5G Equipment ID and Subscriber ID Security
Table of Contents
11.0 (EoL)
Expand all | Collapse all
End-of-Life (EoL)
5G Equipment ID and Subscriber ID Security
Information about 5G equipment ID and subscriber ID security.
5G is the next generation mobile technology. New use cases, services, and applications in 5G are
in the areas of enhanced Mobile Broadband (eMBB), Ultra-Reliable and Low Latency
Communications (URLLC), and massive IoT (MIoT). High value assets and critical processes
run on 5G networks. Early adopters of 5G technology are enterprises focused on smart
manufacturing, transport and logistics, critical infrastructure, oil, gas, and mining.
5G will accelerate the evolution of IoT as more devices become connected.
The attack surface increases in 5G. One major concern is a greater
number of devices connected to 5G networks, which increases the
number of opportunities for attackers to exploit the vulnerability
of a device. For example, the increased number of devices connected
to 5G networks makes it easier to launch a DDoS attack. Most of
these devices likely lack robust security and software update mechanisms. Compromised
devices can also impact service of the 5G network.
Security is one of the top concerns of organizations planning
to adopt 5G. Network security capabilities are required, with the
ability to identify and prevent the attack with the granularity
of device or equipment identifier and subscriber or user identifier.
Detection of these threats in 5G mobile networks requires identification
of compromised equipment, devices, subscribers, and users. Prevention
requires the ability to apply network security based on equipment
ID, which is a Permanent Equipment Identifier (PEI) including International
Mobile Equipment Identity (IMEI), and subscriber ID, which is Subscriber
Permanent Identifier (SUPI) including International Mobile Subscriber
Identity (IMSI).
5G network functions communicate with each other using the HTTP/2
protocol; HTTP/2 messages carry various mobile network identifiers,
such as PEI. Traffic from IoT devices is carried in GTP-U tunnels
in the 5G network. The firewall is positioned in N3 and N11 interfaces
to inspect both HTTP/2 and GTP-U traffic, and it correlates the
mobile network identifier information with the IP traffic inside
the GTP-U tunnels in a 5G network.

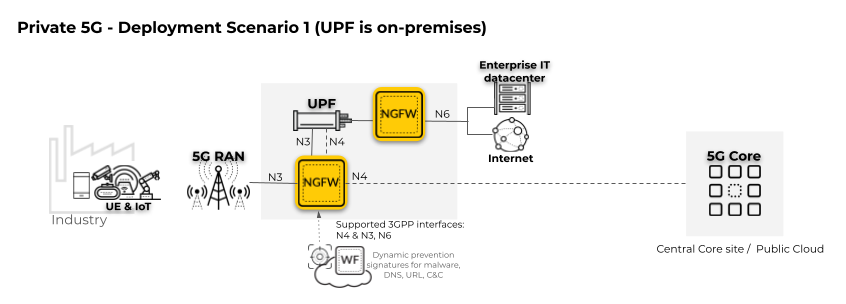
In the following private 5G network deployment scenario, only
the User Plane Function (UPF) is located on-premises. The 5G Core
is located remotely in a central core site or public cloud. To enforce
security policy for user and control traffic, the firewall must
be positioned on the 5G interfaces, including the User Plane (N3)
and Control Plane (N4).
The
second firewall in the diagram is positioned on the perimeter (the
N6 interface connected to the internet and the enterprise IT datacenter).
For complete subscriber-level
and equipment-level visibility and security policy control for network
traffic threats, enable GTP Security.
In the following private 5G network deployment scenario, the
5G Core, including the User Plane Function (UPF), is located on-premises.
The 5G Core includes network functions (NFs) such as Session Management
(SMF) and Access and Mobility Management Function (AMF), as well
as others. To enforce security policy for user and control traffic,
the firewall must be positioned on the 5G interfaces, including
the User Plane (N3) and the Control Plane (N4).
The
second firewall in the diagram is positioned on the perimeter (the
N6 interface connected to the internet and the enterprise IT datacenter).
For complete
subscriber-level and equipment-level visibility and security policy
control for network traffic threats, enable GTP Security. Apply security
policy to the Control Plane (N2) between the 5G RAN and the 5G Core
for signaling protection by enabling SCTP Security.

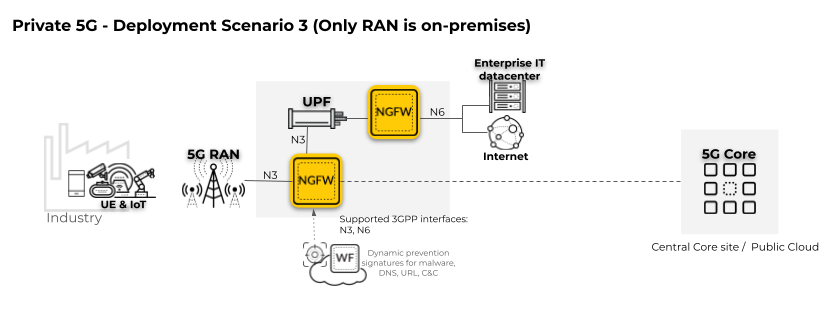
In the following private 5G network deployment scenario, only
the Radio Access Network (RAN) is located on-premises.
The
firewall must be positioned on the 5G interface for the User Plane
(N3).
To apply security policy to user traffic,
enable Tunnel Content Inspection.
PAN-OS supports the following HTTP/2 control messages on an N11
interface. From these messages the firewall extracts the identifiers
(such as Equipment ID, Subscriber ID, and Network Slice SST) in
order to correlate traffic to a specific user at the N3 interface
and to match the identifiers to Security policy rules.
- Nsmf_PDUSession_CreateSMContext Request
- Nsmf_PDUSession_CreateSMContext Response
- Nsmf_PDUSession_UpdateSMContext Request
- Nsmf_PDUSession_UpdateSMContext Response
- Nsmf_PDUSession_ReleaseSMContext Request
- Nsmf_PDUSession_ReleaseSMContext Response
- Namf_Communication_N1N2MessageTransfer Request
- Namf_Communication_N1N2MessageTransfer Response
You can apply network security based on the equipment identity
of any device or equipment or the subscriber identity of any subscriber
or user that is trying to access your 5G network.
You can investigate a security event related to a piece of equipment
in a 5G network when you have the PEI including IMEI, or a security
event related to a subscriber when you have the SUPI including IMSI.
You can look at the traffic, threat, URL filtering and WildFire® logs
and reports.
You can apply the following per equipment ID or subscriber ID:
application control, Antivirus, Anti-Spyware, URL filtering, intrusion
prevention, and advanced threat prevention with WildFire based on
an IMEI, IMSI, or a group of IMEIs or IMSIs.
PAN-OS® supports HTTP/2 control
messages on an N11 interface.
5G equipment ID and subscriber ID security support an additional
Radio Access Technology (RAT) not supported in 4G, and that is New
Radio (NR).
When deciding which firewall model to purchase, consider the
total number of 3G, 4G, and 5G network identifiers (Subscriber IDs
and Equipment IDs) you need to include as EDL entries or static
entries. The following table provides capacities of EDL entries
and static entries for each firewall model:
Firewall Model | Total 3G, 4G, and 5G Network Identifiers
Supported by Dynamic EDL | Total 3G, 4G, and 5G Network Identifiers
Supported by Static Entries |
|---|---|---|
PA-7080 | 10,000,000 | 100,000 |
PA-7050 | 6,000,000 | 60,000 |
PA-5440 | 1,200,000 | 100,000 |
PA-5430 | 720,000 | 100,000 |
PA-5420 | 500,000 | 100,000 |
PA-5410 | 360,000 | 60,000 |
PA-5280 | 2,000,000 | 20,000 |
PA-5260 | 1,000,000 | 10,000 |
PA-5250 | 250,000 | 5,000 |
PA-5220 | 125,000 | 5,000 |
|
PA-3430
|
250,000
|
50,000
|
PA-3440 | 250,000 | 50,000 |
VM-700 | 300,000 | 5,000 |
VM-500 | 75,000 | 1,000 |
VM-300 | 20,000 | 500 |
VM-100 | 2,000 | 200 |
