Strata Logging Service
Forward Logs to AWS S3 Bucket
Table of Contents
Expand All
|
Collapse All
Strata Logging Service Docs
Forward Logs to AWS S3 Bucket
Learn how to forward logs from the Strata Logging Service to an Amazon Simple
Storage Service (S3).
| Where Can I Use This? | What Do I Need? |
|---|---|
| One of these:
|
To meet your long-term storage, reporting and monitoring, or legal and compliance
needs, you can configure Strata Logging Service to forward all logs or a
subset of logs to the AWS S3 Bucket. This integration enables you to make use of the
beneficial features that both Strata Logging Service and Amazon S3 offer for
log management.
Strata Logging Service batch logs based on either a size limit of 1000 lines
or a time limit of 10 seconds, whichever is reached first. Strata Logging Service compresses the log file using Snappy and forwards it
to S3 bucket in JSON format. It is important to note that Palo Alto Networks is only
responsible for delivering logs to the S3 bucket. Any other actions on logs, such as
decompression or processing, should be taken care of by your organization based on
its needs.
- Create and configure the Amazon S3 bucket in the AWS Management Console.Create an Identity and Access Management (IAM) role to permit write access to the Amazon Security Lake bucket location.
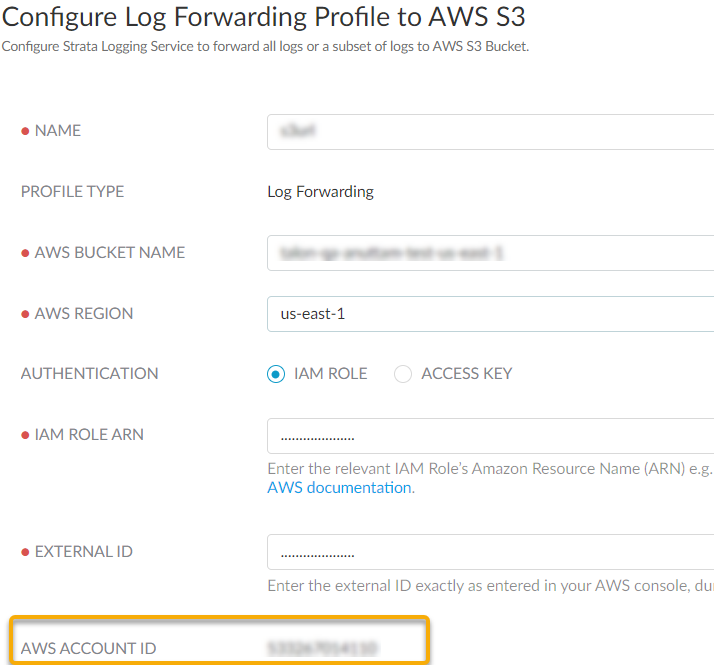
- In the AWS Management Console navigation pane of the console, click RolesCreate role.In the Select trusted entity page, select AWS accountAnother AWS account and enter the Account ID displayed in the Strata Logging Service Configure Log Forwarding Profile to AWS S3 page. This allows your AWS account to assume this role, and share the logs to the desired destination.
![]() Select Require external ID and enter a password to establish connection between Amazon Security Lake and Strata Logging Service.Create policy or use an existing policy in the Add permissions page.
Select Require external ID and enter a password to establish connection between Amazon Security Lake and Strata Logging Service.Create policy or use an existing policy in the Add permissions page.- When you create a new policy, select JSON as the Policy Editor
- Edit the following code to replace DOC-EXAMPLE-BUCKET1 and
DOC-EXAMPLE-BUCKET1/* with your Amazon S3 bucket name.
⦁ { "Version":"2012-10-17", "Statement":[ { "Effect":"Allow", "Action":"s3:PutObject", "Resource": [ "arn:aws:s3:::DOC-EXAMPLE-BUCKET1", "arn:aws:s3:::DOC-EXAMPLE-BUCKET1/*" ] } ] }
- Enter a policy name and create policy.
- Provide a role name and save the changes.In the Roles page, select the role you created and copy and save the IAM Role ARN. You need to use the same ARN when configuring the log forwarding profile.Sign In to the hub.Select the Strata Logging Service instance that you want to configure for log forwarding.If you have multiple Strata Logging Service instances, click the Strata Logging Service tile and select an instance from the list of those available.If you're using Strata Cloud Manager to manage Strata Logging Service, click System SettingsStrata Logging ServiceLog Forwarding forward logs to an external server.Select Log ForwardingCloud Storage to add a new Amazon S3 profile in Strata Logging Service.
![]() Configure the log forwarding profile to forward logs to the AWS S3 bucket.
Configure the log forwarding profile to forward logs to the AWS S3 bucket.- Enter a descriptive Name for the profile.Enter the name of the Amazon S3 configured bucket that is used as the storage container for your forwarded log data. You can get the name from the Amazon Console.Enter the geographic region (regional code) where the Amazon S3 bucket is located.Select the external identification method to authenticate the Amazon S3 bucket.
- IAM Role
- IAM Role ARN - The Amazon Resource Names (ARN) of the role that has access to the Amazon S3 bucket. Enter the ARN you saved in step 1.f. The IAM Role ARN needs to be in the following format: arn:partition:service:region:account-id:resource-type:resource-id
- External ID - The external identifier that you defined while linking the IAM role to your Amazon account.
- Access Key- If you have created a long-term access key to authenticate your AWS account, enter the key and secret password here.
- To create an access key for the Amazon S3 bucket:
- Log in to AWS Management Console with your AWS account ID.
- On the Console Home page, select the IAM service.
- Select Users and then select Create user from the navigation pane.
- On the Specify user details page, enter the name for the new user.
- Do not select Provide user access to the – AWS Management Console and click Next.
- Set Permissions for the
user. Here is a sample of the JSON code to set the
permission boundaries in the
policy:{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": "s3:PutObject", "Resource": [ "arn:aws:s3:::DOC-EXAMPLE-BUCKET1", "arn:aws:s3:::DOC-EXAMPLE-BUCKET1/*" ] } ] }
- Review the selection and create the user.
- In the Summary page, select Security credentials > Create Access Key.
- Select the Third-party service option as the reason for enabling the access key and confirm the recommendation to create the access key.
- Retrieve the access key and use it while configuring the log forwarding.
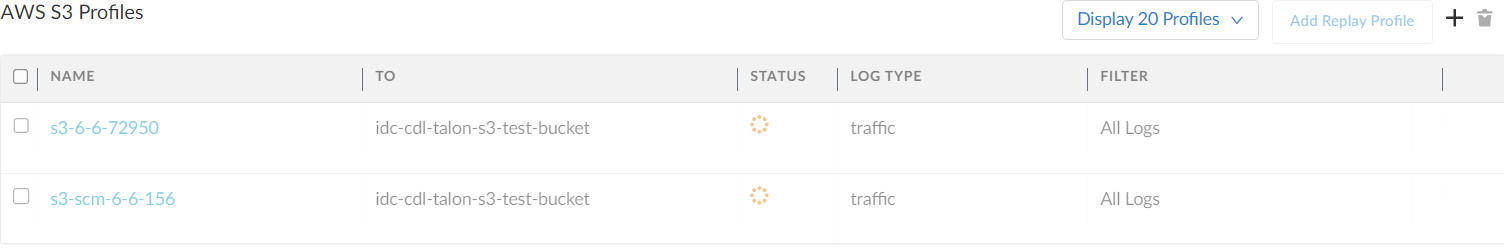
Use this AWS Account ID to connect to the AWS S3 bucket.Test Connection to ensure that the Strata Logging Service can communicate with the receiver.This sends an empty log to the sls_test_events folder in the configured destination to verify that transmission is possible.If the test fails, you won't be able to proceed.Click Next.Specify the Payload Format as JSON - the log format in which the Strata Logging Service forwards logs.(Optional) To receive a STATUS NOTIFICATION when the Strata Logging Service is unable to connect to the Amazon S3 bucket, enter the email address at which you’d like to receive the notification.You'll receive notifications about the issue at least once every 60 minutes until the connection is restored. To prevent any log loss, you must address the connectivity issue within 72 hours. After restoring connectivity, you must manually initiate a log replay within the Strata Logging Service to resend all buffered logs that were not forwarded during the outage. If the connectivity issue persists, logs older than 72 hours will be permanently lost and cannot be recovered.Add the type of log you want to forward and optionally write a query to create filter to forward only the logs that are most critical to you. Save your changesIf you want to forward all logs of the type you selected, do not enter a query.Save your changes.Verify that the Status of your forwarding profile is Running ().![]() Verify if the logs are forwarded to the destination location. This is a sample path: /Amazon S3 bucket location > folder name > logsource.logtype > year > month > date.(Optional) You can use the running Amazon S3 forwarding profile to forward past logs spanning up to 3 days.
Verify if the logs are forwarded to the destination location. This is a sample path: /Amazon S3 bucket location > folder name > logsource.logtype > year > month > date.(Optional) You can use the running Amazon S3 forwarding profile to forward past logs spanning up to 3 days.