Simplified IoT Security Onboarding
Table of Contents
10.2
Expand all | Collapse all
-
- CN-Series Firewall as a Kubernetes CNF
- High Availability Support for CN-Series Firewall as a Kubernetes CNF
- High Availability Support for CN-Series Firewall on AWS EKS
- DPDK Support for CN-Series Firewall
- Daemonset(vWire) IPv6 Support
- Panorama Plugin for Kubernetes 3.0.0
- L3 IPV4 Support for CN-Series
- 47 Dataplane Cores Support for VM-Series and CN-Series Firewalls
- Memory Scaling of the VM-Series Firewall
Simplified IoT Security Onboarding
Use a simplified workflow to add a Log Forwarding profile
to the Security policy rules on your firewall.
When onboarding IoT Security, a part of the
firewall setup involves creating a Log Forwarding profile and applying
it to Security policy rules. From PAN-OS 10.2, you simply select
a predefined Log Forwarding profile and apply it to as many rules
as you like in bulk.
To use this workflow, you must
have already configured Security policy rules,
enabled logging on the rules, and enabled logging services with
enhanced application logging.
- Apply a Log Forwarding profile for IoT Security to Security policy rules.
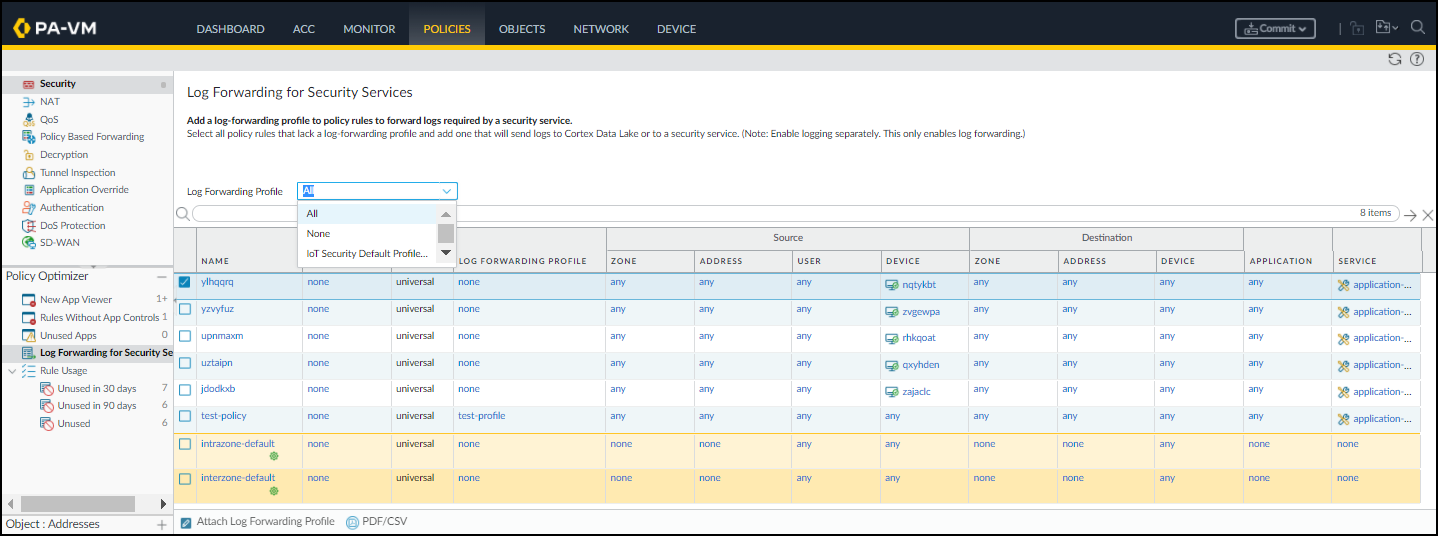
- Log in to your next-generation firewall, select PoliciesLog Forwarding for Security Services in the Policy Optimizer section.
- To view all your Security policy rules—including those with a Log Forwarding profile and those without it—choose All for Log Forwarding Profile.
![]()
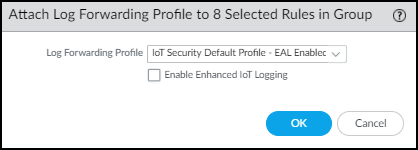
- Select the rules for which you want to forward logs to the logging service and Attach Log Forwarding Profile.
- To apply the default Log Forwarding profile to your rules, choose IoT Security Default Profile - EAL Enabled and then OK.The default profile is preconfigured to provide IoT Security with all the log types it requires, including enhanced application logs (EALs).You don’t have to select Enable Enhanced IoT Logging because enhanced application logging (EAL) is already enabled on IoT Security Default Profile.
![]() orTo add the forwarding of EALs to an existing Log Forwarding profile that doesn’t already have it, choose it from the Log Forwarding Profile list, select Enable Enhanced IoT Logging, and then OK.When you select Enable Enhanced IoT Logging, PAN-OS updates the chosen Log Forwarding profile itself and thereby enables enhanced log forwarding on all rules that use the same Log Forwarding profile.PAN-OS adds the chosen Log Forwarding profile to those rules that don’t already have one and replaces previously assigned profiles with this one.
orTo add the forwarding of EALs to an existing Log Forwarding profile that doesn’t already have it, choose it from the Log Forwarding Profile list, select Enable Enhanced IoT Logging, and then OK.When you select Enable Enhanced IoT Logging, PAN-OS updates the chosen Log Forwarding profile itself and thereby enables enhanced log forwarding on all rules that use the same Log Forwarding profile.PAN-OS adds the chosen Log Forwarding profile to those rules that don’t already have one and replaces previously assigned profiles with this one.
Commit your changes.