SaaS Security
Begin Scanning a Slack Enterprise App
Table of Contents
Expand All
|
Collapse All
SaaS Security Docs
Begin Scanning a Slack Enterprise App
Authorize Data Security to connect to Slack Enterprise to scan all content
shared within the app.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Data Security license:
|
In addition to the Grid license, Data Security also supports the Select license for Slack Enterprise.
If you have Slack Pro or Slack Business+ plan, you must
onboard using the Slack Pro and Business app
instead.
Delete any previously
installed Slack Enterprise Grid app of the same instance before onboarding Slack
Enterprise. If you use both versions at the same time, rate limits for Slack
will be shared between the two and might impact asset discovery.
To connect Slack Enterprise to Data Security and begin scanning assets, you need to:
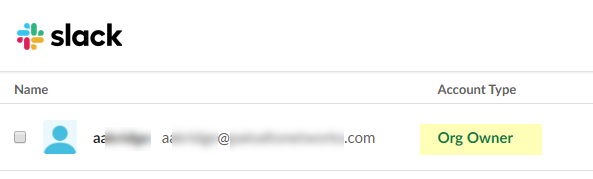
- Ensure that you have a Slack Enterprise administrator account with Organization Owner permissions.
- Grant Data Security access to Slack.
- Add the Slack Enterprise app to Data Security, providing Data Security information about your Slack account.
Support for automated remediation capabilities varies by SaaS application.
Add Slack Enterprise App
For Data Security to scan assets, you must consent to specific permissions during adding
the Slack Enterprise app.
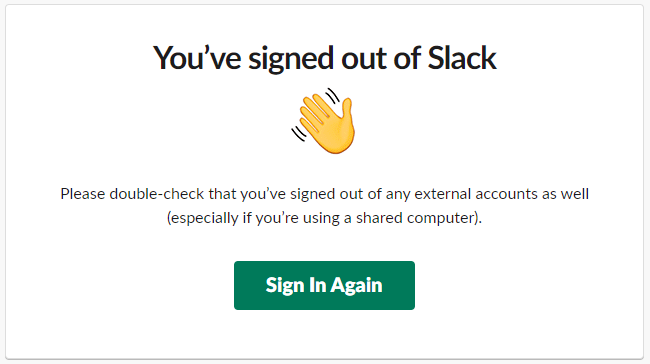
- (Recommended) Add your Slack Enterprise domain as an internal domain.See Define Your Internal Domains.Sign out of all Slack workspaces.Doing so ensures that you sign in under the correct account and workspace.
![]() Enable the privileges required for communication between Data Security and the Slack app.The Organization Owner must contact exports@slack.com and request that Slack Support enables the Slack app for DLP API access and integration with Data Security. Slack Support requires over-the-phone enablement whereby you answer a series of security questions.DLP API access provides visibility into the assets in Slack and allows Data Security to monitor the sharing of assets.To add the Slack app, go to Data SecurityApplicationsAdd ApplicationSlack Enterprise.
Enable the privileges required for communication between Data Security and the Slack app.The Organization Owner must contact exports@slack.com and request that Slack Support enables the Slack app for DLP API access and integration with Data Security. Slack Support requires over-the-phone enablement whereby you answer a series of security questions.DLP API access provides visibility into the assets in Slack and allows Data Security to monitor the sharing of assets.To add the Slack app, go to Data SecurityApplicationsAdd ApplicationSlack Enterprise.![]()
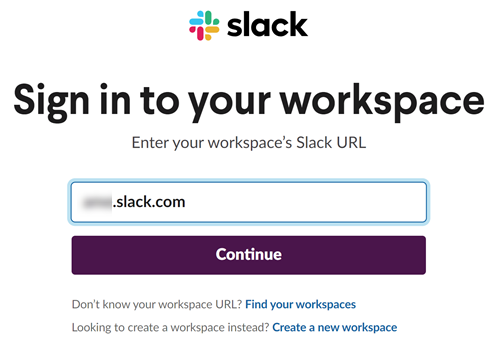
- Select Slack Enterprise.Select Connect to Slack Enterprise Account.Enter your team’s Slack domain or workspace (top-level enterprise organization), then Continue.
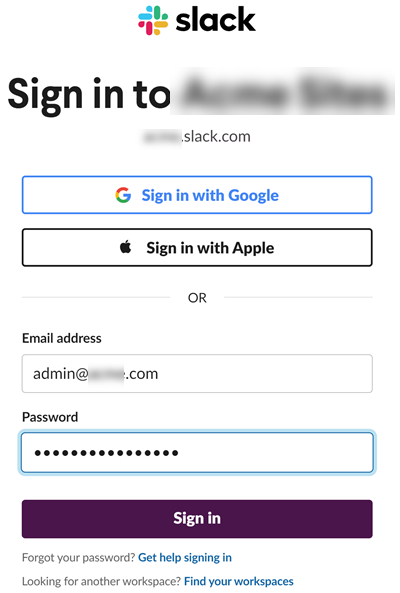
![]() Sign in with an administrator account that is an Organization Owner.If this account is deleted from Slack, the associated credentials or tokens will be revoked. Therefore, it is advisable to create a service account that remains unaffected by deletions, ensuring uninterrupted access to APIs.
Sign in with an administrator account that is an Organization Owner.If this account is deleted from Slack, the associated credentials or tokens will be revoked. Therefore, it is advisable to create a service account that remains unaffected by deletions, ensuring uninterrupted access to APIs.![]()
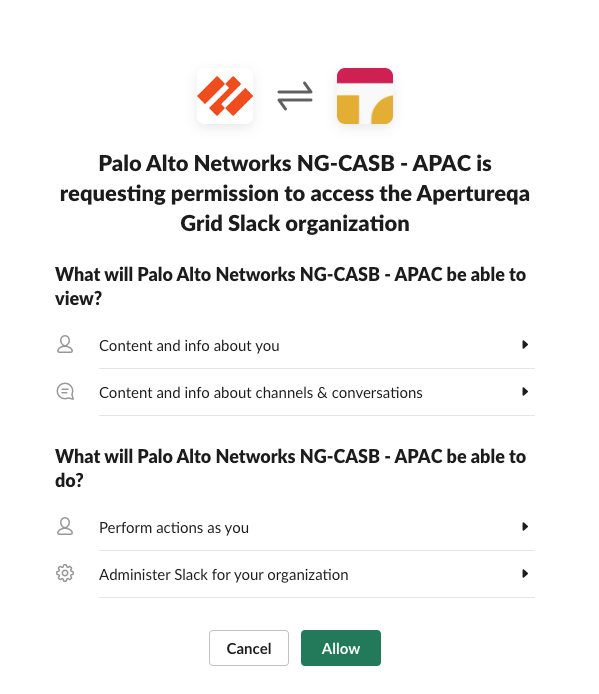
![]() Review and Allow the requested permissions.Data Security requires these permissions to scan your assets on Slack Enterprise.
Review and Allow the requested permissions.Data Security requires these permissions to scan your assets on Slack Enterprise.Enable Notifications Using Slack Bot
- Authorize a Data Security bot to enable notifications.
- Select the Slack n link on the Cloud Apps list.
(Optional) Customize your Slack Enterprise App Instance
- Give a descriptive name to this app instance.
- Select the Slack n link on the Cloud Apps list.Enter a descriptive Name to differentiate this instance of Slack from other instances.Click Done to save your changes.
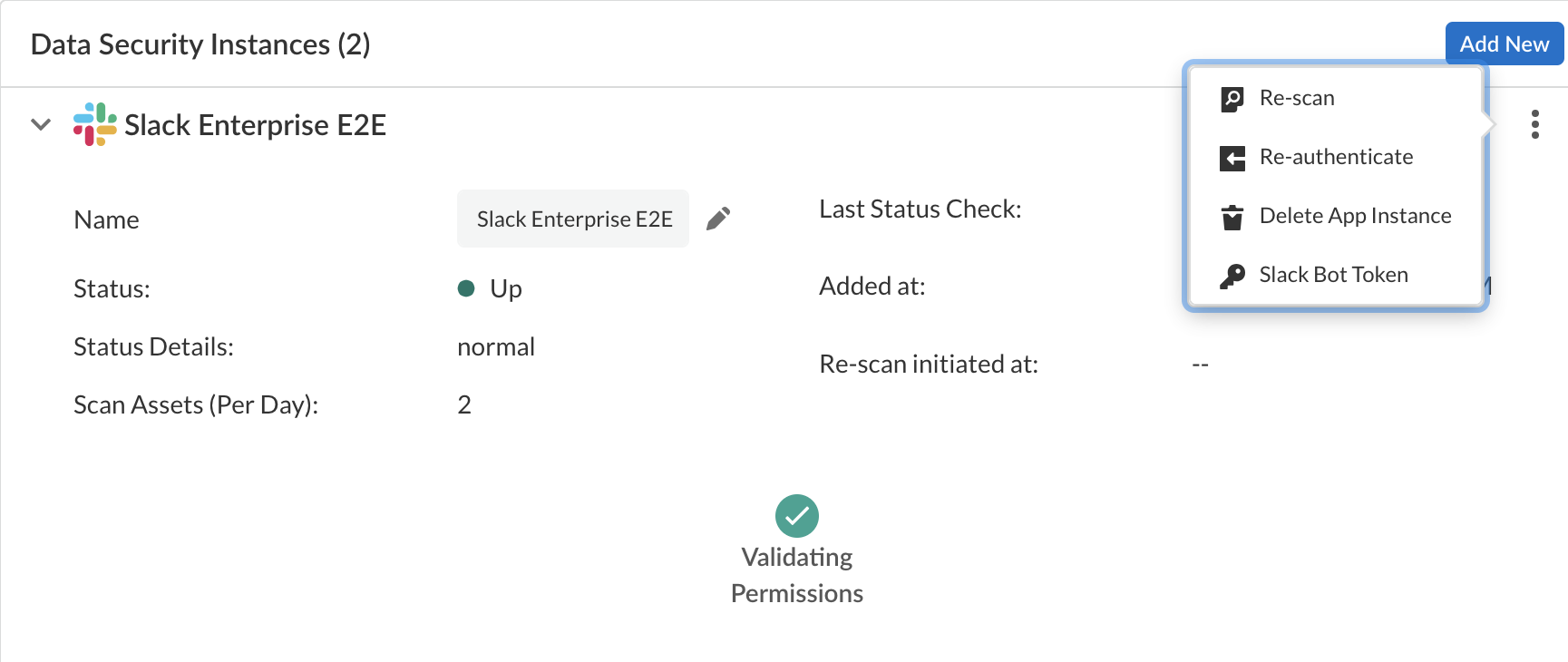
Troubleshooting Onboarding for Slack Enterprise App
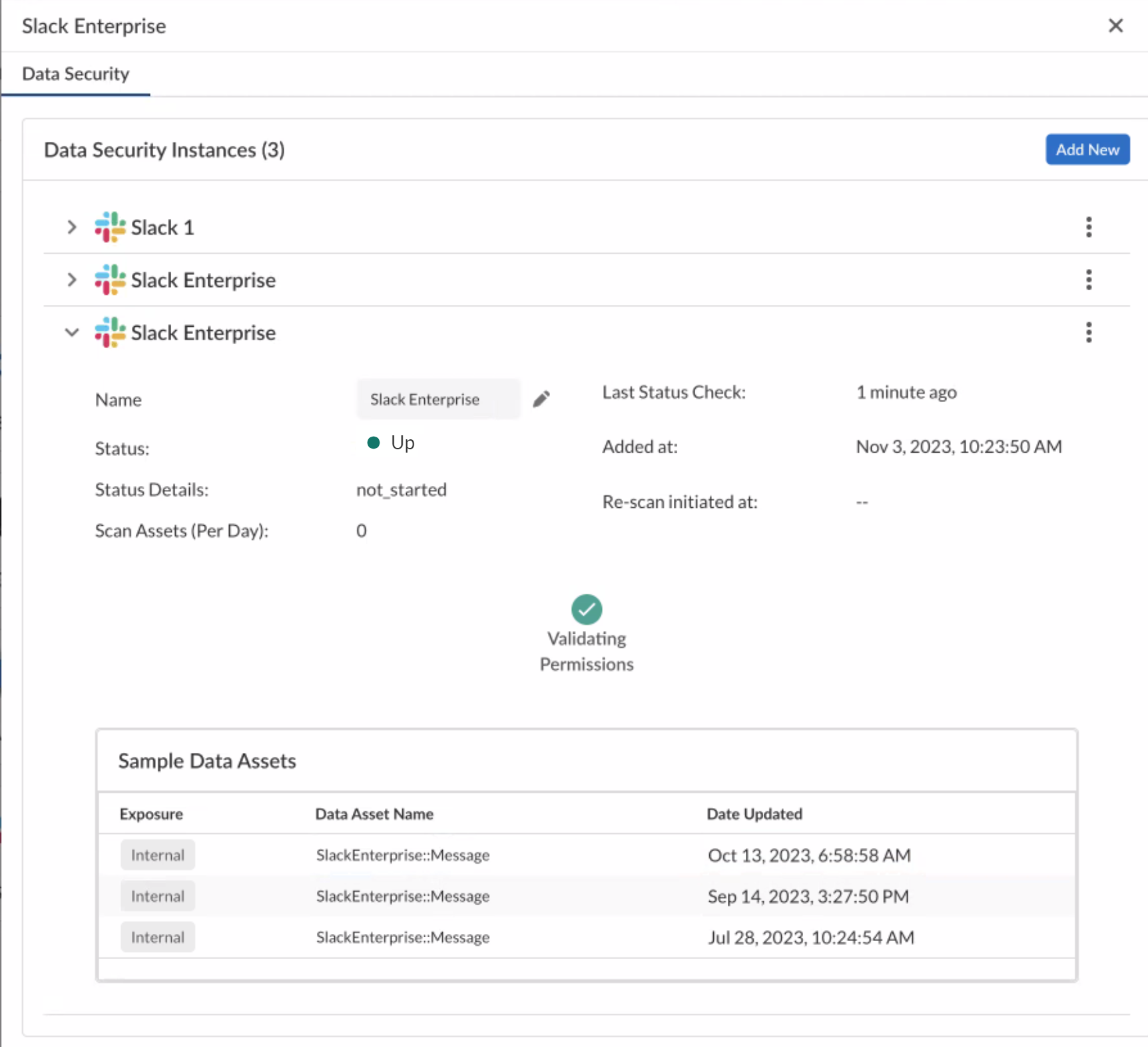
To ensure that your app has onboarded correctly without any issues in authentication or permissions, Data Security performs validation checks between the onboarding and scanning process. You can start scanning only after a successful validation. For Slack Enterprise, the following validation happens:- Validating Permissions
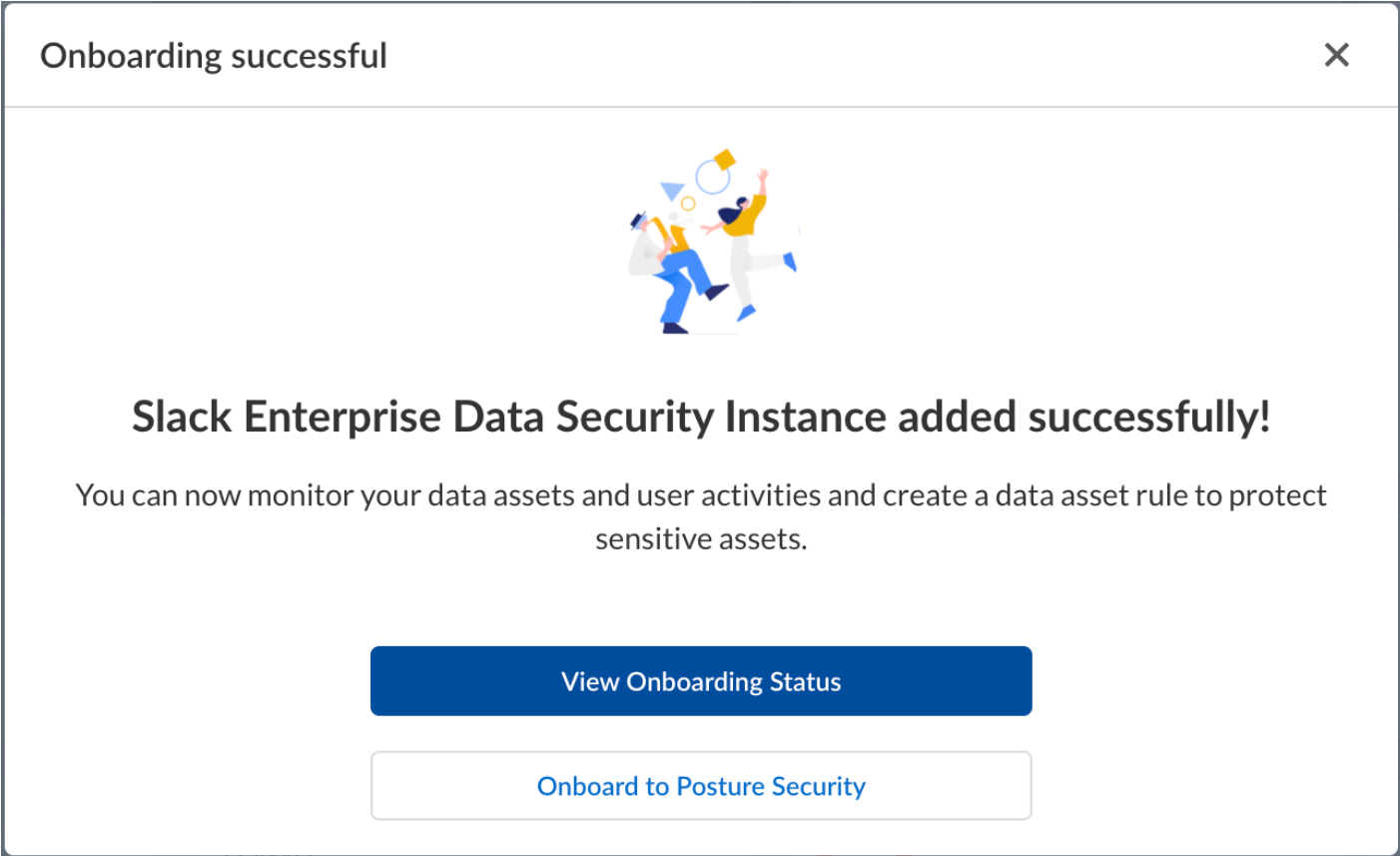
After the validation is successful, Data Security displays the sample data assets.![]() If the Validating Permissions check fails, ensure you have administrator permissions.If you are unable to configure Slack notifications, try the following:
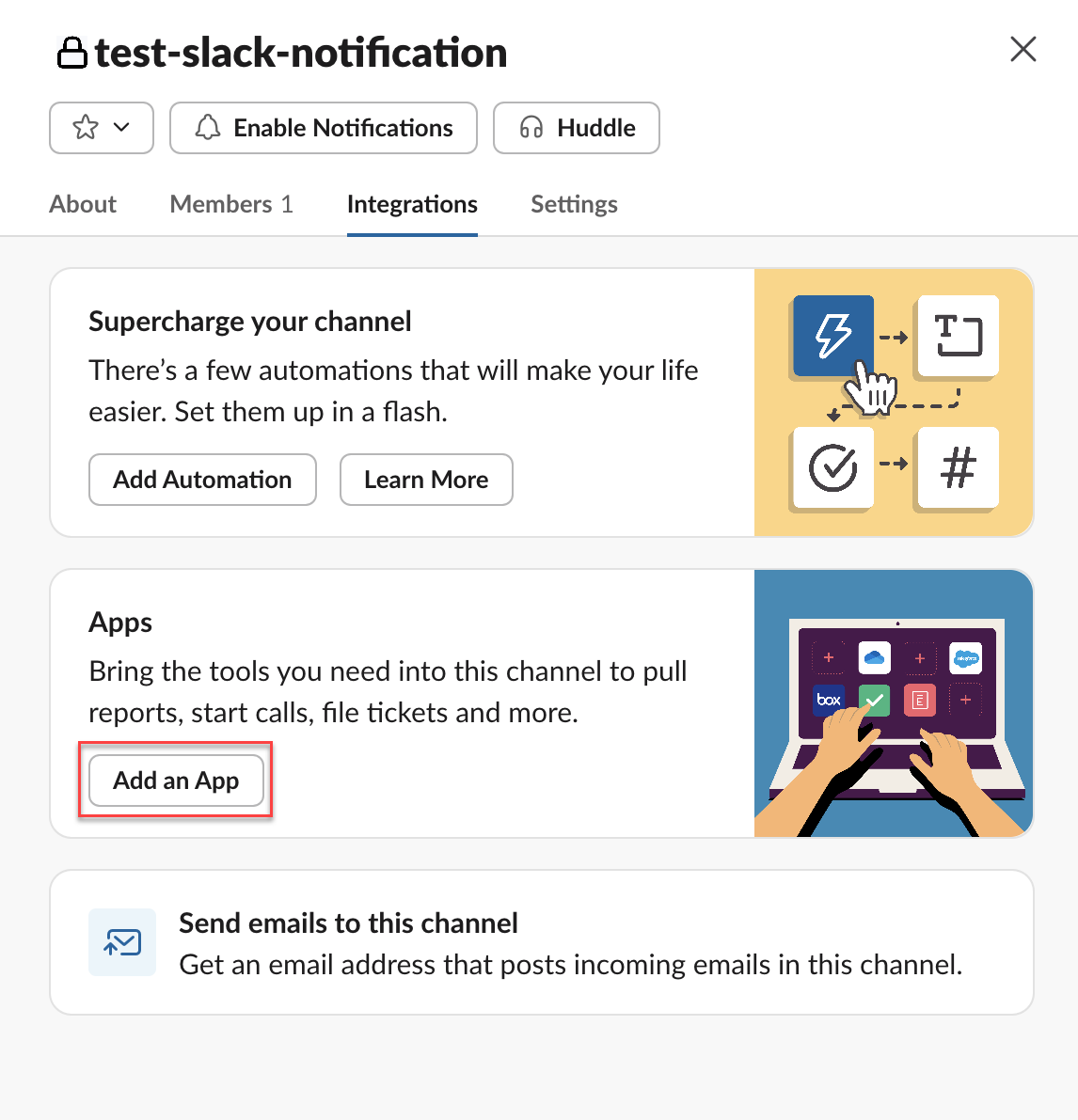
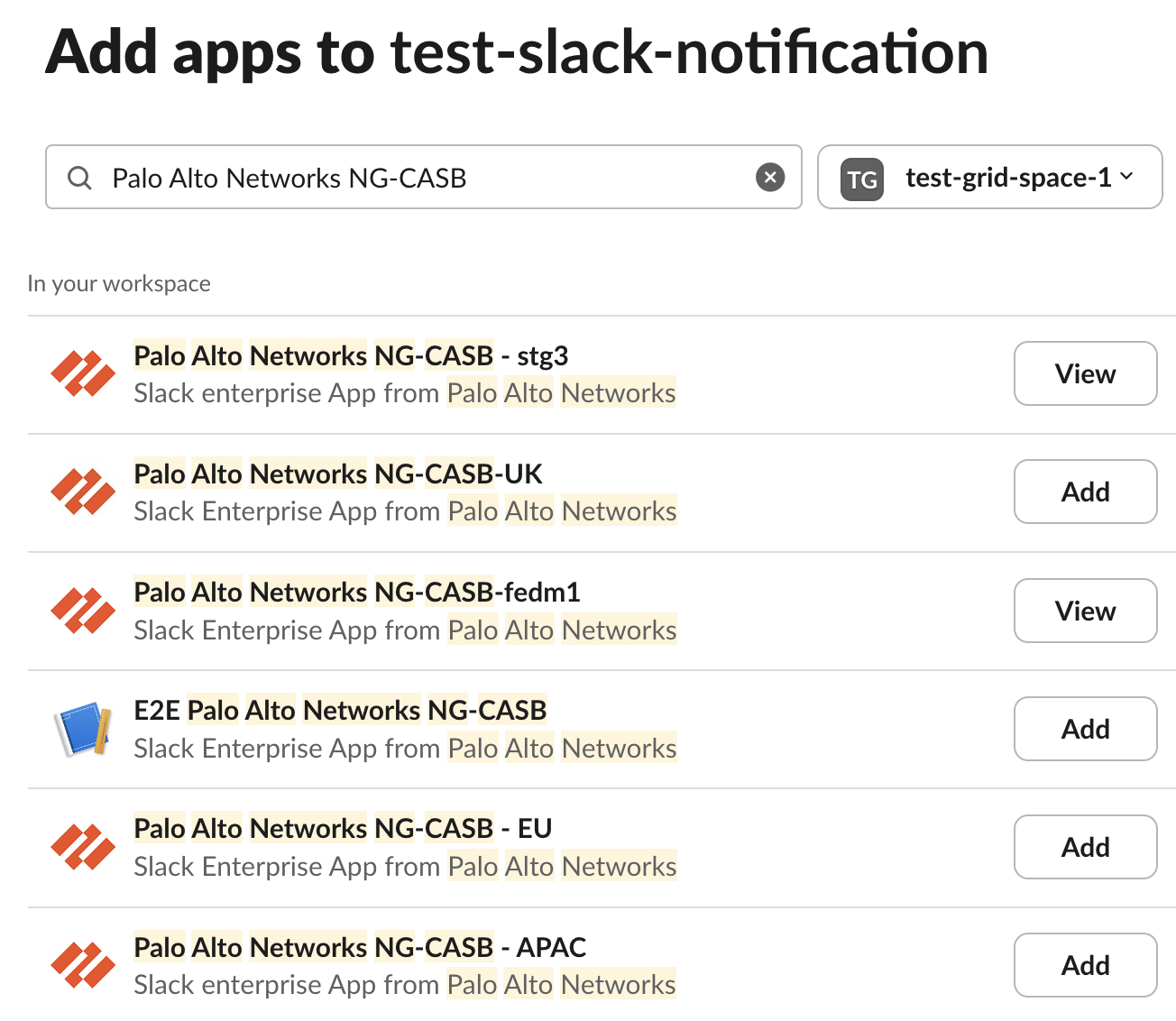
If the Validating Permissions check fails, ensure you have administrator permissions.If you are unable to configure Slack notifications, try the following:- Ensure you have added the Palo Alto app to your specific channel where you want
the notifications to be sent. To do this, go to <Your Slack Channel>IntegrationsAdd an App<App Name of Your Region>. Following are the app names for specific regions:
- VPC region: Palo Alto Networks NG-CASB
- India region: Palo Alto Networks NG-CASB - India
- Australia region: Palo Alto Networks NG-CASB - AU
- Japan region: Palo Alto Networks NG-CASB - JP
- UK region: Palo Alto Networks NG-CASB - UK
- EU region: Palo Alto Networks NG-CASB - EU
- APAC region: Palo Alto Networks NG-CASB - APAC
![]()
![]()
Handling ErrorsTo understand your error messages and ways to resolve them, see:The other most common issues related to onboarding a Slack Enterprise app are as follows:SymptomExplanationSolutionWhen you attempt to log in to your Slack administrator account during the onboarding process, an authorization error is returned: Something went wrong when authorizing Palo Alto Networks NG-CASB for Slack.You have a Slack workspace open in your browser for a workspace other than the workspace associated with the administrator account that you’re using to onboard the Slack Enterprise app or the administrator account isn’t an Organization Owner.Log out of all Slack workspaces and verify that the administrator account is an Organization Owner.If the issue persists, contact SaaS Security Technical Support.Start Scanning and Monitor Results
Before beginning to scan for risks, Configure Data Patterns to identify specific strings of text, characters, words, or patterns to make it possible to find all instances of text that match a data pattern you specifyWhen you add a new cloud app and enable scanning, Data Security automatically scans the cloud app against the default data patterns and displays the match occurrences. You can take action now to improve your scan results and identify risks.- To start scanning the new Slack Enterprise app for risks, go to Data SecurityApplicationsSlack EnterpriseView Settings...Start Scanning.Monitor the scan results.During the discovery phase, Data Security scans files and matches them against enabled default policy rules.Verify that your default policy rules are effective. If the results don’t capture all risks or you see false positives, proceed to the next step.(Optional) Modify your match criteria for existing policy rules.(Optional) Add new policy rules.Consider the business use of your app, then identify risks unique to your organization. As necessary, add new: