Strata Cloud Manager
New Features in May 2025
Table of Contents
Expand All
|
Collapse All
Strata Cloud Manager Docs
New Features in May 2025
Here are the new features available in Strata Cloud Manager in SCM R3,
2025.
Here are the new features we've added to Strata Cloud Manager in May 2025.
New Strata Cloud Manager Management Features (May 2025)
See the new configuration management features we've added to Strata Cloud Manager in
May 2025.
Here's the new configuration management features we've added to Strata Cloud
Manager in May 2025; we use a scheduled upgrade to deliver these features to you and
they are supported with the Cloud Manager 2025.R3.0 release version. Check your Strata
Cloud Manager in-product notifications for updates on the release upgrade schedule. You
can verify which Strata Cloud Manager release version you're running by navigating to
your configuration overview, and checking the
Cloud Management Version.
Strata Cloud Manager: New Best Practice Assessment Checks and Custom Checks
|
May 16, 2025
Supported on Strata Cloud Manager for:
Strata Cloud Manager introduces the following new
checks:
|
Strata Cloud Manager lets you validate your configuration against
predefined Best Practices and custom checks
you create based on the needs of your organization. As you make changes to your
service routes, connection settings, allowed services, and administrative access
settings for the management and auxiliary interfaces for your firewalls, Strata
Cloud Manager gives you assessment results inline so you can take immediate
corrective action when necessary. This eliminates problems that misalignments with
best practices can introduce, such as conflicts and security gaps.
Inline checks let you:
- Gauge the effectiveness of, assess the impact of, and validate changes you make to your configuration using inline assessment results.
- Prioritize and perform remediations based on the recommendations from the inline assessment.
Strata Cloud Manager: Config Cleanup Enhancements
|
May 16, 2025
Supported on Strata Cloud Manager for:
Here are the enhancements for Config Cleanup:
These enhancements offer improved usability, and more
precise control over your configuration cleanup process.
|
Do dynamic business needs often require you to deal with rapid configuration changes
that result in complex configurations with a number of zero hit rules, zero hit
objects, unused objects, and duplicate objects? Such configurations can lead to a
poor security posture and can inadvertently increase the attack surface of your
network. Config Cleanup has you covered.
Config Cleanup gives you a comprehensive view of all policy rules that have no hits,
objects that aren't referenced directly or indirectly in your configuration, objects
that are referenced in a policy rule but have no hits in the Traffic log during the
specified time frame, and objects of the same type with different names but have the
same values so that you can better:
- Manage attack surface exposure
- Prioritize remediation actions
- Remediate over time
- Respond to audit questions when they arise
Identify and remove unused configuration objects and policy rules from your
configuration. Removing unused configuration objects eases administration by
removing clutter and preserving only the configuration objects that are required for
security enforcement.
Review unused objects and policy rules across your entire Strata Cloud Manager
configuration for the last 6 months, and optimize policy rules that are overly
permissive rules to convert these to be more specific, focused rules that only allow
the applications you’re actually using.
Together with Policy Optimizer, these tools help you
ensure that your policy rules stay fresh and up to date.
Strata Cloud Manager: Policy Optimizer Enhancements
|
May 16, 2025
Supported on Strata Cloud Manager for:
Policy Optimizer now
allows you to create address groups within policy
recommendations, addressing challenges in efficiently managing
firewall policies at scale. You can create source and
destination address groups within recommended rules, allowing
you to adjust and preview suggested groups before accepting
recommendations. These enhancements streamline the process of
optimizing firewall policies, helping you balance security and
operational efficiency as your network grows.
|
Overly permissive security rules—such as those allowing "any" application traffic—are
common in large networks, creating security gaps by enabling unused applications and
unnecessarily increasing the attack surface. Manual review and optimization of these
broad rules require extensive log analysis and introduce deployment risk. Strata
Cloud Manager introduces Policy Optimizer that analyzes log data to identify overly
permissive security rules. Policy Optimizer auto-generates specific,
focused rule recommendations based only on the applications actively observed on
your network. This capability eliminates the need for manual log analysis,
strengthens your security posture, and reduces administrative overhead.
Administrators receive actionable, auto-generated optimization recommendations that
can be reviewed and accepted through a guided workflow, ensuring that rule
consolidation and replacement are secure and policy integrity is maintained.
Together with Config Cleanup, these tools help you
ensure that your policy rules stay fresh and up to date.
Strata Cloud Manager: IPv4 Multicast Routing Support
|
May 16, 2025
Supported for:NGFW (Managed by Strata Cloud Manager)
|
Strata Cloud Manager (SCM) now enables you to configure IPv4 multicast routing on
virtual routers and logical routers. You can enable Protocol-Independent Multicast (PIM),
Internet Group Management Protocol (IGMP), and Multicast Source Discovery Protocol
(MSDP) on supported interfaces. Additionally, SCM enables you to configure PIM Interface Timer profiles, MSDP Timer
profiles, and IGMP Interface Query profiles. You can also create IPv4 mroutes, which are static
unicast routes that point to a multicast source. Logical routers support only IGMPv2
and IGMPv3 (not IGMPv1). Only logical routers support a multicast static group
(virtual routers do not).
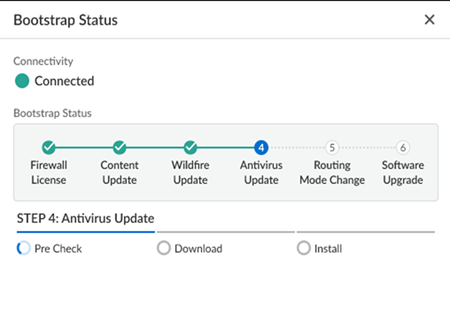
Enhanced Visibility for ZTP Onboarding
|
May 16, 2025
Supported for: NGFW (Managed by Strata Cloud Manager)
|
Installers with minimal technical knowledge often face challenges
onboarding NGFWs at branch locations. Enhanced visibility and status monitoring for
Zero Touch Provisioning (ZTP) addresses this by improving the NGFW
activation process for branch locations, providing visibility and troubleshooting
capabilities. Status monitoring for ZTP onboarding and bootstrapping offers
real-time status updates in Strata Cloud Manager for administrators to review and
monitor throughout the activation and onboarding process.
With status monitoring for onboarding and bootstrapping, you can monitor
the detailed bootup status, including Firewall Licensing, Content Updates, Wildfire
Updates, Antivirus Updates, Routing Mode Changes, and Software Upgrades. The feature
introduces status bars and status spinners that reflect the progress of each stage,
ensuring you have a clear understanding of the activation process. In case of any
interruptions or errors, such as issues with device certificates, TSG ID validation,
software updates, or content updates, the bootstrap status indicates where the
process failed and allows you to immediately restart.
Strata Cloud Manager: Configuration Management Support by Region
May 16, 2025 Supported on:
|
Strata Cloud Manager for Configuration Management is a solution that is defined and
controlled based on the region where it is deployed. You can deploy Strata Cloud
Manager in the locations of your choosing, based on data location preferences and
where you have the most users. For this reason, we are rolling out region-specific
support for Strata Cloud Manager as soon as we are able to do so for each region.
Update:
Strata Cloud Manager now supports the following additional regions:
- Saudi Arabia
- Israel
- Indonesia
Enhanced UI for Security Policy Rules and Software Update Schedules
|
May 16, 2025
Supported on Strata Cloud Manager
|
Strata Cloud Manager provides user interface improvements that streamline
security operations and management efficiency. These updates focus specifically on
making policy and device management more intuitive, simplifying complex workflows,
improving data visibility, and ensuring a smoother user experience. The core goal is
to provide administrators with greater control and clarity over their security
posture and device lifecycle.
- Precise Security Policy Rule Insertion: New security policy rules can now be inserted immediately after a selected rule, simplifying the organization and management of rule sets.
- NGFW Update Schedule Pagination: NGFW software update schedules now feature pagination with clearly defined column headings, which improves both clarity and performance when handling large datasets.
- Non-Disruptive Device Details View: Device details for each update schedule now open in a sidebar panel instead of expanding within the main table. This allows users to view essential details without losing context or disrupting the main table's structure.
New NetSec Platform Features on Strata Cloud Manager (May 2025)
See all the new features made available for Strata Cloud Manager in May
2025.
These new features follow the Strata Cloud Manager release model of continuous feature deployment; as they're ready, we make them
available to ensure the latest support for all products and subscriptions across the
NetSec platform. There's no Strata Cloud Manager upgrade or management version
requirement associated with these features; however, check if they have version or
license dependencies associated with other parts of the NetSec platform (like a
cloud-delivered security service subscription, or a Prisma Access version, for
example).
Granular File Transfer Control in Remote Browser Isolation
|
May 30, 2025
Supported for: Strata Cloud Manager
|
Previously, Remote Browser Isolation (RBI) limited administrators to allowing or
blocking all downloads or all uploads during isolation, regardless of file type.
This lack of flexibility forced administrators to choose between allowing all file
transfers, which could lead to security issues, or blocking all file transfers,
which could result in usability issues and user dissatisfaction.
You can now use isolation profiles in RBI to specify the types of files users can upload or
download, enabling more granular control over data transfers during
isolated browsing sessions. The new capability helps to enhance the security posture
by reducing the attack surface and preventing various types of cybersecurity
threats. It also helps in data exfiltration by controlling which categories of file
types a user is able to upload.
Key use cases include permitting users to download only document files, blocking
downloads of executable files, or permitting transfers of only specific approved
file types. The granular controls enable you to balance security and usability by
tailoring allowed file types to your organization's needs. Configuring file type
filtering enhances your data loss prevention capabilities and provides an additional
layer of protection against potential threats introduced through file transfers.
Strata Copilot: New Region Support
|
May 22, 2025
Supported for: Strata Cloud Manager
|
Strata Copilot now extends its reach to new regions, enhancing global
accessibility. This expansion brings the powerful AI-driven assistance to users in
China, Qatar, and Saudi Arabia. By increasing geographical coverage, Strata Copilot
offers more organizations the opportunity to streamline their security operations,
leverage intelligent insights, and improve overall efficiency in managing their Palo
Alto Networks solutions in Strata Cloud Manager across these diverse locations.
Update:
Strata Copilot now supports the following additional regions:
- China
- Qatar
- Saudi Arabia
Capacity Planning for Mobile Users
Prisma Access now introduces automated capacity planning and IP
address optimization, significantly streamlining the onboarding process for new
administrators. This enhancement eliminates the need for manual capacity estimation
and complex IP address allocation, which historically could extend deployment times
by months. Now, administrators can reduce this to minutes. Users simply input their
anticipated user capacity across various regions, and the system intelligently
determines optimal VM sizing and allocates all necessary IPv4 and IPv6
ingress/egress addresses. This includes support for Mobile User, Explicit Proxy, and
consolidated MU and EP deployments. The system also configures intelligent
autoscaling, ensuring resources dynamically adapt to real-time traffic demands and
user bursts without manual intervention. This comprehensive automation not only
accelerates initial setup but also optimizes ongoing resource utilization, improves
time to value, and simplifies operations for network administrators.
Customizable Prisma Access Agent Session Timeout Settings
|
May 20, 2025
Supported for: Prisma Access (Managed by Strata Cloud
Manager)
|
Unexpected session timeouts and inactivity logouts can significantly disrupt user
productivity and lead to increased helpdesk tickets. Prisma® Access Agent addresses
this issue by introducing configurable notifications that alert users before their
sessions expire or terminate due to inactivity. You can now set up timely warnings
and custom messages to keep your users informed and provide them with the option to
extend their sessions when needed.
You can customize sessions by setting their
duration, scheduling logout notifications, and creating custom expiration messages.
You can set the duration a user can stay logged in to a session, and also set the
amount of time to wait before the agent session ends due to user inactivity. The
ability to customize session timeouts and notifications helps balance user access
needs with network security. It enables you to control session timeouts, keep users
informed about their session status, and communicate important information.
Disable Prisma Access Agent with One-Time Password
|
May 20, 2025
Supported for: Prisma Access (Managed by Strata Cloud
Manager)
|
To address the potential risks of end users disabling the Prisma® Access Agent, your
users can now use a one-time password (OTP) system to
securely disable the agent. With the OTP system, Prisma Access Agent can generate
unique, single-use codes for agent disabling, enhancing security and administrative
control. You can configure the OTP system on a per-user or per-user group basis,
providing granular control over who can disable agents and when. When users enter
the correct OTP, the agent verifies it locally and disables itself, ensuring
functionality even in offline scenarios. This feature also improves auditing
capabilities by logging all OTP-related activities, helping you track and monitor
agent disabling events across your network. By implementing this OTP system, you can
meet compliance requirements, align with industry standards, and provide a more
secure and flexible solution for managing Prisma Access Agents.
Explicit Proxy IPv6 Support
IPv6 support for Explicit Proxy and network services allows you to configure and
manage network policies, security settings, and forwarding profiles using IPv6
addresses directly within your management interface. This crucial update addresses
the critical need for IPv6 integration, helping to overcome IPv4 address exhaustion
and support modern network deployments. This feature extends the platform's
capabilities to fully support IPv6 address ranges across Explicit Proxy and various
network service configurations, integrated seamlessly across UI front-end forms and
pages in both Strata Cloud Manager and Panorama. This
enhancement ensures compatibility and future-readiness for your network deployments
by addressing the evolving landscape of network infrastructures and the increasing
adoption of IPv6, providing flexible and robust security.
Explicit Proxy SOCKS and Basic Authentication
To solve the challenge of securing legacy applications and diverse traffic
types, Prisma Access introduces SOCKS (Socket Secure) proxy and Basic
Authentication support for Explicit Proxy within Prisma Access. This
update allows you to manage SOCKS v5 and v4 settings directly in Strata Cloud Manager, enabling secure delivery for non-HTTPs traffic like FTP and SSH. Additionally,
you can now configure Basic Authentication to ensure compatible identification for
clients that do not support modern authentication protocols.
Explicit Proxy Trusted Source IP List Expansion
To solve the challenge of managing large-scale distributed environments with
extensive IP address allow lists, Prisma Access increases the
Trusted Source IP list limit for Explicit Proxy to 1,024 addresses. This
change allows you to secure traffic from larger networks without reaching
configuration limits or impacting App-ID™ performance. You can manage these
expanded lists within Strata Cloud Manager.
IPv6 Sinkholing for Prisma Access Agent
|
May 20, 2025
Supported for: Prisma Access (Managed by Strata Cloud
Manager)
|
While the Prisma® Access Agent routes mobile user IPv4 traffic through a protected
tunnel to Prisma Access, IPv6 traffic is conventionally sent to the local network
adapter on an endpoint. Prisma Access offers the ability to enhance security for
dual-stack endpoints by sinkholing IPv6 traffic.
By enabling IPv6 sinkholing, you can
effectively mitigate risks associated with IPv6-based threats, thus reducing your
overall attack surface. This feature is valuable in scenarios where you need to
maintain a secure environment for mobile users accessing the internet. As endpoints
can automatically fall back to IPv4 addresses, you can ensure a continuous and
protected user experience without compromising on security. By implementing this
capability, you strike an optimal balance between robust threat prevention and
uninterrupted connectivity for your mobile workforce.
LDAP Support for Prisma Access Agent
|
May 20, 2025
Supported for:
Prisma Access (Managed by Strata Cloud Manager)
|
Organizations transitioning to Prisma® Access Agent face challenges when their
existing authentication infrastructure uses LDAP/LDAPS, as Prisma Access Agent
previously only supported SAML and certificate authentication through Cloud Identity
Engine (CIE). This can create significant adoption barriers, especially in regions
where LDAP usage is prevalent. LDAP support for Prisma Access Agent addresses this
challenge by enabling you to leverage your existing GlobalProtect® portal LDAP
authentication infrastructure, eliminating the need to reconfigure authentication
methods when migrating to Prisma Access Agent.
With LDAP authentication support, you can now
configure your Prisma Access Agent to authenticate users against your existing
directory services through the GlobalProtect portal. This integration provides a
seamless authentication experience for your users while maintaining your existing
security policies. The feature supports all standard LDAP configuration options,
including Base DN, Bind DN, multiple LDAP servers, SSL/TLS secure connections, and
server certificate verification for SSL sessions. You can also combine LDAP
authentication with client certificate authentication using AND/OR logic to meet
your specific security requirements.
The enhanced user experience includes support for saved user credentials, enabling
seamless authentication across device states such as sleep-wake cycles, hibernation,
and network transitions. When properly configured, users won't need to repeatedly
enter their credentials after logging into their operating system.
By supporting LDAP authentication through the GlobalProtect portal, Prisma Access
Agent provides you with a smoother migration path from GlobalProtect to Prisma
Access Agent, preserving your authentication setup while enabling you to transition
to a newer access agent. This feature is valuable for existing deployments where
reconfiguring authentication methods would otherwise increase deployment complexity
and time.
Pre-Logon for Prisma Access Agent
|
May 20, 2025
Supported for: Prisma Access (Managed by Strata Cloud
Manager)
|
To avoid delays in critical device updates and maintain security, you need a way to
connect remote corporate-owned machines to the network before users log in. The
pre-logon feature for Prisma® Access Agent
addresses this challenge by establishing a secure device-level connection before
user authentication occurs.
This feature improves IT productivity and enhances your overall security posture by
ensuring all managed devices receive essential updates and configuration changes,
regardless of the user's login status. You can now perform critical management
tasks—such as applying group policies, installing software updates, and
synchronizing roaming profiles—without waiting for a user to log in.
Pre-logon is designed to provide consistent connectivity for your managed devices
across system restarts and sleep-wake cycles. By utilizing this capability, you
significantly improve the management of your remote assets and enhance security by
ensuring devices are properly configured and updated before users gain full network
access.
Prisma Access Agent Captive Portal Support
|
May 20, 2025
Supported for:
|
Mobile users often struggle to connect securely when working from locations with
captive portals, such as hotels, cafes, and airports. These captive portals require
authentication before allowing internet access. Prisma® Access Agent automatically
detects when a user has connected to a network with a captive portal and opens the
captive portal authentication page in its embedded browser, enabling users to
authenticate without bypassing security policies. This approach enhances security by
containing the captive portal interaction within the controlled environment of the
embedded browser, mitigating risks associated with external browser use.
By using captive portal support with Prisma Access
Agent's embedded browser functionality, you ensure that your mobile workforce
maintains secure access to corporate resources across diverse network environments.
It prevents scenarios where employees are unable to access the internet or corporate
resources due to undetected captive portals, while also addressing security concerns
related to captive portal interactions. This solution significantly reduces
connectivity-related support tickets, improves overall user productivity, and
provides an integrated, secure experience for your remote and traveling employees
while maintaining the stringent security standards your organization requires.
Prisma Access Agent Embedded Browser Support for SAML Authentication
|
May 20, 2025
Supported for:
|
Managing SAML authentication across various web browsers poses significant challenges
for administrators, often resulting in a cumbersome user experience with annoying
pop-ups and redirection issues between the access agent and browser.
The Prisma® Access Agent embedded browser addresses this issue by
integrating a dedicated browser directly into the agent, providing your users with a
consistent in-app experience for Prisma Access Agent logins, simplifying
administration, and significantly enhancing security posture. By keeping the
authentication process within the application, you eliminate the need for external
browser interactions, reduce the risk of user confusion, and mitigate potential
security vulnerabilities associated with browser redirections. This internal
processing environment ensures strict adherence to conditional access policies,
which also simplifies administrative overhead.
With support for various authentication methods and compatibility with existing
Prisma Access Agent features, the embedded browser significantly improves both
security and usability in your remote access infrastructure.
Transparent Proxy Support for Prisma Access Agent
|
May 20, 2025
Supported for:
Prisma Access (Managed by Strata Cloud Manager)
|
Prisma® Access Agent now supports transparent proxy connections, offering
always-on internet security and private app access for your mobile users. This
feature enables seamless coexistence with third-party VPN agents, enhancing your
organization's security posture. You can use it to secure all internet traffic from
browser and nonbrowser apps, even when users are disconnected from the tunnel. The
solution forwards internet traffic to Prisma Access, preventing users from bypassing
Prisma Access.
You can support various scenarios including users connecting from home, branch
offices, or public Wi-Fi. It's compatible with endpoints running third-party VPNs in
full or split tunnel modes. The feature prevents conflicts on endpoints and offers
admin controls to maintain smooth operation. You will find this useful for
maintaining consistent security across diverse networks. It supports continuous
trust verification for mobile users through device posture checks. By implementing
this functionality, you can enforce security policies regardless of user location or
connection method, strengthening your overall security stance and strengthening your
overall security posture with always-on connectivity.
Extend Prisma Access User Group Policy Support with Short Form Format
|
May 16, 2025
Supported for: Prisma Access (Managed by Strata Cloud
Manager) and Prisma Access (Managed by Panorama)
|
We introduced the ability to extend Prisma Access user group policy
with the short form format. Migrating security policies from NGFW to Prisma Access
requires policy elements standardization. Prisma Access only supports long-form DN
entries for group-based policies, while the NGFW allows using other formats such as
SAML account name/Common Name and email address. This feature enables customers to
define the group format choice for security policy creation, allowing standardized
policy creation across Prisma Access and NGFW.
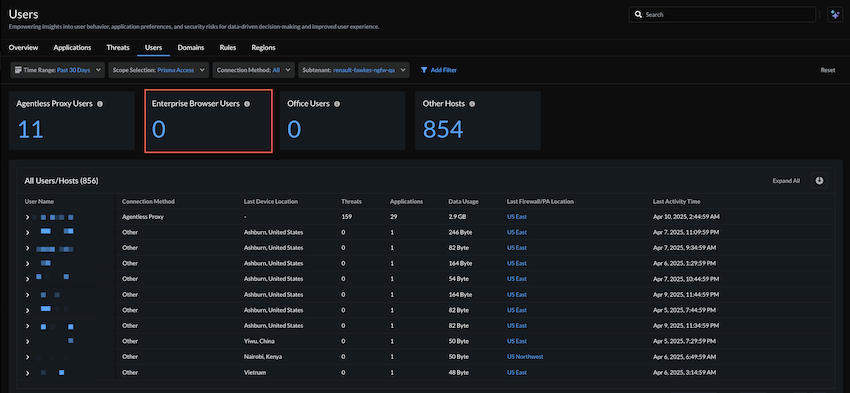
Visibility for Enterprise Browser
|
May 13, 2025
Supported for: Strata Cloud Manager
|
Achieving granular visibility into user activity across various enterprise browsers
was previously a challenge. Now, depending on your license, Strata Cloud Manager
offers the following new features for advanced monitoring:
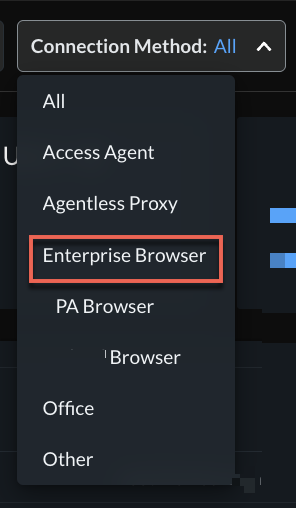
- Activity InsightsUsersNew Connection Method = Enterprise BrowserEnterprise Browser is now available as a Connection Method to filter user activity by Enterprise Browsers in Prisma® Access. You can view the following details:
- Active Users trend chart
- Current Active User count and list
- Risky Users
- Active Users list including User Name, Browser Type, Browser Version, Last Source IP, Last Source Location, Last Used PA Location, and Last Activity Time
![]() If you have multiple enterprise browsers, you can switch to Prisma® Access Browser or any other supported third-party enterprise browser using Connection Method.
If you have multiple enterprise browsers, you can switch to Prisma® Access Browser or any other supported third-party enterprise browser using Connection Method.![]()
- Subscription Usage for Mobile Users: MonitorSubscription UsageMobile UsersYou can see the usage count under Total Unique Users.
- Prisma® Access locations: MonitorPrisma Access LocationsNew widget for Explicit Proxy locations, status, and connectivity to Strata Logging Service.
CVE Threat Research for Strata Copilot
|
May 9, 2025
Supported on Strata Cloud Manager
|
You can now quickly determine if Palo Alto
Networks provides protection against specific vulnerabilities using Strata
Copilot. When investigating specific CVEs, Strata Copilot searches
comprehensive data sources to provide detailed protection information including
unique threat IDs, descriptions, categories, compatible PAN-OS versions, release
dates, and current status.
To receive information about available safeguards for deeper investigation,
you can simply ask questions like:
"Is there coverage for the CVE mentioned in this article?
<articleURL>"
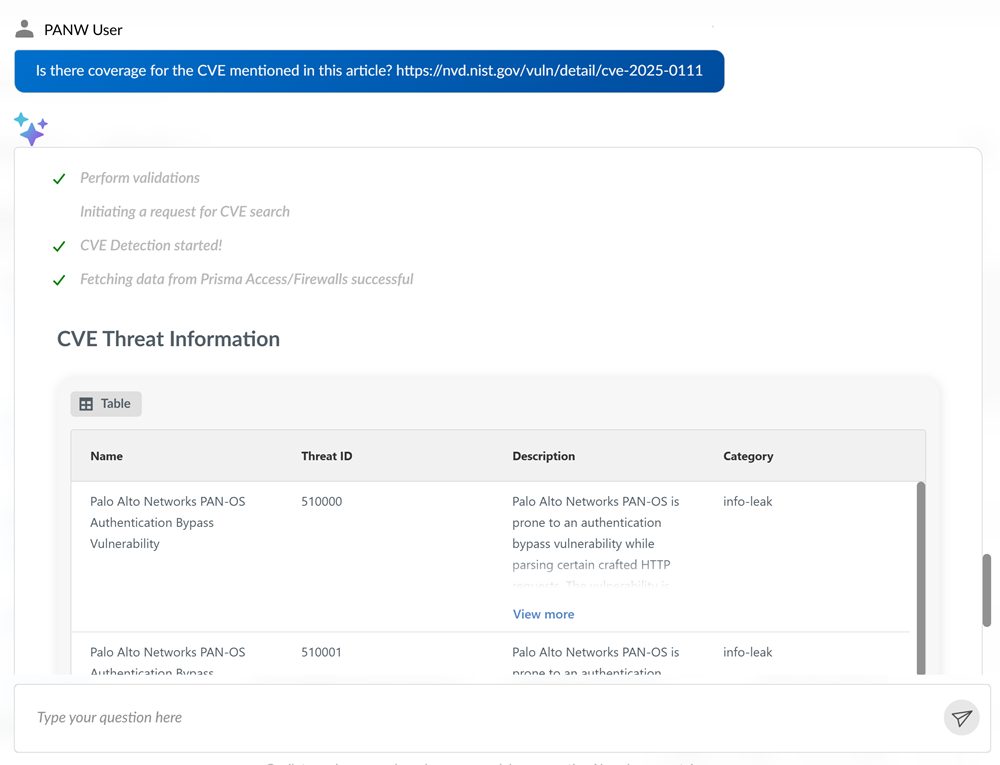
"Does Palo Alto Networks protect against
<CVE>?"
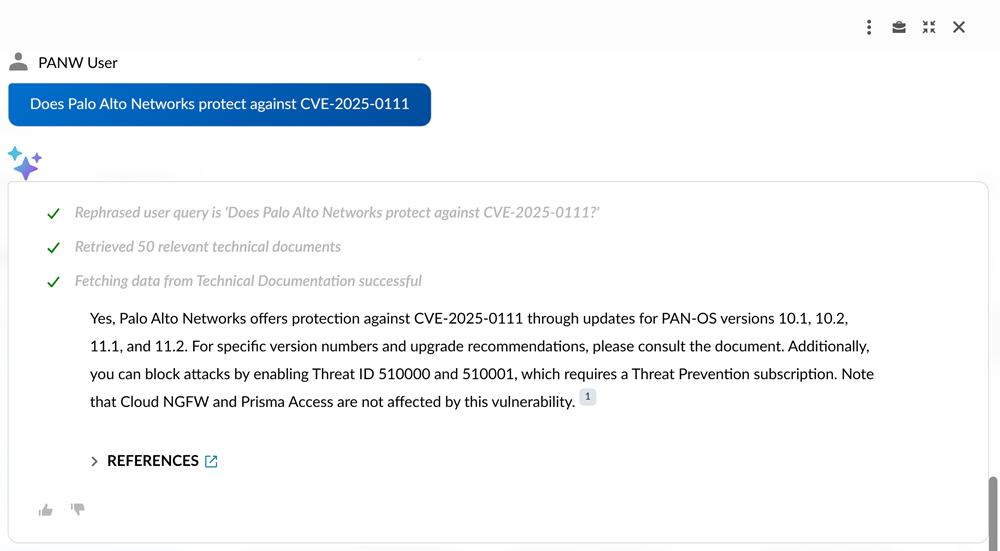
Designed for enterprise-scale performance, Strata Copilot handles large
datasets related to Threat Detection and Prevention data while delivering responses
in under 5 seconds for most threat intelligence queries. Strata Copilot minimizes
latency between data updates and availability to ensure you always receive the most
current information about CVE protection status and potential threat actor
exploitation activity in your environment.