Prisma Access
Authorize Mobile Users in Prisma Access
Table of Contents
Expand All
|
Collapse All
Prisma Access Docs
-
- 6.1 Preferred and Innovation
- 6.0 Preferred and Innovation
- 5.2 Preferred and Innovation
- 5.1 Preferred and Innovation
- 5.0 Preferred and Innovation
- 4.2 Preferred
- 4.1 Preferred
- 4.0 Preferred
- 3.2 Preferred and Innovation
-
-
- 4.0 & Later
- Prisma Access China
-
-
Authorize Mobile Users in Prisma Access
Learn how to authorize mobile users in Prisma Access.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
If you are using an explicit proxy, ensure to set it up for mobile users. After adding
your Microsoft Entra ID (formerly Azure Active Directory (Azure AD)) in the Cloud Identity Engine, authorize users in Prisma
Access.
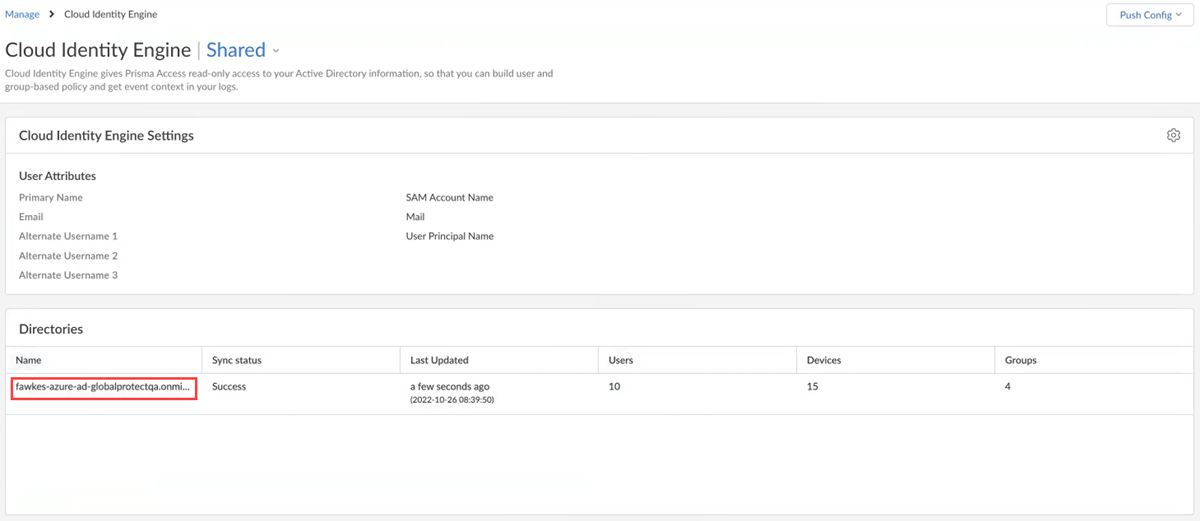
- In Prisma Access, verify if it is connected to Cloud Identity Engine, and that Cloud Identity Engine is sharing directory information with Prisma Access.
- Select ConfigurationNGFW and Prisma AccessIdentity ServicesCloud Identity Engine.Confirm the directory details you added in the Cloud Identity Engine app for the integration.
![]() Mark the incoming traffic based on the source.
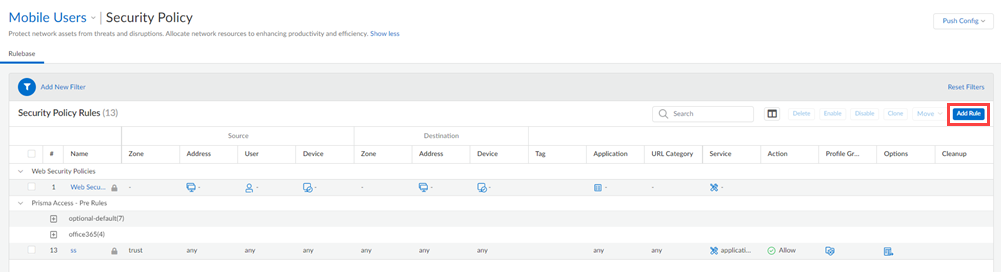
Mark the incoming traffic based on the source.- Select ConfigurationNGFW and Prisma AccessSecurity ServicesSecurity Policy.(For GlobalProtect mobile users and remote networks only) Add Rule or edit an existing security policy rule for GlobalProtect mobile users or Remote Networks.
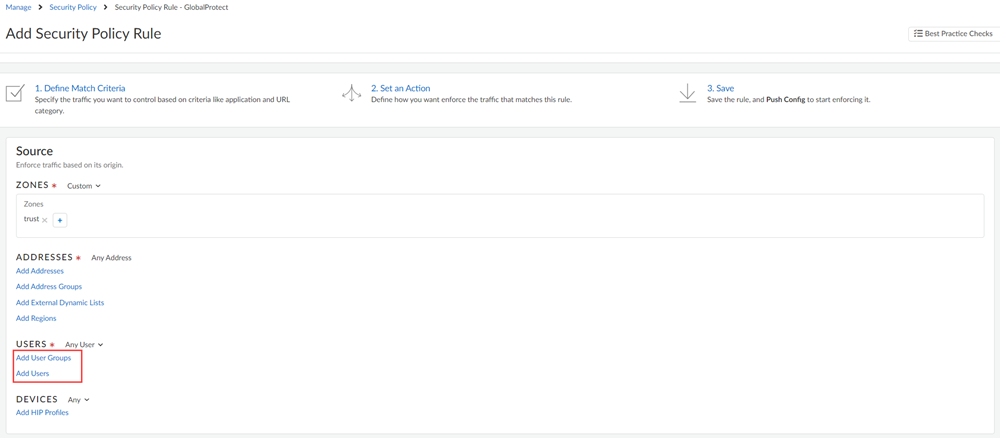
![]() (For explicit proxy mobile users only) Add Rule or edit an existing security policy rule for Explicit Proxy mobile users.Add users or user groups from the Microsoft Entra ID to your security policy rule and save the policy.
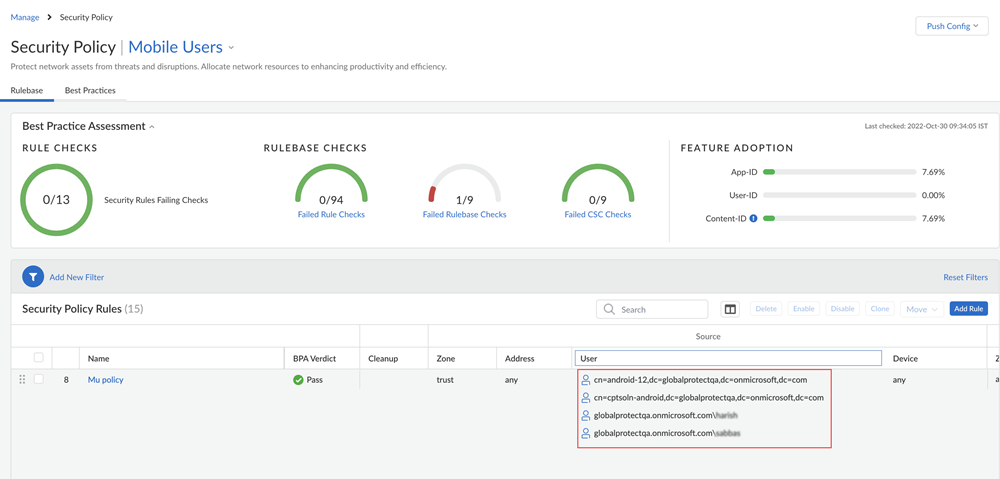
(For explicit proxy mobile users only) Add Rule or edit an existing security policy rule for Explicit Proxy mobile users.Add users or user groups from the Microsoft Entra ID to your security policy rule and save the policy.![]() View the users and user groups you added under the Source column.
View the users and user groups you added under the Source column.![]() Push the configurations.Verify the user or user group mapping.
Push the configurations.Verify the user or user group mapping.- For GlobalProtect mobile users only
- In Prisma Access, select Activity InsightsInsightsUsers.View details about mobile users and devices connected for a time range you select.
- For explicit proxy mobile users only
- Copy the PAC file URL to the endpoint.Go to ConfigurationNGFW and Prisma AccessConfiguration ScopePrisma AccessExplicit ProxyInfrastructure Settings to view the PAC file URL.Access a URL that requires authorization.Enter the credentials.In Prisma Access, view the user mapping information by running the show user ip-user-mapping all command.(Optional) In Prisma Access, select Activity InsightsInsightsUsers.View details about mobile users connected for a time range you select.