Prisma Access
New Features in Prisma Access 4.2
Table of Contents
Expand All
|
Collapse All
Prisma Access Docs
-
- 6.1 Preferred and Innovation
- 6.0 Preferred and Innovation
- 5.2 Preferred and Innovation
- 5.1 Preferred and Innovation
- 5.0 Preferred and Innovation
- 4.2 Preferred
- 4.1 Preferred
- 4.0 Preferred
- 3.2 Preferred and Innovation
-
-
- 4.0 & Later
- Prisma Access China
-
-
New Features in Prisma Access 4.2
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
The following table describes the new features that will be available with Prisma Access 4.2 Preferred.
Prisma Access Application Name Update
|
November 18, 2023
The application tile name on the hub for Prisma Access is now
changed to Strata Cloud Manager.
|
The application tile names on the hub for Prisma Access, Prisma SD-WAN, and
AIOps for NGFW (the premium app only) are now changed to Strata Cloud
Manager. With this update, the application URL has also changed to stratacloudmanager.paloaltonetworks.com, and
you’ll also now see the Strata Cloud Manager logo on the left navigation
pane.
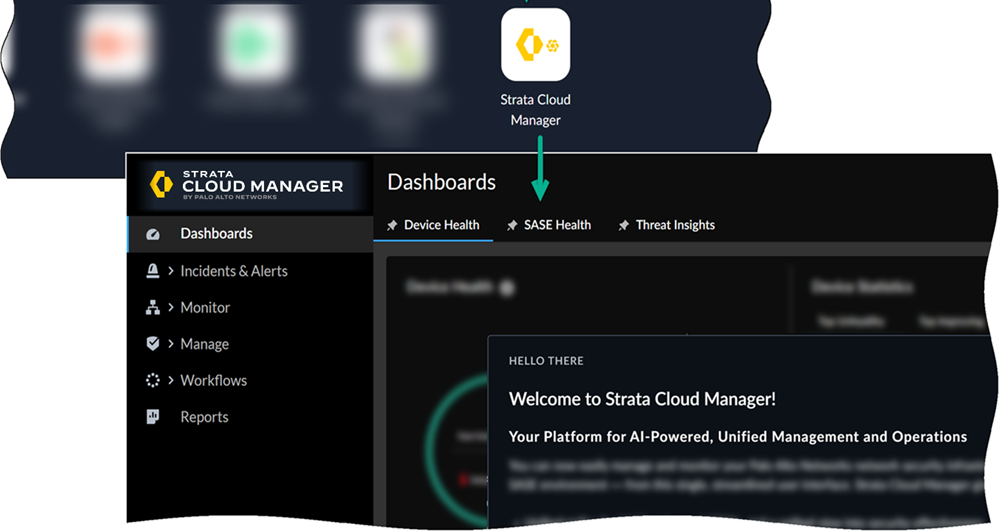
Moving forward, continue using the Strata Cloud Manager app to manage and
monitor your deployments.
Cisco Catalyst SD-WAN Integration
|
Supported in:
|
To use Cisco Catalyst SD-WAN with Prisma® Access,
you needed to create remote networks and IPSec tunnels manually. You can now onboard
a remote network using IPSec tunnels between Cisco Catalyst SD-WAN and Prisma Access
automatically. This feature automatically discovers eligible sites, creates the
necessary remote networks, and establishes IPSec tunnels between Cisco Catalyst
SD-WAN and Prisma Access, which significantly reduces manual configuration time and
enables faster deployment.
Contact your Palo Alto Networks account representative to enable this functionality.
After you enable the automatic creation of tunnels, configure the settings to
establish the connection between Prisma Access and Cisco Catalyst SD-WAN. View the
discovered sites that are eligible for the integration, and enable them accordingly.
This creates remote networks and establishes IPSec tunnels. Ensure to follow all the
requirements and prerequisites before you enable this functionality.
Credential Phishing Prevention Support
|
Supported in:
|
Phishing websites are fraudulent sites designed to steal user credentials
and gain access to your network. To defend against these attacks, it's critical to
prevent the submission of corporate credentials to unsanctioned sites. Prisma®
Access 4.2 introduces credential phishing prevention for
Panorama® managed and Cloud managed deployments, helping you secure remote
networks.
You can restrict where users submit corporate credentials by specifying the
action taken (alert, allow, block, or continue) when Prisma Access detects
submissions to specific URL categories. The continue action, for example, presents a
response page that warns users about potential account compromise and requires them
to acknowledge this risk before they can proceed to the requested site.
Credential phishing prevention works by scanning username and password
submissions for valid corporate credentials using your chosen credential detection method. While some
methods focus only on usernames, the domain credential filter method validates
both usernames and passwords against a directory server. Each detection method
varies in detection ability and requires a different User-ID™ configuration. When
Prisma Access detects a valid corporate credential submission, it enforces the
appropriate Security policy rule.
Prisma Access PAC File Endpoint for Explicit Proxy
|
Supported in:
|
Organizations often face administrative and security challenges managing firewall
exceptions and allow lists for the existing AWS S3-hosted PAC file. Prisma® Access solves this problem by rolling out a new,
simplified PAC file endpoint hosted directly by Palo Alto Networks,
significantly reducing administrative overhead and simplifying access.
This change is designed to make it easier for you to enable access to PAC files and
will be automatically reflected when you modify your PAC file.
GlobalProtect Migration Guidance
If you are using GlobalProtect
® in proxy mode or tunnel and proxy mode, and your devices
cannot access all domains under prismaaccess.com (due to a third-party VPN split tunnel
or firewall rule), allow your devices to access the new PAC file endpoint
(store.swg.prismaaccess.com) to avoid interruptions. For full migration
instructions, including required IP addresses and steps for overriding the PAC File
URL in GlobalProtect® App Settings, you can refer the PAC file guidelines.
User-Based Enforcement for Explicit Proxy Kerberos Authentication
|
Supported in:
|
Achieving consistent user identity-based control for undecrypted HTTPS traffic using
Kerberos authentication was previously impossible in Prisma® Access forcing administrators to accept
inconsistent policy enforcement. This new feature solves that challenge by allowing
you to implement user identity-based visibility and control using security policies
for undecrypted HTTPS traffic when a user or system authenticates using Kerberos.
This functionality ensures consistent user visibility and policy enforcement for all
HTTP-based traffic (undecrypted HTTPS, decrypted HTTPS, and HTTP traffic).
Furthermore, administrators no longer need to configure Trusted Source Addresses,
which simplifies your initial configuration and supports the use case in which your
branch locations employ dynamic egress IP addresses. Previously, you could
authenticate decrypted and undecrypted traffic, but enforcement was limited to
decrypted HTTPS traffic. Now, all HTTP-based traffic can authenticate and undergo
consistent user-based controls. This feature also eliminates the requirement for
users or systems to come from static IP addresses configured as Trusted Source
Addresses, simplifying initial configuration and supporting dynamic IP
addresses.
Local Zone Additions
|
Supported in:
|
Local zones place compute, storage,
database, and other services close to large population and industry centers. These
locations have their own compute locations.
Keep in mind the following guidelines when deploying local zones:
- Local zone locations do not support IPv6.
- Local zone locations do not use Palo Alto Networks registered IP addresses.
- 1 Gbps support for remote networks is not supported.
- Remote network and service connection node redundancy across availability zones is not available if you deploy them in the same local zone, as both nodes are provisioned in a single zone.
- These local zones do not use Palo Alto Networks registered IPs. If you have problems accessing URLs, report the website issue using https://reportasite.gpcloudservice.com/ or reach out to Palo Alto Networks support.
- Some SaaS applications might experience a higher latency in local zones when compared with non-local zone locations.
Enterprise DLP Support for AI Applications
|
Supported in:
|
ChatGPT is the fastest growing consumer application in history, with 100 million
monthly active users just two months after launch. Many organizations may be
surprised to learn that their employees are already using AI-based tools to
streamline their daily workflows, potentially putting sensitive company data at
risk. Software developers can upload proprietary code to help find and fix bugs,
while corporate communications teams can ask for help in crafting sensitive press
releases.
To safeguard against the growing risk of sensitive data leakage to AI apps and APIs,
we are excited to announce a new set of capabilities to secure ChatGPT and other AI
apps as part of our Next-Generation CASB solution that includes: Comprehensive app
usage visibility for complete monitoring of all SaaS usage activity, including
employee use of new and emerging generative AI apps that can put data at risk.
Granular SaaS application controls that safely enable employee access to
business-critical applications, while limiting or blocking access to high risk
apps—including generative AI apps—that have no legitimate business purpose.
While AI apps can significantly boost productivity and creative output, they also
pose a serious data security risk to modern enterprises. Enterprise Data Loss
Prevention (E-DLP) provides advanced data security that provides ML-based data
classification and data loss prevention to detect and stop company secrets,
personally identifiable information (PII), and other sensitive data from being
leaked to generative AI apps by well-intentioned employees.
New Prisma Access Location
|
Supported in:
|
- Sweden
- Kazakhstan
- Qatar
- Senegal
