Setting Microsoft AD CS Permissions
Table of Contents
Expand all | Collapse all
-
- Activate Next-Generation Trust Security
-
-
- Configure Akamai Connection
- Configure AWS Connection
- Configure Azure Key Vault Connection
-
- Workload Identity Federation Authentication
- Workload Identity Federation - Azure Identity Provider Authentication
- Next-Gen Trust Security Generated Key Authentication
- User Permissions
- Workload Identity Federation Authentication
- Next-Gen Trust Security Generated Key Authentication
- User Permissions
- Supported OIDC Claims
-
-
-
- Working with the Built-in CA
- Add AWS Public CA
- Add AWS Private CA
- Add DigiCert One Certificate Authority
- Add Entrust
- Add GlobalSign Atlas
- Add GlobalSign MSSL
- Add GoDaddy
- Add Google Cloud Private CA
- Add a HID PKIaaS CA
- Add Certificate Manager - Self-Hosted
- Set Up an OpenSSL Certificate Authority Connector
- Create a Sectigo Certificate Manager Certificate Authority
- Add Zero Touch PKI
- Set Up Certificate Expiration Notifications
- Using a Custom DNS Provider
-
-
-
-
- Create an F5 BIG-IP LTM Machine
- Create a Microsoft Azure Private Key Vault Machine
- Create a Microsoft Azure Application Registration Machine
- Create a Microsoft IIS Machine
- Create a Microsoft Windows (PowerShell) Machine
- Create a Microsoft SQL Server Machine
- Create a Common KeyStore Machine
- Create a Citrix ADC Machine
- Create an Imperva WAF Machine
- Create a VMware NSX Advanced Load Balancer (AVI) Machine
- Create an A10 Thunder ADC Machine
- Create a Cloudflare Machine
- Create Kemp Virtual LoadMaster Machine
- Create a Palo Alto Networks Panorama Machine
- Create a Radware Alteon Machine
-
- Provision to an F5 BIG-IP LTM
- Provision to a Microsoft Azure Private Key Vault
- Provision to Microsoft IIS
- Provision to Microsoft Windows (PowerShell)
- Provision to Microsoft SQL Server
- Provision to a Common KeyStore
- Provision to a Citrix ADC
- Provision to an Imperva WAF
- Provision to VMware NSX Advanced Load Balancer (AVI)
- Provision to an A10 Thunder ADC
- Provision to Cloudflare
- Provision to a Kemp Virtual LoadMaster
- Provision to Palo Alto Networks Panorama
- Provision Certificates to Radware Alteon
-
-
- 47-Day Validity Readiness TLS Certificates
- About the Certificate Inventory
- Managing Certificate Lifecycle Settings
- Reissuing Certificates in Next-Gen Trust Security
- Downloading Certificates, Certificate Chains, and Keystores
- Retiring, Recovering, and Deleting Certificates
- Finding Certificates in the Certificate Inventory
- Importing Certificates from DigiCert
- Importing Certificates from EJBCA
- Importing Certificates from GlobalSign Atlas
- Importing Certificates from GlobalSign MSSL
- Domain-Based Validation for External Emails
-
- Create a Workload Identity Management or Discovery Agent Built-in Account
- Create an OCI Registry Built-in Account
- Create a Certificate Manager - Self-Hosted Built-in Account
- Create a Scanafi Built-in Account
- Toggling a Built-in Account on or Off
- Editing Built-in Accounts
- Deleting Existing Built-in Accounts
- Renew Existing Built-in Accounts
- Troubleshooting
Setting Microsoft AD CS Permissions
Next-Gen Trust Security can manage certificates issued by Microsoft Active Directory Service (AD CS) if you configure AD CS to connect to Next-Gen Trust Security.
When setting up AD CS with Next-Gen Trust Security, it is essential to use the appropriate Service Account or User Account with the necessary permissions to ensure a smooth and secure connection.
This topic walks you through how to set up your Microsoft AD CS account so that it can integrate with Next-Gen Trust Security. Go through these steps prior to setting up the AD CS certificate authority in Next-Gen Trust Security.
Service Account Requirements
To connect Microsoft AD CS to Next-Gen Trust Security, you must use a Service Account with the following permissions:
- Read - Necessary for the Service Account to access CA configuration and certificate information, ensuring it can perform its duties correctly.
- Log on as a service - Required because the certificate service (VSatellite Worker, which is the bridge that allows VSatellite to interact with AD CS) runs as a background service. Without this right, the Service Account cannot start the service, leading to failures in certificate issuance and management.
- Issue and Manage Certificates - Allows the Service Account to issue, revoke, and manage certificates, which is essential for maintaining the CA and its operations.
- Request Certificates - Allows the Service Account to request new certificates, a fundamental function in certificate management.
Set AD CS Permissions
Following these steps will allow Next-Gen Trust Security to enroll certificates for any template that does not require a signature and to which its group has been given Enroll permissions.
- Create an Active Directory group.
- Create an Active Directory user account to use when enrolling with Microsoft AD CS.Info About the term user account: In this context, a user account is synonymous with service account. In Windows, a service account is just a user account that represents an application rather than a person.
- Add this user to the group you created.
- Using the Certification Authority MMC snap-in, right-click on the CA name and select Properties. On the Security tab, add the group and grant it Read, Log on as a service, Issue and Manage Certificates and Request Certificates permissions.Info: If you're not familiar with using MMC snap-ins, see Adding an MMC Snap-in below.
- Using the Certificate Templates MMC snap-in, right-click on a template that Next-Gen Trust Security will enroll and select Properties. On the Security tab, grant the group Read and Enroll permissions. Repeat this step for all templates that this group will enroll.
- Create a Microsoft AD CS Certificate Authority in Next-Gen Trust Security. Next-Gen Trust Security will automatically test that the used group can enroll certificates for the specified templates.
What's Next
You're now ready to set up an AD CS certificate authority in Next-Gen Trust Security. Have the following AD CS information ready before you begin:
- IP or hostname of your Microsoft AD CS server
- Username and password for the AD CS account you set up in these steps
- Microsoft AD CS Issuing Certificate Common Name
Where Can I Find the Common Name?
There are two ways to obtain the Common Name of the Issuing Certificate:
- Open the Issuing Certificate, go to the Details Tab and check the CN value for Issuer.
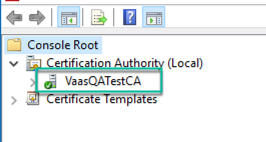
- From the Certification Authority MMC snap-in, expand the root node, and the name of the CA itself is the CN of the Issuing Certificate. In the example below, the CN is VaasQATestCA.
Adding an MMC Snap-In
If you're unfamiliar with how view the MMC snap-ins referenced in the steps above, follow these steps.
- On your Windows server, select Run from the Start menu, and then enter mmc. The MMC opens.
- From the File menu, select Add/Remove Snap-in. The Add or Remove Snap-ins window opens.
- From the Available snap-ins list on the left, select the snap-in that you want to add, and then click Add.
- For the Certificate Authority MMC snap-in, select the computer you want the snap-in to manage. If you're performing these steps from your AD CS server, click Local Computer. Otherwise, select Another Computer and specify your AD CS server.
- Click Finish, and then click OK.
