Enterprise DLP
Create a Nested Data Profile
Table of Contents
Expand All
|
Collapse All
Enterprise DLP Docs
Create a Nested Data Profile
Create a single Enterprise Data Loss Prevention (E-DLP) data profile containing multiple data
profiles to simplify management of sensitive data leaving your network.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Enterprise DLP license
|
Enterprise Data Loss Prevention (E-DLP) supports creating a single data profile that contains
multiple nested data profiles. Creating a
single data profile that contains multiple nested data profiles allows you to
consolidate the match criteria to prevent exfiltration of sensitive data to a single
data profile that you can associate with a single Security policy rule. This allows
you to simplify the management of sensitive data leaving your network and reduces
the need to manage multiple Security policy rules and data profiles. Enterprise DLP synchronizes nested data profiles between Panorama and
Strata Cloud Manager
When you create a data profile that contains predefined data profiles and patterns,
be sure to consider the detection types used by the predefined
data patterns because the detection type determines how Enterprise DLP arrives
at a verdict for scanned files.
- Enterprise DLP does not support adding a nested data profile to another nested data profile.
- Enterprise DLP supports adding a data profile that includes an advanced detection method to an existing nested data profile if you did not include one when you originally created the data profile.
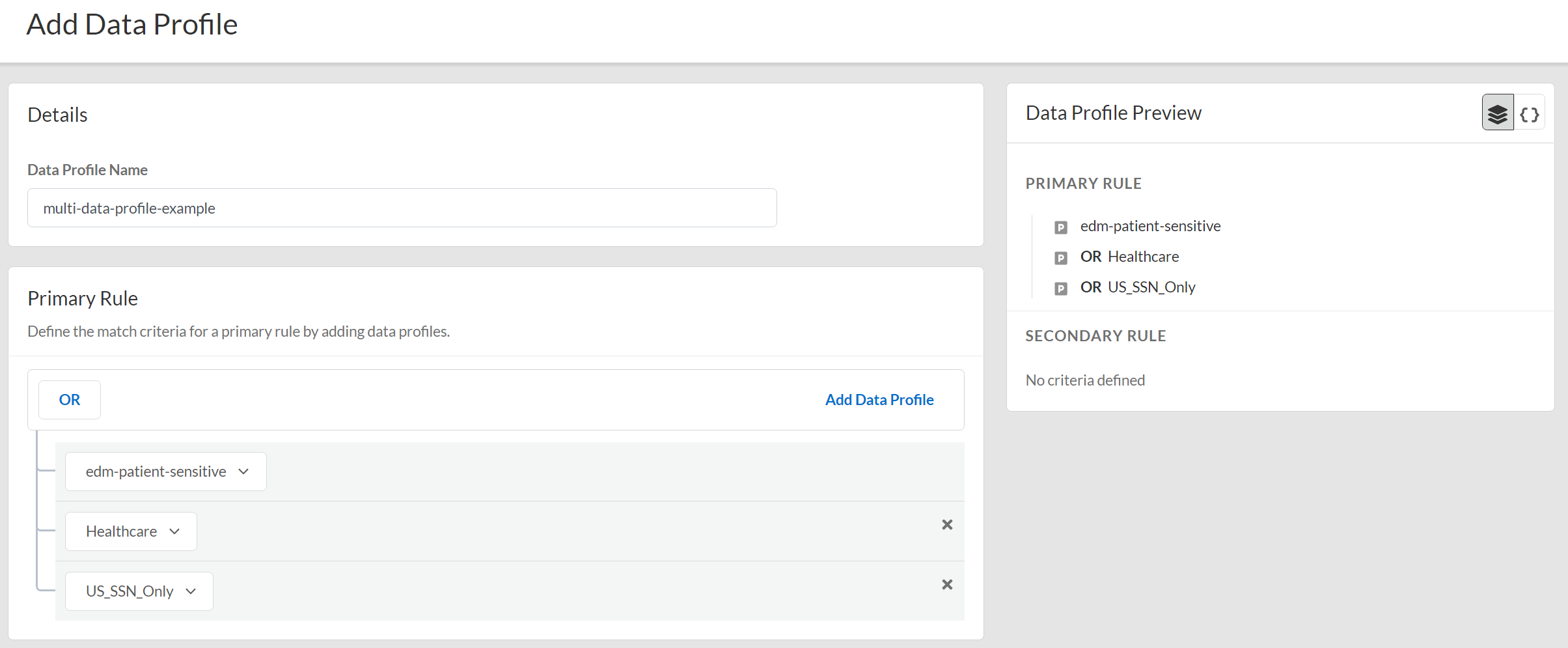
- Log in to Strata Cloud Manager.(Optional) Create your classic or advanced data profiles on Strata Cloud Manager.You can create a data profile that contains multiple data profiles using both predefined data profiles and custom data profiles you create.Select ManageConfigurationData Loss PreventionData Profiles and Add Data ProfilesNested Data Profiles.You can also create a new data profile by copying an existing data profile that already contains multiple data profiles. This allows you to quickly modify an existing data profile with additional data profile match criteria while preserving the original data profile from which the new data profile was copied.Enterprise DLP appends the name of copied a data profile with Copy - <name_of_original_data_profile>.Enter the Data Profile Name.Configure the Primary Rule for the data profile.Add Data Profile to add predefined or custom data profiles. Repeat this step to include additional data profiles.Add the data profile match criteria for allowed traffic to the Primary Rule. Add data profiles for blocked traffic to either Primary Rule or Secondary Rule.A data profile containing multiple data profiles support any combination of data profiles with data patterns only, data patterns and EDM data sets, and EDM data sets only.Nested data profiles support only the OR operator.
![]() (Optional) Configure a Secondary Rule.Add Data Profile to add predefined or custom data profiles. Repeat this step to include additional data profiles.Data profile match criteria added to the Secondary Rule block all traffic that meets the match criteria for the data profile by default and can’t be modified. If you want to allow traffic that matches a data profile match criteria, add it to the Primary Rule.A data profile containing multiple data profiles support any combination of data profiles with data patterns only, data patterns and EDM data sets, and EDM data sets only.Nested data profiles support only the OR operator.Save the data profile.Test a Data Profile to verify it accurately detects the sensitive data you configured it to detect.Verify that the data profile you created.
(Optional) Configure a Secondary Rule.Add Data Profile to add predefined or custom data profiles. Repeat this step to include additional data profiles.Data profile match criteria added to the Secondary Rule block all traffic that meets the match criteria for the data profile by default and can’t be modified. If you want to allow traffic that matches a data profile match criteria, add it to the Primary Rule.A data profile containing multiple data profiles support any combination of data profiles with data patterns only, data patterns and EDM data sets, and EDM data sets only.Nested data profiles support only the OR operator.Save the data profile.Test a Data Profile to verify it accurately detects the sensitive data you configured it to detect.Verify that the data profile you created.- Strata Cloud Manager—Log in to Strata Cloud Manager and select ManageConfigurationData Loss PreventionData Profiles and search for the data profile you created.
- Panorama and Prisma Access (Managed by Panorama)See Update a Data Profile for more information on which data profile settings are editable on Panorama for a data profile created on Strata Cloud Manager.If the data profile has both Primary and Secondary Patterns, changing the data profile Action on Panorama deletes all Secondary Pattern match criteria.
- Select the data profile created on Strata Cloud Manager.
- Set the data profile Action to Block traffic that matches the data profile match criteria.
- Select CommitCommit to Panorama and Commit.
- Click OK.
- Select CommitPush to Devices and Edit Selections.
- Select Device Groups and Include Device and Network Templates.
- Push your configuration changes to your managed firewalls that are using Enterprise DLP.
Modify a DLP Rule on Strata Cloud Manager to Attach the data profile to a Security policy rule.The DLP Rule defines the type of traffic to inspect, the impacted file types, action, log severity, and more for the data profile match criteria. Enterprise DLP automatically creates a DLP rule with an identical name as the data profile from which it was created.