Deploy the VM-Series Firewall from the Azure Marketplace (Solution Template)
Table of Contents
9.1 (EoL)
Expand all | Collapse all
-
- VM-Series Deployments
- VM-Series in High Availability
- Enable Jumbo Frames on the VM-Series Firewall
- Hypervisor Assigned MAC Addresses
- Custom PAN-OS Metrics Published for Monitoring
- Interface Used for Accessing External Services on the VM-Series Firewall
- PacketMMAP and DPDK Driver Support
-
- VM-Series Firewall Licensing
- Create a Support Account
- Serial Number and CPU ID Format for the VM-Series Firewall
-
- Activate Credits
- Transfer Credits
- Create a Deployment Profile
- Manage a Deployment Profile
- Provision Panorama
- Migrate Panorama to a Software NGFW License
- Renew Your Software NGFW Credits
- Amend and Extend a Credit Pool
- Deactivate License (Software NGFW Credits)
- Delicense Ungracefully Terminated Firewalls
- Create and Apply a Subscription-Only Auth Code
- Migrate to a Flexible VM-Series License
-
- Generate Your OAuth Client Credentials
- Manage Deployment Profiles Using the Licensing API
- Create a Deployment Profile Using the Licensing API
- Update a Deployment Profile Using the Licensing API
- Get Serial Numbers Associated with an Authcode Using the API
- Deactivate a VM-Series Firewall Using the API
- Use Panorama-Based Software Firewall License Management
- What Happens When Licenses Expire?
- Install a Device Certificate on the VM-Series Firewall
-
- Supported Deployments on VMware vSphere Hypervisor (ESXi)
-
- Plan the Interfaces for the VM-Series for ESXi
- Provision the VM-Series Firewall on an ESXi Server
- Perform Initial Configuration on the VM-Series on ESXi
- Add Additional Disk Space to the VM-Series Firewall
- Use VMware Tools on the VM-Series Firewall on ESXi and vCloud Air
- Use vMotion to Move the VM-Series Firewall Between Hosts
- Use the VM-Series CLI to Swap the Management Interface on ESXi
-
-
- VM-Series Firewall for NSX-V Deployment Checklist
- Install the VMware NSX Plugin
- Apply Security Policies to the VM-Series Firewall
- Steer Traffic from Guests that are not Running VMware Tools
- Add a New Host to Your NSX-V Deployment
- Dynamically Quarantine Infected Guests
- Migrate Operations-Centric Configuration to Security-Centric Configuration
- Use Case: Shared Compute Infrastructure and Shared Security Policies
- Use Case: Shared Security Policies on Dedicated Compute Infrastructure
- Dynamic Address Groups—Information Relay from NSX-V Manager to Panorama
-
- Supported Deployments of the VM-Series Firewall on VMware NSX-T (North-South)
- Components of the VM-Series Firewall on NSX-T (North-South)
-
- Install the Panorama Plugin for VMware NSX
- Enable Communication Between NSX-T Manager and Panorama
- Create Template Stacks and Device Groups on Panorama
- Configure the Service Definition on Panorama
- Deploy the VM-Series Firewall
- Direct Traffic to the VM-Series Firewall
- Apply Security Policy to the VM-Series Firewall on NSX-T
- Use vMotion to Move the VM-Series Firewall Between Hosts
- Extend Security Policy from NSX-V to NSX-T
-
- Components of the VM-Series Firewall on NSX-T (East-West)
- VM-Series Firewall on NSX-T (East-West) Integration
- Supported Deployments of the VM-Series Firewall on VMware NSX-T (East-West)
-
- Install the Panorama Plugin for VMware NSX
- Enable Communication Between NSX-T Manager and Panorama
- Create Template Stacks and Device Groups on Panorama
- Configure the Service Definition on Panorama
- Launch the VM-Series Firewall on NSX-T (East-West)
- Add a Service Chain
- Direct Traffic to the VM-Series Firewall
- Apply Security Policies to the VM-Series Firewall on NSX-T (East-West)
- Use vMotion to Move the VM-Series Firewall Between Hosts
- Extend Security Policy from NSX-V to NSX-T
- Use Migration Coordinator to Move Your VM-Series from NSX-V to NSX-T
-
-
- Deployments Supported on AWS
-
- Planning Worksheet for the VM-Series in the AWS VPC
- Launch the VM-Series Firewall on AWS
- Launch the VM-Series Firewall on AWS Outpost
- Create a Custom Amazon Machine Image (AMI)
- Encrypt EBS Volume for the VM-Series Firewall on AWS
- Use the VM-Series Firewall CLI to Swap the Management Interface
- Enable CloudWatch Monitoring on the VM-Series Firewall
- VM-Series Firewall Startup and Health Logs on AWS
- Use Case: Secure the EC2 Instances in the AWS Cloud
- Use Case: Use Dynamic Address Groups to Secure New EC2 Instances within the VPC
-
-
- What Components Does the VM-Series Auto Scaling Template for AWS (v2.0) Leverage?
- How Does the VM-Series Auto Scaling Template for AWS (v2.0 and v2.1) Enable Dynamic Scaling?
- Plan the VM-Series Auto Scaling Template for AWS (v2.0 and v2.1)
- Customize the Firewall Template Before Launch (v2.0 and v2.1)
- Launch the VM-Series Auto Scaling Template for AWS (v2.0)
- SQS Messaging Between the Application Template and Firewall Template
- Stack Update with VM-Series Auto Scaling Template for AWS (v2.0)
- Modify Administrative Account and Update Stack (v2.0)
-
- Launch the Firewall Template (v2.1)
- Launch the Application Template (v2.1)
- Create a Custom Amazon Machine Image (v2.1)
- VM-Series Auto Scaling Template Cleanup (v2.1)
- SQS Messaging Between the Application Template and Firewall Template (v2.1)
- Stack Update with VM-Series Auto Scaling Template for AWS (v2.1)
- Modify Administrative Account (v2.1)
- Change Scaling Parameters and CloudWatch Metrics (v2.1)
-
-
- Enable the Use of a SCSI Controller
- Verify PCI-ID for Ordering of Network Interfaces on the VM-Series Firewall
-
- Deployments Supported on Azure
- Deploy the VM-Series Firewall from the Azure Marketplace (Solution Template)
- Deploy the VM-Series Firewall from the Azure China Marketplace (Solution Template)
- Deploy the VM-Series Firewall on Azure Stack
- Enable Azure Application Insights on the VM-Series Firewall
- Set up Active/Passive HA on Azure
- Use the ARM Template to Deploy the VM-Series Firewall
-
- About the VM-Series Firewall on Google Cloud Platform
- Supported Deployments on Google Cloud Platform
- Create a Custom VM-Series Firewall Image for Google Cloud Platform
- Prepare to Set Up VM-Series Firewalls on Google Public Cloud
-
- Deploy the VM-Series Firewall from Google Cloud Platform Marketplace
- Management Interface Swap for Google Cloud Platform Load Balancing
- Use the VM-Series Firewall CLI to Swap the Management Interface
- Enable Google Stackdriver Monitoring on the VM Series Firewall
- Enable VM Monitoring to Track VM Changes on GCP
- Use Dynamic Address Groups to Secure Instances Within the VPC
- Locate VM-Series Firewall Images in the GCP Marketplace
-
- Prepare Your ACI Environment for Integration
-
-
- Create a Virtual Router and Security Zone
- Configure the Network Interfaces
- Configure a Static Default Route
- Create Address Objects for the EPGs
- Create Security Policy Rules
- Create a VLAN Pool and Domain
- Configure an Interface Policy for LLDP and LACP for East-West Traffic
- Establish the Connection Between the Firewall and ACI Fabric
- Create a VRF and Bridge Domain
- Create an L4-L7 Device
- Create a Policy-Based Redirect
- Create and Apply a Service Graph Template
-
- Create a VLAN Pool and External Routed Domain
- Configure an Interface Policy for LLDP and LACP for North-South Traffic
- Create an External Routed Network
- Configure Subnets to Advertise to the External Firewall
- Create an Outbound Contract
- Create an Inbound Web Contract
- Apply Outbound and Inbound Contracts to the EPGs
- Create a Virtual Router and Security Zone for North-South Traffic
- Configure the Network Interfaces
- Configure Route Redistribution and OSPF
- Configure NAT for External Connections
-
-
- Choose a Bootstrap Method
- VM-Series Firewall Bootstrap Workflow
- Bootstrap Package
- Bootstrap Configuration Files
- Generate the VM Auth Key on Panorama
- Create the bootstrap.xml File
- Prepare the Licenses for Bootstrapping
- Prepare the Bootstrap Package
- Bootstrap the VM-Series Firewall on AWS
- Bootstrap the VM-Series Firewall on Azure
- Bootstrap the VM-Series Firewall on Google Cloud Platform
- Verify Bootstrap Completion
- Bootstrap Errors
End-of-Life (EoL)
Deploy the VM-Series Firewall from the Azure Marketplace (Solution Template)
The following instructions describe how to
deploy the solution template for the VM-Series firewall that is
available in the Azure® Marketplace and the Azure Government Marketplace.
To use the customizable Azure Resource Manager (ARM) templates available
in the GitHub repository, see Use
the ARM Template to Deploy the VM-Series Firewall.

- Set up an Azure account.
- If you don’t have one already, create a Microsoft® account.
- Log in to the Azure portal (https://portal.azure.com or https://portal.azure.us)
using your Microsoft account credentials.If you are using a trial subscription, you may need to open a support request (Help + SupportNew Support Request) to increase the quota of allocated VM cores.
- Find the VM-Series solution template in the Azure Marketplace.
- Select MarketplaceVirtual Machines.
- Search for Palo Alto Networks® and a list of offerings
for the VM-Series firewall will display. For the differences in
the BYOL (bring your own license) and PAYG (pay as you go) models,
see VM-Series
Firewall Licenses for Public Clouds.
![]()
- Select an offering to Create a new VM-Series firewall.
- Deploy the firewall.
- Configure basic settings for the firewall.
- Select your Azure Subscription.
- Create a new resource group or select an existing resource group that is empty. The resource group will hold all the resources associated with the VM-Series firewall for this deployment.Azure has removed the option to select an existing resource group for Marketplace solutions that enable multiple network interface controllers (NICs). To deploy the firewall into an existing resource group, use the ARM template in the GitHub Repository or use your own custom ARM template.
- Select the Azure Region in which you are deploying the firewall.
- Enter a Username for the firewall administrator.
- Select the Authentication type—Password or SSH Public Key.You must enable SSH key authentication if you plan to use the firewall in FIPS-CC operational mode. Although you can deploy the VM-Series firewall using a username and password, you will be unable to authenticate using the username and password after changing the operational mode to FIPS-CC. After resetting to FIPS-CC mode, you must use the SSH key to log in and can then configure a username and password that you can use for subsequently logging in to the firewall web interface. For details on creating the SSH key, refer to the Azure documentation.
- Enter a Password (up to 31 characters) or copy and paste an SSH public key for securing administrative access to the firewall.
- Configure networking.
- Select an existing Azure Virtual Network (VNet) or create a new one and enter the IP address space for the VNet. By default, the Classless Inter-Domain Routing (CIDR) IP address is 10.8.0.0/16.
- Configure the subnets for the network interfaces.If you use the default subnets, you must review the configuration. If you use an existing VNet, you must have set up three subnets: one each for the management,trust, and untrust interfaces. If you create a new VNet, verify or change the prefixes for each subnet. The default subnets are 10.8.0.0/24 for the management subnet, 10.8.1.0/24 for the untrust subnet, and 10.8.2.0/24 for the trust subnet.
- Enter the source IP address or IP range (include the CIDR block) that can access the VNet. Network Security Group: inbound source IP allows you to restrict inbound access to the Azure VNet.Restrict access to the firewall. Make sure to supply a CIDR block that corresponds to your dedicated management IP addresses or network. Do not make the allowed source network range larger than necessary and never configure the allowed source as 0.0.0.0/0. Verify your IP address before you configure it on the template to make sure that you do not lock yourself out.
![]()
- Define management access to the firewall.
- Use the default variable ((new) fwMgmtPublicIP)) to assign a Public IP address to the management interface (eth0) of the firewall.Azure accelerated networking is not supported on the management interface.
- Enter a prefix to access the firewall using a DNS name. You must combine the prefix you enter with the suffix displayed on screen to access the web interface of the firewall. For example:<your-name><your-region>.cloudapp.azure.com
- Select latest VM-Series Version.
- Enter a display name to identify the VM-Series firewall within the resource group.
![]()
- Add the information to configure the firewall at launch.
See Bootstrap
the VM-Series Firewall on Azure.
- Select yes to Enable Bootstrap.
- Enter the Storage Account Name that holds the Bootstrap Package.
- Enter the Storage Account Access Key. This firewall needs this access key to authenticate to the storage account and access the files stored within.
- Add the File share name to which you have uploaded the files required for bootstrapping the firewall. The storage account must be in the same region in which you are deploying the firewall and it must have the correct folder structure for bootstrapping.
- (Optional) Share-directory—If you have a common file share you can use a share-directory to create a folder hierarchy and access a specific set of subfolders within the common file-share.
- Select the Azure virtual machine tier and size to meet your needs. Use the Change size link to view supported instance types, and to review the Minimum System Requirements for the VM-Series on Azure.
- Review the summary, and OK.
Then accept the terms of use and privacy policy, and Create to
launch the firewall.
![]()
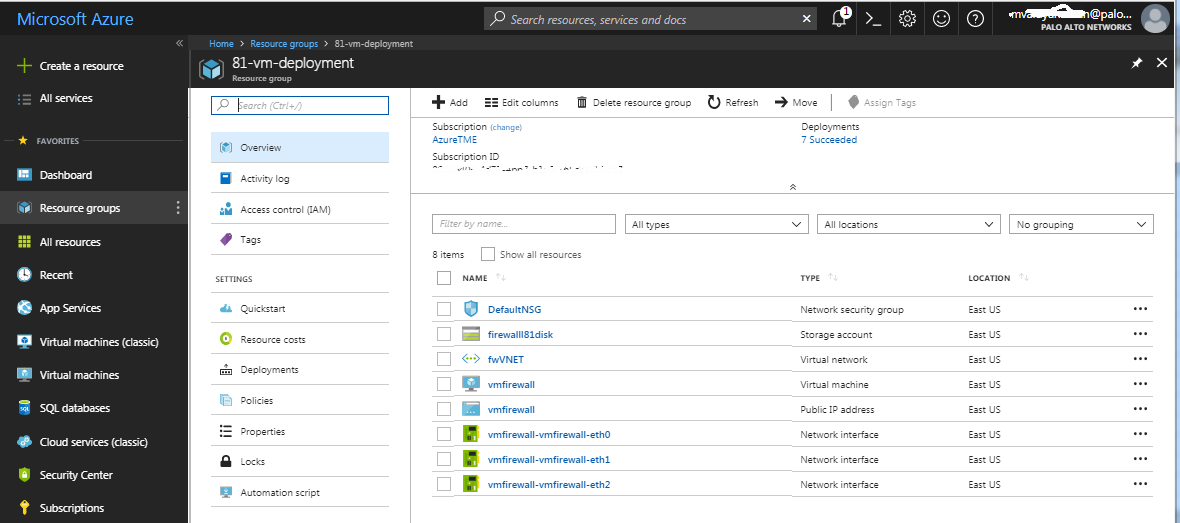
- Verify that you have successfully deployed the VM-Series
firewall.
- Select DashboardResource Groups and select the resource group.
- Select your resource group and see the Overview for detailed status on which resources are deployed successfully.
![]()
- Configure basic settings for the firewall.
- Attach a public IP address for the untrust interface
of the VM-Series firewall. When you create a new public IP address,
you get one from the block of IP addresses that Microsoft owns,
so you can’t choose a specific one. The maximum number of public
IP addresses you can assign to an interface is based on your Azure
subscription.
- On the Azure portal, select the network interface for which you want to add a public IP address (such as the eth1 interface).
- Select IP ConfigurationsAdd and, for Public IP address, select Enabled. Create a new public IP address or select one that you have available.
- Verify that you can view the secondary IP address associated with the interface.
![]() When you attach a secondary IP address to a network interface, the VM-Series firewall does not automatically acquire the private IP address assigned to the interface. You will need to manually configure the private IP address using the VM-Series firewall web interface. See Configure the dataplane network interfaces as Layer 3 interfaces on the firewall.
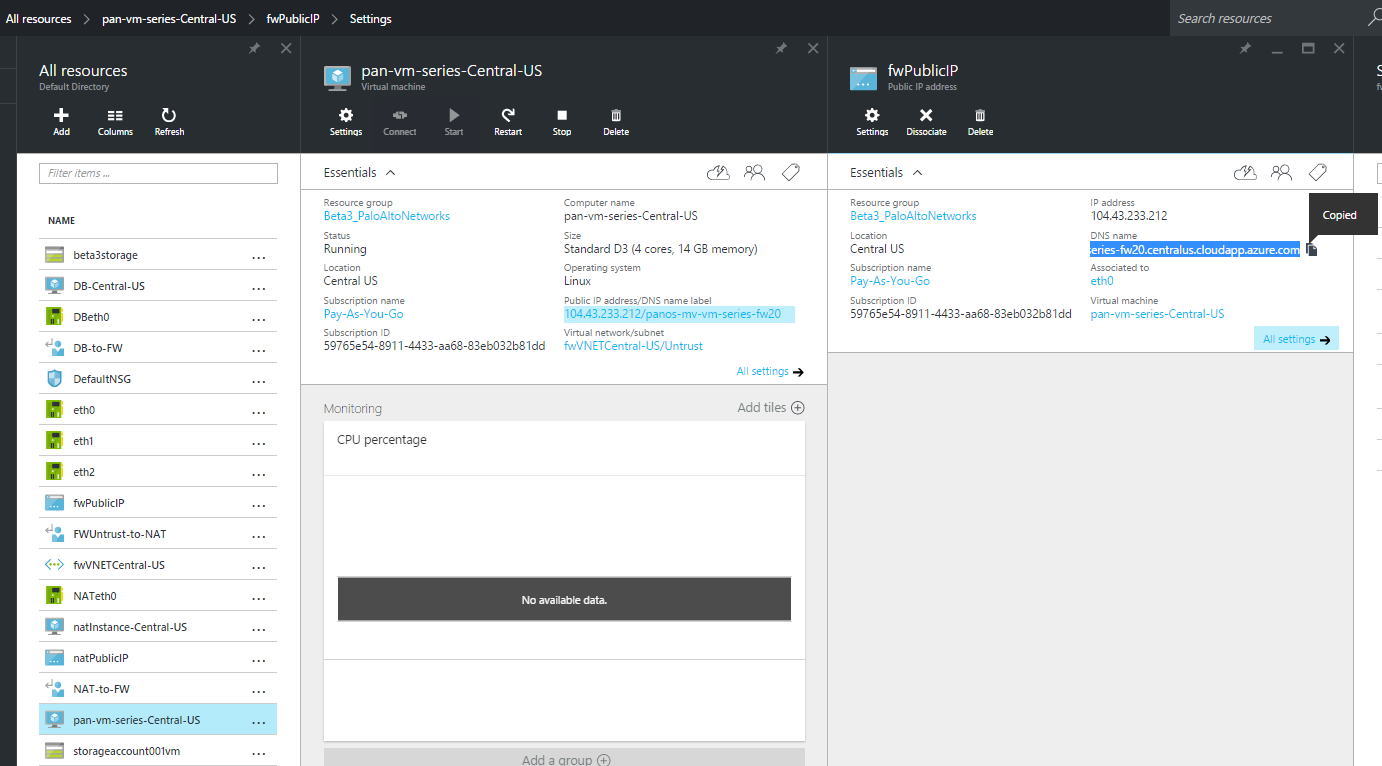
When you attach a secondary IP address to a network interface, the VM-Series firewall does not automatically acquire the private IP address assigned to the interface. You will need to manually configure the private IP address using the VM-Series firewall web interface. See Configure the dataplane network interfaces as Layer 3 interfaces on the firewall. - Log in to the web interface of the firewall.
- On the Azure portal, in All Resources, select the VM-Series firewall and view the full DNS name for the firewall.
![]()
- Using a secure (https) connection from your web browser, log in to the DNS name for the firewall.
- Enter the usernamepassword that you defined in the parameters file. You will see a certificate warning but that is OK—continue to the web page.
- Activate the licenses on the VM-Series firewall.For the BYOL version
- Create a Support Account.
- Register the VM-Series Firewall (with auth code).
- On the firewall web interface, select DeviceLicenses and select Activate feature using authentication code.
- Enter the capacity authentication code (auth-code) that you registered on the support portal. The firewall will connect to the update server (updates.paloaltonetworks.com), and download the license and reboot automatically.
- Log back in to the web interface and confirm the following
on the Dashboard:
- A valid serial number displays in Serial#.If the term Unknown displays, it means the firewall is not licensed. To view traffic logs on the firewall, you must install a valid capacity license.
- The VM Mode displays as Microsoft Azure.
For the PAYG version - Configure
the dataplane network interfaces as Layer 3 interfaces on the firewall.If you are hosting multiple websites or services with different IP addresses and SSL certificates on a single server, you might need to configure more than one IP address on the VM-Series firewall interfaces.
- Select NetworkInterfacesEthernet.
- Click ethernet 1/1 and configure
as follows:
- Set Interface Type to Layer3 (default).
- On the Config tab, assign the interface to the default router.
- Also on the Config tab, expand the Security Zone drop-down and select New Zone. Define a new zone called UnTrust, and then click OK.
- On the IPv4 tab, select DHCP Client if you plan to assign only one IP address on the interface—the firewall will automatically acquire the private IP address assigned in the ARM template. If you plan to assign more than one IP address, select Static and manually enter the primary and secondary IP addresses assigned to the interface on the Azure portal.
- Disable (clear) the Automatically create default route to default gateway provided by server to ensure that traffic handled by this interface does not flow directly to the default gateway in the VNet.
- Click ethernet 1/2 and configure
as follows:
- Set Interface Type to Layer3 (default).
- Set Security Zone to Trust.
- Set IP address DHCP Client or Static.
- Disable (clear) the Automatically create default route to default gateway provided by serverto ensure that traffic handled by this interface does not flow directly to the default gateway in the VNet.
- Commit your changes and verify that the link state for the interfaces is up.
- Add a static route on the virtual router of the VM-Series
firewall for any networks that the firewall needs to route.For example, to add a default route to the destination subnets for the servers that the firewall secures:
- Select NetworkVirtual Routerdefault
- Select Static RoutesIPv4, and add the next hop IP address for the destination servers. You can set x.x.x.1 as the next hop IP address for all traffic (destined to 0.0.0.0/0 from interface ethernet1/1).
- Configure the firewall for your specific deployment.
- Gateway—Deploy a third-party load balancer in front of the UnTrust zone.
- Hybrid and Inter-VNet—Deploy an Azure VPN Gateway or a NAT virtual machine in front the UnTrust zone.
- Inter-Subnet—On the VM-Series firewall, add an intrazone Security policy rule to allow traffic based on the subnets attached to the Trust interface.
- GlobalProtect™—Deploy a NAT virtual machine in front of the UnTrust zone.
- Direct traffic to the VM-Series firewall.
- To ensure that the VM-Series firewall secures all traffic within the Azure resource group, configure static routes on the firewall.
- Configure user defined routes to direct all traffic
through the interfaces on the VM-Series firewall. Refer to the Azure
documentation on UDRs for details.The user defined routes on the internal subnets must send all traffic through the Trust interface. The user defined routes on the UnTrust side direct all traffic from the Internet through the UnTrust interface on the VM-Series firewall. The traffic from the Internet may be coming from an Azure Application Gateway or Azure Load Balancer, or through the Azure VPN Gateway in the case of a hybrid deployment that connects your on-premise network with the Azure cloud.
- To publish PAN-OS® metrics to Azure Application Insights, see Enable Azure Application Insights on the VM-Series Firewall.