SaaS Security
Search in Data Security
Table of Contents
Expand All
|
Collapse All
SaaS Security Docs
Search in Data Security
Learn how to perform search in Data Security.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Data Security license:
|
Use Faceted Search to Filter Assets
Learn how to use faceted search on Data Security to investigate and view details
about assets discovered when scanning your SaaS apps.
The SaaS Security web interface provides faceted search to help you investigate and view details
about assets discovered when scanning your SaaS apps.
Use Faceted Search to Filter Assets
In addition to the highlights from the
Dashboard, Data Security provides visibility into all assets
in your managed SaaS apps. Search provides you different views to help you:
- Find the incidents that are most important to you.
- Simplify the remediation process. For example, you can find PII violations with external exposure, assign issues to an administrator, and send an email to the owners—all in one streamlined work flow.
- Explore the assets to determine if you should Fine-Tune Policy.
If you cannot locate the incidents you need with a faceted search, perform an advanced search.
Search Inside Data Security
The following table lists the various ways in which you can search and use filters.
The Data Patterns column displays matches/data pattern names only
for High Confidence matches. It does not display Low Confidence and
Medium Confidence matches.
|
Navigation
|
Search For
|
Filters
|
|---|---|---|
|
Data Assets
| ||
|
Data AssetsAll Assets
|
Data assets or owner
|
|
|
Data AssetsQuarantined Assets
|
Data assets or owner
|
|
|
Data AssetsLabeled by Policy
|
Search assets by name
|
|
|
Users & Activity
| ||
|
Users & ActivityMonitored Users
|
Search by name or email
|
|
|
Users & ActivityUser Activities
|
Search by user, file name, or app instance
|
|
|
Incidents
| ||
|
IncidentsData Asset Incidents
|
Search by Data Asset
|
|
|
IncidentsUser Activity Incidents
|
Search by Policy
|
|
|
IncidentsSecurity Control Incidents
|
Search by User
|
|
|
IncidentsEmail DLP Incidents
|
Search incidents (by subject and sender)
|
|
- Click Reset to reset all of the above filters.
- Most of the filters have a time range that you can select. For example, Past 24 hours, Past 7 days, All time, Custom date, and so on.
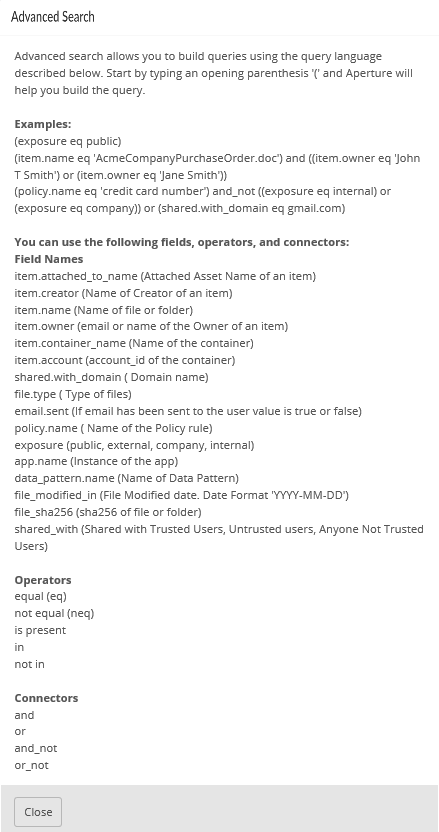
Use Advanced Search Expressions
Perform a more detailed search of incidents on Data Security using advanced search expressions.
An advanced search expression is
composed of a set of supported fields, operators, and connectors. Fields
and field values can include:
- item.attached_to_name—Attached asset name of an item.
- item.creator—Name of the creator of an item. The name can be partial.
- item.creator_email—Email of the creator of an item. The email address must be complete.
- item.name—Name of file or folder, such as techsupport.tgz.
- item.owner—Name of the owner of an item. The name can be partial.
- item.owner_email—Email of the owner of an item. The email address must be complete.
- item.container_name—Name of the container.
- item.account—Account ID of the container.
- shared.with_domain—Any domain name.
- file.type—File format supported by Data Security, such as TGZ.
- email.sent—If email has been sent to the user the value is true or false.
- policy.name—Name of a policy rule.
- exposure—Public, External, Internal, Company, or hasCustomURL.
- app.name—Name of any application instance, such as Google Drive Prod.
- data_pattern.name—Name of the data pattern.
- file_modified_in—File modification date with date format YYYY-MM-DD.
- file_sha256—sha256 of file or folder.
- shared_with—Shared with trusted users, untrusted users, or anyone not trusted users.
Operators define the relationship between a field and a value.
The following list includes all the available Operators, and you should
use the auto completion to verify the operators for a specific field:
- eq—equals.
- neq—not equal.
- is present—included (partial match).For example, item.owner_email does not support the is present operator.
- in—included.
- not in—not included.
Connectors define the logic associated with groups of items.
The following list includes all the Connectors available:
- and—logical AND operation.
- or—logical OR operation.
- and_not—AND is not.
- or_not—OR is not.
![]()
Combine fields, operators, and connectors based on the following
syntax rules:
Syntax Rule | Example |
|---|---|
Use parentheses to group items in an expression. | (item.owner neq 'rjsmith@smith.com') |
Include field values in single quotes. | (file.type eq 'PDF') |
Recognized keywords by Data Security
and logical operators do not need quotes. | (exposure eq public) |
Use comma-separated lists for multiple values. | (file.type not_in 'PDF','PPT') |
The following are examples of advanced search expressions:
To Search for | Example |
|---|---|
| (item.owner eq 'msmith') |
| (exposure neg internal) and (email.sent is true) |
| (item.name eq 'apple vs samsung.pdf') and ((owner neq 'John T Smith') or (owner neq 'Jane Smith')) |
| (policy.name eq 'credit card number') and not ((exposure eq internal) or (exposure eq company)) or (shared.with eq 'gmail.com') |
Use Advanced Search
Learn how to use advanced search on Data Security
to isolate specific assets.
In some cases, a faceted search will
not provide you enough detail to find high priority incidents. To
isolate important problems, use advanced search to:
- Match more than one rule.
- Ignore the assets that match rules but that are not important to you.
Advanced search provides the same filters
as a basic faceted search, but gives you more options to apply connectors
and operators. For example, if you have a company policy that considers
social security numbers, tax information numbers, and credit card
numbers to be sensitive data, you may need to search for all assets
that contain any of these numbers and notify the owners.
Before
you perform an advanced search, learn how to compose an expression.
- To show the assets, select ConfigurationSaaS SecurityData SecurityData AssetsAll AssetsAdvanced.The fields policy.name, incident.category, email.sent, and assigned.to are:
- Applicable only when you perform an advanced search in the Data Assets page.
- Not applicable when you create a policy (using Match CriteriaAdvanced).
Type your expression in the search box.Your search expression is composed of a set of supported fields, operators, and values. Type an opening parenthesis to display syntax help. As you type, the autofill function displays existing values (policies, data patterns, etc), helping you build your query accurately and efficiently. For example, you can:- Search by existing policy. For example, (policy.name)—Use this option to locate incidents that you want to remediate.
![]()
- Search by existing data patterns. For example, (data_pattern.name)—Use this option to retrieve a results set with the intention of building a policy. Click Create Policy to add the expression as match criteria in a new policy.
![]()
(Optional) Export this data to a CSV file to view and sort the search results.(Optional) Take actions on the cloud assets that match your filtering criteria.- Download File or View Snippet
- Learn about the supported remediation actions.
Export Results to CSV File
Learn how to export results to a CSV file on Data Security.When you choose to download search results, such as incident and asset data, the service enables you to either download the data to a CSV file immediately or download the CSV file later after you receive an email notification with a download link. Exporting records is not the same as downloading a quarantined asset, which includes a maximum of 90 days (one record per day) and, therefore, never exceeds the record limit outlined below.Your ability to export data is directly tied to the number of records in your data set. Adhere to the following guidelines:- Before you export data, apply filters to narrow your search and shrink your data set. Only include data that you need.
- Verify the number of records in your query.
For a GDRP Report, there is no data set limit because the summary report is not based on records. The summary report includes as much data as the report needs to provide you actionable intelligence.Immediate Download Record Limit Email Download Record Limit Assets 10K 2M Incidents 10K 2M User Activity 10K 2M Quarantine 10K 2M - Click the download icon on the page.
![]() Select an export option.
Select an export option.- Download Now—Immediately downloads the CSV file to your local drive, if the file does not exceed the record limits outlined above.
- Get Email—Generates the CSV file that you request, then sends you a Your file is ready email notification with a link to download the CSV file (in .zip), if that file does not exceed the record limits outlined above.The download link is active for up to 30 days. For security reasons, you must log on as the user who initiated the request: if you forward the link to another user, the service denies that user file access.