SaaS Security
Onboard a Slack Enterprise App to SSPM
Table of Contents
Expand All
|
Collapse All
SaaS Security Docs
Onboard a Slack Enterprise App to SSPM
Connect a Slack Enterprise instance to SSPM to detect posture risks.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Data Security license:
|
To enable SSPM to display information about Slack
Enterprise account risks in the Identity Security dashboard, we
updated the Slack Enterprise connector in May 2025. If you onboarded your Slack
Enterprise instance prior to this update, and you want to view account risks in the
Identity Security dashboard, you must re-onboard your Slack instance. Before
onboarding, you must update your Slack org-wide app to give SSPM access to the
admin.users:read OAuth scope. Refer to the following instructions for more
information on adding the admin.users:read scope to your org-wide app.
For SSPM to detect posture risks in your Slack Enterprise instance, you must onboard
your Slack Enterprise instance to SSPM. Through the onboarding process, SSPM
connects to a Slack Enterprise API and, through the API, scans your Slack Enterprise
instance for misconfigured settings. If there are misconfigured settings, SSPM
suggests a remediation action based on best practices.
SSPM gets access to your Slack Enterprise instance by connecting to a Slack API using
an access token that you provide. To obtain this token, you first create an OAuth
integration application in Slack Enterprise. From your OAuth integration
application, you copy a user OAuth token. You then provide this OAuth token to SSPM
during onboarding.
To onboard your Slack Enterprise instance, you complete the following actions:
Create an App for Accessing Your Slack Enterprise Instance
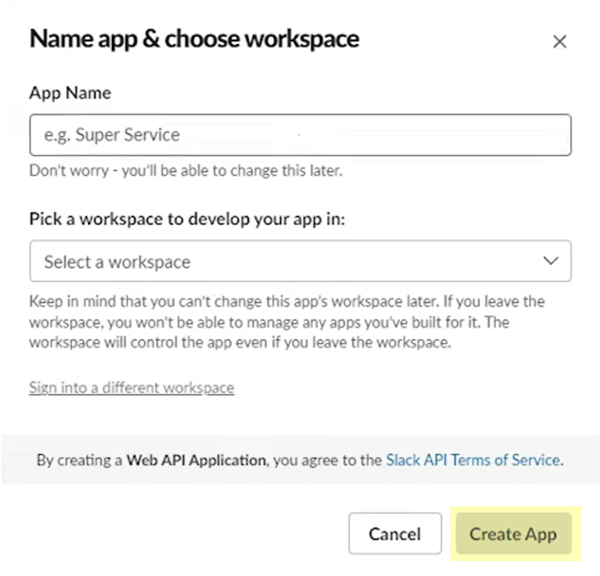
- Identify the administrator account that you will use to create your Slack org-wide app.Required Permissions: Because you will install the app across all workspaces in your organization, you must be assigned to the Org Admin role or a role with greater permissions.Log into the Slack API console and navigate to the Your Apps page (api.slack.com/apps).Create New App.In the Create an app dialog, specify that you want to create the app From scratch.In the Name app & choose workspace dialog, specify a name for your app and choose a workspace. You will be configuring your app in this workspace, and later will deploy it across the other workspaces your organization.Create App in the selected workspace.
![]() Slack Enterprise displays the configuration settings your new app.Configure your app according to the specifications required by SSPM.
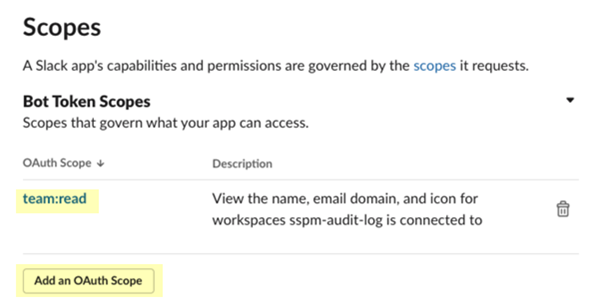
Slack Enterprise displays the configuration settings your new app.Configure your app according to the specifications required by SSPM.- Navigate to the OAuth and Permissions settings and locate the Scopes section.
- Under Bot Token Scopes, Add an OAuth Scope
and select the team:read scope.
![]()
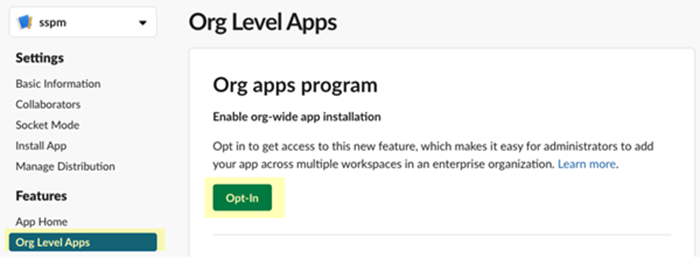
- Navigate to the Org Level Apps settings and
Opt in to the org apps program.
![]()
- Navigate back to the OAuth and Permissions settings and locate the Scopes section.
- Under User Token Scopes, Add an OAuth Scope
and select the following scopes:
- admin.teams:read
- auditlogs:read
- team:read
For identity scans, SSPM also requires the following scope:- admin.users:read
Install your app across your organization's workspaces to generate the User OAuth Token that SSPM requires.- In the OAuth and Permissions settings, locate
the OAuth Tokens for Your Workspace section and Install
to Organization.Slack Enterprises generates tokens for your app.
- Copy the User OAuth Token and paste it into a text file.Do not continue to the next step unless you have copied the User OAuth Token. You must provide the User OAuth Token during onboarding when SSPM prompts you for an API Key.
Connect SSPM to Your Slack Enterprise Instance
By adding a Slack Enterprise app in SSPM, you enable SSPM to connect to your Slack Enterprise instance. - Log in to Strata Cloud Manager.Select ConfigurationSaaS SecurityPosture SecurityApplicationsAdd Application and click the Slack Enterprise tile.On the Posture Security tab, Add New instance.Specify the User OAuth Token and Connect with Slack Enterprise.