CIoT Security
Table of Contents
11.0 (EoL)
Expand all | Collapse all
End-of-Life (EoL)
CIoT Security
GTP deployments on a Palo Alto Networks firewall include
cellular IoT security.
Cellular internet of things (CIoT) security
enables you to protect your mobile network and CIoT traffic from
attacks and to get visibility into CIoT communications in your network.
If you are a mobile network operator (MNO) or a mobile virtual network
operator (MVNO), for example a utility company that focuses on oil, gas,
or energy operating as an MVNO, you can use CIoT security to secure
CIoT traffic. The firewall supports CIoT technologies (S11-U tunnels,
Narrowband IoT [NB-IoT], and LTE-M). The firewall also supports
logging of Remote UE identifiers using Proximity Service (ProSe)
with device-to-device (D2D) communications over air interfaces in
your network. The logging is especially helpful in public safety
use cases.
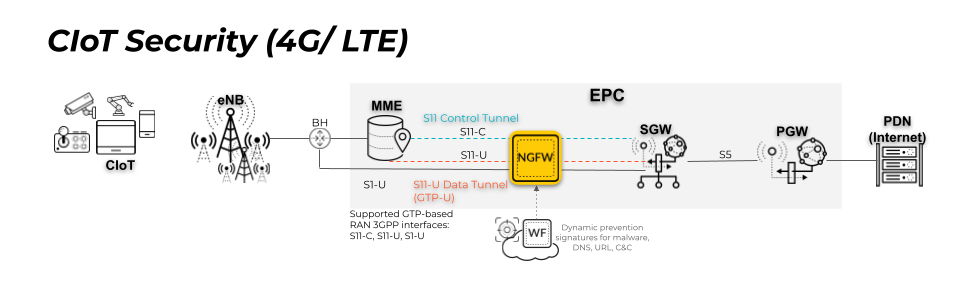
| Acronyms in the Topology Figure | |
|---|---|
BH | Backhaul |
MME | Mobile Management Entity |
PGW | Packet Gateway |
SGW | Serving Gateway |
CIoT security includes:
- Support for CIoT Evolved Packet System (EPS) optimization:
- GTP Stateful Inspection of S11 and S11-U tunnels
- GTP-U Content Inspection of S11-U tunnels (inspect the content of inner IP sessions of S11 GTP-U tunnels)
- Filtering traffic from IoT devices that connect a mobile network using EUTRAN-NB-IoT (Radio Access Network for NB-IoT). For example, allowing only devices that use NB-IoT to access the network. LTE-M filtering is also supported.
- Displaying and reporting on D2D (device-to-device) communication using Remote User ID (IMSI) and Remote User IP when you monitor GTP or Unified log messages, when you generate custom reports from the GTP Summary or GTP Detailed database, and when you forward GTP logs.
The CIoT security deployment illustrates the S11-U data tunnel,
which carries encapsulated data messages using GTP-U. If mobile-originated
or mobile-terminated data is transported in control plane CIoT EPS
Optimization with PGW connectivity, the MME and SGW use an S11-U
tunnel. Information in the GTP payload initiates the establishment
of the S11-U tunnel; the Create Session Request and Response exchange
between the MME and SGW establishes the S11-U tunnel without needing
a Modify Bearer Request and Response exchange to transfer downlink
or uplink user data.
For use cases that involve less data (such as communication to
or from an IoT device because IoT devices typically send data infrequently),
you can use an S11-U data tunnel to reduce the number of signaling
messages exchanged on the network. To inspect this data traffic,
position a firewall between the MME and the SGW.
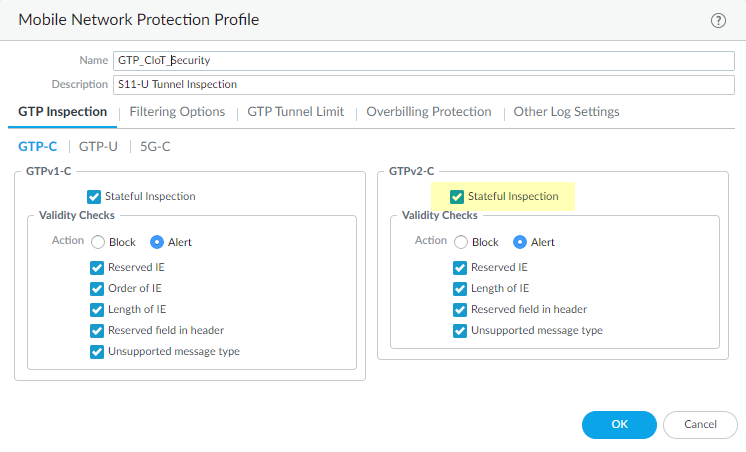
To protect your mobile network and CIoT traffic that use 3rd
Generation Partnership Project (3GPP) technologies, follow the procedure
to configure GTPv2-C
Stateful Inspection to statefully inspect the S11-U tunnels.
Create a Mobile Network Protection Profile and enable GTP-U Content
Inspection to inspect the content of the GTP-U traffic
inside the S11-U tunnels. Attach the profile to a Security policy
rule (that identifies the application, such as gtpv2-c and gtp-u)
and apply the rule to zones for network elements that use GTP, such
as between an MME and SGW.
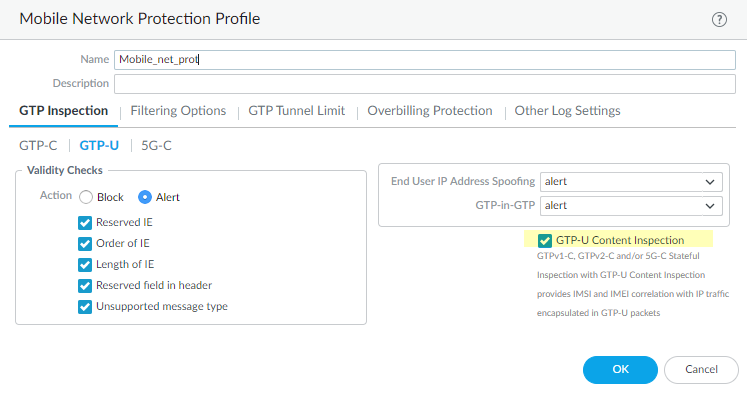
By enabling GTP-U Content Inspection,
you can secure CIoT traffic by creating Security policy rules and
applying the following security capabilities on IP traffic inside
a GTP-U tunnel:
- App-ID
- Antivirus
- Anti-Spyware
- Vulnerability Protection
- URL Filtering
- WildFire® Analysis
- Data Filtering
The source and destination zones of GTP-U inner IP sessions
are the same zones as those for GTP-U outer sessions.
The firewall does not support Decryption of IP traffic
inside GTP-U tunnels.
If you use Narrowband IoT (NB-IoT) as Radio Access Technology
(RAT), your GTP Protection profile can filter GTP traffic generated
for IoT devices and, thus, safely allow only EUTRAN-NB-IoT traffic
for trusted services.
If you are using NB-IoT, create a Mobile Network Protection Profile with RAT filtering
to allow only NB-IoT traffic (allow EUTRAN-NB-IoT)
from the trusted services and set the remaining RAT filters to block.
