Enterprise DLP
Strata Cloud Manager
Table of Contents
Strata Cloud Manager
Configure role-based access for Enterprise Data Loss Prevention (E-DLP) on Strata Cloud Manager.
Strata Cloud Manager supports the following roles to grant access privileges for the
Enterprise DLP app specifically.
|
Predefined Enterprise DLP Role
|
Privileges
|
|---|---|
|
DLP Incident Manager
|
Read and Write Access — Alerts, Incidents, health and
telemetry, reports, and Audit Logs
Read Only Access—Data patterns, profiles, DLP Rules, EDM
data sets, OCR setting, and all DLP settings
|
|
DLP Policy Manager
|
Read and Write Access — Data patterns, profiles, DLP
Rules, EDM data sets, OCR setting, health and telemetry, audit
logs, alerts, and all DLP settings
No Access— Incidents and reports
|
|
Multitenant Superuser
|
Full read and write privileges to Enterprise DLP for all
tenants in the particular multitenant hierarchy where the role
is assigned
|
|
Superuser
|
Full read and write privileges for Enterprise DLP
|
|
View Only Administrator
|
Read-only privileges for Enterprise DLP
|
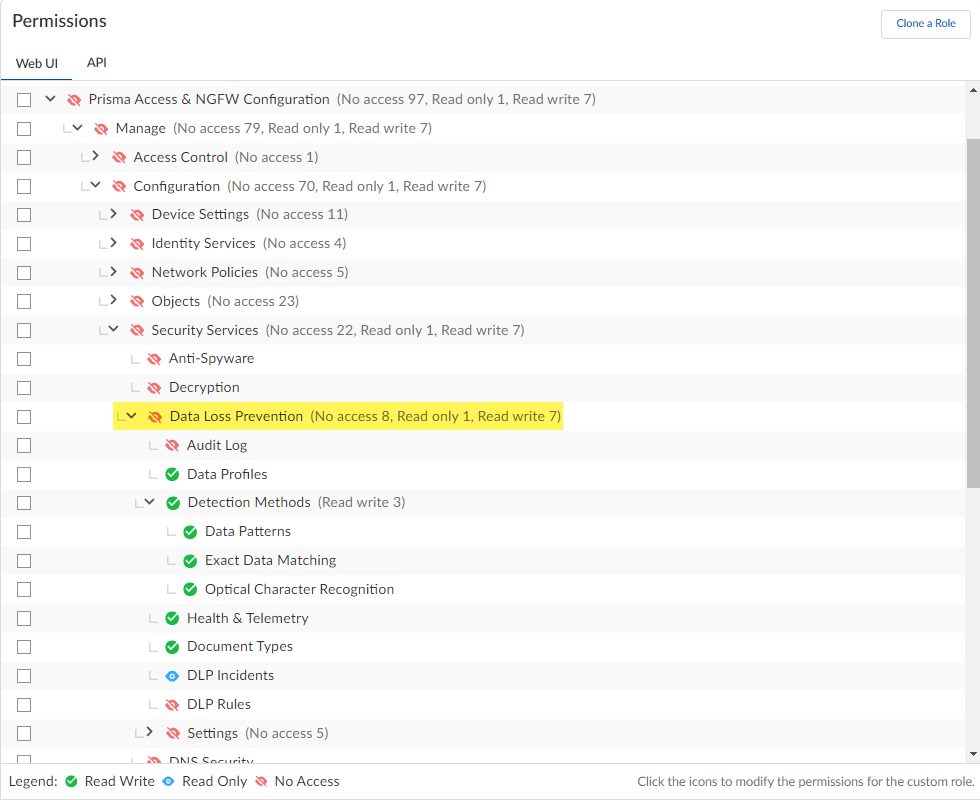
- Use one of the various ways to access Identity & Access.Add Access to your tenant where Enterprise DLP is active.This step is required only if the user for which you’re granting Enterprise DLP access isn’t already registered with the Palo Alto Networks Customer Support Portal (CSP).Select Prisma Access & NGFWManageSecurity ServicesData Loss Prevention to add a custom role.You can use custom roles allow to define which permissions are enforced for your users and allow more granular access control to Enterprise DLP than predefined roles.The access permissions applied to the Data Loss Prevention parent node determines the lowest access privilege you can assign to any of its child node. For example, if you want provide No Access and Read Only to some areas of Enterprise DLP, you must first assign No Access to the Enterprise DLP application.Below is an example of a custom Enterprise DLP role. The custom role is configured with no access privileges to Audit Logs or any of the Enterprise DLP settings. However, read-only access is configured for the Health & Telemetry and DLP Incidents, and full read and write privileges are configured for Data Profiles, all Detection Methods, Document Types, and DLP Rules.
![]() Assign role-based access for Enterprise DLP.You don’t need to configuring a tenant role for a user if access to only Enterprise DLP is required.
Assign role-based access for Enterprise DLP.You don’t need to configuring a tenant role for a user if access to only Enterprise DLP is required.- Select User and for the Identity Address, enter the email address for which you granted access in the previous step.For Apps & Services, select Enterprise DLP.Select a predefined or custom Enterprise DLP Role.Submit.Continue based on your Enterprise DLP access privileges.
- Enable Enterprise DLP on Strata Cloud Manager
- Create Data Patterns
- Create Data Profiles