SaaS Security
Track Down Threats with WildFire Report
Table of Contents
Expand All
|
Collapse All
SaaS Security Docs
Track Down Threats with WildFire Report
Learn how to use the WildFire report on Data Security to investigate potentially malicious threats on your network.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Data Security license:
|
Data Security leverages the WildFire service to detect known and unknown malware by file
type. Use the WildFire Report on Data Security to track down threats.
Before Data Security can display a WildFire Report, you must configure WildFire analysis on Data Security.
If an asset in one of
your monitored SaaS applications matches the WildFire rule,
WildFire identifies the asset as malicious. Data Security reports
this information in a WildFire Report, which includes:
- Asset information—file information, including the hash, file, type, and size.
- WildFire static analysis—results of machine learning capabilities of WildFire to display samples that contain characteristics of known malware.
- WildFire dynamic analysis—details about the malicious host and network activity the file exhibited in the different WildFire sandbox environments.
- Log in to Strata Cloud Manager.View Asset Details.
- Select ConfigurationSaaS SecurityData SecurityIncidents.Click on an asset (that matches with the WildFire rule) from the Data Asset Name column.The asset's details are displayed.Click View WildFire Report to review the WildFire Report to get context into the malware findings.
![]() Download the report in XML or PDF format. This report contains the following sections:
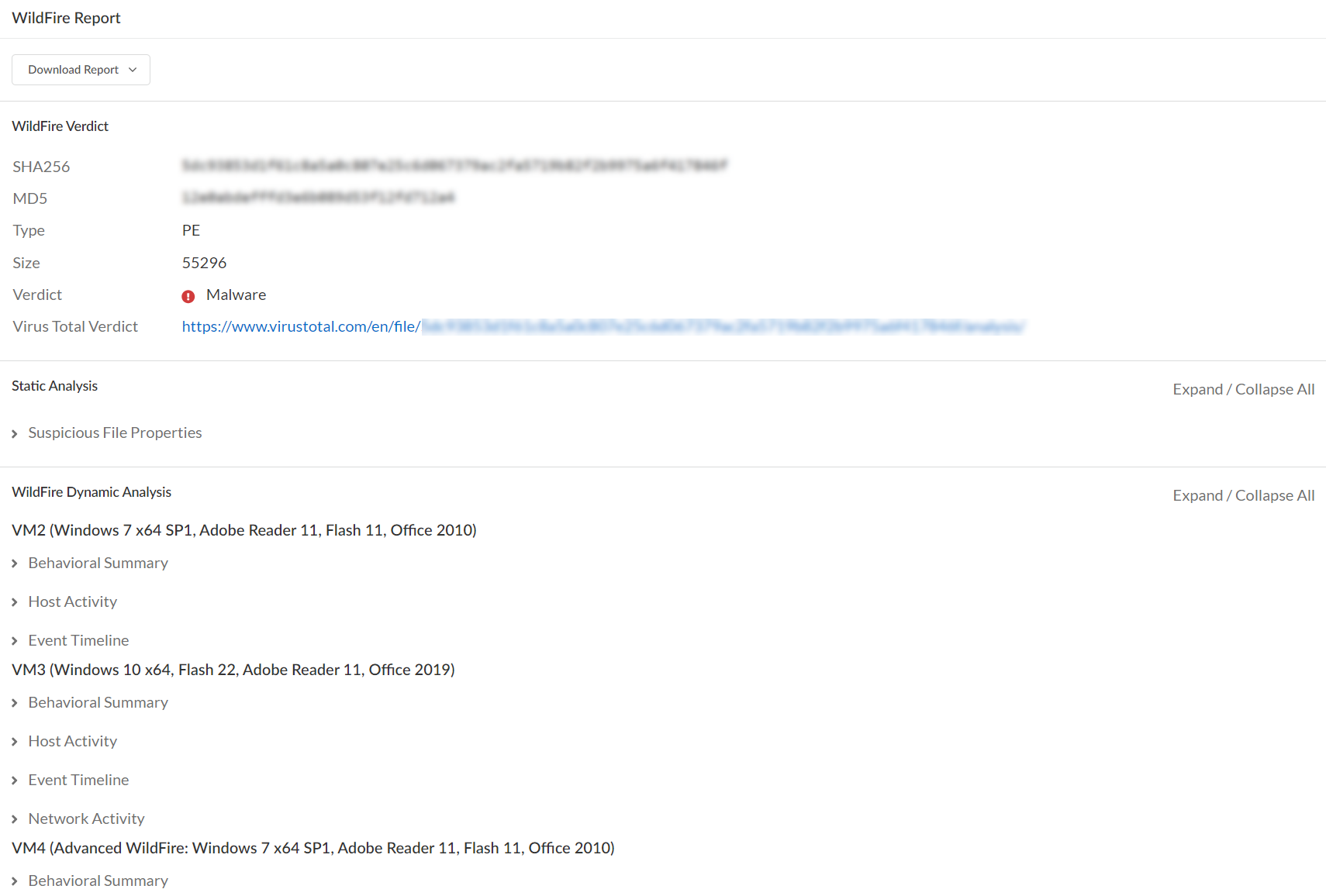
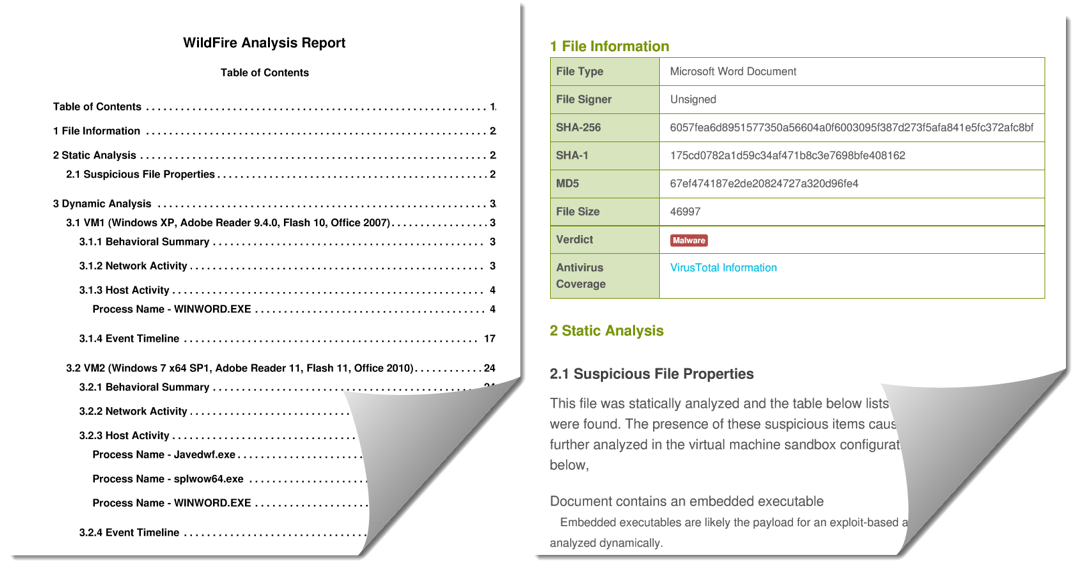
Download the report in XML or PDF format. This report contains the following sections:- WildFire Verdict—Displays details about the file,
including the hash (SHA256), file type, and size. Additionally:
- Report Incorrect Verdict—If you disagree with a WildFire verdict, send the WildFire team a request for further analysis. You will receive an email notification directly from the WildFire team with the results. If applicable, the verdict will be updated on WildFire. However, SaaS Security does not currently reflect such verdict updates. Contact SaaS Security Technical Support to manually refresh the verdict in the SaaS Security pending an integration to automatically refresh verdict updates.
- VirusTotal Verdict—Displays a link to malware analysis. If the malware has never been discovered before, a file not found error displays.
- Static Analysis—Leverages the machine learning capabilities of WildFire to display samples that contain characteristics of known malware.
- Dynamic Analysis—Displays details about the malicious host and network activity that the file exhibited in different WildFire sandbox environments.
![]()