Configure Intelligent Security Using RADIUS for User Equipment to IP Address Correlation
Table of Contents
11.0 (EoL)
Expand all | Collapse all
End-of-Life (EoL)
Configure Intelligent Security Using RADIUS for User Equipment to IP Address Correlation
Learn how to use Intelligent Security to correlate IP addresses with User Equipment
using RADIUS for Security policy enforcement.
Information such as the Subscriber ID (IMSI or SUPI) and the Equipment ID (IMEI or
PEI) for User Equipment (UE) mobile devices are key identifiers for Security policy
enforcement in mobile networks such as 5G and 4G/LTE networks. Mapping the IMSI or
IMEI to subscriber or user IP addresses requires access to the signaling protocol
traffic exchanges over the 3GPP interfaces; however, in some deployments, the 3GPP
interfaces between network functions are not exposed.
Intelligent Security with RADIUS in 5G supports the following platforms:
- VM-Series
- CN-Series
- PA-3430 and PA-3440
- PA-5400 Series (excluding PA-5450)
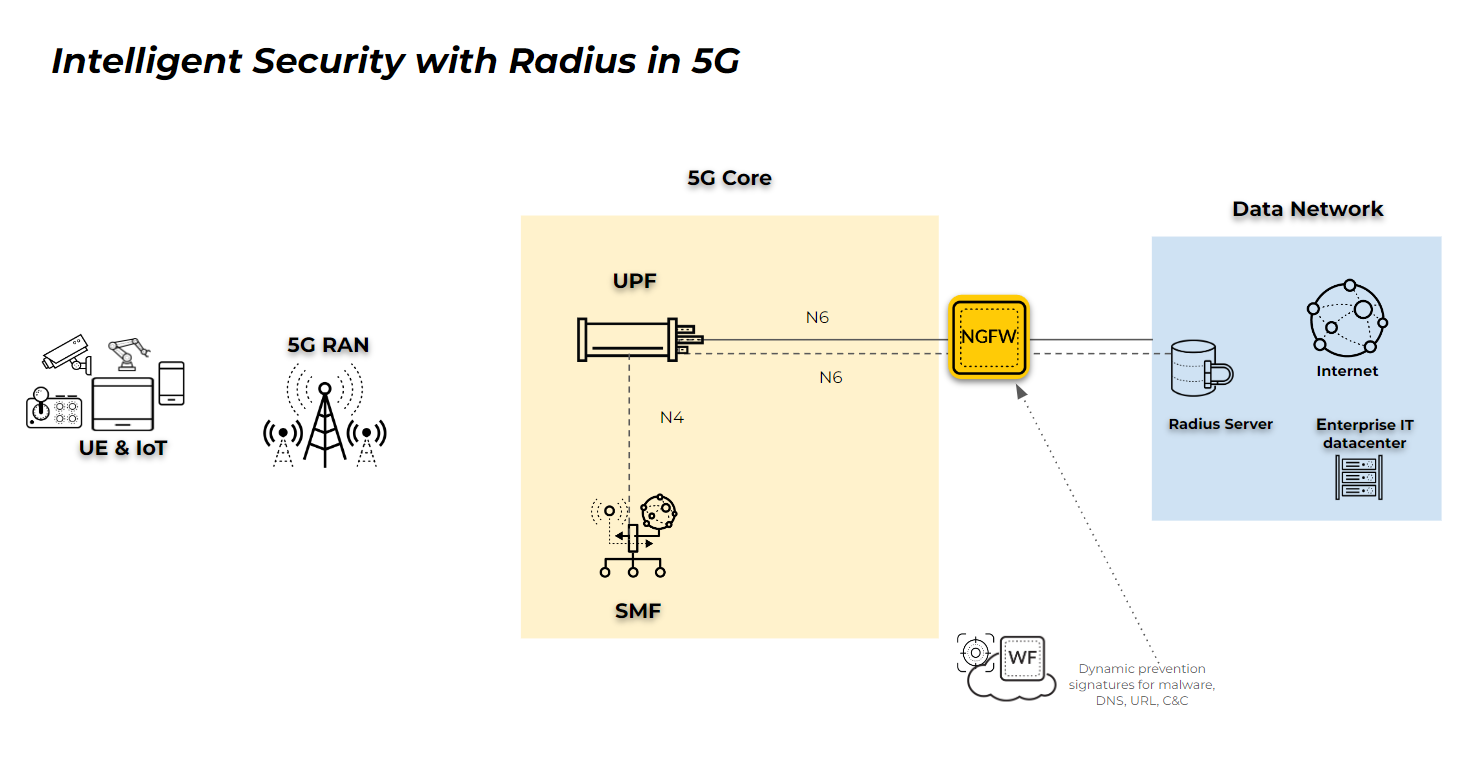
Intelligent Security with RADIUS in 5G allows deployment of the firewall on the
N6/SGi interface, which contains the RADIUS traffic for the management plane, and
Internet Protocol traffic without outer GTP-U headers for the dataplane. The
firewall inspects the RADIUS traffic to extract information for correlation with the
user plane. This provides subscriber and equipment-level visibility, as well as
consistent policy enforcement for vulnerabilities, malware, URLs, C2, and
applications.
If you enable UEIP Correlation, the following options are
not available in the same Mobile Network Protection Profile:
- GTP-C
- 5G-C
- Packet Forwarding Control Protocol (PFCP)
The following diagram represents a possible deployment for UE to IP address
correlation for an N6 deployment with RADIUS.
When the UE attempts to connect with the network, the SMF exchanges authentication,
authorization, and accounting messages with the DN-AAA server using RADIUS. The
accounting message provides a record of the network services that the authenticated
UE accesses. This message contains parameters, which include the user's ID and IPv4
or IPv6 address, that the application servers use to identify the user.
The firewall monitors the Accounting Start messages on UDP ports 1813 and 1646 and
Interim Updates to map the UE to the IP address and adds the mapping to the
correlation database on the firewall. The firewall also generates a log during IP
address allocation.
When the firewall receives the RADIUS session end message, it removes the mapping
from the correlation database on the firewall and creates a log.
Intelligent Security requires the following fields and Vendor-Specific Attributes
(VSAs) in the RADIUS messages:
- Framed-IP-Address(8): <IPv4-address>
- Framed-IPv6-Prefix(97): <IPv6-prefix>
- Vendor-Specific(26): VSA: t=3GPP-IMSI(1): <IMSI_value>
- Vendor-Specific(26): VSA: t=3GPP-IMEISV(20): <IMEI_value>
- Enable GTP Security.
- Log in to the firewall web interface.Select DeviceSetupManagementGeneral Settings then select GTP Security.Click OK.Commit the change.Select DeviceSetupOperations and Reboot Device.Create a Mobile Network Protection Profile.
- Select ObjectsSecurity ProfilesMobile Network Protection and Add a new profile.Give the profile a unique Name.Select Correlation and enable UEIP Correlation.Select the Mode you want to use.
- Loose—(Default) When the firewall detects traffic, it queries the source or destination address to find the correlated IMEI or IMSI information. If there are no results, the firewall forwards the traffic.
- Strict—Drops the traffic if the GTP-U query does not return any results.
Select RADIUS as the Source.Select the Source that you want the firewall to use to correlate the management plane and user plane information for subscriber-level and equipment-level Security policy enforcement. The firewall inspects traffic for the source type you select to process and extract 5G/4G identity information, such as Subscriber ID (SUPI and IMSI), Equipment ID (PEI and IMEI), and the IP address of the User Equipment (UE), to correlate with 5G/4G subscriber Internet Protocol traffic.![]() (Optional) Select whether you want to log UEIP correlation events when the firewall allocates an IP address to the UE (Log At Ueip Start), when the firewall releases the allocated IP address (Log At Ueip End), or both.The firewall logs the following GTP events during correlation that you can view by going to MonitorLogsGTP:
(Optional) Select whether you want to log UEIP correlation events when the firewall allocates an IP address to the UE (Log At Ueip Start), when the firewall releases the allocated IP address (Log At Ueip End), or both.The firewall logs the following GTP events during correlation that you can view by going to MonitorLogsGTP:- UEIP mapping start
- UEIP mapping end
The logs contain the following user information:- Subscriber Identity (including IMSI and SUPI)
- Equipment Identity (including IMEI and PEI)
- End User IP address allocated to UE
Create a Security policy to identify and allow RADIUS traffic between the SMF and the RADIUS server.There are two methods for policy creation based on the necessary level of security between the SMF and the RADIUS server. Select the appropriate method based on your security needs.- (Recommended) To allow all traffic between the SMF and RADIUS server
zone, as well as the UPF and Data Network zones:
- Select PoliciesSecurity and Add a unique Namefor the rule in the General tab.
- In the Source tab, Add the Source Zone as Any and the Source Address as Any.
- In the Destination tab, Add the Destination Zone as Any and the Destination Address as Any.
- In the Application tab, Add radius as the Application you want to allow.
- In the Service/URL Category tab, select the Serviceas Any.
- In the Actions tab, select the Action as Allow.
- Attach the Mobile Network Protection profile to the Security policy rule by selecting Profiles and selecting the profile as the Profile Type.
- Select Log at Session End if isn't already selected.
- (Alternate method) To allow RADIUS application traffic only between the
SMF and the RADIUS server:
- Select PoliciesSecurity and Add a unique Namefor the rule in the General tab.
- In the Source tab, Add the Source Zone and Source Address of the interface that the SMF uses to communicate with the RADIUS server.
- In the Destination tab, Add the Destination Zone and Destination Address for the interface that contains the IP address of the RADIUS server.
- In the Application tab, Add radius as the Application you want to allow.
- In the Service/URL Category tab, select the Serviceas Any.
- In the Actions tab, select the Action as Allow.
- Attach the Mobile Network Protection profile to the Security policy rule by selecting Profiles and selecting the profile as the Profile Type.
- Select Log at Session End if it isn't already selected.
(Alternate method only) Create a custom application and a Security policy that uses the custom application.Because the firewall applies this policy rule first, it processes the first packet of all user traffic and enables UEIP database querying, move this policy rule above any other policy rules in your Security policy for user traffic on the N6 interface. Any application-specific or IMSI/IMEI-based policy rules must occur after this policy rule. You only need to complete this step if you select the alternate method in the previous step.- Select ObjectsApplications and Add a unique Name for the application (for example, radius-ueip).
![]() Select PoliciesSecurity and Add a unique Name for the policy rule.In the Source tab, Add the zone that contains traffic to the UPF as the Source Zone and select Any as the Source Address. If you use an IP pool for the UE IP address, add the IP pool as the Source Address .Don't select anything in the Source Subscriber or Source Equipment tabs.In the Destination tab, Add the zone that contains traffic to the Packet Data Network as the Destination Zone and select Any as the Destination Address.In the Application tab, Add the Applicationyou created in step 4.1.In the Service/URL Category tab, select Any as the Service.In the Actions tab, select Allow as the Action.Attach the Mobile Network Protection profile to the Security policy rule by selecting Profiles and selecting the profile you created in step 3 as the Profile Type.Select Log at Session Endif it isn't already selected.Create Security policy rules for User Equipment (UE) traffic based on the criteria you want to use, such as IP address, application, URL category, IMSE, or IMEI.
Select PoliciesSecurity and Add a unique Name for the policy rule.In the Source tab, Add the zone that contains traffic to the UPF as the Source Zone and select Any as the Source Address. If you use an IP pool for the UE IP address, add the IP pool as the Source Address .Don't select anything in the Source Subscriber or Source Equipment tabs.In the Destination tab, Add the zone that contains traffic to the Packet Data Network as the Destination Zone and select Any as the Destination Address.In the Application tab, Add the Applicationyou created in step 4.1.In the Service/URL Category tab, select Any as the Service.In the Actions tab, select Allow as the Action.Attach the Mobile Network Protection profile to the Security policy rule by selecting Profiles and selecting the profile you created in step 3 as the Profile Type.Select Log at Session Endif it isn't already selected.Create Security policy rules for User Equipment (UE) traffic based on the criteria you want to use, such as IP address, application, URL category, IMSE, or IMEI.- Select PoliciesSecurity and Add a unique Name for the rule.In the Source tab, Add the Source Zone and Source Address.If you use an IP pool for the UE IP address, add the IP pool as the Source Address .In the Source tab, Add the Source Subscriber and if required, the Source Equipment.In the Destination tab, Add the Destination Zone and Destination Address the address of the servers in the corporate network or MEC site or use any for internet access.In the Application tab, Add the Application or applications you want to allow, such as dns, web-browsing, or ssl.In the Service/URL Category tab, select the type or types of Service you want to allow.In the Actions tab, select the Action you want to take for the selected traffic (Allow the traffic or Deny it).Select Log at Session End if it isn't already selected.Verify your configuration is correct.
- Verify the session traffic on the firewall.-------------------------------------------------------------------------------- ID Application State Type Flag Src[Sport]/Zone/Proto (translated IP[Port]) Vsys Dst[Dport]/Zone (translated IP[Port]) -------------------------------------------------------------------------------- 9777 radius ACTIVE FLOW 15.15.15.20[2000]/TapZone/17 (15.15.15.20[2000]) vsys1 16.16.16.10[1813]/TapZone (16.16.16.10[1813]) 9776 radius ACTIVE FLOW 15.15.15.20[2000]/TapZone/17 (15.15.15.20[2000]) vsys1 16.16.16.10[1812]/TapZone (16.16.16.10[1812])Verify the mappings on the firewall display radius as the source (src).admin@PA-VM> show gtp ueip all Total entry = 1, Displayed entry = 1 Showing max 512 entries start-at 0: [0 @ Bucket 2094] UEIP 15.15.15.10: IMSI 123456789012345, IMEI 987654321987650, SST 0, SD 0, Last_update 522115, src_sess_id 9777, src radius, TTL 86374 seconds, Pending Delete 0 Next show should start-at 0View the logs (MonitorLogsGTP) and verify that the GTP Event Type displays UEIP mapping start and UEIP mapping end.
![]() Verify the Traffic logs (MonitorLogsTraffic) display the IMSI or IMEI in the Subscriber Identity column for the UE traffic.
Verify the Traffic logs (MonitorLogsTraffic) display the IMSI or IMEI in the Subscriber Identity column for the UE traffic.![]() Use the Global Counters to verify the configuration.session_gtpu_fwd_ueip_entry_found 29 0 info session pktproc GTPu packets with matching UEIP entry session_gtpu_fwd_ueip_entry_not_found 2 0 drop session pktproc GTPu packets without matching UEIP entry forwarded flow_radius_req_start_recv 1 0 info flow pktproc radius request start packet received flow_radius_req_update_recv 2 0 info flow pktproc radius request update packet received flow_radius_req_stop_recv 1 0 info flow pktproc radius request stop packet received flow_radius_adding_ueip 1 0 info flow pktproc radius packet adding a ueip entry flow_radius_deleting_ueip 1 0 info flow pktproc radius packet deleting a ueip entry flow_radius_updating_ueip 2 0 info flow pktproc radius packet updating a ueip entry gtp_ueip_entry_insert 1 0 info gtp pktproc UEIP entry insert gtp_ueip_entry_modify 2 0 info gtp pktproc UEIP entry modify gtp_ueip_entry_delete 1 0 info gtp pktproc UEIP entry delete
Use the Global Counters to verify the configuration.session_gtpu_fwd_ueip_entry_found 29 0 info session pktproc GTPu packets with matching UEIP entry session_gtpu_fwd_ueip_entry_not_found 2 0 drop session pktproc GTPu packets without matching UEIP entry forwarded flow_radius_req_start_recv 1 0 info flow pktproc radius request start packet received flow_radius_req_update_recv 2 0 info flow pktproc radius request update packet received flow_radius_req_stop_recv 1 0 info flow pktproc radius request stop packet received flow_radius_adding_ueip 1 0 info flow pktproc radius packet adding a ueip entry flow_radius_deleting_ueip 1 0 info flow pktproc radius packet deleting a ueip entry flow_radius_updating_ueip 2 0 info flow pktproc radius packet updating a ueip entry gtp_ueip_entry_insert 1 0 info gtp pktproc UEIP entry insert gtp_ueip_entry_modify 2 0 info gtp pktproc UEIP entry modify gtp_ueip_entry_delete 1 0 info gtp pktproc UEIP entry delete




