Best Practices for Content Updates—Security-First
Table of Contents
11.0 (EoL)
Expand all | Collapse all
-
-
- Upgrade Panorama with an Internet Connection
- Upgrade Panorama Without an Internet Connection
- Install Content Updates Automatically for Panorama without an Internet Connection
- Upgrade Panorama in an HA Configuration
- Migrate Panorama Logs to the New Log Format
- Upgrade Panorama for Increased Device Management Capacity
- Upgrade Panorama and Managed Devices in FIPS-CC Mode
- Downgrade from Panorama 11.0
- Troubleshoot Your Panorama Upgrade
-
- What Updates Can Panorama Push to Other Devices?
- Schedule a Content Update Using Panorama
- Panorama, Log Collector, Firewall, and WildFire Version Compatibility
- Upgrade Log Collectors When Panorama Is Internet-Connected
- Upgrade Log Collectors When Panorama Is Not Internet-Connected
- Upgrade a WildFire Cluster from Panorama with an Internet Connection
- Upgrade a WildFire Cluster from Panorama without an Internet Connection
- Upgrade Firewalls When Panorama Is Internet-Connected
- Upgrade Firewalls When Panorama Is Not Internet-Connected
- Upgrade a ZTP Firewall
- Revert Content Updates from Panorama
-
End-of-Life (EoL)
Best Practices for Content Updates—Security-First
Follow these best practices to deploying content updates
in a security-first network, where threat prevention is top priority.
The Best Practices for Applications and Threats Content Updates help to
ensure seamless policy enforcement as new application and threat
signatures are released. Follow these best practices to deploy content
updates in a security-first network, where you’re primarily
using the firewall for its threat prevention capabilities and your
first priority is attack defense.
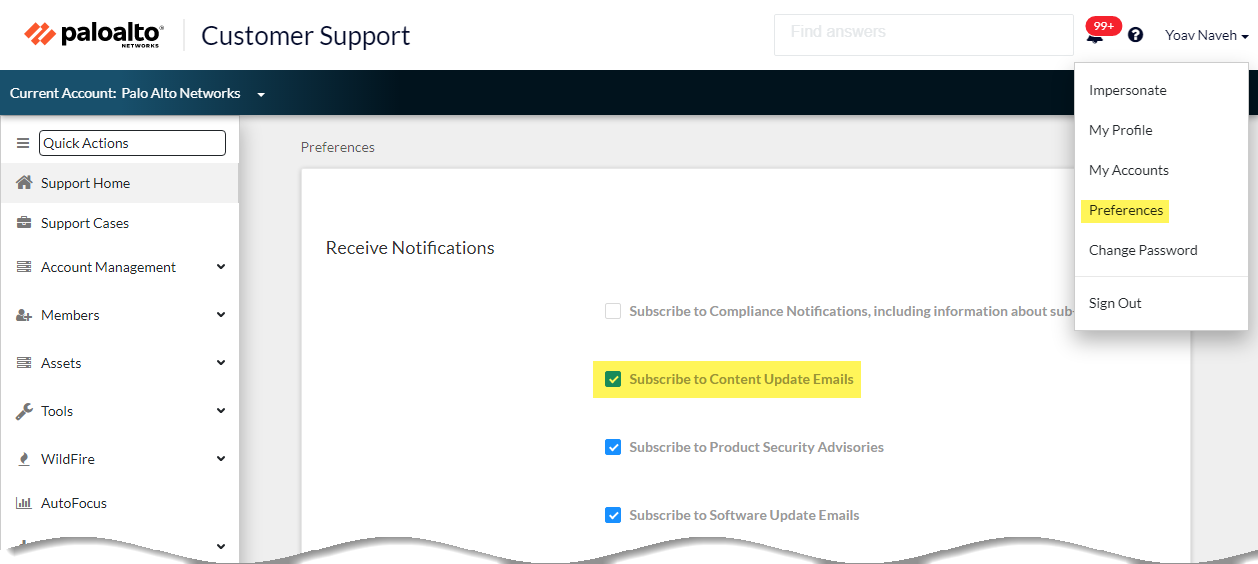
- Always review Content Release Notes for the list of newly-identified and modified application and threat signatures that the content release introduces. Content Release Notes also describe how the update might impact existing security policy enforcement and provides recommendations on how you can modify your security policy to best leverage what’s new.To subscribe to get notifications for new content updates, visit the Customer Support Portal, edit your Preferences, and select Subscribe to Content Update Emails.
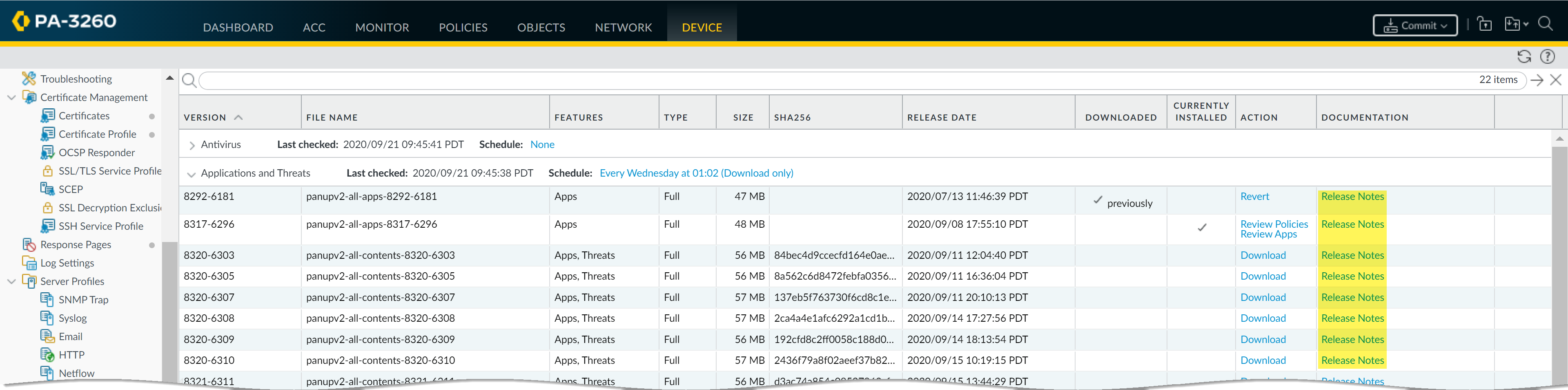
![]() You can also review Content Release Notes for apps and threats on the Palo Alto Networks Support Portal or directly in the firewall web interface: select DeviceDynamic Updates and open the Release Note for a specific content release version.
You can also review Content Release Notes for apps and threats on the Palo Alto Networks Support Portal or directly in the firewall web interface: select DeviceDynamic Updates and open the Release Note for a specific content release version.![]() The Notes section of Content Release Notes highlights future updates that Palo Alto Networks has identified as possibly significantly impacting coverage: for example, new App-IDs or decoders. Check for these future updates, so that you can account for any policy impact in advance of the release.
The Notes section of Content Release Notes highlights future updates that Palo Alto Networks has identified as possibly significantly impacting coverage: for example, new App-IDs or decoders. Check for these future updates, so that you can account for any policy impact in advance of the release. - To mitigate any impact to security policy enforcement that is associated with enabling new application and threat signatures, stagger the roll-out of new content. Provide new content to locations with less business risk (fewer users in satellite offices) before deploying them to locations with more business risk (such as locations with critical applications). Confining the latest content updates to certain firewalls before deploying them across your network also makes it easier to troubleshoot any issues that arise. You can use Panorama to push staggered schedules and installation thresholds to firewalls and device groups based on organization or location (Use Panorama to Deploy Updates to Firewalls).
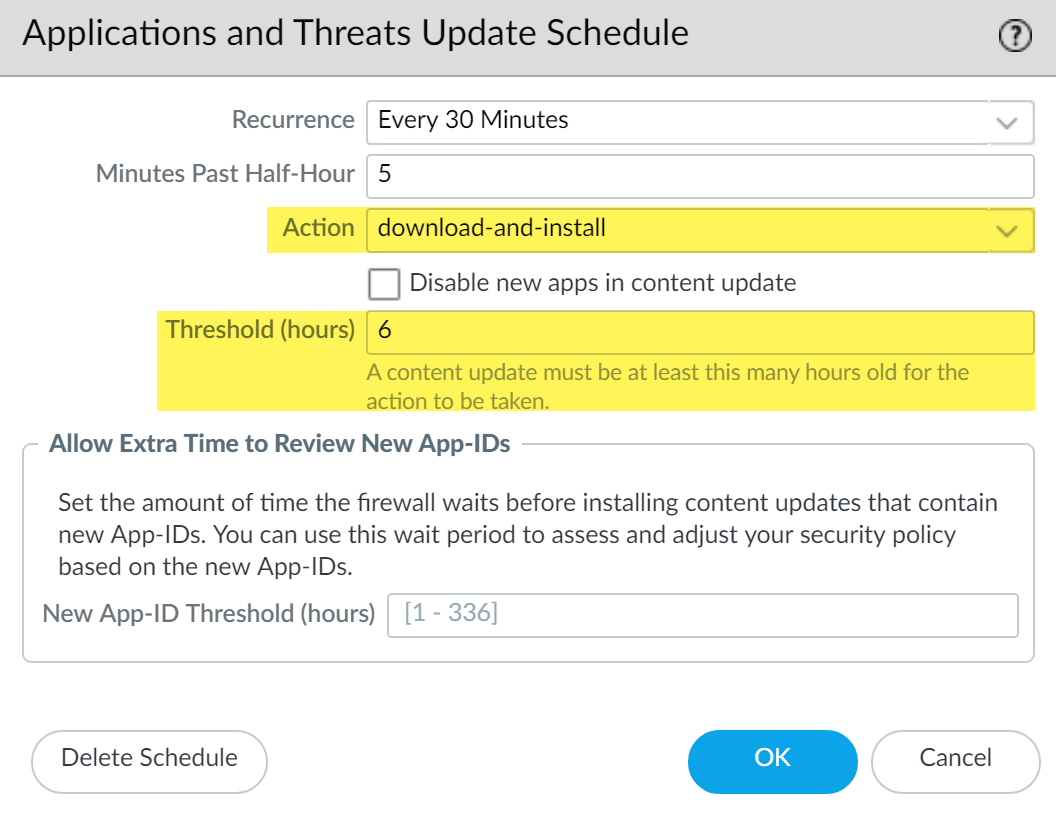
- Schedule content updates so that they download-and-install automatically. Then, set a Threshold that determines the amount of time the firewall waits before installing the latest content. In a security-first network, schedule a six to twelve hour threshold.
![]() The installation delay ensures that the firewall only installs content that has been available and functioning in customer environments for the specified amount of time. To schedule content updates, select DeviceDynamic UpdatesSchedule.Do not schedule a New App-ID Threshold. This threshold allows mission-critical organizations extra time to adjust security policy enforcement based on new App-IDs. However, because this threshold also delays delivery of the latest threat prevention updates, it is not recommended for organizations with a security-first posture.
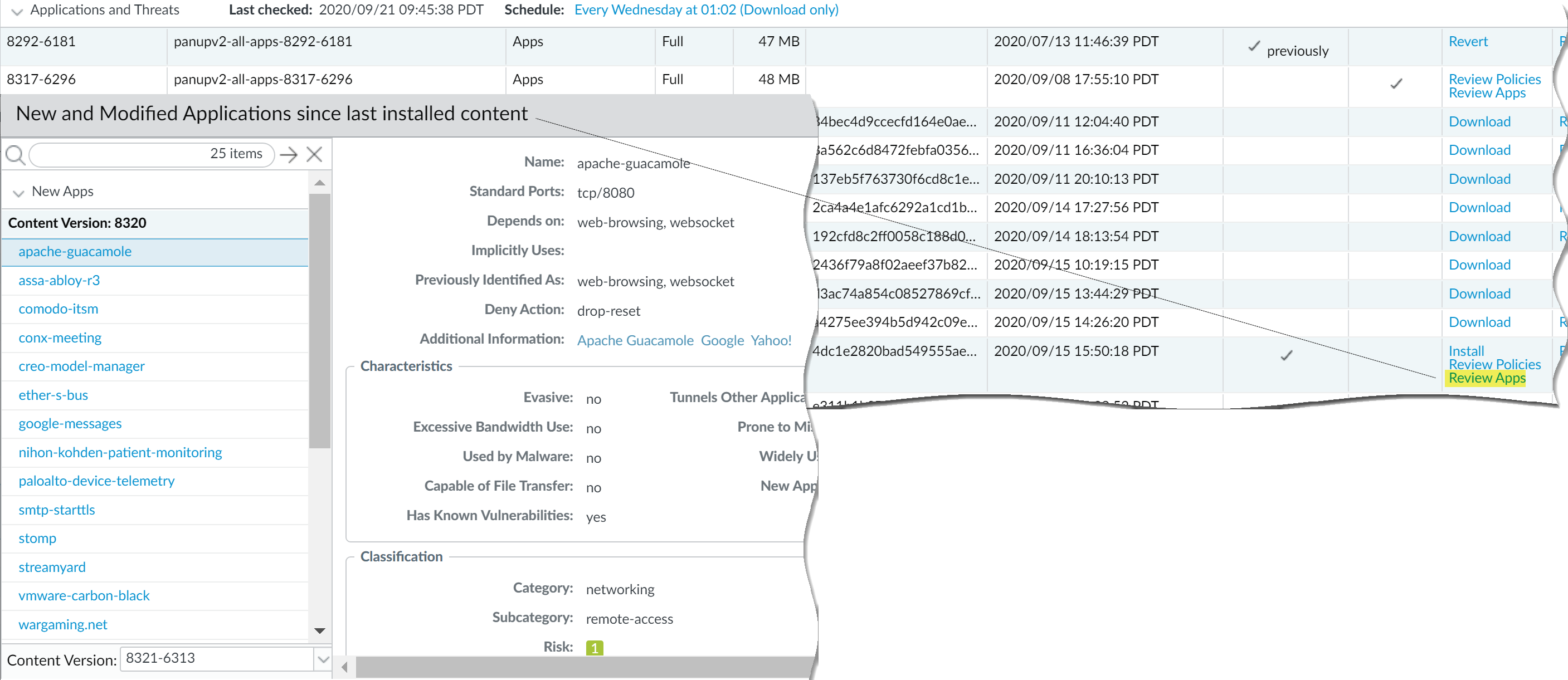
The installation delay ensures that the firewall only installs content that has been available and functioning in customer environments for the specified amount of time. To schedule content updates, select DeviceDynamic UpdatesSchedule.Do not schedule a New App-ID Threshold. This threshold allows mission-critical organizations extra time to adjust security policy enforcement based on new App-IDs. However, because this threshold also delays delivery of the latest threat prevention updates, it is not recommended for organizations with a security-first posture. - Review the new and modified App-IDs that a content release introduces, in order to assess how the changes might impact your security policy. The following topic describes the options you can use to update your security policy both before and after installing new App-IDs: Manage New and Modified App-IDs.
![]()
- Set up log forwarding to send Palo Alto Networks critical content alerts to external services that you use for monitoring network and firewall activity. This allows you to ensure that the appropriate personnel is notified about critical content issues, so that they can take action as needed. Critical content alerts are logged as system log entries with the following Type and Event: (subtype eq dynamic-updates) and (eventid eq palo-alto-networks-message).
![]() PAN-OS 8.1.2 changed the log type for critical content alerts from general to dynamic-updates. If you’re using PAN-OS 8.1.0 or PAN-OS 8.1.1, critical content are logged as system log entries with the following Type and Event, and you should set up forwarding for these alerts using the following filter: (subtype eq general) and (eventid eq palo-alto-networks-message).
PAN-OS 8.1.2 changed the log type for critical content alerts from general to dynamic-updates. If you’re using PAN-OS 8.1.0 or PAN-OS 8.1.1, critical content are logged as system log entries with the following Type and Event, and you should set up forwarding for these alerts using the following filter: (subtype eq general) and (eventid eq palo-alto-networks-message).