SaaS Security
Configure SSPM to Create Tickets in an Issue Tracking System
Table of Contents
Expand All
|
Collapse All
SaaS Security Docs
Configure SSPM to Create Tickets in an Issue Tracking System
To create an view tickets in an issue tracking system, you must fist link SSPM to the
Jira or ServiceNow issue tracking system.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Data Security license:
|
If you are using the Jira or ServiceNow issue tracking system to manage your team's
tasks, you can configure SaaS Security Posture Management (SSPM) to create tickets directly from
SSPM. To configure SSPM for ticket creation, you link SSPM to a Jira or ServiceNow
instance. Be aware that SSPM does not automatically create tickets. Instead, you
must explicitly create a ticket from within SSPM.
The administrator of your issue tracking system might have configured certain
fields to be mandatory for ticket creation. When SSPM creates a ticket, it
provides values for only a few fields and might not provide values for the
required fields. For this reason, ticket creation might fail with an error
message.
For ServiceNow, SSPM provides values only for the following fields:
- Short Description
- Description
For Jira, SSPM provides values only for the following fields:
- Summary
- Project
- Issue Type
- Description
- Link SSPM to a Jira Instance
- Link SSPM to a ServiceNow Instance
- Unlink SSPM from a Jira or ServiceNow Instance
Link SSPM to a Jira Instance
Link SSPM to an instance of the Jira issue tracking system to create tickets from
SSPM.
If you are using the Jira issue tracking system to manage your team's tasks, you can
link SSPM to a Jira instance, which is also referred to as a Jira site. This link
enables you to create a ticket in Jira directly from
SSPM. Be aware that SSPM does not automatically create tickets in Jira. Linking SSPM
to a Jira instance only enables you to explicitly create a ticket from within SSPM.
To create and view tickets, SSPM requires view and update permissions to the
jira-work access scope for your Jira instance. During the linking process, SSPM will
redirect you to Jira to grant the access to this scope.
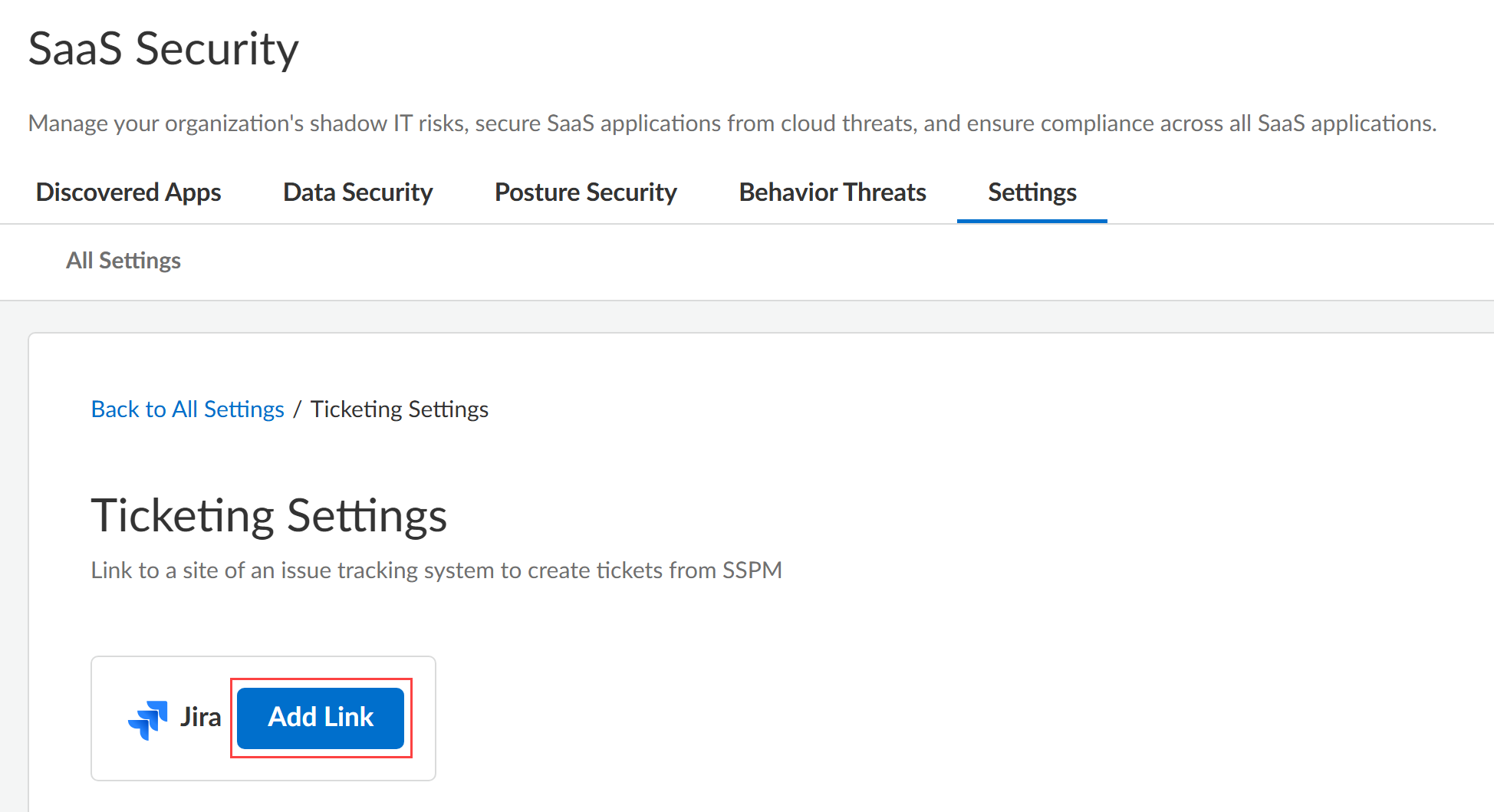
- Log in to Strata Cloud Manager.Select ConfigurationSaaS SecuritySettings WorkflowTicketing Settings.The Ticketing Settings page is displayed.Add Link for Jira.
![]() SSPM will link to Jira through OAuth 2.0 authorization. For authorization, SSPM redirects you to the Jira login page.Log in to Jira. When you are prompted to grant SSPM access, select the Jira site that you want SSPM to be able to access and Confirm.
SSPM will link to Jira through OAuth 2.0 authorization. For authorization, SSPM redirects you to the Jira login page.Log in to Jira. When you are prompted to grant SSPM access, select the Jira site that you want SSPM to be able to access and Confirm.Link SSPM to a ServiceNow Instance
Link SSPM to an instance of the ServiceNow issue tracking system to create tickets in ServiceNow from SSPM.If you are using the ServiceNow issue tracking system to manage your team's tasks, you can link SSPM to a ServiceNow instance. This link enables you to create tickets in ServiceNow directly from SSPM. Be aware that SSPM does not automatically create tickets in ServiceNow. Linking SSPM to a ServiceNow instance only enables you to explicitly create a ticket from within SSPM.SSPM links to your ServiceNow instance through OAuth 2.0 authorization. To enable OAuth 2.0 authorization, you first register an OAuth 2.0 integration application in ServiceNow. You can then link to the ServiceNow instance by supplying SSPM with your ServiceNow instance URL and the application credentials for your OAuth 2.0 application. This OAuth 2.0 application can be the same OAuth 2.0 application that you use to connect SSPM to ServiceNow for configuration scans. However, be aware that SSPM uses different redirect URLs depending on whether you are onboarding ServiceNow for configuration scans or linking to ServiceNow for ticketing. Your OAuth 2.0 integration application can specify both of these redirect URLs.- To create an OAuth 2.0 application for ticketing, follow the instructions for onboarding ServiceNow for configuration scans. In your OAuth 2.0 application, make sure that you include the redirect URL for ticketing.If a ServiceNow instance was already onboarded for configuration scans, you can link to that ServiceNow instance using the same OAuth 2.0 application that was already created. However, you will need the application credentials of the OAuth 2.0 application, and you will need to make sure that the OAuth 2.0 application includes the redirect URL for ticketing. Contact the administrator who created the OAuth 2.0 application for this information and to verify that the redirect URL for ticketing is included.If you are a ServiceNow administrator and can edit the OAuth 2.0 application, complete the following steps to get the application credentials and to verify that the redirect URL for ticketing is included.
- Log in to Strata Cloud Manager.Select ConfigurationSaaS SecuritySaaS SecuritySettings Workflow Ticketing Settings.Add Link for ServiceNow.The login page for linking to a ServiceNow instance is displayed. The Redirect URL field displays the redirect URL value.Get the application credentials and verify that the OAuth 2.0 application contains the redirect URL.
- Log in to ServiceNow as an administrator.
- Navigate to the Application Registries page (System OAuth Application Registry).
- From the list of application registries, open the OAuth 2.0 application.
- Copy the Client ID and Client Secret into a text file. You will need this information to link to the ServiceNow instance.
- Check the Redirect URL field to see if it includes the redirect URL for ticketing. If necessary, add the redirect URL for ticketing to the Redirect URL field. Do not remove the existing redirect URL for configuration scans. Separate the two URLs with a comma.
- Update to save your changes.
Select ConfigurationSaaS SecuritySaaS SecuritySettings Workflow Ticketing Settings.Add Link for ServiceNow.Log in with Credentials.On the login page, enter your Instance URL and the application credentials (Client ID and Client Secret) and Connect.SSPM redirects you to the ServiceNow login page.Log in using your ServiceNow account.ServiceNow displays a consent form that details the access permissions that SSPM requires.Review the consent form and allow the requested permissions.Unlink SSPM from a Jira or ServiceNow Instance
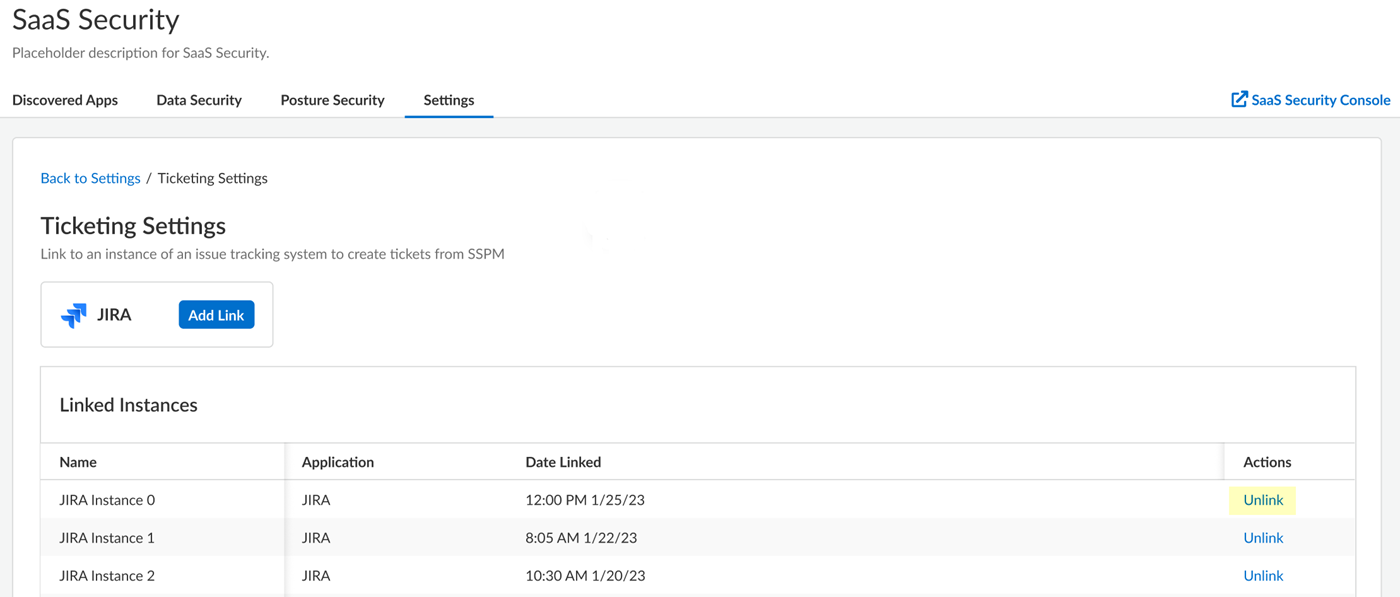
When you no longer need to create tickets in an issue tracking system from SSPM, you can remove SSPM's link to your Jira instance.Linking SSPM to an issue tracking system (Jira or ServiceNow) enables you to create tickets in the issue tracking system directly from SSPM. When you no longer need this capability, you can unlink SSPM from the issue tracking system. For example, you might want to unlink a Jira instance because you are no longer using the Jira instance to manage your team's tasks.Unlinking an instance of Jira or ServiceNow also unlinks all tickets that were created in the issue tracking system from SSPM. Unlinking the tickets does not delete the tickets from the issue tracking system.- Log in to Strata Cloud Manager.Select ConfigurationSaaS SecuritySettings Workflow Ticketing Settings.The Ticketing Settings page is displayed. This page lists the links that exist between SSPM and instances of Jira and ServiceNow.In the Linked Instances area, locate the instance of Jira or ServiceNow and Unlink the instance.
![]()