Prisma Access
Proxy Mode on Remote Networks
Table of Contents
Expand All
|
Collapse All
Prisma Access Docs
-
- 6.1 Preferred and Innovation
- 6.0 Preferred and Innovation
- 5.2 Preferred and Innovation
- 5.1 Preferred and Innovation
- 5.0 Preferred and Innovation
- 4.2 Preferred
- 4.1 Preferred
- 4.0 Preferred
- 3.2 Preferred and Innovation
- 3.1 Preferred and Innovation
- 3.0 Preferred and Innovation
- 2.2 Preferred
-
-
- 4.0 & Later
- Prisma Access China
-
-
Proxy Mode on Remote Networks
Learn how to use multicast and unicast IP address to secure mobile users and devices at
Remote Networks with an explicit proxy.
| Where Can I Use This? | What Do I Need? |
|---|---|
If you'd like to enable Private Source IP-based
visibility and enforcement on explicit proxy in your Prisma Access environment, get in touch with your account
team to learn more. |
|
Proxy mode on remote networks helps to secure outbound internet traffic for users and
servers in your branches that need PAC-based connection method due to networking or
compliance reasons.
You no longer need a Mobile User license for headless
endpoints that connect to explicit proxy from remote sites. The new site-based
license allows traffic to explicit proxy only from known site IP addresses or
through remote networks.
You can use Proxy Mode for remote networks to:
- Secure Internet-bound traffic from branch sites that use nondefault routes.
- Secure Internet-bound traffic from your branches without backhauling it to a data center or HQ site.
- Connect to Prisma Access explicit proxy over private IP addresses.
Prisma Access provides you with four anycast IP addresses globally, and one unicast IP address per remote network, that you use to forward traffic to explicit proxy.
- Enforce security controls and get visibility based on Source IP for the Systems in the branch.
- Skip authentication for servers based on the Source IP address.
- Connect to Prisma Access from your branch through an IPSec Tunnel.
- If you require more than 1,000 Mbps of bandwidth, you can create a high-bandwidth remote network connection using multiple Remote Network connections and specify the explicit proxy anycast and unicast addresses in each connection.
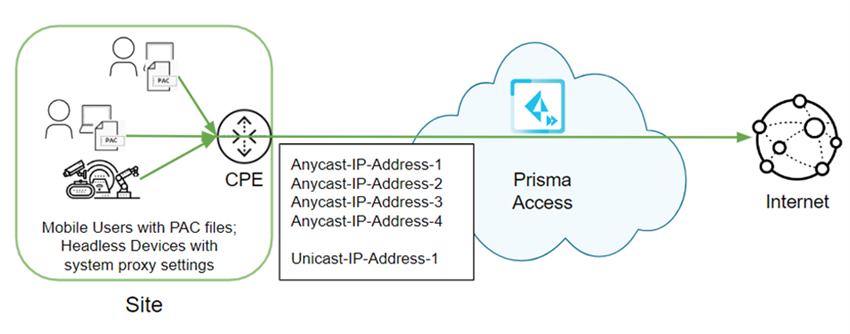
The following diagram shows a remote network that has been configured for a site that
has no default route configured. To protect users and headless devices at the site
using explicit proxy, the administrator has made the following configuration
changes:
- Onboarded remote networks and explicit proxy locations and have retrieved the anycast and unicast IP addresses that Prisma Access takes from its infrastructure subnet.You can also create a hostname for explicit proxy-directed traffic and add the explicit proxy unicast and anycast IP addresses to that hostname.
- Configured the customer premises equipment (CPE) to forward explicit proxy traffic to these anycast and unicast addresses.Use the anycast IP addresses in the PAC file to have the CPE select from any onboarded remote network tunnel to forward traffic to explicit proxy. Use the unicast address to have the CPE forward traffic through a specific remote network tunnel that connects directly from the CPE. In this example, you can use either anycast or unicast addresses, since the traffic is going only through one remote network IPSec tunnel.
- Specified these IP addresses in the PAC files of the users’ endpoints and in the system proxy settings of the headless devices.
After configuration is complete, Prisma Access forwards the traffic from the
remote network tunnel to explicit proxy.
Proxy Mode on Remote Networks (Strata Cloud Manager)
Learn how to use multicast and unicast IP address to
secure mobile users and devices at Remote Networks with an Explicit
Proxy.
To secure users at remote networks using explicit proxy in Prisma Access (Managed by Strata Cloud Manager),
complete the following steps.
- Configure your explicit proxy setup and onboard the explicit proxy locations you want to add.Onboard your remote networks if you have not done so already.You must enable Prisma Access remote networks in the locations that are supported with explicit proxy.Push Config, being sure that Mobile Users—Remote Workforce and Remote Networks are selected in the Push scope.The push operation retrieves and anycast addresses you need to integrated explicit proxy with the remote network.Get the anycast IP addresses you use for your explicit proxy or remote network deployment.
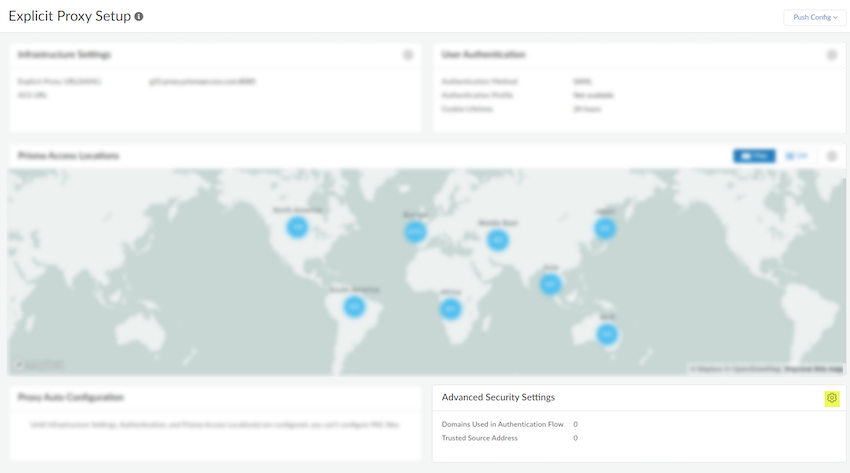
- Go to ConfigurationNGFW and Prisma AccessConfiguration ScopePrisma AccessExplicit ProxyAdvanced Security Settings.
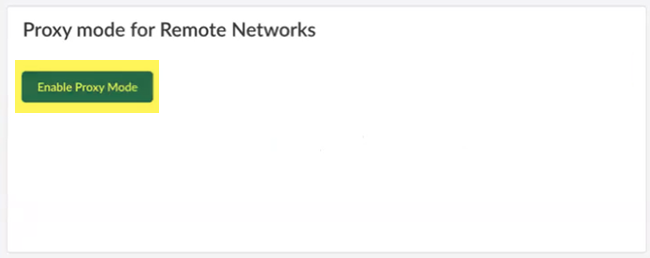
![]() If you want to forward traffic to explicit proxy from your branches through a secure IPSec tunnel, Enable Proxy Mode.
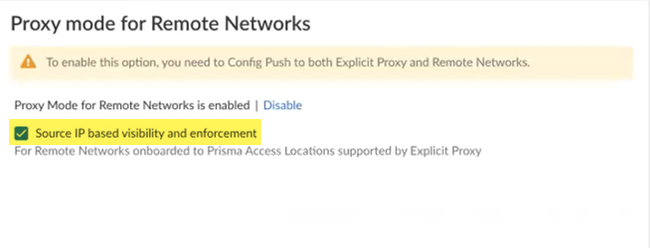
If you want to forward traffic to explicit proxy from your branches through a secure IPSec tunnel, Enable Proxy Mode.![]() To leverage the source IP addresses of the systems in your branch locations that are forwarding traffic to explicit proxy, select Source IP based visibility and enforcement.This functionality has these requirements:
To leverage the source IP addresses of the systems in your branch locations that are forwarding traffic to explicit proxy, select Source IP based visibility and enforcement.This functionality has these requirements:- A minimum Prisma Access dataplane of 10.2.4
- You must use only remote network locations supported with Explicit Proxy.
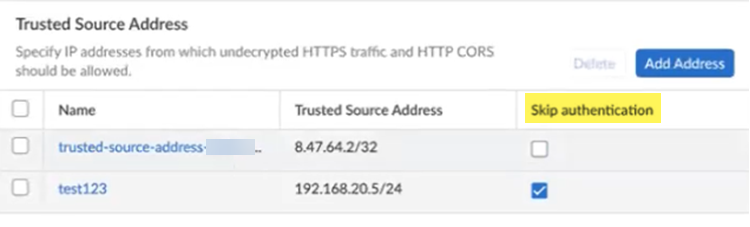
![]() Add a policy to allow traffic bound to anycast and unicast IP on remote networks. If you have enabled Source IP visibility and enforcement, use the Source IP field in Security policies in explicit proxy to secure the traffic. You need additional policies in the remote networks.(Optional) To bypass authentication of any trusted source addresses you entered, specify IP addresses that should have authentication skipped in the Trusted Source Address area and select Skip authentication.You can use Skip authentication with Source IP based visibility and enforcement to Skip authentication of headless systems that can't authenticate, set up security policies, and get visibility of the traffic on Prisma Access Explicit Proxy.You can add either IP addresses or subnets. A maximum of 100,000 IP addresses are supported after expanding the subnets.
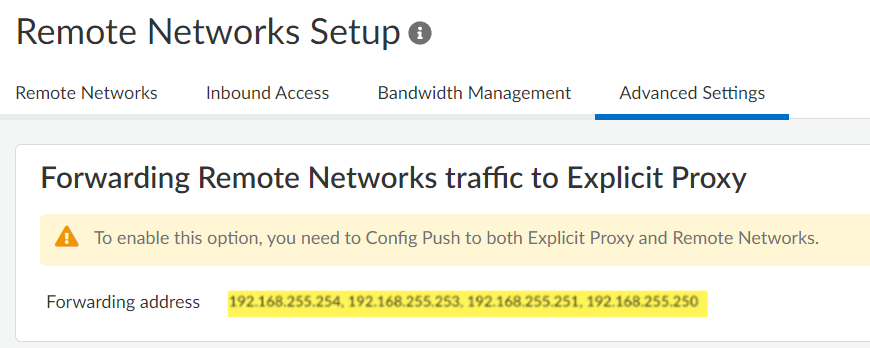
Add a policy to allow traffic bound to anycast and unicast IP on remote networks. If you have enabled Source IP visibility and enforcement, use the Source IP field in Security policies in explicit proxy to secure the traffic. You need additional policies in the remote networks.(Optional) To bypass authentication of any trusted source addresses you entered, specify IP addresses that should have authentication skipped in the Trusted Source Address area and select Skip authentication.You can use Skip authentication with Source IP based visibility and enforcement to Skip authentication of headless systems that can't authenticate, set up security policies, and get visibility of the traffic on Prisma Access Explicit Proxy.You can add either IP addresses or subnets. A maximum of 100,000 IP addresses are supported after expanding the subnets.![]() Go to ConfigurationNGFW and Prisma AccessConfiguration ScopePrisma AccessRemote Networks.Push Config, being sure that Mobile Users—Remote Workforce and Remote Networks are selected in the Push scope.Go to Advanced Settings in your Remote Networks Setup and find the anycast IP addresses used to forward traffic to explicit proxy.
Go to ConfigurationNGFW and Prisma AccessConfiguration ScopePrisma AccessRemote Networks.Push Config, being sure that Mobile Users—Remote Workforce and Remote Networks are selected in the Push scope.Go to Advanced Settings in your Remote Networks Setup and find the anycast IP addresses used to forward traffic to explicit proxy.![]() (Optional) Find the unicast address to use for your explicit proxy or remote network deployment.Use the unicast IP address in the PAC file only if you want to target a specific remote network to forward traffic to explicit proxy. If you want to use all deployed remote networks to forward traffic to explicit proxy, use the anycast addresses.
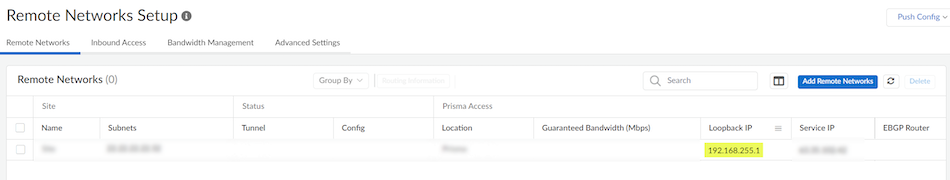
(Optional) Find the unicast address to use for your explicit proxy or remote network deployment.Use the unicast IP address in the PAC file only if you want to target a specific remote network to forward traffic to explicit proxy. If you want to use all deployed remote networks to forward traffic to explicit proxy, use the anycast addresses.- Go to ConfigurationNGFW and Prisma AccessConfiguration ScopePrisma AccessRemote Networks.Make a note of the Loopback IP address.If you have IPv4 and IPv6 addresses, make a note of the IPv4 address.
![]()
Proxy Mode on Remote Networks (Panorama)
Learn how to use multicast and unicast IP address to secure mobile users and devices at Remote Networks with an Explicit Proxy.To secure users at remote networks using explicit proxy in Prisma Access (Managed by Panorama) Access, complete the following steps.- Configure your explicit proxy deployment and onboard the explicit proxy locations you want to add.Retrieve the anycast IP addresses you use for your explicit proxy/remote network deployment.
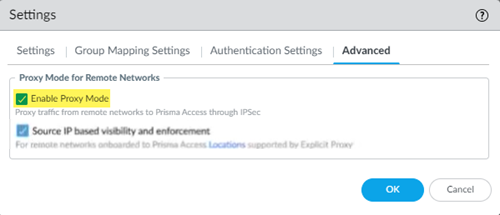
- Select PanoramaCloud ServicesConfigurationMobile Users—Explicit Proxy.Select the gear icon to edit the Settings.Select Enable Proxy Mode.
![]() To leverage the private IP addresses of the systems in your branch locations that are forwarding traffic to explicit proxy, select Source IP based visibility and enforcement.This functionality has these requirements:
To leverage the private IP addresses of the systems in your branch locations that are forwarding traffic to explicit proxy, select Source IP based visibility and enforcement.This functionality has these requirements:- A minimum Prisma Access dataplane of 10.2.4
- A Prisma Access (Managed by Panorama) deployment with a minimum Cloud Services plugin of 4.1
- You must use only remote network locations supported with explicit proxy.
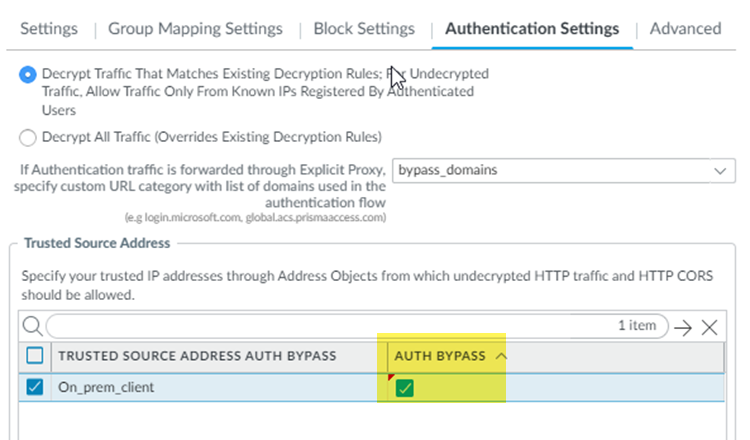
![]() Add a policy to allow traffic bound to anycast and unicast IP on remote networks. If you have enabled Source IP visibility and enforcement, use the Source IP field in Security policies in explicit proxy to secure the traffic. You need additional policies in the remote networks.(Optional) Under Authentication Settings, enter any IP addresses from which undecrypted HTTP or HTTP Cross-Origin Resource Sharing (CORS) traffic should be allowed to the Trusted Source Address Auth Bypass.Add the IP addresses to IP address-based Address Objects and Add the address objects in the field.Enter a maximum of 100,000 addresses. Make sure that the address object uses IP addresses only.(Optional) To bypass authentication of any trusted source addresses you entered, select Auth Bypass.You can use Auth Bypass with Source IP based visibility and enforcement to skip authentication of headless systems that can't authenticate, set up security policies, and get visibility of the traffic on Prisma Access explicit proxy.You can add either IP addresses or subnets. A maximum of 100,000 IP addresses are supported after expanding the subnets.
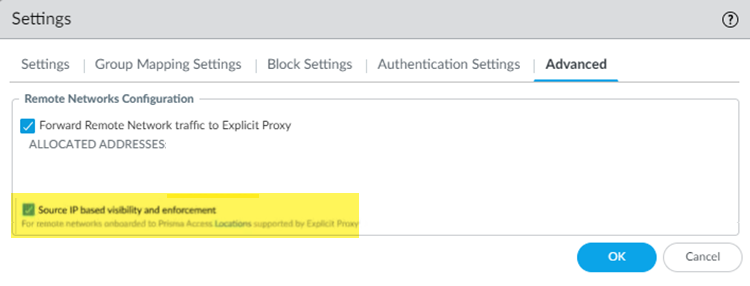
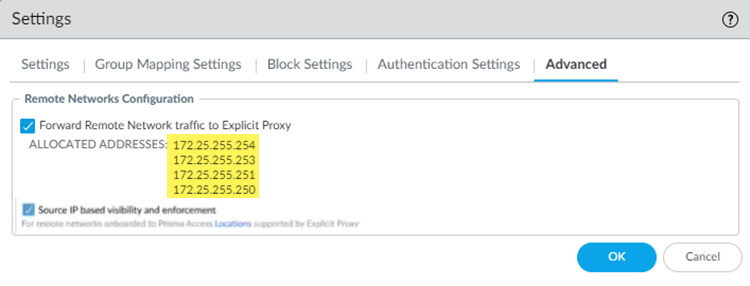
Add a policy to allow traffic bound to anycast and unicast IP on remote networks. If you have enabled Source IP visibility and enforcement, use the Source IP field in Security policies in explicit proxy to secure the traffic. You need additional policies in the remote networks.(Optional) Under Authentication Settings, enter any IP addresses from which undecrypted HTTP or HTTP Cross-Origin Resource Sharing (CORS) traffic should be allowed to the Trusted Source Address Auth Bypass.Add the IP addresses to IP address-based Address Objects and Add the address objects in the field.Enter a maximum of 100,000 addresses. Make sure that the address object uses IP addresses only.(Optional) To bypass authentication of any trusted source addresses you entered, select Auth Bypass.You can use Auth Bypass with Source IP based visibility and enforcement to skip authentication of headless systems that can't authenticate, set up security policies, and get visibility of the traffic on Prisma Access explicit proxy.You can add either IP addresses or subnets. A maximum of 100,000 IP addresses are supported after expanding the subnets.![]() Select PanoramaCloud ServicesConfigurationRemote Networks.Onboard your Remote Network Locations if you have not done so already.You must enable Prisma Access remote networks in the locations that are supported with explicit proxy.Select CommitCommit and Push.Edit Selections and, in the Prisma Access tab, make sure Prisma Access for networks is selected in the Push Scope, then click OK.Commit and Push your changes.You must perform a commit and push for your remote networks for Prisma Access to retrieve the IP addresses used in an explicit proxy/remote network deployment.Return to the explicit proxy Settings (PanoramaCloud ServicesConfigurationMobile Users—Explicit ProxySettingsAdvanced) and make a note of the ALLOCATED ADDRESSES that display in under Remote Networks Configuration.
Select PanoramaCloud ServicesConfigurationRemote Networks.Onboard your Remote Network Locations if you have not done so already.You must enable Prisma Access remote networks in the locations that are supported with explicit proxy.Select CommitCommit and Push.Edit Selections and, in the Prisma Access tab, make sure Prisma Access for networks is selected in the Push Scope, then click OK.Commit and Push your changes.You must perform a commit and push for your remote networks for Prisma Access to retrieve the IP addresses used in an explicit proxy/remote network deployment.Return to the explicit proxy Settings (PanoramaCloud ServicesConfigurationMobile Users—Explicit ProxySettingsAdvanced) and make a note of the ALLOCATED ADDRESSES that display in under Remote Networks Configuration.![]() (Optional) Find the unicast address you use for your explicit proxy/remote network deployment.Use the unicast IP address in the PAC file only if you want to target a specific remote network to forward traffic to explicit proxy. If you want to use all deployed remote networks to forward traffic to explicit proxy, use the anycast addresses.
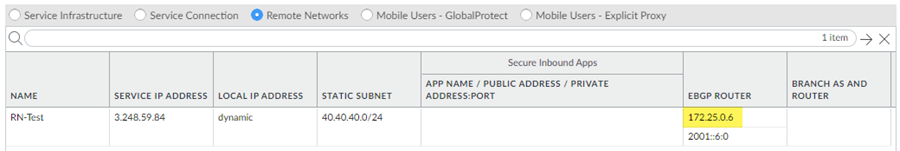
(Optional) Find the unicast address you use for your explicit proxy/remote network deployment.Use the unicast IP address in the PAC file only if you want to target a specific remote network to forward traffic to explicit proxy. If you want to use all deployed remote networks to forward traffic to explicit proxy, use the anycast addresses.- Select PanoramaCloud ServicesStatusNetwork DetailsRemote Networks.Make a note of the EBGP Router address.If you have IPv4 and IPv6 addresses, make a note of the IPv4 address.This address is also known as the loopback address. If you have made configuration changes that changed the EBGP router address, you can retrieve the loopback IP address using the Prisma Access legacy API.
![]() Ensure that the CPE in your network is set up correctly for endpoints to forward traffic to explicit proxy via the anycast and unicast IP addresses.
Ensure that the CPE in your network is set up correctly for endpoints to forward traffic to explicit proxy via the anycast and unicast IP addresses.