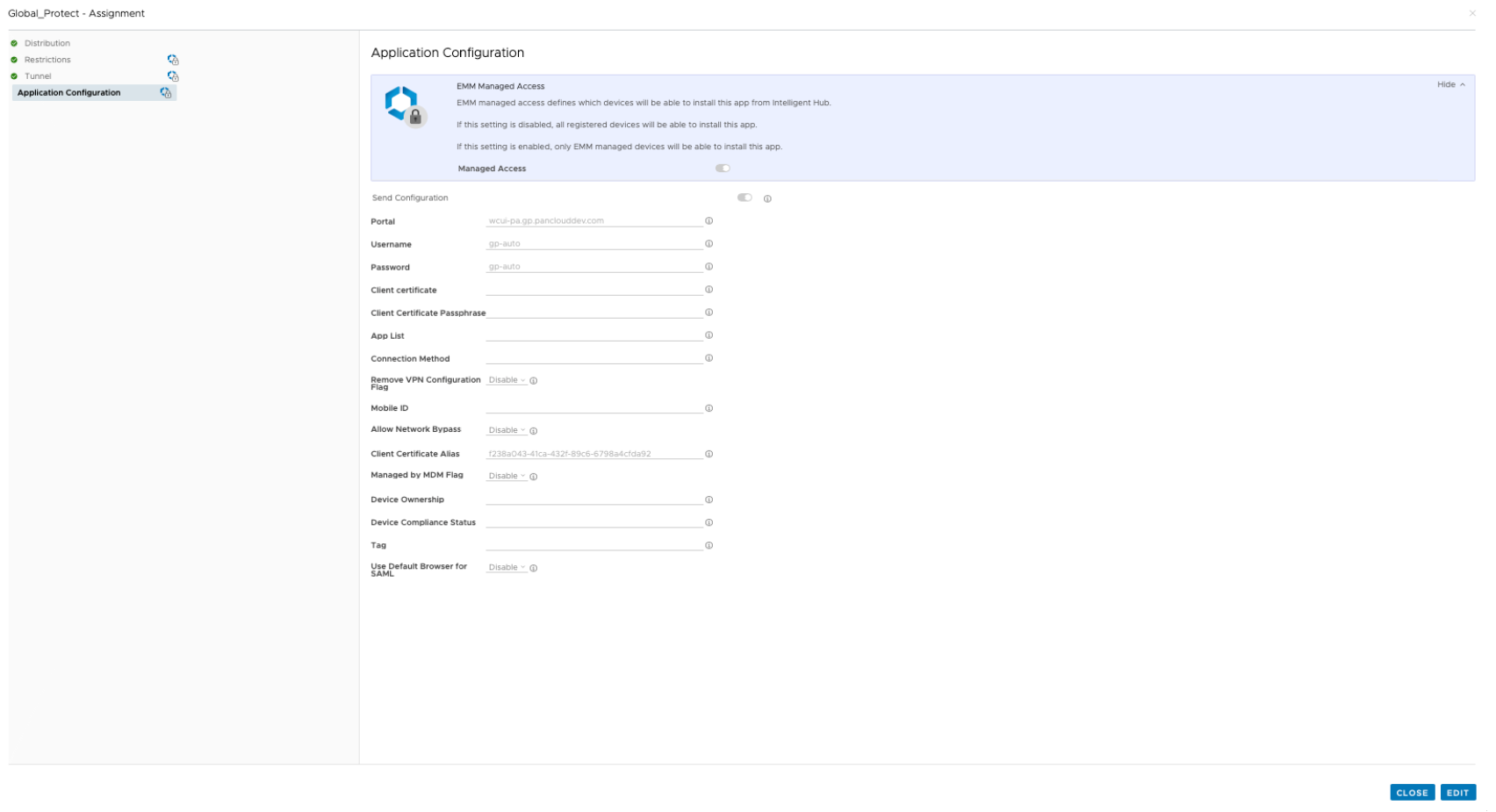
Android—Toggle on Send Configuration and specify the settings in the application configuration that are relevant for your company:
-
Portal—IP address or fully qualified domain name (FQDN) of the portal.
-
Username—Username for portal authentication.
-
Password—Password for portal authentication.
-
Client Certificate—Client certificate for portal authentication.
-
Client Certificate Passphrase—Passphrase for the client certificate.
-
App List—Begin the string with either the allowlist keyword or blocklist keyword followed by a colon, and follow it with an array of app names separated by semicolons. The block list or allow list enables you to control which application traffic can go through the VPN tunnel in a per-app VPN configuration (for example, allowlist| blocklist: com.google.calendar; com.android.email; com.android.chrome).
-
Connection Method—VPN connection method (for example, user-logon | on-demand).
-
Remove VPN Configuration Flag—Flag to remove the VPN configuration.
-
Mobile ID—Unique identifier used to identify mobile endpoints, as configured in a third-party MDM system.
-
Allow Network Bypass—Flag to allow application traffic to bypass the VPN tunnel.
-
Client Certificate Alias—Unique name to identify the client certificate during portal or gateway authentication.
-
Specify the Managed by MDM Flag to indicate whether the device is enrolled with an MDM server.
-
Device Ownership—Ownership category of the device (for example, Employee Owned).
-
Device Compliance Status—Compliance status that indicates whether the device is compliant with the compliance policies that you have defined.
-
Tag—Tags to enable you to identify devices. Each tag must be separated by a comma.
-
Use Default Browser for SAML—Whether to enable or disable the default system browser for SAML authentication.
![]()
-
-
- On the Distribution tab, specify the following
information:
- Click Create and then Save to preview the assigned devices.
- Click Publish to push the App Catalog to the endpoints in the Smart Groups that you assigned.