SaaS Security
Begin Scanning a Gmail App
Table of Contents
Expand All
|
Collapse All
SaaS Security Docs
Begin Scanning a Gmail App
Add your Gmail app to Data Security to begin scanning
and monitoring assets for possible security risks.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Data Security license:
|
Ensure that the Super Admin account
added to the Strata Cloud Manager for onboarding the Gmail app has logged in at
least once into the Strata Cloud Manager. Only then will the account be enabled.
Onboarding will fail if this account has never logged into the Strata Cloud
Manager.
Support for automated remediation
capabilities varies by SaaS application.
Supported Content
|
Support For
|
Details
|
|---|---|
|
Scan Content
| Email content, Attachments |
|
Backward Scan
|
No
|
|
Forward Scan
|
Yes
|
|
Rescan
|
No
|
|
Selective Scan
|
No
|
|
Exposure
|
Internal, External
For internal emails, only attachments are scanned. For
external emails, both email content and attachments are
scanned.
|
|
Remediation Actions
|
|
|
Post-Remediation Actions (Actions after Admin
Quarantine):
You can delete, restore, or download a quarantined file
after performing a remediation action (for example
quarantine or incident generation).
|
|
|
Notifications
|
|
|
User Activities
|
|
|
Snippet Support
|
Yes
|
|
Known License and Version restrictions
|
Supported Versions
|
|
Caveats and Notes
|
None
|
Onboard Gmail App
- Prerequisites to be completed on Google
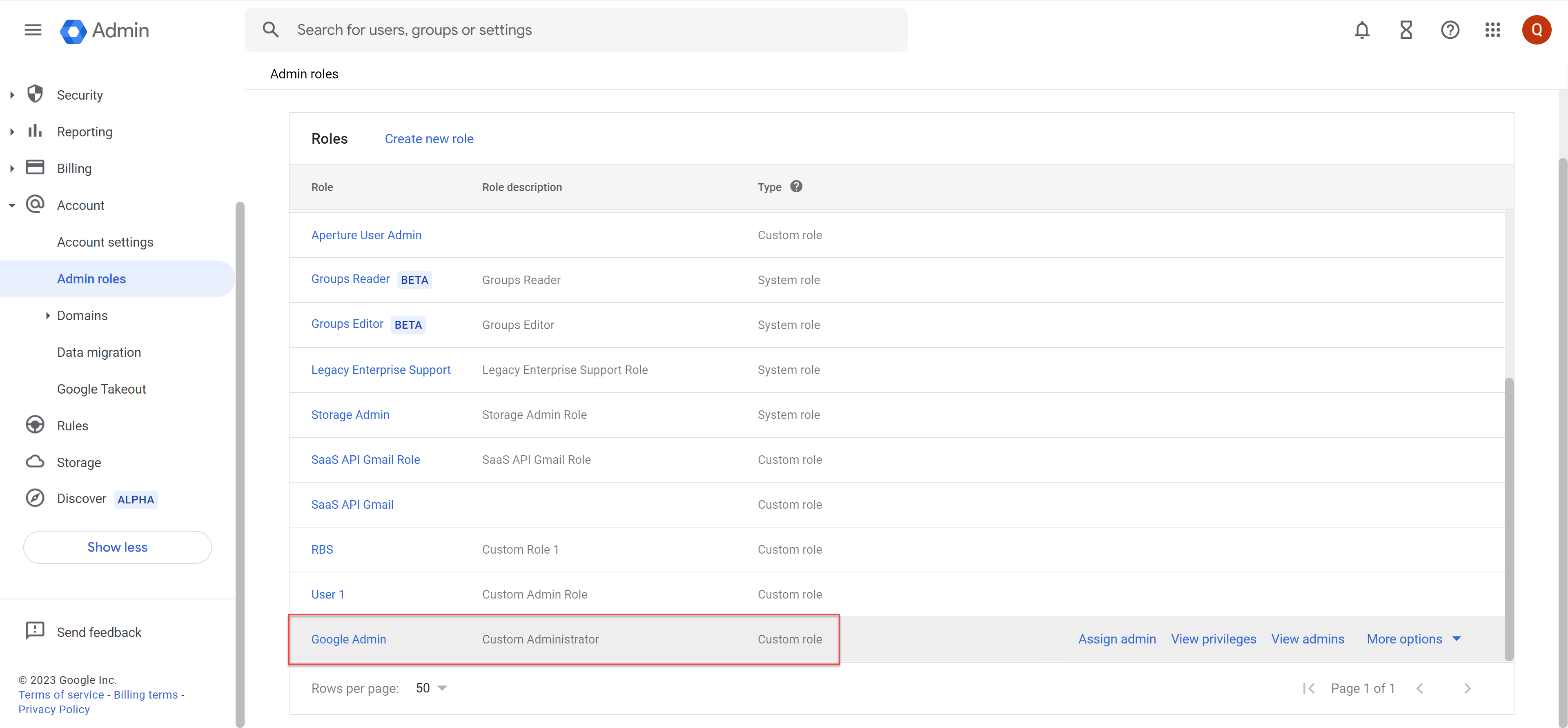
- Verify that your Google administrator account is assigned as a custom admin role:
- that can read, write, and relocate assets in the app.
- that has API access. API access provides visibility into the assets in Gmail and enables Data Security to monitor the sharing of assets.
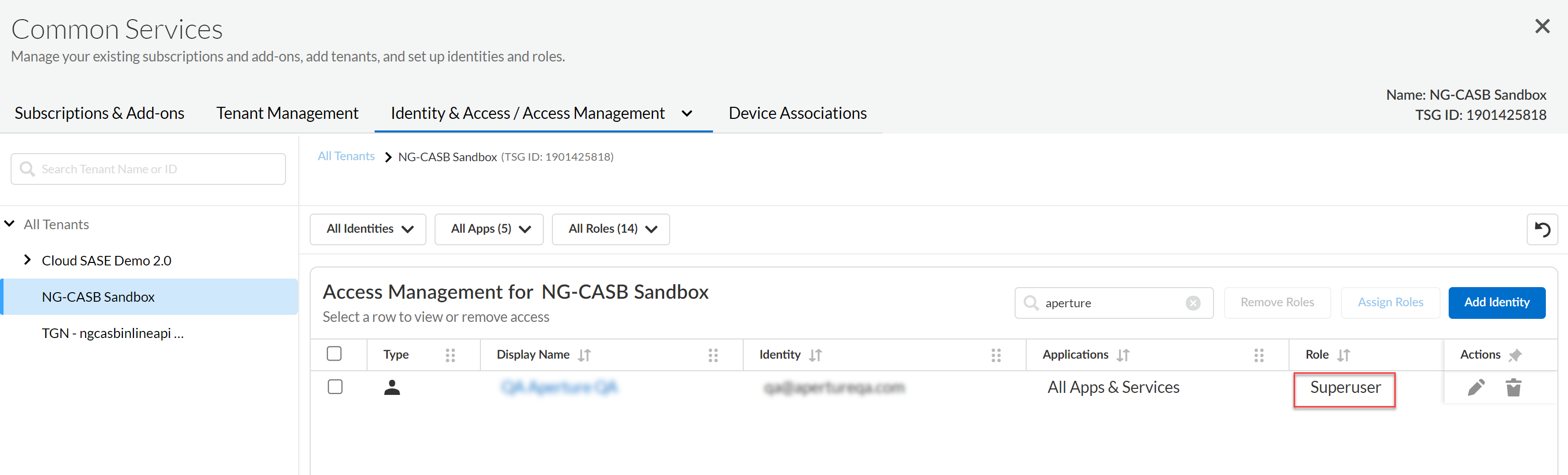
![]() (Recommended) Add your Gmail domain as an internal domain.Log in to Google Marketplace using an admin account with Super admin role permissions. To do this, go to Google Workspace Marketplace and log out of Google Marketplace to ensure that you're not logged in as a user other than an account with Super admin role permissions. Log in again to Google Marketplace using an account that has Super admin role permissions.Add the email address of the custom admin to Data Security and assign a Superuser role.
(Recommended) Add your Gmail domain as an internal domain.Log in to Google Marketplace using an admin account with Super admin role permissions. To do this, go to Google Workspace Marketplace and log out of Google Marketplace to ensure that you're not logged in as a user other than an account with Super admin role permissions. Log in again to Google Marketplace using an account that has Super admin role permissions.Add the email address of the custom admin to Data Security and assign a Superuser role.![]() Next step: Proceed to Add Gmail App to Data Security.Add Gmail App to Data Security
Next step: Proceed to Add Gmail App to Data Security.Add Gmail App to Data Security- Log in to Strata Cloud Manager,Select ConfigurationSaaS SecurityData SecurityApplicationsAdd ApplicationGmail.
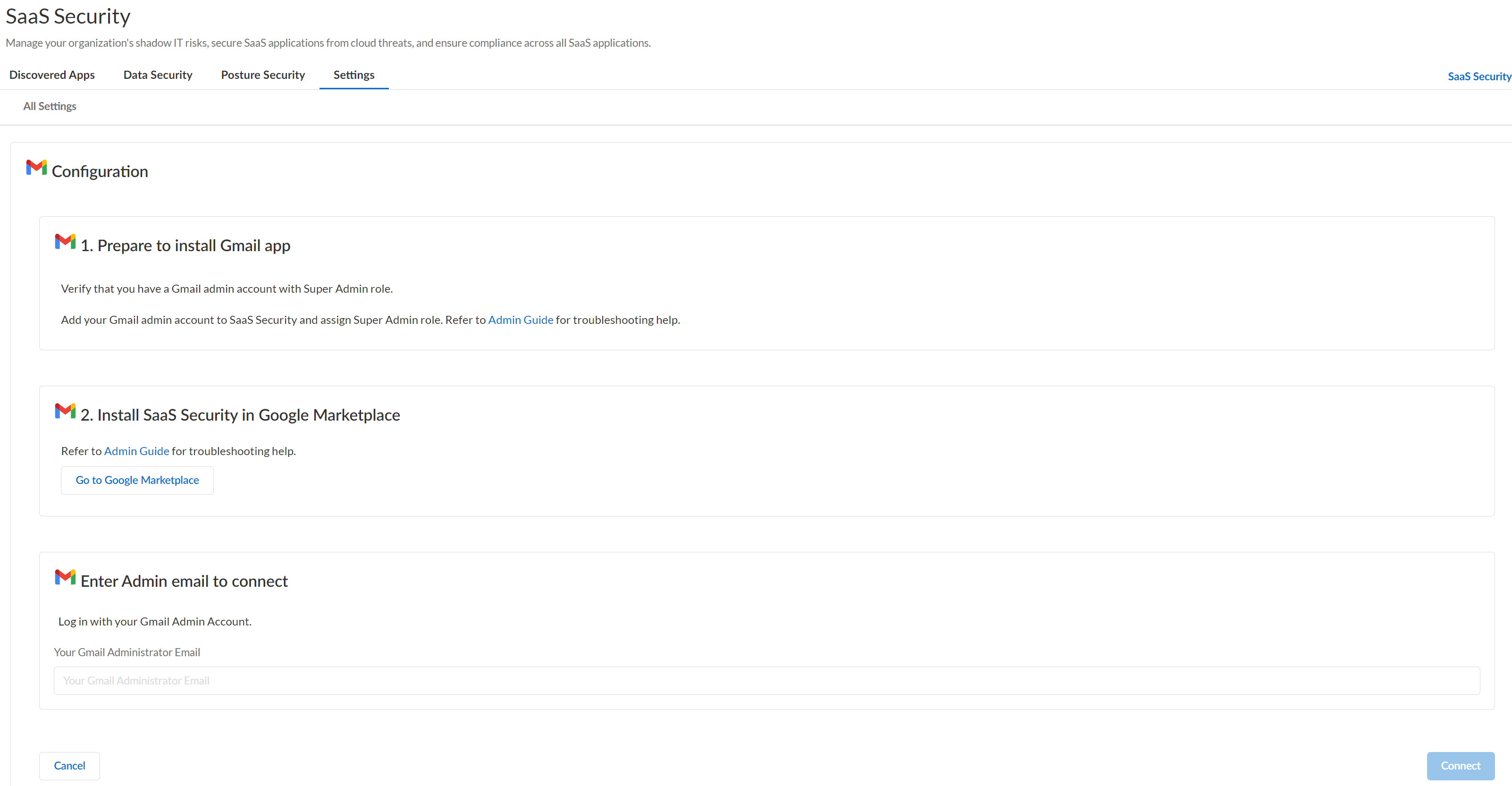
![]()
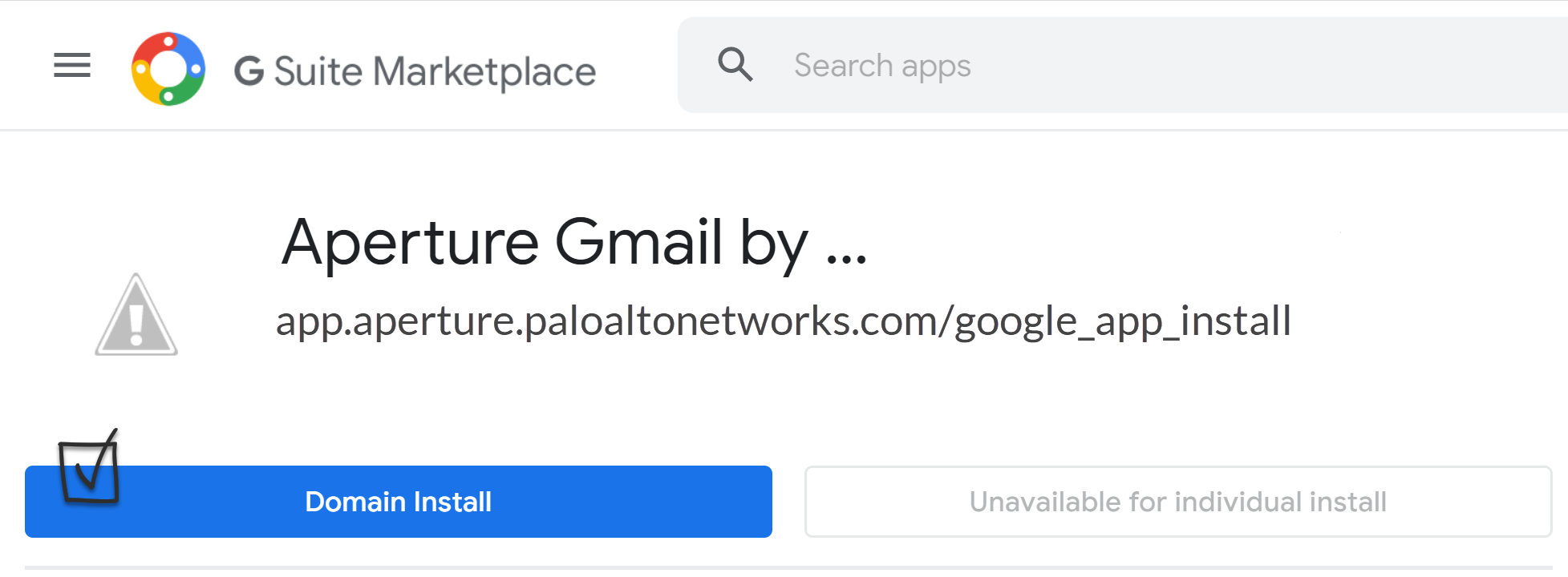
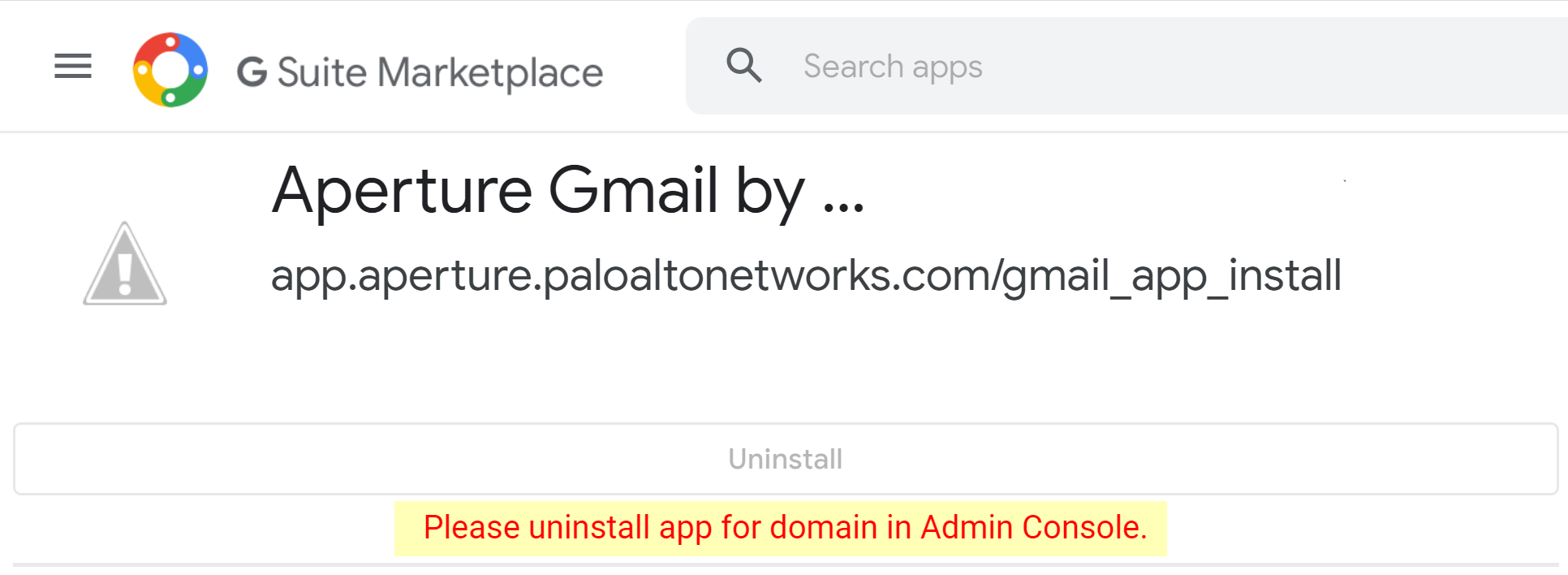
![]() As indicated in the onscreen instructions in Step 1, complete the prerequisites on Google, if you haven’t already done so.Follow the onscreen instructions in Step 2: Go to Google Marketplace. Afterward, the Domain Install button is replaced by a disabled Uninstall button with a message that reads Please uninstall app for domain in Admin Console. This behavior is expected.Select Domain Install on the Google Marketplace page.Don't go to the link provided. Doing so aborts the onboarding process. If you inadvertently do so, simply repeat the process starting with adding the Gmail app to Data Security.
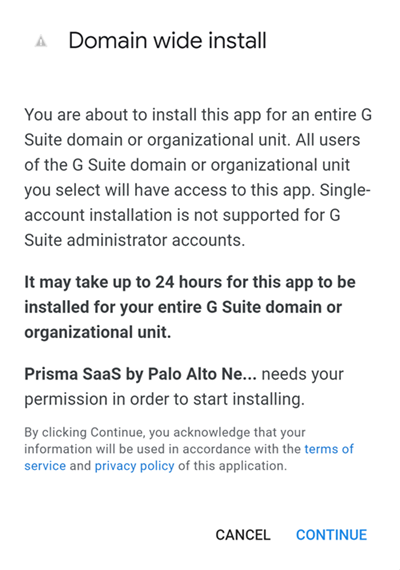
As indicated in the onscreen instructions in Step 1, complete the prerequisites on Google, if you haven’t already done so.Follow the onscreen instructions in Step 2: Go to Google Marketplace. Afterward, the Domain Install button is replaced by a disabled Uninstall button with a message that reads Please uninstall app for domain in Admin Console. This behavior is expected.Select Domain Install on the Google Marketplace page.Don't go to the link provided. Doing so aborts the onboarding process. If you inadvertently do so, simply repeat the process starting with adding the Gmail app to Data Security.![]() Click Continue to proceed with the Domain wide install process.
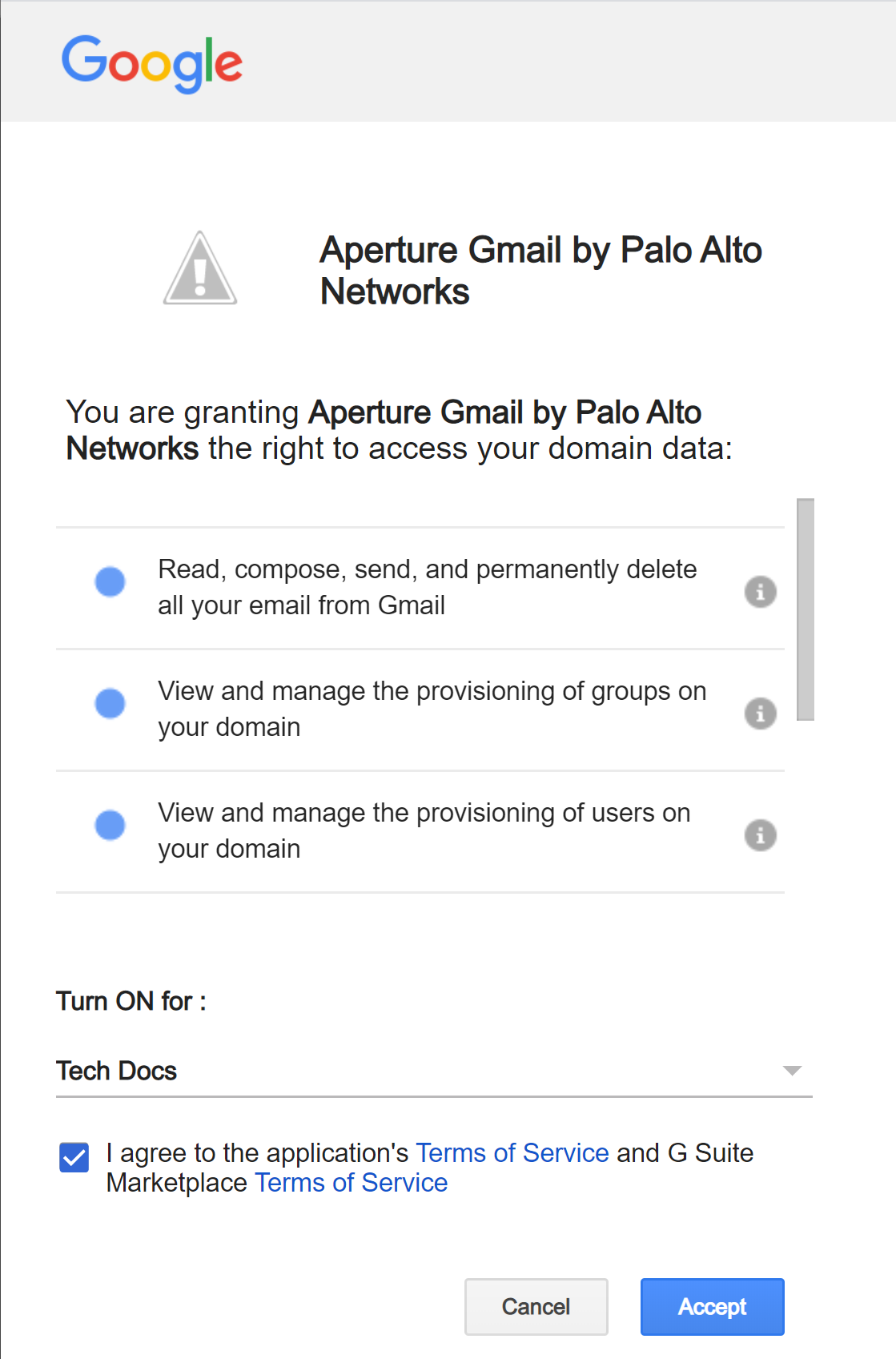
Click Continue to proceed with the Domain wide install process.![]() Review and Accept the requested permissions.Data Security requires these permissions to scan your assets on Gmail. A new browser window opens in the foreground.
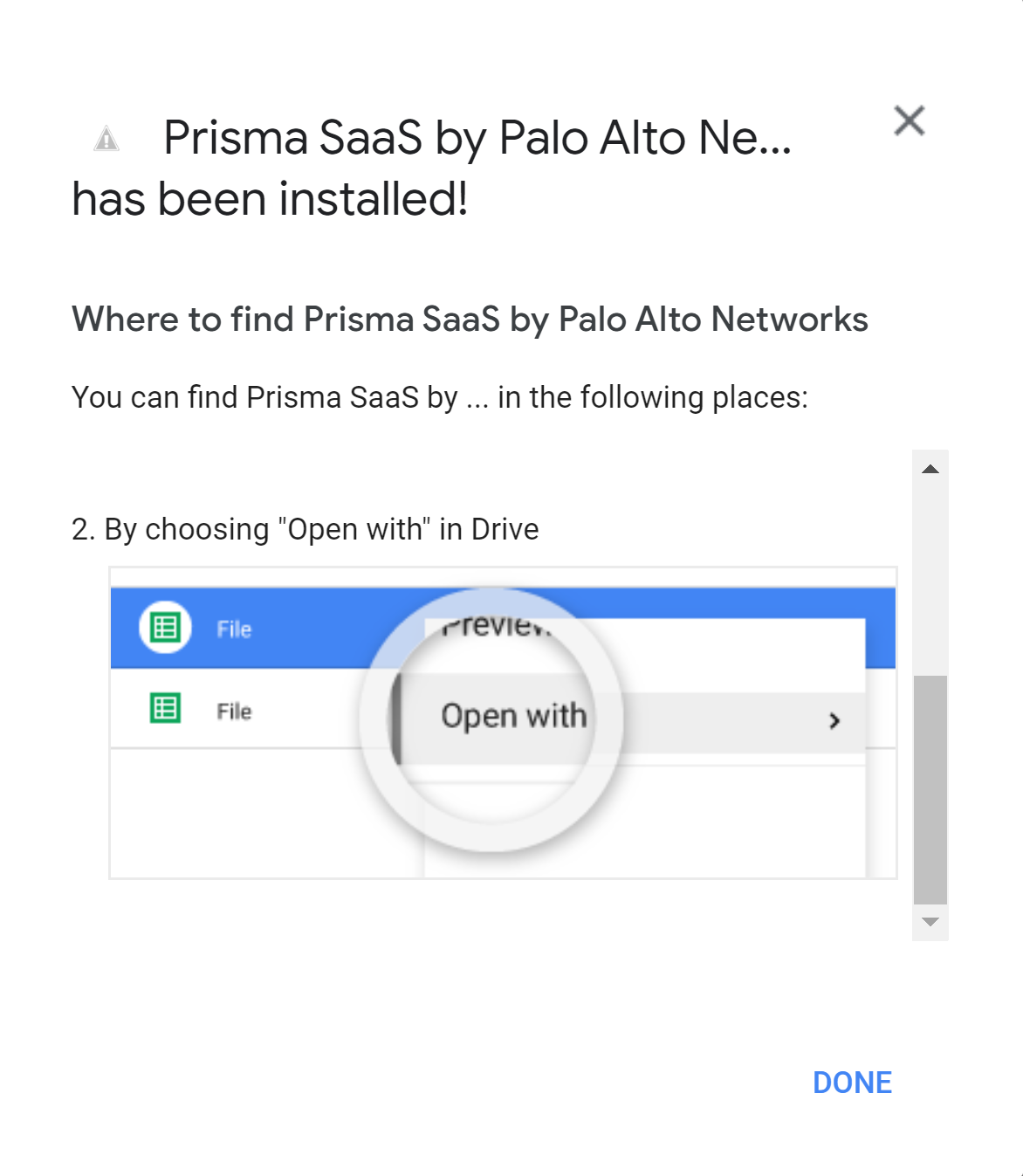
Review and Accept the requested permissions.Data Security requires these permissions to scan your assets on Gmail. A new browser window opens in the foreground.![]() Click Done.
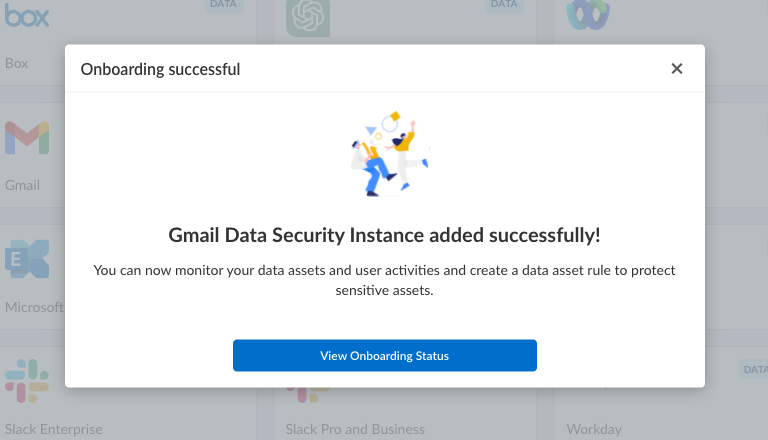
Click Done.![]() Follow the onscreen instructions in Step 3: Connect to Gmail Account.After you enter the Gmail admin email, on successful onboarding, the following message is displayed.
Follow the onscreen instructions in Step 3: Connect to Gmail Account.After you enter the Gmail admin email, on successful onboarding, the following message is displayed.![]() Click View Onboarding Status to know if the validation checks have passed. You will be able to start scanning only after successful validation.Optional Data Security adds the new Gmail app to the Cloud Apps list as Gmail n, where n is the number of Gmail app instances that you connected to Data Security. For example, if you added one Gmail app, the name displays as Gmail 1 . You’ll specify a descriptive name soon.Next step: Proceed to Start Scanning and Monitor Results and begin scanning your assets.
Click View Onboarding Status to know if the validation checks have passed. You will be able to start scanning only after successful validation.Optional Data Security adds the new Gmail app to the Cloud Apps list as Gmail n, where n is the number of Gmail app instances that you connected to Data Security. For example, if you added one Gmail app, the name displays as Gmail 1 . You’ll specify a descriptive name soon.Next step: Proceed to Start Scanning and Monitor Results and begin scanning your assets.Troubleshooting Onboarding for Gmail App
To ensure that your app has onboarded correctly without any issues in authentication or permissions, Data Security performs validation checks between the onboarding and scanning process. You can start scanning only after a successful validation. For Gmail, the following three validations happen:- App Authentication
- User Permission
- Validating Permissions
After the validation is successful, Data Security displays the sample data assets and sample user activities.![]() If the App Authentication, User Permission, or Validating Permissions checks fail, try the following:
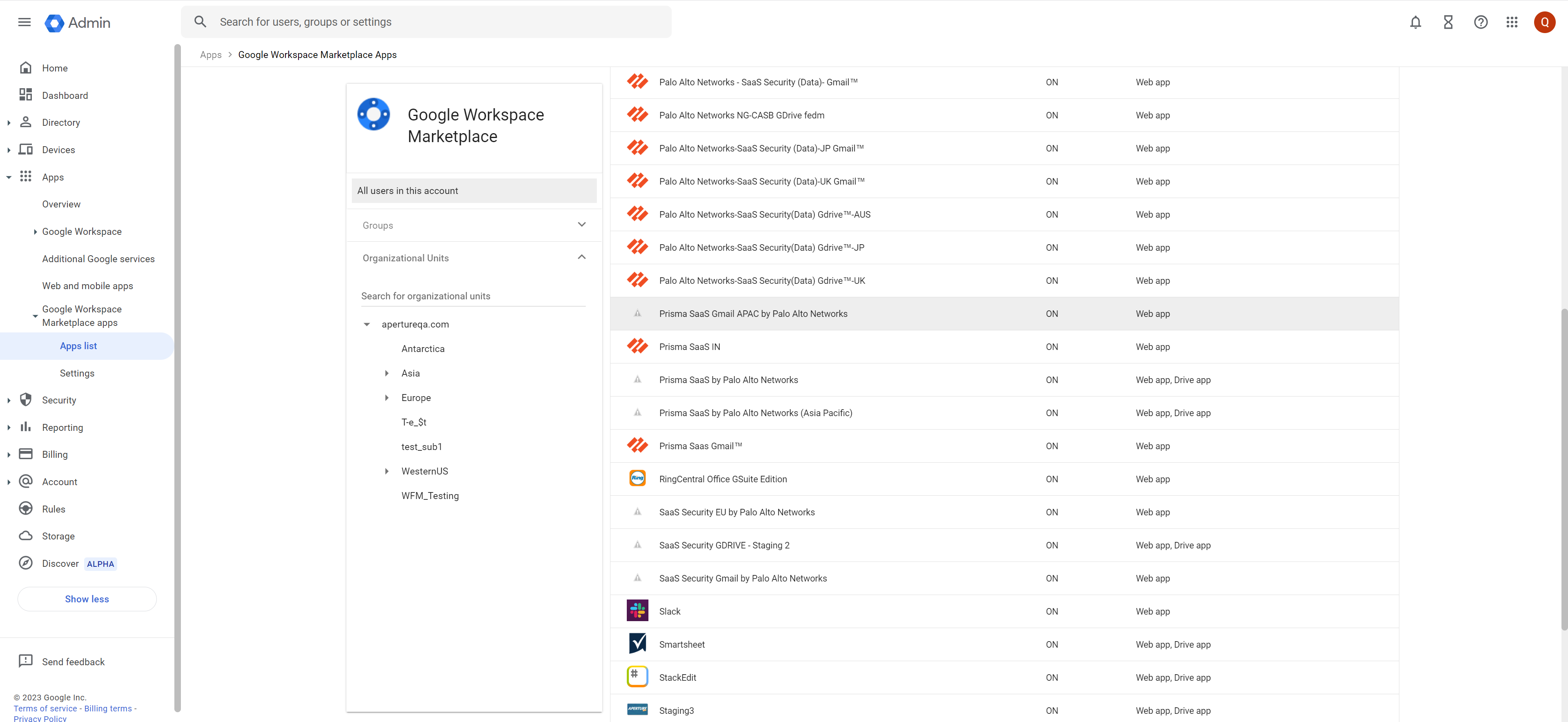
If the App Authentication, User Permission, or Validating Permissions checks fail, try the following:- Ensure you have administrator permissions.
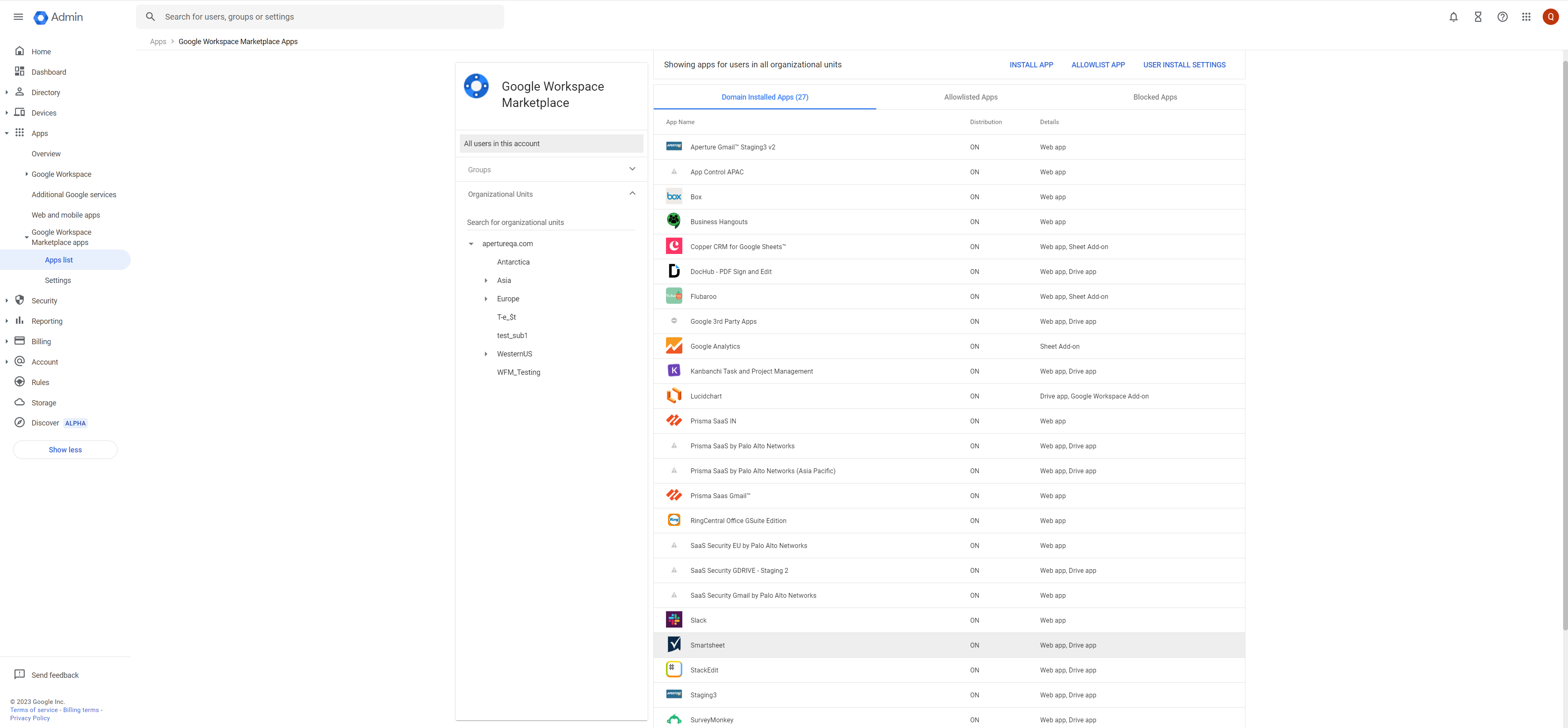
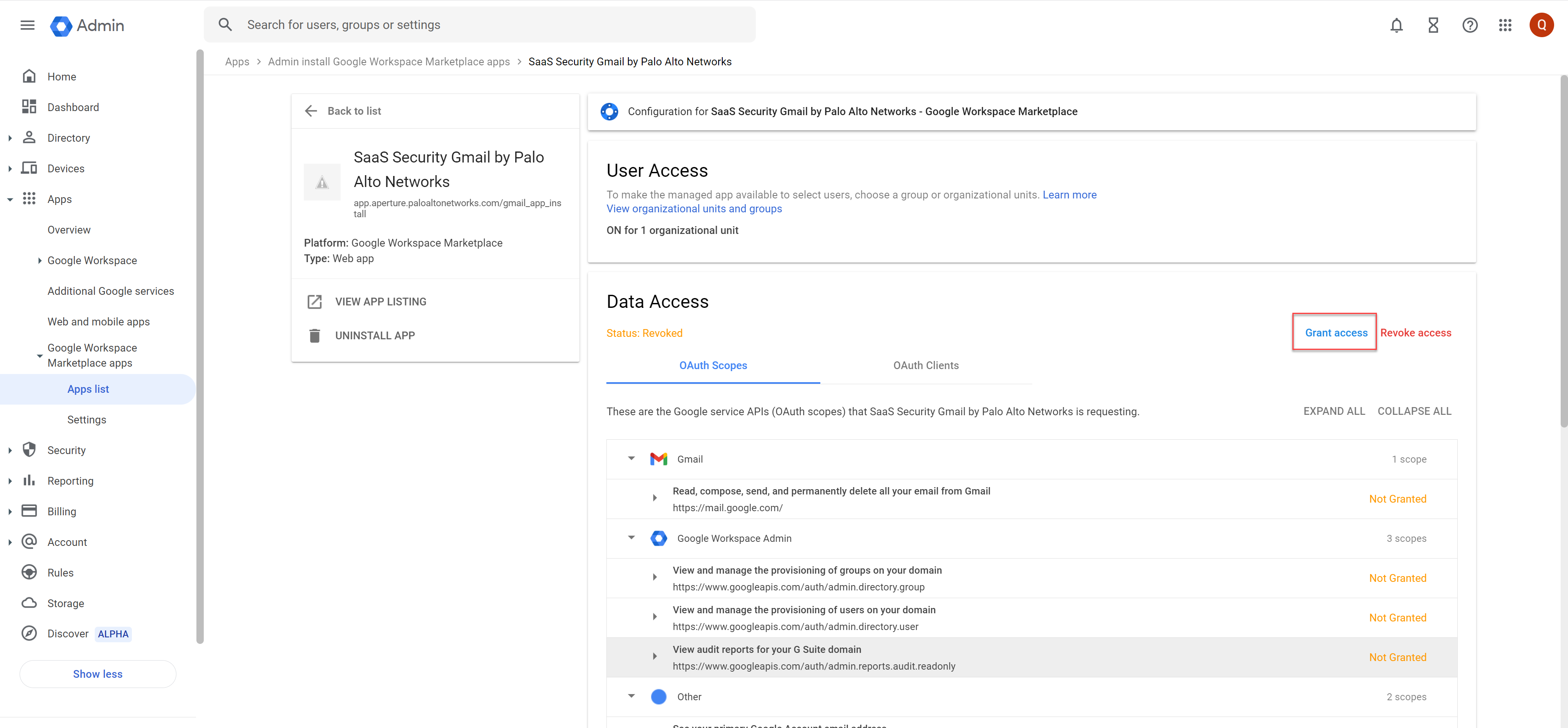
- Go to the Google Admin Console and check if the Palo Alto Networks application
is listed in the list of Google Workspace Marketplace Apps. Following are the
app names for specific regions:
- India region: Prisma SaaS Gmail
- Australia region: Palo Alto Networks - SaaS Security (Data)- Gmail
- Japan region: Palo Alto Networks-SaaS Security (Data)-JP Gmail
- UK region: Palo Alto Networks-SaaS Security (Data)-UK Gmail
- EU region: SaaS Security EU by Palo Alto Networks
- APAC region: Prisma SaaS Gmail APAC by Palo Alto Networks
- VPC: SaaS Security Gmail by Palo Alto Networks
- FEDM region: Palo Alto Networks - SaaS Security FEDM- Gmail
![]()
Handling ErrorsTo understand your error messages and ways to resolve them, see:- Common Errors
- User Permission Errors: Ensure that the user is a Super Admin in the Google console.
- App Authentication Failure (unauthorized_client error): Domain Wide Delegation isn’t provided or the application is not installed in the Google Dashboard.
- Errors in App Authentication
- Errors during fetching sample data assets and sample user activities
The other most common issues related to onboarding a Gmail app are as follows:SymptomExplanationSolutionWhen you click Connect to Gmail Account (Step 3 of the Install page), you receive an authentication error.The Google account doesn’t have sufficient permissions to authenticate and access all the assets within Gmail.Make sure your Google account is an administrator with default super admin role or applicable custom role with the permission outlined in Create Custom Admin Roles.When you click Connect to Gmail Account (Step 3 of Install page), you receive a login error: This email must be added as a Super AdminThe Google account doesn’t have an administrator account in Data Security.Make sure your Google account is super admin on Data Security as outlined in Prerequisites to be completed on Google.When you click Connect to Gmail Account (Step 3 of the Install page), you’re redirected to a product landing page, and the Gmail app doesn’t display in the Cloud Apps list.![]() Cached files are preventing the correct redirect.Don't log out of Data Security. Instead, open Data Security in an incognito window. Repeat the onboarding process and click on Connect to Gmail Account (Step 3) again. The Gmail app now appears in the Cloud app list.When click on Go to Google Marketplace (Step 2 of Install page), a Please uninstall app for domain in Admin Console message displays.
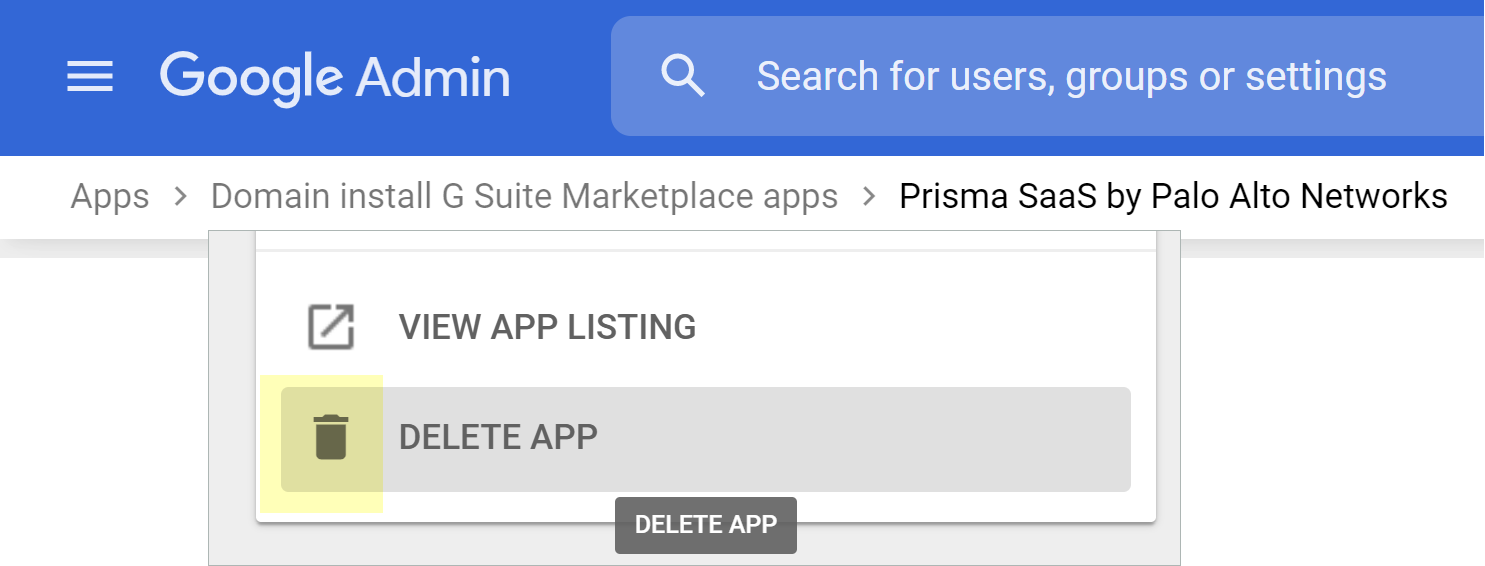
Cached files are preventing the correct redirect.Don't log out of Data Security. Instead, open Data Security in an incognito window. Repeat the onboarding process and click on Connect to Gmail Account (Step 3) again. The Gmail app now appears in the Cloud app list.When click on Go to Google Marketplace (Step 2 of Install page), a Please uninstall app for domain in Admin Console message displays.![]() This usually occurs if you previously installed the app and deleted it from Data Security but did not delete it from Google Marketplace.Delete the app from the Google Marketplace, then you’ll be able to add the Gmail app in Data Security.
This usually occurs if you previously installed the app and deleted it from Data Security but did not delete it from Google Marketplace.Delete the app from the Google Marketplace, then you’ll be able to add the Gmail app in Data Security.![]() This problem occurs if you complete step 2 of the Install page and either abort your install or forget to click Connect to Google Drive Account (Step 3 of Install page).If the Google Marketplace page is open in the same browser and session that you used when you initially added the Gmail app, simply click Connect to Gmail Account.Otherwise, delete the Gmail app from the Google Marketplace and repeat the Gmail app onboarding process in Data Security.
This problem occurs if you complete step 2 of the Install page and either abort your install or forget to click Connect to Google Drive Account (Step 3 of Install page).If the Google Marketplace page is open in the same browser and session that you used when you initially added the Gmail app, simply click Connect to Gmail Account.Otherwise, delete the Gmail app from the Google Marketplace and repeat the Gmail app onboarding process in Data Security.![]() If the issue persists, contact SaaS Security Technical Support.
If the issue persists, contact SaaS Security Technical Support.Start Scanning and Monitor Results
When you add a new cloud app and enable scanning, Data Security automatically scans the cloud app against the default data patterns and displays the match occurrences. You can take action now to improve your scan results and identify risks.- To start scanning the new Gmail app for risks, select ConfigurationSaaS SecurityData SecurityApplicationsGmailView Settings...Start Scanning.Monitor the scan results.During the discovery phase, Data Security scans files and matches them against enabled default policy rules.Verify that your default policy rules are effective. If the results don’t capture all risks or you see false positives, proceed to the next step.(Optional) Add new policy rules.Consider the business use of your app, then identify risks unique to your enterprise. As necessary, add new:(Optional) Configure or edit a data pattern.You can Configure Data Patterns to identify specific strings of text, characters, words, or patterns to make it possible to find all instances of text that match a data pattern you specify.Next step: Proceed to Customize Gmail App.
Customize Gmail App
If you plan to manage more than one instance of the Gmail app, consider differentiating your instances.- (Optional) Give a descriptive name to this app instance.
- Select the Gmail n link on the Cloud Apps list.Enter a descriptive Name.Click Done to save your changes.Next step: Proceed to Start Scanning and Monitor Results.
Create Domain Wide Delegation
You need domain wide delegation to make API calls to Google and fetch user data. To implement domain wide delegation, perform the following steps.- Log in to the Google Admin Console as a superuser and select SecurityAccess and data controlAPI controlsMANAGE DOMAIN WIDE DELEGATIONAdd new.Enter the client ID that’s applicable for your region:
- NAM: 101758057381597102755
- EU: 107302012290887199743
- APAC: 102431511463016019359
- IN: 113162770221785136577
- AU: 115902749905704876540
- JP: 103755143451773842949
- UK: 117282843217256637356
- FEDM: 117466562875859030537
Enter the following comma-delimited OAuth scopes and click AUTHORIZE.- https://www.googleapis.com/auth/admin.directory.group.readonly
- https://www.googleapis.com/auth/admin.directory.user.readonly
- https://www.googleapis.com/auth/admin.reports.audit.readonly
- https://www.googleapis.com/auth/gmail.readonly
Create Custom Admin Roles
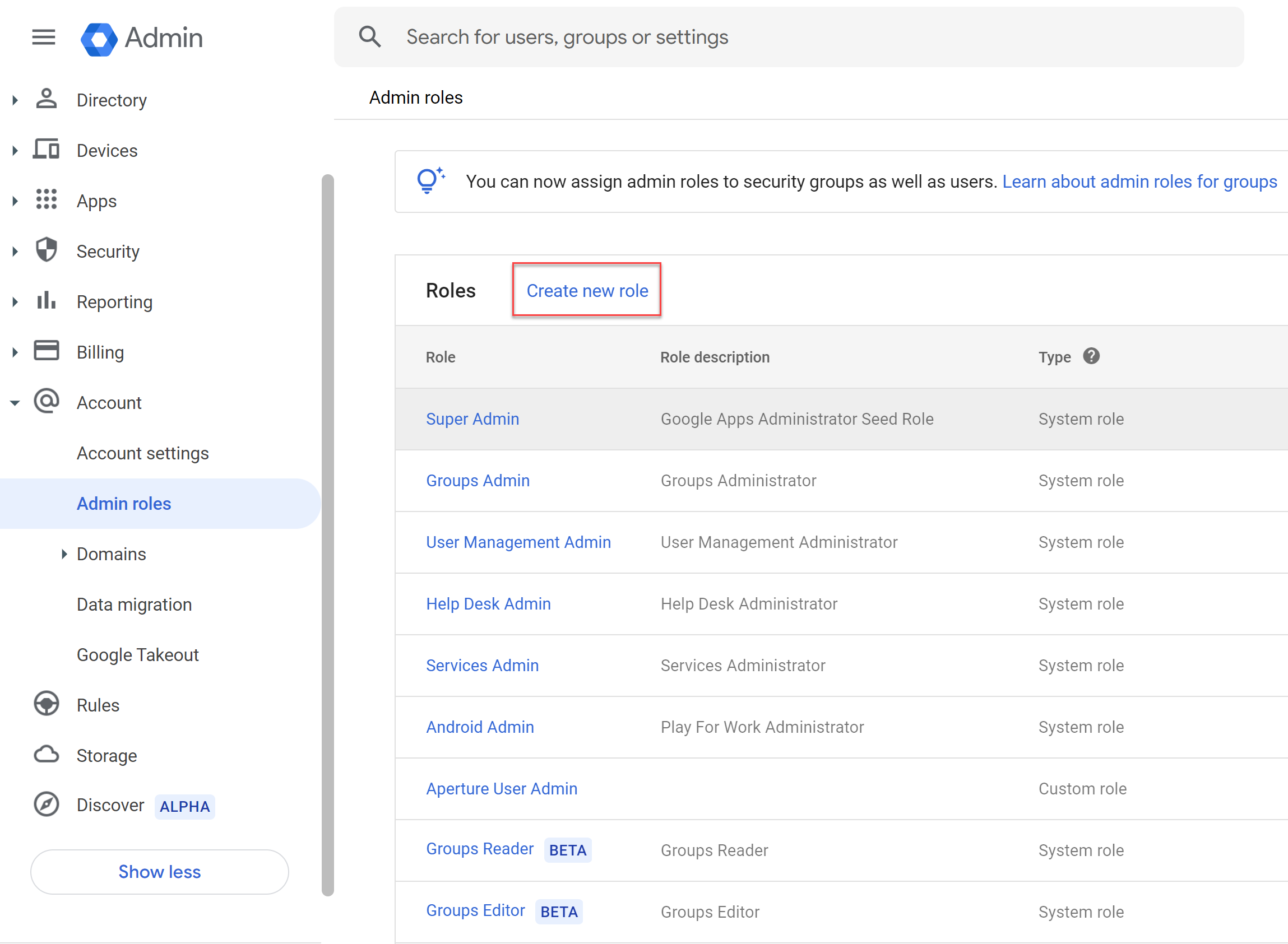
To avoid using a super admin account for Gmail onboarding, you can create a custom admin role with the least required privileges for successful onboarding. To create custom admin roles:- Go to the Google Admin Console and select AccountAdmin rolesCreate new role.
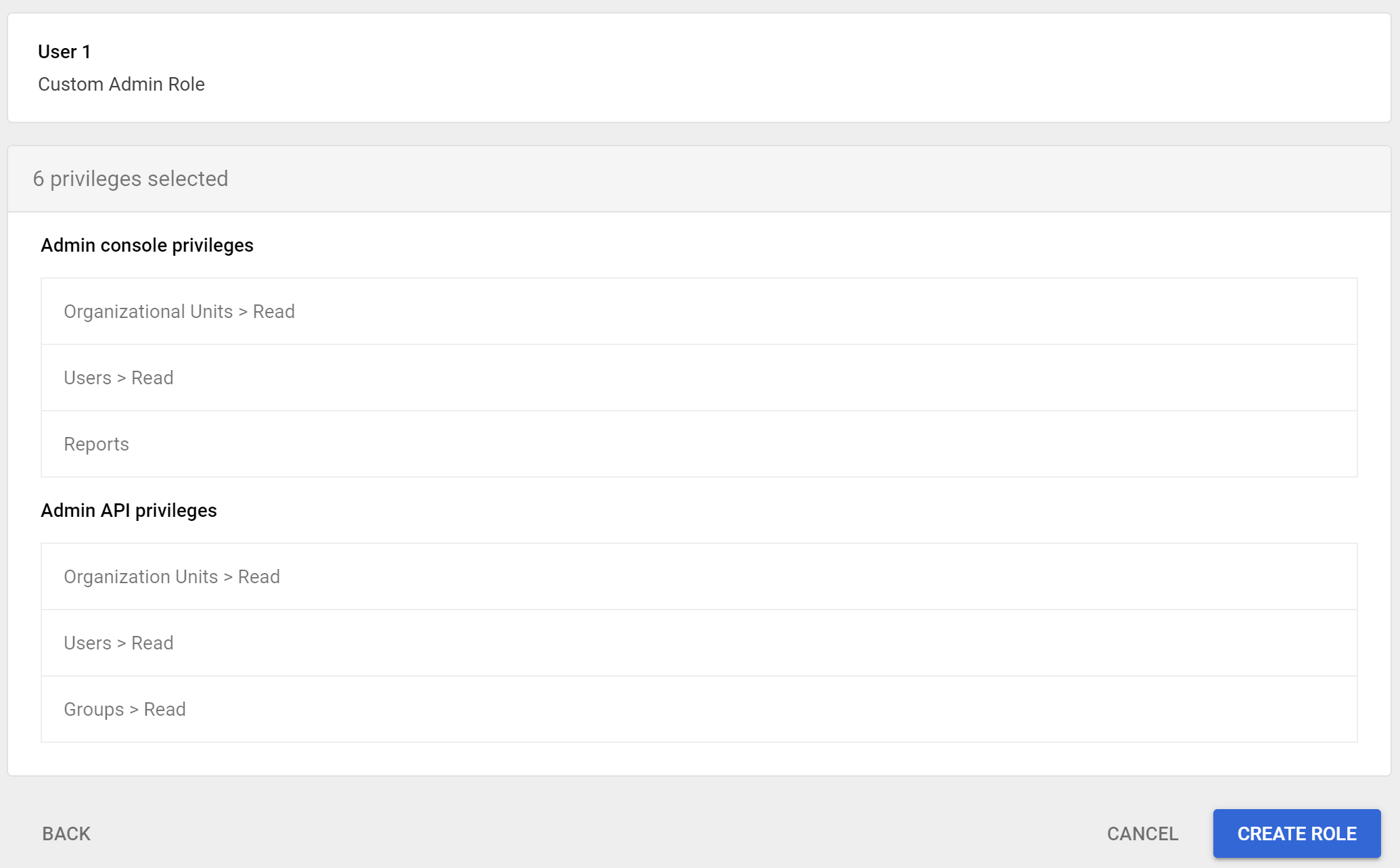
![]() Enter a name and description and click Continue.Select the following privileges:
Enter a name and description and click Continue.Select the following privileges:- Admin console privileges
- Organizational Units > Read
- Users > Read
- Reports
- Admin API privileges
- Organizational Units > Read
- Users > Read
- Groups > Read
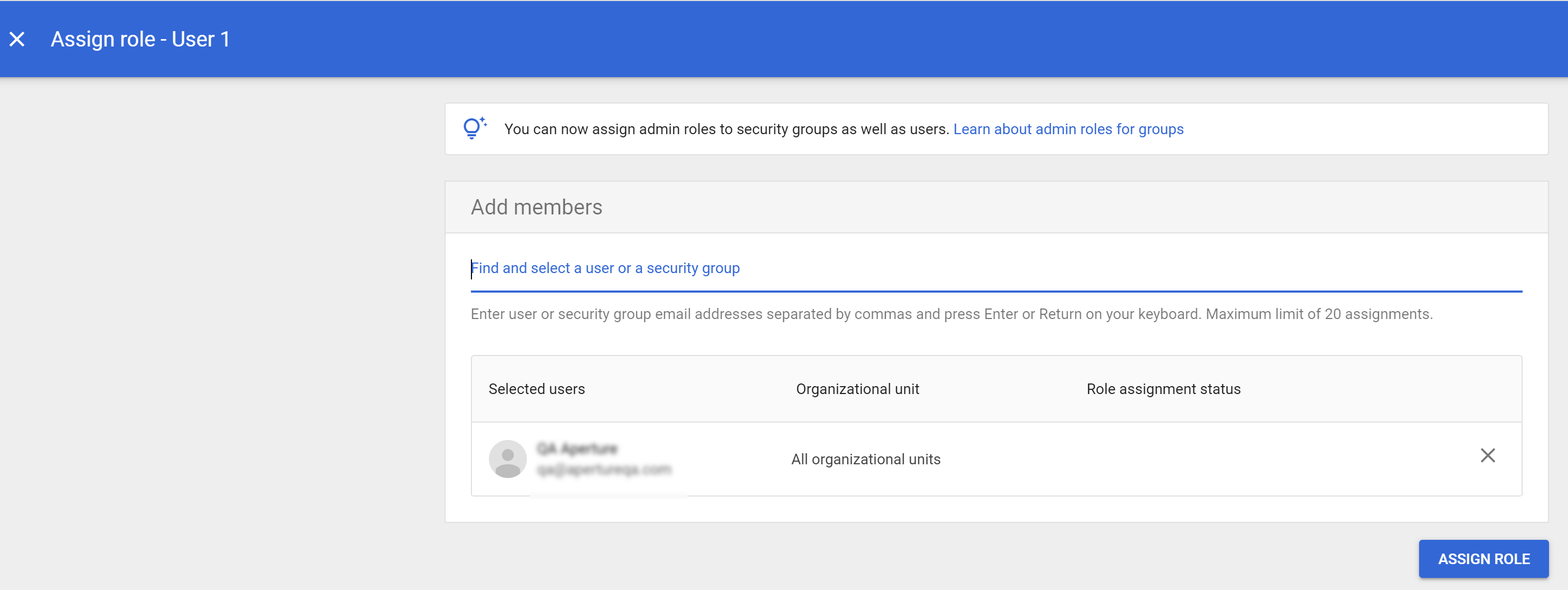
![]() After creating the role, assign a member to the created role.
After creating the role, assign a member to the created role.![]() Add the same user email to the Gmail Administrator Email field in SaaS Security Gmail App onboarding UI and click Connect. For an existing instance of Gmail app, you can’t edit the email address in Strata Cloud Manager. So, edit it from the SaaS Security Console.
Add the same user email to the Gmail Administrator Email field in SaaS Security Gmail App onboarding UI and click Connect. For an existing instance of Gmail app, you can’t edit the email address in Strata Cloud Manager. So, edit it from the SaaS Security Console.![]()
Grant Access to Reduced Privileges
- This step is applicable only for existing instances of the Gmail app.To grant access to the reduced privileges, from the Google Admin Console, select AppsGoogle Workspace marketplace appsApps List. Select the SaaS Security App from the list and click Grant Access.
![]()
![]()