Configure Entra ID SAML Integration for Authentication and Authorization
Table of Contents
Expand all | Collapse all
- Get Started with Common Services: Identity & Access
-
- Add an Identity Federation
- Manually Configure a SAML Identity Provider
- Upload SAML Identity Provider Metadata
- Get the URL of a SAML Identity Provider
- Clone SAML Identity Provider Configuration
- Add or Delete an Identity Federation Owner
- Configure Palo Alto Networks as a Service Provider
- Delete an Identity Federation
- Map a Tenant for Authorization
- Update Tenant Mapping for Authorization
- PAN Resource Name Mapping Properties
- Manage Single Tenant Transition to Multitenant
- Release Updates
Configure Entra ID SAML Integration for Authentication and Authorization
Configure SAML integration where Microsoft Entra ID handles both user authentication
and authorization, with roles and permissions defined in Entra ID.
This section describes how to configure a Security Assertion Markup Language (SAML)
integration where Microsoft Entra ID acts as the identity provider and the SCM
platform acts as the Service Provider (SP). In this setup, Entra ID is used for both
user authentication and authorization—users sign in through Entra ID, and their
roles and permissions are also defined and managed there.
- Add and verify your domain.This step establishes the trust boundary between your tenant and domain through DNS verification. You add your organization's domain and verify ownership by adding a DNS TXT record. This verification is required for creating an identity federation and is the foundation for all subsequent SSO configuration.
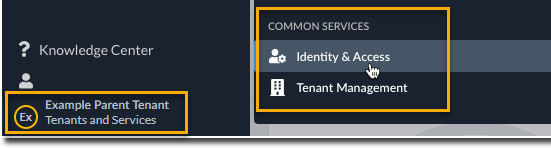
- Use one of the various ways to access Common ServicesIdentity & Access.
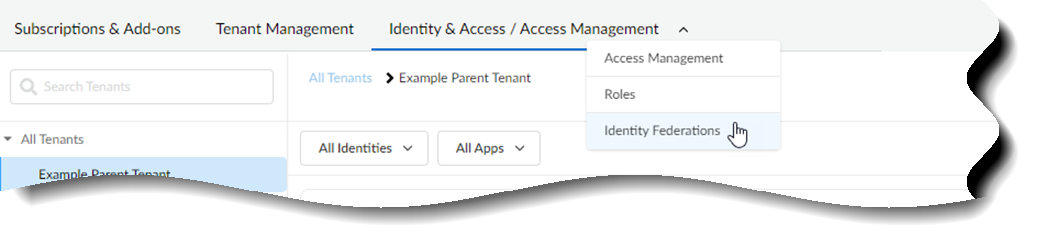
![]() Select Identity & Access.Select Identity & Access/Access ManagementIdentity FederationsAdd Identity Federation to add an identity federation.
Select Identity & Access.Select Identity & Access/Access ManagementIdentity FederationsAdd Identity Federation to add an identity federation.![]()
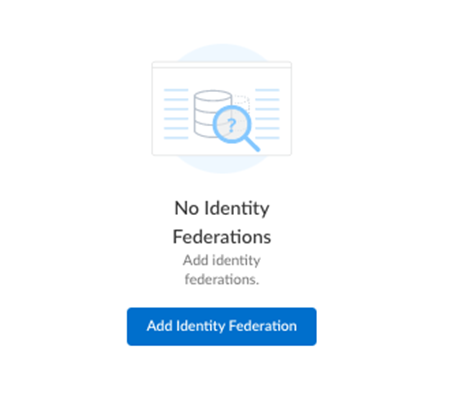
![]() Add the Domain information for your enterprise.The character limit is 50. Special characters are not allowed, with the exception of "-" and "."Select Next.Follow the Instructions for Verification to add a DNS record within your domain name provider.
Add the Domain information for your enterprise.The character limit is 50. Special characters are not allowed, with the exception of "-" and "."Select Next.Follow the Instructions for Verification to add a DNS record within your domain name provider.- Copy the TXT record from Common Services.
- Select Finish.
- Go to your domain provider's console and paste the TXT record, so that Palo Alto Networks can verify that you are an owner of the domain.
- (Optional) In the domain provider's console, revise your identity provider's time to live (TTL) setting if you need a faster refresh rate. The TTL setting impacts, for example, how long it takes to verify ownership of the identity federation.
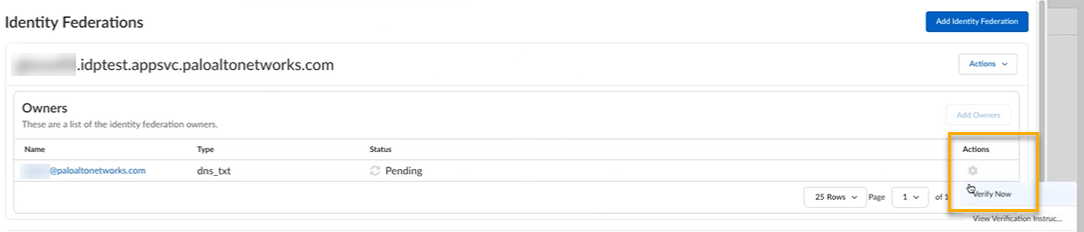
![]() In Common Services, select Verify Now to verify ownership of the identity federation.
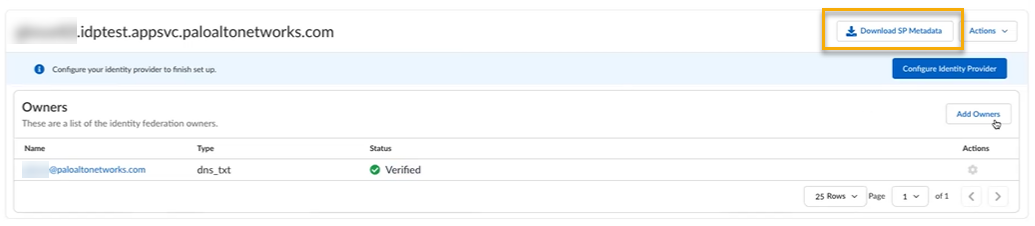
In Common Services, select Verify Now to verify ownership of the identity federation.![]() Download the SAML metadata.After you add an identity federation, you can configure Palo Alto Networks as a service provider by downloading the service provider (SP) metadata from Common Services. The SP metadata helps you configure your identity provider integration with Palo Alto Networks as an SP, so that you don't have to provide the details manually.
Download the SAML metadata.After you add an identity federation, you can configure Palo Alto Networks as a service provider by downloading the service provider (SP) metadata from Common Services. The SP metadata helps you configure your identity provider integration with Palo Alto Networks as an SP, so that you don't have to provide the details manually.- Use one of the various ways to access Common ServicesIdentity & Access.Select Identity & Access/Access ManagementIdentity Federations.
![]() Scroll to your identity federation and select Download SP Metadata.
Scroll to your identity federation and select Download SP Metadata.![]() Save the metadata file in a secure location. You need this file to upload to Entra ID. The metadata file contains the Entity ID, Assertion Consumer Service (ACS) URL, and certificate that Entra ID needs to send SAML assertions.Create an enterprise application in Entra ID and configure it to use SAML for single sign-on.
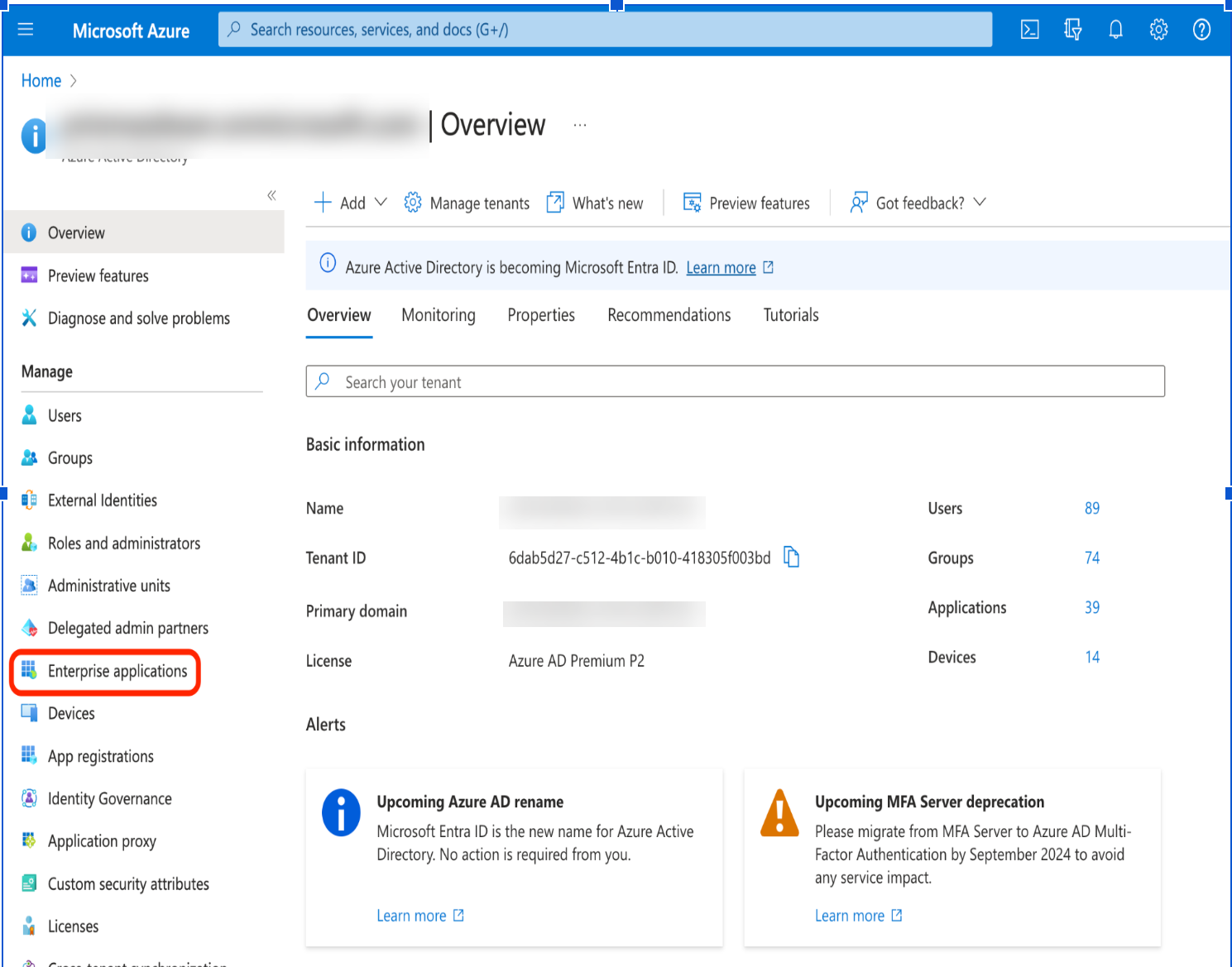
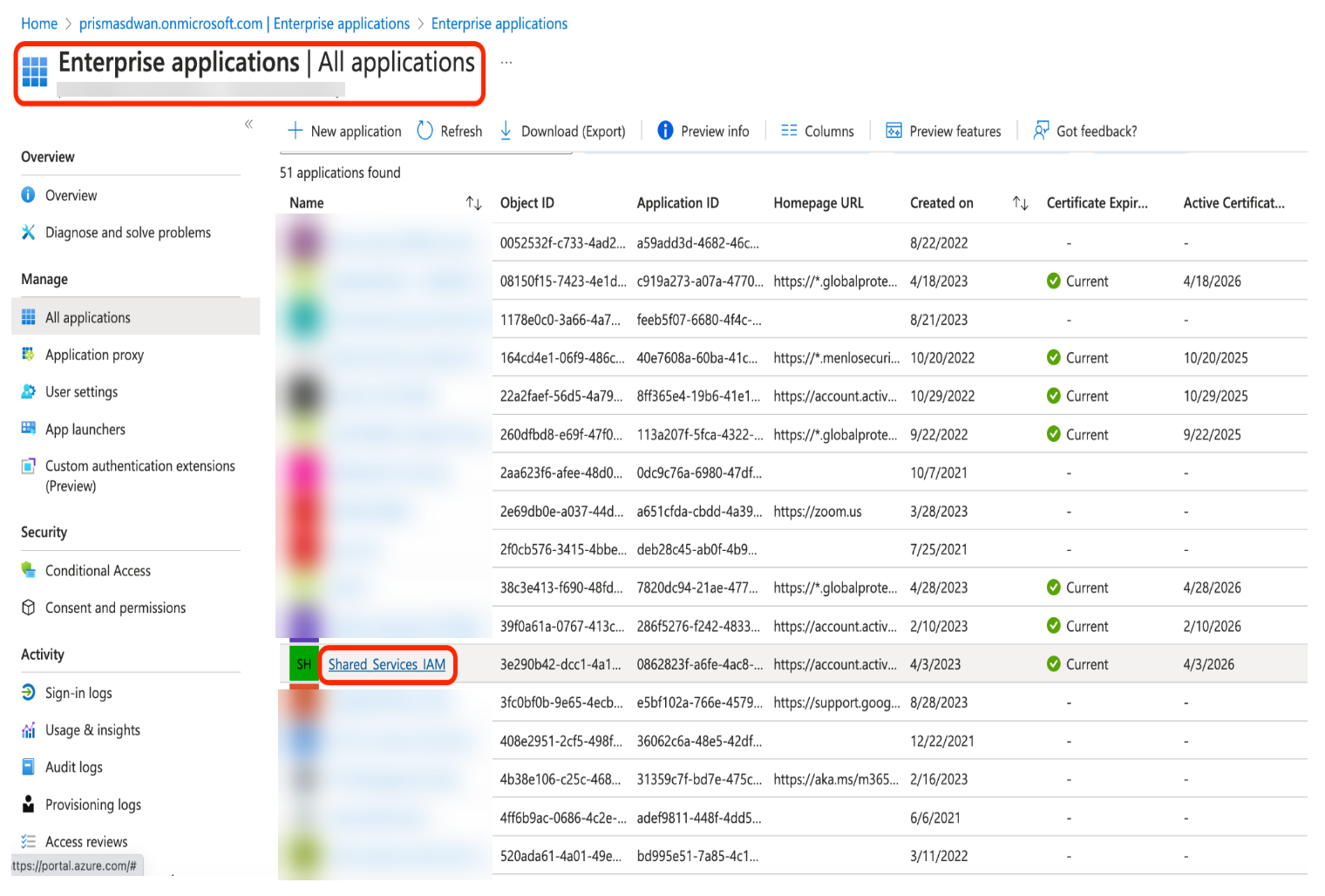
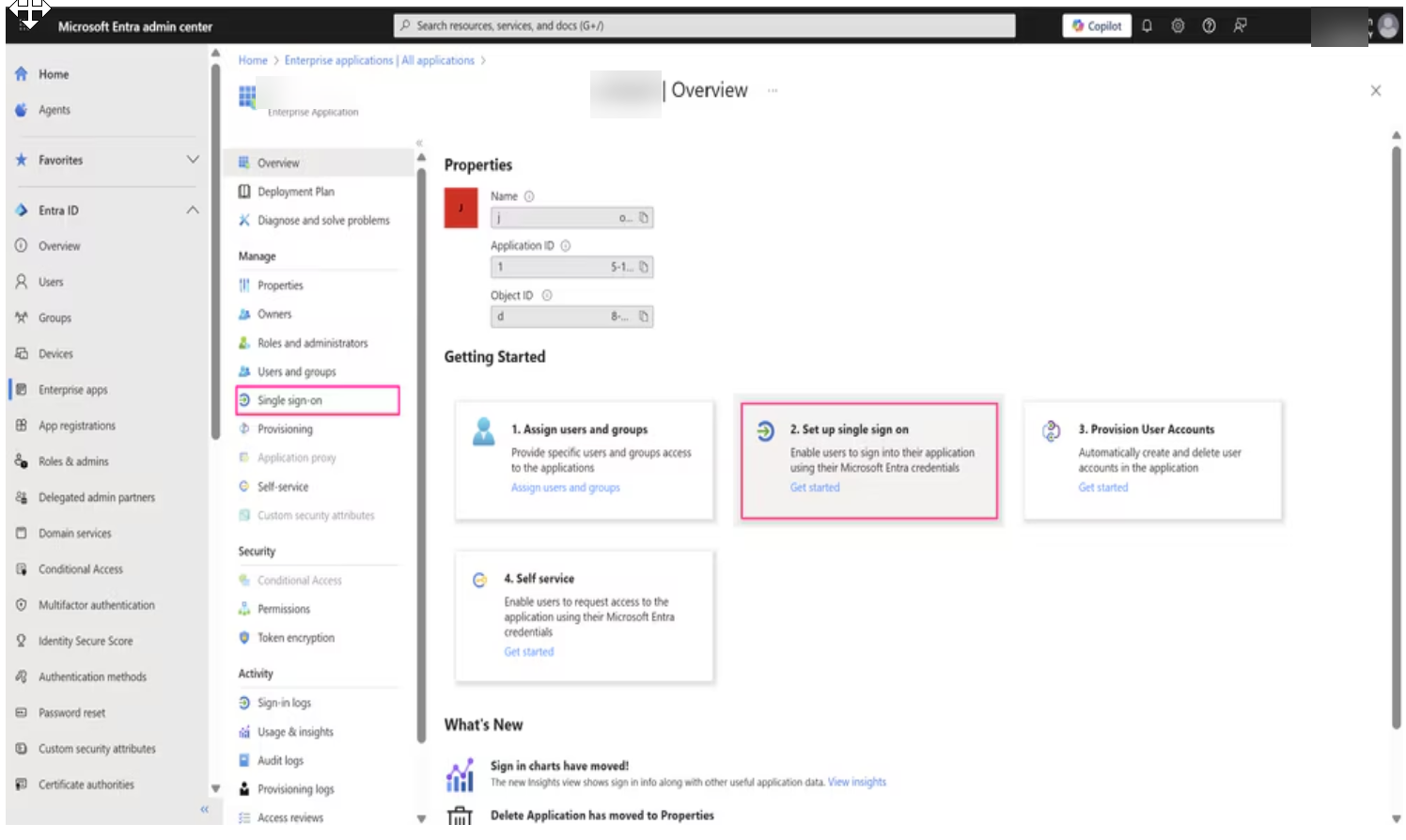
Save the metadata file in a secure location. You need this file to upload to Entra ID. The metadata file contains the Entity ID, Assertion Consumer Service (ACS) URL, and certificate that Entra ID needs to send SAML assertions.Create an enterprise application in Entra ID and configure it to use SAML for single sign-on.- Log in to the Entra ID Portal with your Cloud Application Administrator or Application Administrator account.Select Enterprise applications.
![]() Select the application that you enabled for SAML authentication.
Select the application that you enabled for SAML authentication.![]() In the enterprise application, go to Single sign-onSet up Single Sign-On and then select SAML.
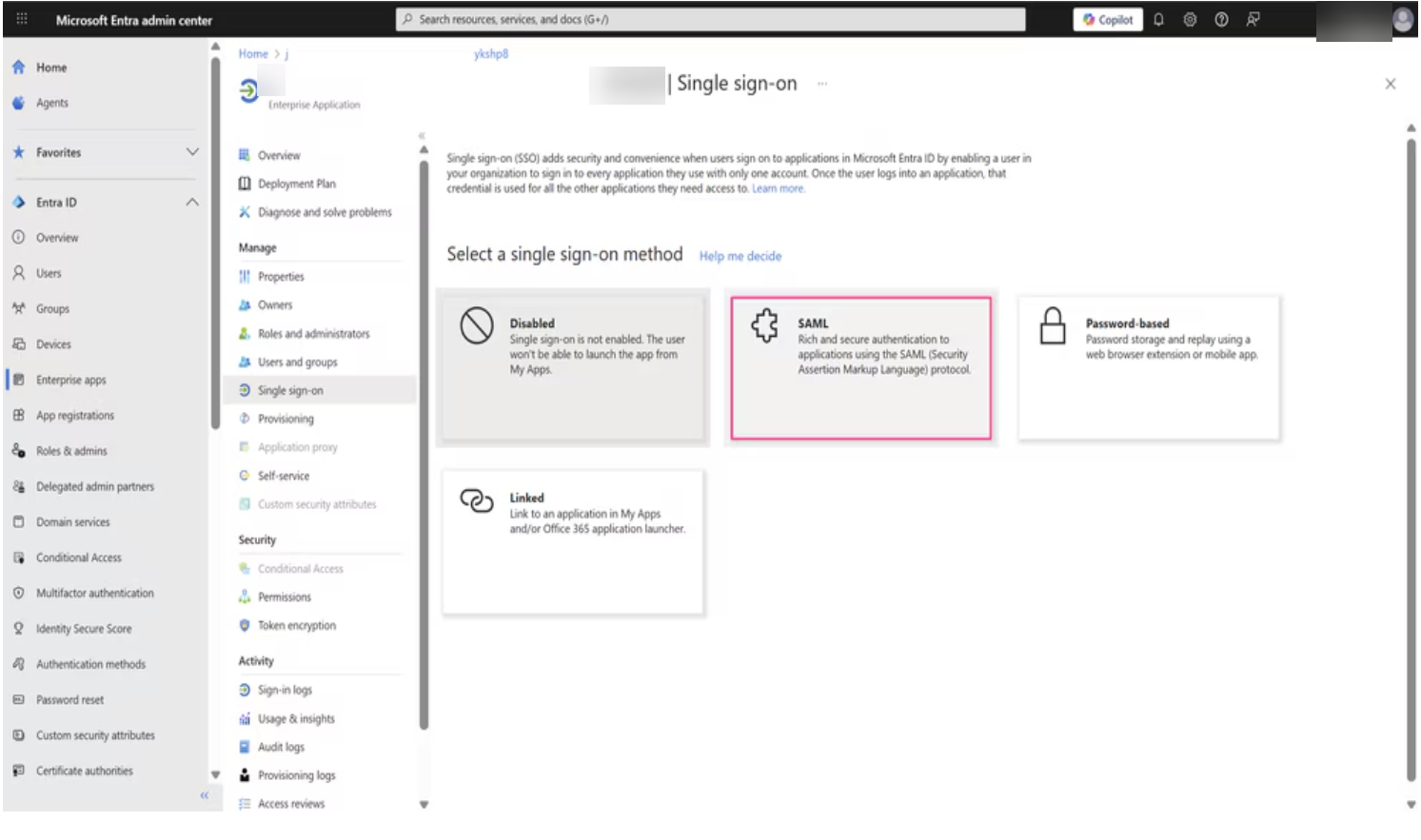
In the enterprise application, go to Single sign-onSet up Single Sign-On and then select SAML.![]() Select SAML.
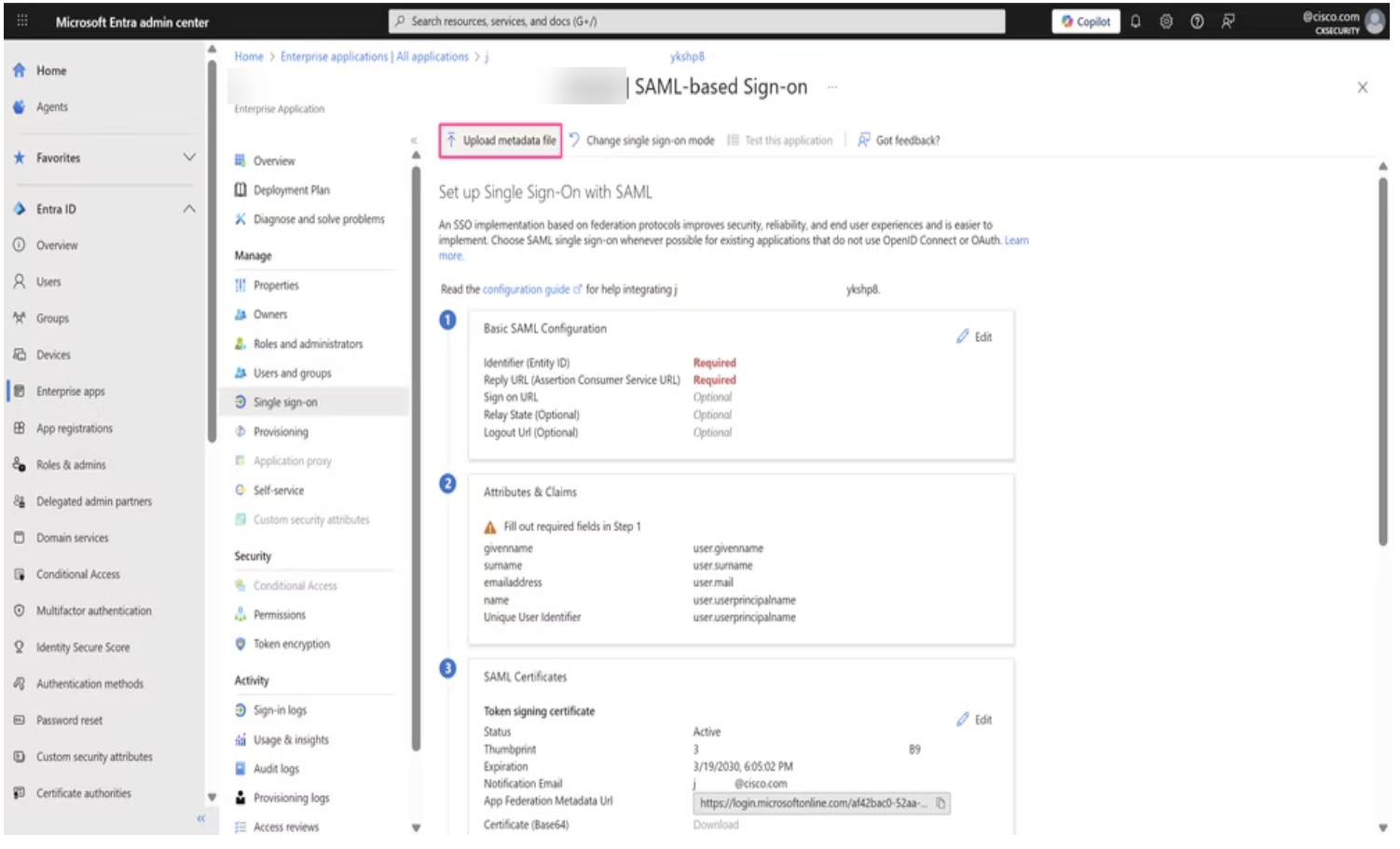
Select SAML.![]() On the SAML configuration page, click Upload metadata file and select the metadata file you downloaded in the previous step.
On the SAML configuration page, click Upload metadata file and select the metadata file you downloaded in the previous step.![]() After uploading the metadata, verify that the following fields are correctly populated in the Basic SAML Configuration section:
After uploading the metadata, verify that the following fields are correctly populated in the Basic SAML Configuration section:- Identifier (Entity ID)- The Entity ID from the metadata
- Reply URL (ACS URL) - The SAML assertion consumer service endpoint
- Logout URL- The logout endpoint
If any field is incorrect, click Edit in the Basic SAML Configuration section and update the values to match the metadata.Create users and groups in Entra ID and map the user group to the enterprise application to authorize which users can access the platform.- In the Entra ID portal, open the enterprise application that you created.Add new users to the application.Create a new user group and assign users to the group.Assign the user group to the enterprise application.Configure SAML claims and access policies in Entra ID to pass user role information based on group membership.
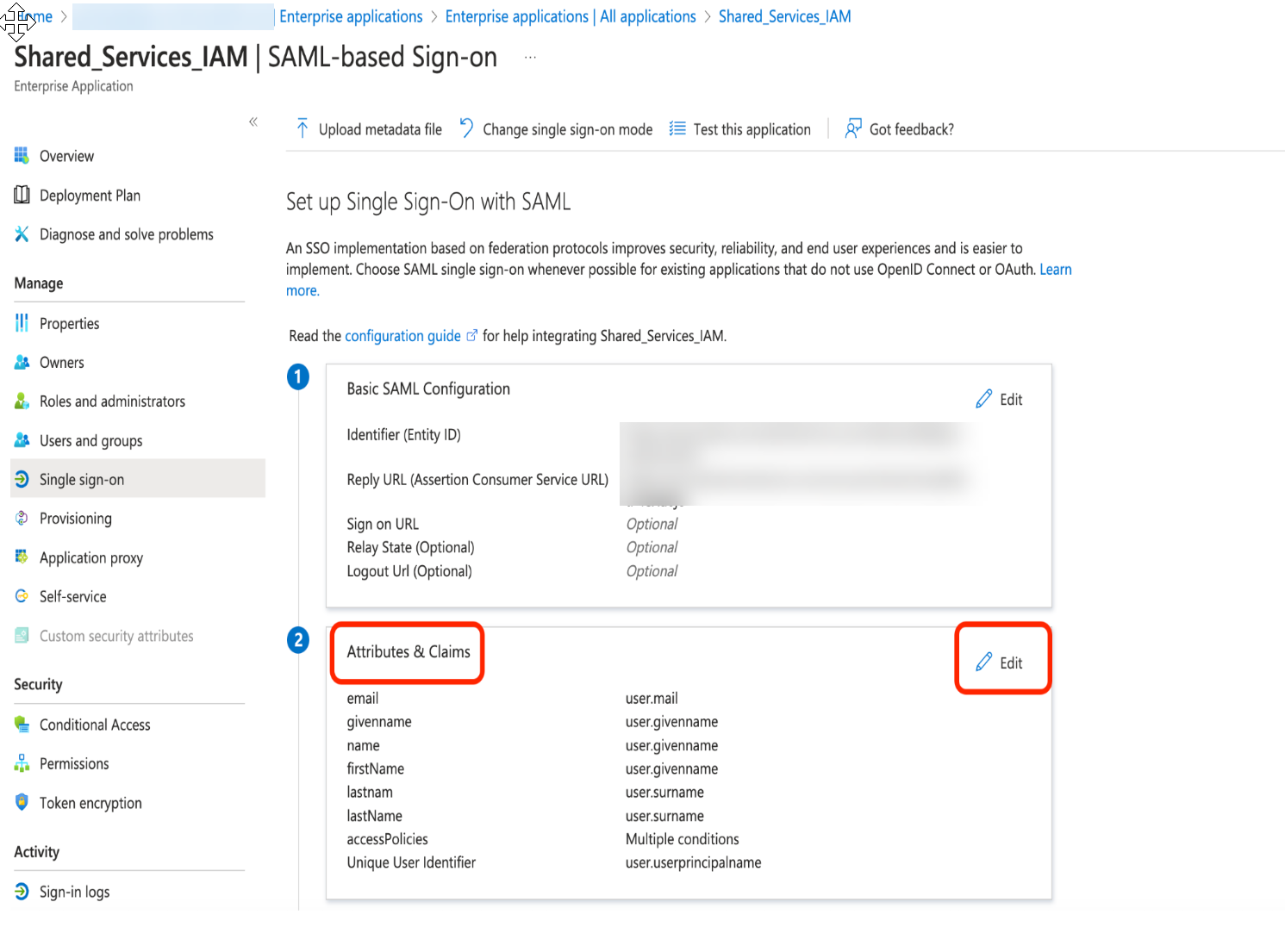
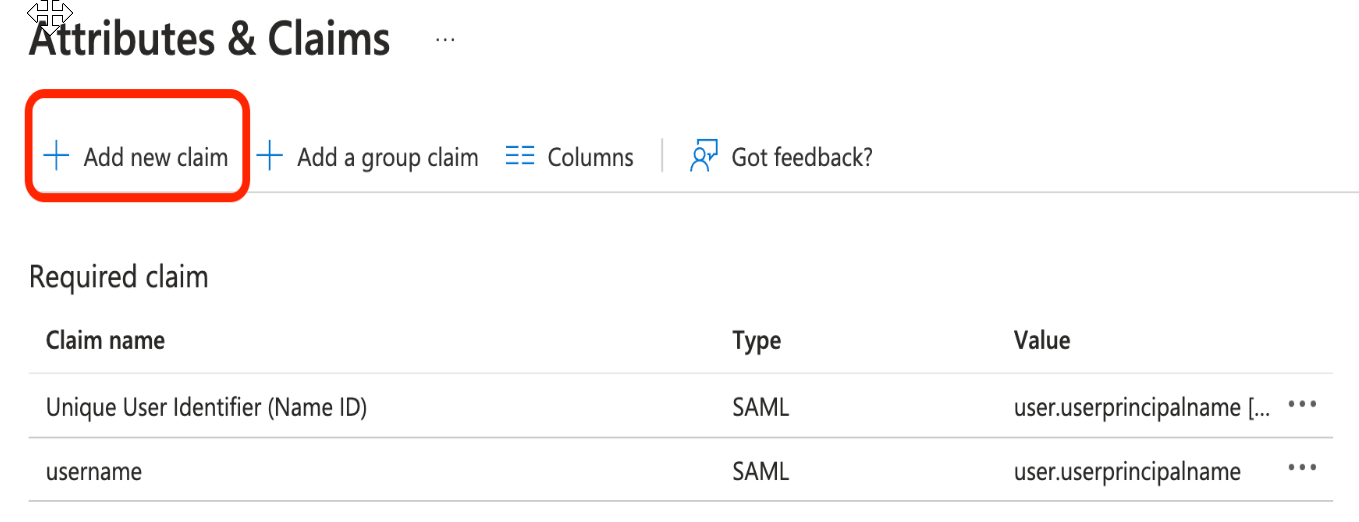
- In the Entra ID portal, open the enterprise application you created and select Single sign-onAttributes & Claims.
![]() Remove all existing claims and add the following new claims:
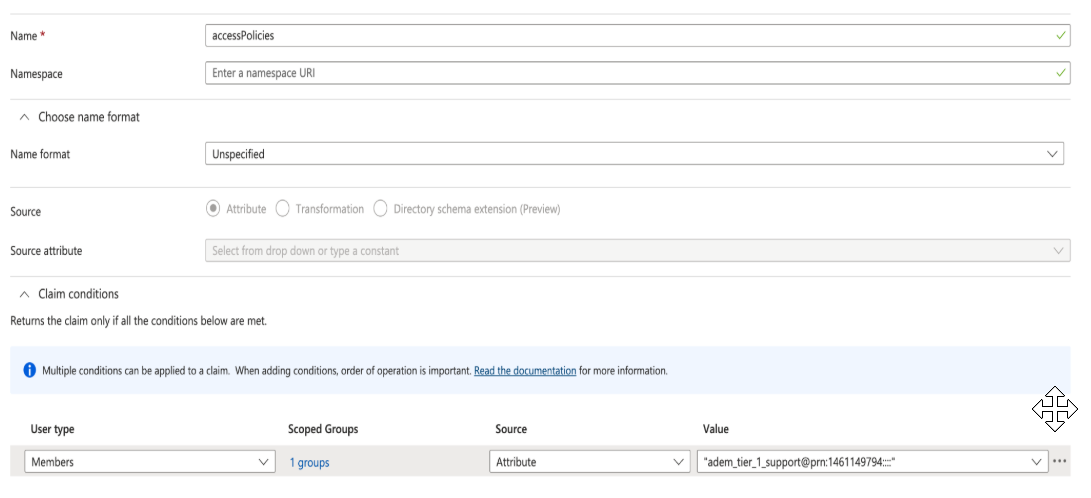
Remove all existing claims and add the following new claims:Claim Name Claim Value firstName user.firstName lastName user.lastName email user.email ![]() Create a conditional claim with the source attribute pointing to the role and Tenant Service Group (TSG) ID.
Create a conditional claim with the source attribute pointing to the role and Tenant Service Group (TSG) ID.![]() Scoped Group: Add the group whose members are authorized using the claim value that includes the role and TSG ID.Claim value format: <predefined_role_name or custom_role_id>@prn:<TSG_ID>:<app_id>:<region>:<instance>:<resource_scope>For the role-name or role-id in the claim value:
Scoped Group: Add the group whose members are authorized using the claim value that includes the role and TSG ID.Claim value format: <predefined_role_name or custom_role_id>@prn:<TSG_ID>:<app_id>:<region>:<instance>:<resource_scope>For the role-name or role-id in the claim value:- Use a predefined role to assign a predefined set of permissions to a user. For details and syntax, see properties for predefined roles.
- Use a custom role to assign a custom set of permissions to a user. For details and syntax, see properties for custom roles.
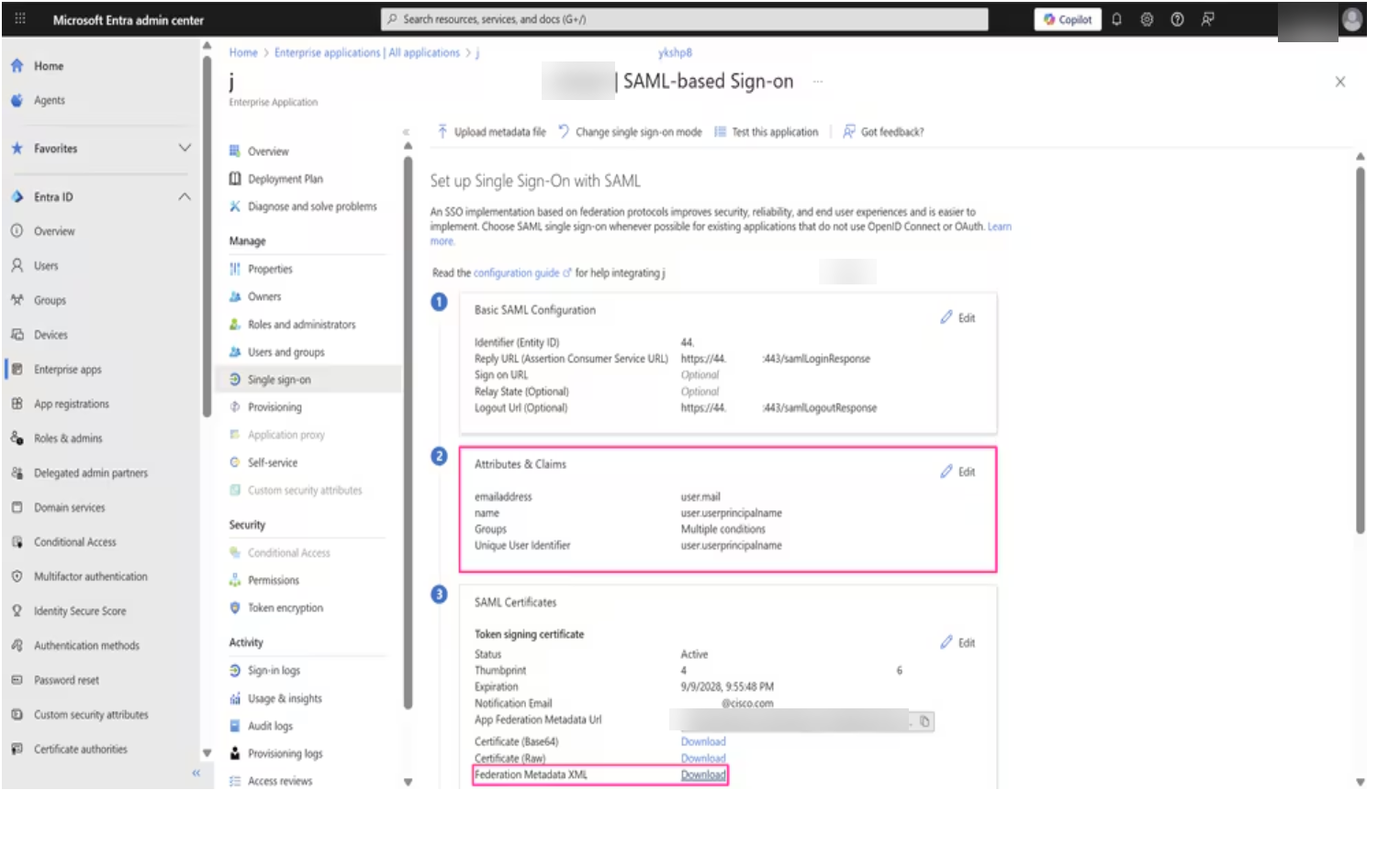
Click Save to apply all changes.Click Download next to Federation Metadata XML to download the Entra ID metadata file.Save the metadata file in a secure location. You need this file to upload to the platform.![]() Upload the Entra ID metadata to complete the integration.
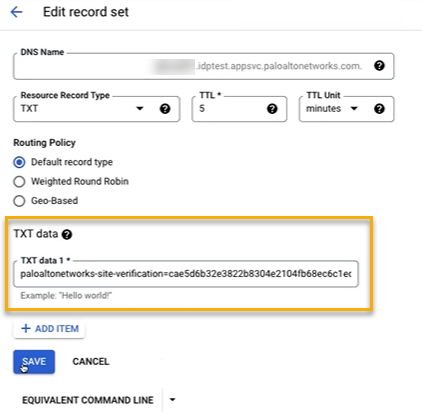
Upload the Entra ID metadata to complete the integration.- Use one of the various ways to access Common ServicesIdentity & Access.Select Common ServicesIdentity & AccessIdentity Federations.
![]() Select Configure Identity Provider.
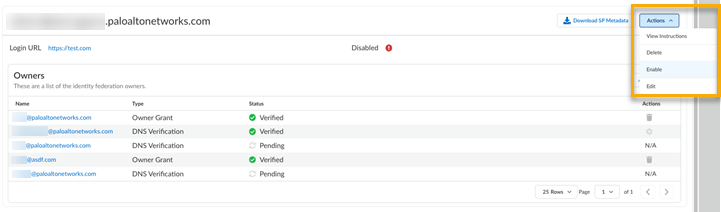
Select Configure Identity Provider.![]() Select Upload Metadata and choose the file downloaded in the previous step.After the provider profile fields auto-populate, select Finish.The Configure Identity Provider button is replaced with the Login URL. Select ActionsEnable.
Select Upload Metadata and choose the file downloaded in the previous step.After the provider profile fields auto-populate, select Finish.The Configure Identity Provider button is replaced with the Login URL. Select ActionsEnable.![]() The Login URL is how Palo Alto Networks knows where to send the user when they log in. This is disabled by default.Map a tenant for authorization.If you want to grant authorization to your users by passing the login information through your SAML provider, you can map your identity federation to a tenant or tenant service group (TSG) hierarchy. By using the tenant mapping, you no longer have to add users and access directly through Common Services, but that option is still available.After you add an identity federation and add an identity federation owner, the federation owner can map tenants for authorization. In addition to adding an admin as a federation owner, you must also give that admin a role that has permissions to assign and remove access policies on the given tenant, such as the following:
The Login URL is how Palo Alto Networks knows where to send the user when they log in. This is disabled by default.Map a tenant for authorization.If you want to grant authorization to your users by passing the login information through your SAML provider, you can map your identity federation to a tenant or tenant service group (TSG) hierarchy. By using the tenant mapping, you no longer have to add users and access directly through Common Services, but that option is still available.After you add an identity federation and add an identity federation owner, the federation owner can map tenants for authorization. In addition to adding an admin as a federation owner, you must also give that admin a role that has permissions to assign and remove access policies on the given tenant, such as the following:- IAM Administrator
- Multitenant IAM Administrator
- Multitenant Superuser
- Superuser
- Custom role that includes iam.federation_mapping.update and iam.federation_mapping.delete
- Use one of the various ways to access Identity & Access.Select Identity & Access/Access ManagementIdentity Federations.
![]() Scroll or search to find your identity federation.Select Edit Tenant Mapping for Authorization.
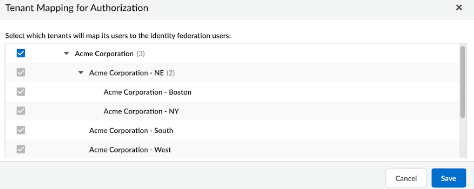
Scroll or search to find your identity federation.Select Edit Tenant Mapping for Authorization.![]() Select which tenants can map users to the identity federation users and Save.
Select which tenants can map users to the identity federation users and Save.![]() Inheritance applies the same way as it does in access management. If you map a tenant at the top level of the hierarchy, the child tenants nested below it inherit the mapping so that the parent can manage them.The identity federation owner can now manage the user access for all the selected tenant service groups.
Inheritance applies the same way as it does in access management. If you map a tenant at the top level of the hierarchy, the child tenants nested below it inherit the mapping so that the parent can manage them.The identity federation owner can now manage the user access for all the selected tenant service groups.