Device Security
Activate Device Security
Table of Contents
Expand All
|
Collapse All
Device Security Docs
Activate Device Security
Learn about Device Security activation.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
Device Security works with
next-generation firewalls to dynamically discover and maintain a real-time inventory
of the IoT devices on your network. If you're trying to activate Device Security
with the add-on Enterprise License Agreement (ELA), see
activate an add-on enterprise license
agreement instead.
Follow the activation workflow to activate Device Security subscriptions for
your firewalls. Through the activation process, you can optionally activate a
Strata Logging Service instance to store data.
When activating a new Device Security license, or when adding an existing
Device Security license to a new tenant, after June 30, 2025, you can only
access Device Security through Strata Cloud Manager. If you don't have an
existing Strata Cloud Manager instance, the Device Security activation
process automatically creates a free Strata Cloud Manager Essential instance
in the same TSG as Device Security.
For existing customers who activated your Device Security license before
June 30, 2025, you will continue to have access to your Device Security
portal through your Device Security app subdomain in addition to
Device Security in Strata Cloud Manager. You can access Device Security
in Strata Cloud Manager by navigating to App SwitcherStrata Cloud Manager in the Device Security portal, or by directly accessing
https://stratacloudmanager.paloaltonetworks.com/devicesecurity.
Because Device Security requires network traffic data for analysis, you must enable
firewalls to forward logs with that data to a cloud logging service that
Device Security can access. Depending on the
subscription license type that you have,
you can activate or associate Strata Logging Service when activating
Device Security.
As part of the Device Security subscription, you can integrate
Device Security with third-party services. This allows
Device Security to exchange information about devices, security alerts, and
device vulnerabilities with third-party products that provide services such as asset
management, network access control (NAC), network management, vulnerability
scanning, and security information and event management (SIEM). Device Security
can also enhance the information it has by retrieving data about devices and
vulnerabilities from third-party products.
Device Security supports
third-party integrations through
Cortex XSOAR. If you want to take advantage of third-party integrations,
you can link an existing full-featured Cortex XSOAR or else activate a
complimentary, limited co-hosted Cortex XSOAR. You can link or activate
Cortex XSOAR after you complete Device Security activation and
onboarding.
Select Activate Subscription in your email. Keep the
Device Security activation email you received from Palo Alto Networks. It not
only contains confidential activation-related data but if you still have unused
Device Security licenses after completing the onboarding process, you can click
the Activate button in the email again to repeat the process
and activate more firewalls later.
(Enterprise License Agreement) When you have an
Enterprise License Agreement (ELA), begin the activation process by entering the
auth code that Palo Alto Networks sends you in your
Customer Support Portal account. For complete step-by-step instructions, see
Activate an Add-on Enterprise License Agreement
through Common Services.
Activation for Strata Cloud Manager
Learn how to activate your Device Security application for the first time when using
Strata Cloud Manager.
If you purchased an Enterprise, OT, or Medical Device Security
subscription license, follow these steps for first time Device Security
activation with Strata Cloud Manager.
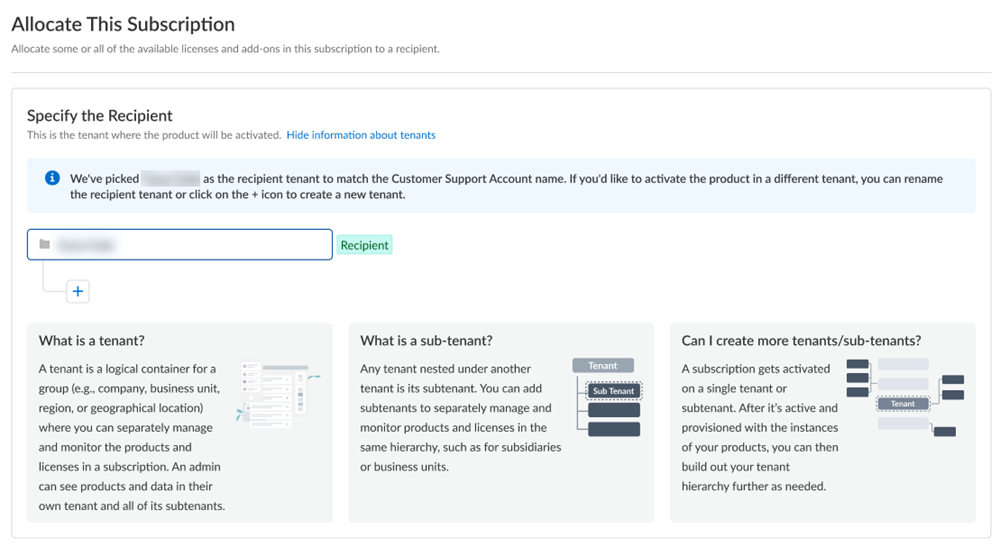
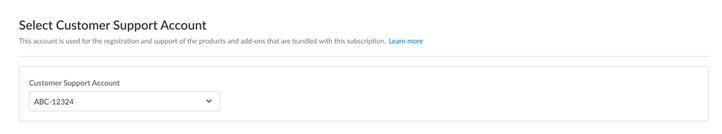
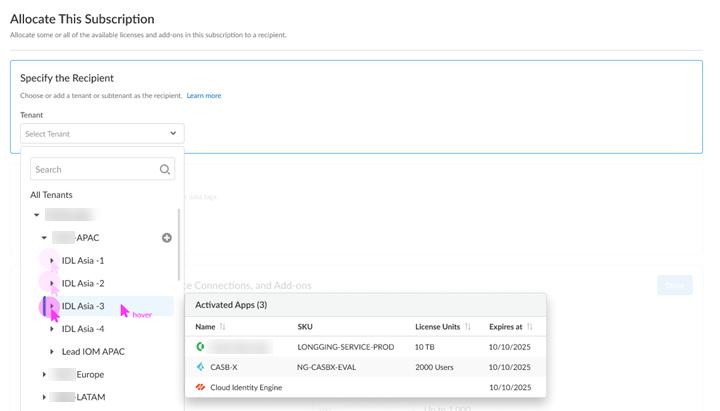
- Choose the Customer Support Account that you want to use.If you only have one Customer Support Portal account associated with your username, the Customer Support Account is prepopulated.Allocate the product to the Recipient of your choice.Multiple Customer Support Portal accounts You can allocate your entire license to one recipient or you can share it with multiple recipients in a tenant hierarchy. What is a tenant?If you have an existing Strata Cloud Manager Essential or Pro license and want to use that Strata Cloud Manager instance with Device Security, select the same TSG as your Strata Cloud Manager instance.If you don't have an existing Strata Cloud Manager instance, then the Device Security activation process automatically creates a Strata Cloud Manager Essential instance in the same TSG for you.
- If you need just one tenant, use or rename the tenant provided. The name provided matches your Customer Support Portal account for convenience.
![]() (Optional) This step applies if you're a managed security service provider (MSSP), a distributed enterprise customer, or need multiple tenants. After you create the first tenant, you can Allocate to subtenant and use or rename the tenant provided.
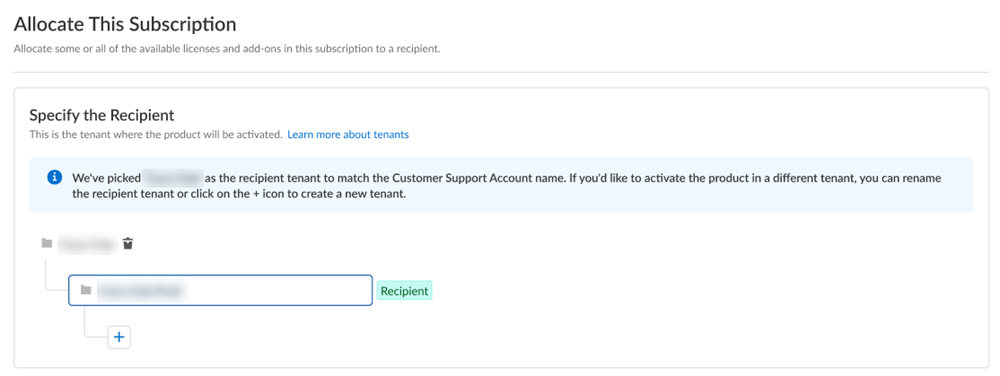
(Optional) This step applies if you're a managed security service provider (MSSP), a distributed enterprise customer, or need multiple tenants. After you create the first tenant, you can Allocate to subtenant and use or rename the tenant provided.![]() A subscription gets allocated on a tenant or a subtenant. This step is for choosing a tenant where you want to allocate a license, not for building a complete tenant hierarchy. You can create only a tenant and subtenant here, and you can choose to allocate a license to that subtenant.After activation, you can build out your tenant hierarchy as needed through tenant management. You can create your tenant hierarchy to reflect your existing organizational structure. You can also consider identity and access inheritance when creating the hierarchy, in addition to tenant hierarchy limits.Select Done.Choose the data ingestion Region, which is the region where Strata Logging Service is receiving data from firewalls.Strata Logging Service
A subscription gets allocated on a tenant or a subtenant. This step is for choosing a tenant where you want to allocate a license, not for building a complete tenant hierarchy. You can create only a tenant and subtenant here, and you can choose to allocate a license to that subtenant.After activation, you can build out your tenant hierarchy as needed through tenant management. You can create your tenant hierarchy to reflect your existing organizational structure. You can also consider identity and access inheritance when creating the hierarchy, in addition to tenant hierarchy limits.Select Done.Choose the data ingestion Region, which is the region where Strata Logging Service is receiving data from firewalls.Strata Logging Service- If you're using Device Security that Doesn't Require Data Lake, this sends data logs to a cloud logging service that streams them directly to Device Security without storing them in a data lake.
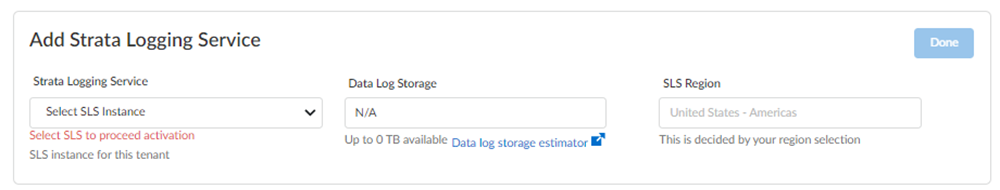
- If you're using Device Security that Does Require Data Lake, add Strata Logging Service.
![]()
- Select a Strata Logging Service instance.
- Enter the amount of data log storage.
- The region is grayed out, but is autopopulated with the same region that you used for Strata Logging Service.
Agree to the terms and conditions, and Activate.The activation process auto creates a single default tenant behind the scenes, and the product is activated in the tenant.This tenant, and any others created by this Customer Support Portal account, will have the Superuser role.Go to the Common ServicesDevice Associations tab to add firewalls to the tenant, associate them with the Device Security application, and then apply the Device Security subscription to them: Device Associations.Get started with Device Security.Optional Manage your product.Optional Manage identity and access.First time Device Security Activation - One Customer Support Portal Account
Learn how to activate your Device Security application for the first time if you have only one Customer Support Portal account.If you have only one Customer Support Portal account, follow these steps for first time Device Security activation.- Because you have only one Customer Support Portal account associated with your username, the Customer Support Account is prepopulated.Allocate the product to the Recipient of your choice.The name provided matches your Customer Support Portal account for convenience. You can use the name provided or change it.Choose the data ingestion Region, which is the region where the cloud logging service is receiving data from firewalls.Strata Logging Service
- If you are using Device Security that doesn't require Strata Logging Service, this sends data logs to a cloud logging service that streams them directly to Device Security without storing them in a data lake. Skip to the App Subdomain step.
- If you are using Device Security that does require Strata Logging Service, add
Strata Logging Service.
![]()
- Select a Strata Logging Service instance.
- Enter the amount of data log storage.
- The region is grayed out, but is autopopulated with the same region that you used for Strata Logging Service.
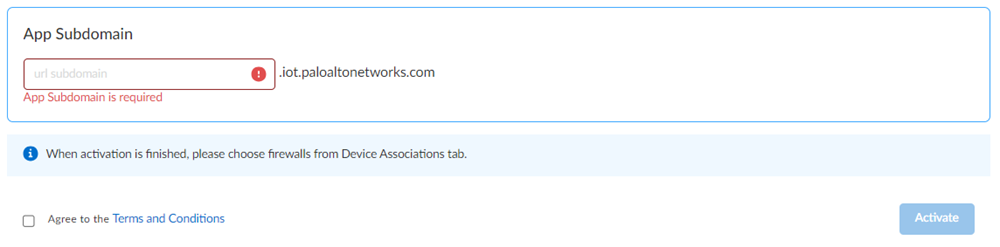
Enter an App Subdomain.![]() Use a unique subdomain to complete the <subdomain>.iot.paloaltonetworks.com URL for your Device Security application. This will be the URL where you log in to the Device Security portal.Agree to the terms and conditions, and Activate.A single default tenant is autocreated behind the scenes, and the product is activated in the tenant.This tenant, and any others created by this Customer Support Portal account, will have the Superuser role.Go to the Common ServicesDevice Associations tab to add firewalls to the tenant, associate them with the Device Security application, and then apply the Device Security subscription to them: Device Associations.Get started with Device Security.Optional Manage your product.Optional Manage identity and access.
Use a unique subdomain to complete the <subdomain>.iot.paloaltonetworks.com URL for your Device Security application. This will be the URL where you log in to the Device Security portal.Agree to the terms and conditions, and Activate.A single default tenant is autocreated behind the scenes, and the product is activated in the tenant.This tenant, and any others created by this Customer Support Portal account, will have the Superuser role.Go to the Common ServicesDevice Associations tab to add firewalls to the tenant, associate them with the Device Security application, and then apply the Device Security subscription to them: Device Associations.Get started with Device Security.Optional Manage your product.Optional Manage identity and access.First time Device Security Activation
Learn how to activate your Device Security application for the first time.If you purchased an Enterprise, OT, or Medical Device Security subscription license, follow these steps for first time Device Security activation.- Choose the Customer Support Account that you want to use.If you only have one Customer Support Portal account associated with your username, the Customer Support Account is prepopulated.Allocate the product to the Recipient of your choice.Multiple CSP accounts You can allocate your entire license to one recipient or you can share it with multiple recipients in a tenant hierarchy. What is a tenant?
- If you need just one tenant, use or rename the tenant provided. The name provided matches your Customer Support Portal account for convenience.
![]() (Optional) This step applies if you are a managed security service provider (MSSP), a distributed enterprise customer, or need multiple tenants. After you create the first tenant, you can Allocate to subtenant and use or rename the tenant provided.
(Optional) This step applies if you are a managed security service provider (MSSP), a distributed enterprise customer, or need multiple tenants. After you create the first tenant, you can Allocate to subtenant and use or rename the tenant provided.![]() A subscription gets allocated on a tenant or a sub-tenant. This step is for choosing a tenant where you want to allocate a license, not for building a complete tenant hierarchy. You can create only a tenant and subtenant here, and you can choose to allocate a license to that subtenant.After activation, you can build out your tenant hierarchy as needed through tenant management. You can create your tenant hierarchy to reflect your existing organizational structure. You can also consider identity and access inheritance when creating the hierarchy, in addition to tenant hierarchy limits.Select Done.Choose the data ingestion Region, which is the region where the cloud logging service is receiving data from firewalls.Strata Logging Service
A subscription gets allocated on a tenant or a sub-tenant. This step is for choosing a tenant where you want to allocate a license, not for building a complete tenant hierarchy. You can create only a tenant and subtenant here, and you can choose to allocate a license to that subtenant.After activation, you can build out your tenant hierarchy as needed through tenant management. You can create your tenant hierarchy to reflect your existing organizational structure. You can also consider identity and access inheritance when creating the hierarchy, in addition to tenant hierarchy limits.Select Done.Choose the data ingestion Region, which is the region where the cloud logging service is receiving data from firewalls.Strata Logging Service- If you are using Device Security that doesn't require Strata Logging Service, this sends data logs to a cloud logging service that streams them directly to Device Security without storing them in a data lake. Skip to the App Subdomain step.
-
If you are using Device Security that does require Strata Logging Service, add
Strata Logging Service.
![]()
- Select a Strata Logging Service instance.
- Enter the amount of data log storage.
- The region is grayed out, but is autopopulated with the same region that you used for Strata Logging Service.
Enter an App Subdomain.![]() Use a unique subdomain to complete the <subdomain>.iot.paloaltonetworks.com URL for your Device Security application. This will be the URL where you log in to the Device Security portal.Agree to the terms and conditions, and Activate.A single default tenant is autocreated behind the scenes, and the product is activated in the tenant.This tenant, and any others created by this Customer Support Portal account, will have the Superuser role.Go to the Common ServicesDevice Associations tab to add firewalls to the tenant, associate them with the Device Security application, and then apply the Device Security subscription to them: Device Associations.Get started with Device Security.Optional Manage your product.Optional Manage identity and access.
Use a unique subdomain to complete the <subdomain>.iot.paloaltonetworks.com URL for your Device Security application. This will be the URL where you log in to the Device Security portal.Agree to the terms and conditions, and Activate.A single default tenant is autocreated behind the scenes, and the product is activated in the tenant.This tenant, and any others created by this Customer Support Portal account, will have the Superuser role.Go to the Common ServicesDevice Associations tab to add firewalls to the tenant, associate them with the Device Security application, and then apply the Device Security subscription to them: Device Associations.Get started with Device Security.Optional Manage your product.Optional Manage identity and access.Return Visit Device Security Activation
Learn how to activate your Device Security for repeat visits.Follow these steps if you have already completed first time activation, you have already created your tenant hierarchy through Identity & AccessTenants or tenant management, and you are returning to activate another product in your existing hierarchy.- Choose the Customer Support Account number that you want to use to activate.
![]() Allocate the subscription to the Recipient tenant of your choice.You can hover over each tenant to see which apps you already activated.
Allocate the subscription to the Recipient tenant of your choice.You can hover over each tenant to see which apps you already activated.![]() Choose the data ingestion Region, which is the region where the cloud logging service is receiving data from firewalls.Strata Logging Service
Choose the data ingestion Region, which is the region where the cloud logging service is receiving data from firewalls.Strata Logging Service- If you are using Device Security that doesn't require Strata Logging Service, this sends data logs to a cloud logging service that streams them directly to Device Security without storing them in a data lake. Skip to the App Subdomain step.
- If you are using Device Security that does require Strata Logging Service (available for Enterprise
Device Security, OT Device Security, and Medical
Device Security), add
Strata Logging Service.
![]()
- Select a Strata Logging Service instance.
- Enter the amount of data log storage.
- The region is grayed out, but is autopopulated with the same region that you used for Strata Logging Service.
Enter an App Subdomain.![]() Use a unique subdomain to complete the <subdomain>.iot.paloaltonetworks.com URL for your Device Security application. This will be the URL where you log in to the Device Security portal.Agree to the terms and conditions, and Activate.A single default tenant is autocreated behind the scenes, and the product is activated in the tenant.This tenant, and any others created by this Customer Support Portal account, will have the Superuser role.Go to the Common ServicesDevice Associations tab to add firewalls to the tenant, associate them with the Device Security application, and then apply the Device Security subscription to them: Device Associations.Get started with Device Security.Optional Manage your product.Optional Manage identity and access.
Use a unique subdomain to complete the <subdomain>.iot.paloaltonetworks.com URL for your Device Security application. This will be the URL where you log in to the Device Security portal.Agree to the terms and conditions, and Activate.A single default tenant is autocreated behind the scenes, and the product is activated in the tenant.This tenant, and any others created by this Customer Support Portal account, will have the Superuser role.Go to the Common ServicesDevice Associations tab to add firewalls to the tenant, associate them with the Device Security application, and then apply the Device Security subscription to them: Device Associations.Get started with Device Security.Optional Manage your product.Optional Manage identity and access.Device Security X Activation
Learn how to activate your Device Security Device Security X subscription.If you purchased a Device Security X subscription, follow these steps for first time Device Security activation.- Choose the Customer Support Account that you want to use.If you only have one Customer Support Portal account associated with your username, the Customer Support Account is prepopulated.Allocate the product to the Recipient of your choice.The Recipient refers to the TSG that you want to allocate device licenses to. You can select an existing TSG or create a new TSG.Choose the data ingestion Region, which is the region where Strata Logging Service is receiving data from firewalls.Assign device security licenses to your TSG.Specify how many Device Security Subscription licenses you want to assign to the TSG you selected. You can assign as many device licenses as you want, up to the maximum that you purchased. If you want to split the device licenses across multiple TSGs, specify how many you want to assign to the currently selected TSG, out of the available number of device licenses.After you activate Device Security X with a tenant, you can update the device security licenses to increase the number of licenses. You can't decrease the number of licenses assigned to a tenant.Enter an App Subdomain
![]() Use a unique subdomain to complete the <subdomain>.iot.paloaltonetworks.com URL for your Device Security application. This will be the URL where you log in to the Device Security portal.Agree to the terms and conditions, and Activate.A single default tenant is autocreated behind the scenes, and the product is activated in the tenant.This tenant, and any others created by this Customer Support Portal account, will have the Superuser role.Go to the Common ServicesDevice Associations tab to add firewalls to the tenant.Go to the Common ServicesDevice Associations tab to associate Device Security with the firewalls in your tenant.Although the Device Security X subscription allocates device licenses to TSGs, you need to associate Device Security with the firewalls in your tenant for those firewalls to stream logs to Device Security. You don't need to allocate device licenses to individual firewalls within a TSG.Optional Manage your product.When managing your Device Security X subscription in the hub, you can view how many device licenses you have assigned so far, which tenants you have activated the subscription for, and the contract details for your subscription. You can also increase the device assignment for a tenant, or activate the subscription on a new tenant in your Customer Service Account.Optional Manage identity and access.
Use a unique subdomain to complete the <subdomain>.iot.paloaltonetworks.com URL for your Device Security application. This will be the URL where you log in to the Device Security portal.Agree to the terms and conditions, and Activate.A single default tenant is autocreated behind the scenes, and the product is activated in the tenant.This tenant, and any others created by this Customer Support Portal account, will have the Superuser role.Go to the Common ServicesDevice Associations tab to add firewalls to the tenant.Go to the Common ServicesDevice Associations tab to associate Device Security with the firewalls in your tenant.Although the Device Security X subscription allocates device licenses to TSGs, you need to associate Device Security with the firewalls in your tenant for those firewalls to stream logs to Device Security. You don't need to allocate device licenses to individual firewalls within a TSG.Optional Manage your product.When managing your Device Security X subscription in the hub, you can view how many device licenses you have assigned so far, which tenants you have activated the subscription for, and the contract details for your subscription. You can also increase the device assignment for a tenant, or activate the subscription on a new tenant in your Customer Service Account.Optional Manage identity and access.