Working with the Built-in CA
Table of Contents
Expand all | Collapse all
-
- Activate Next-Generation Trust Security
-
-
- Configure Akamai Connection
- Configure AWS Connection
- Configure Azure Key Vault Connection
-
- Workload Identity Federation Authentication
- Workload Identity Federation - Azure Identity Provider Authentication
- Next-Gen Trust Security Generated Key Authentication
- User Permissions
- Workload Identity Federation Authentication
- Next-Gen Trust Security Generated Key Authentication
- User Permissions
- Supported OIDC Claims
-
-
-
- Working with the Built-in CA
- Add AWS Public CA
- Add AWS Private CA
- Add DigiCert One Certificate Authority
- Add Entrust
- Add GlobalSign Atlas
- Add GlobalSign MSSL
- Add GoDaddy
- Add Google Cloud Private CA
- Add a HID PKIaaS CA
- Add Certificate Manager - Self-Hosted
- Set Up an OpenSSL Certificate Authority Connector
- Create a Sectigo Certificate Manager Certificate Authority
- Add Zero Touch PKI
- Set Up Certificate Expiration Notifications
- Using a Custom DNS Provider
-
-
-
-
- Create an F5 BIG-IP LTM Machine
- Create a Microsoft Azure Private Key Vault Machine
- Create a Microsoft Azure Application Registration Machine
- Create a Microsoft IIS Machine
- Create a Microsoft Windows (PowerShell) Machine
- Create a Microsoft SQL Server Machine
- Create a Common KeyStore Machine
- Create a Citrix ADC Machine
- Create an Imperva WAF Machine
- Create a VMware NSX Advanced Load Balancer (AVI) Machine
- Create an A10 Thunder ADC Machine
- Create a Cloudflare Machine
- Create Kemp Virtual LoadMaster Machine
- Create a Palo Alto Panorama Machine
- Create a Radware Alteon Machine
-
- Provision to an F5 BIG-IP LTM
- Provision to a Microsoft Azure Private Key Vault
- Provision to Microsoft IIS
- Provision to Microsoft Windows (PowerShell)
- Provision to Microsoft SQL Server
- Provision to a Common KeyStore
- Provision to a Citrix ADC
- Provision to an Imperva WAF
- Provision to VMware NSX Advanced Load Balancer (AVI)
- Provision to an A10 Thunder ADC
- Provision to Cloudflare
- Provision to a Kemp Virtual LoadMaster
- Provision to Palo Alto Panorama
- Provision Certificates to Radware Alteon
-
-
- 47-Day Validity Readiness TLS Certificates dashboard
- About the Certificate Inventory
- Managing Certificate Lifecycle Settings
- Reissuing Certificates in Next-Gen Trust Security
- Downloading Certificates, Certificate Chains, and Keystores
- Retiring, Recovering, and Deleting Certificates
- Finding Certificates in the Certificate Inventory
- Importing Certificates from a CA Using EJBCA
- Domain-Based Validation for External Emails
-
- Create a Workload Identity Management or Discovery Agent Built-in Account
- Create an OCI Registry Built-in Account
- Create a Certificate Manager - Self-Hosted Built-in Account
- Create a Scanafi Built-in Account
- Toggling a Built-in Account on or Off
- Editing Built-in Accounts
- Deleting Existing Built-in Accounts
- Renew Existing Built-in Accounts
- Troubleshooting
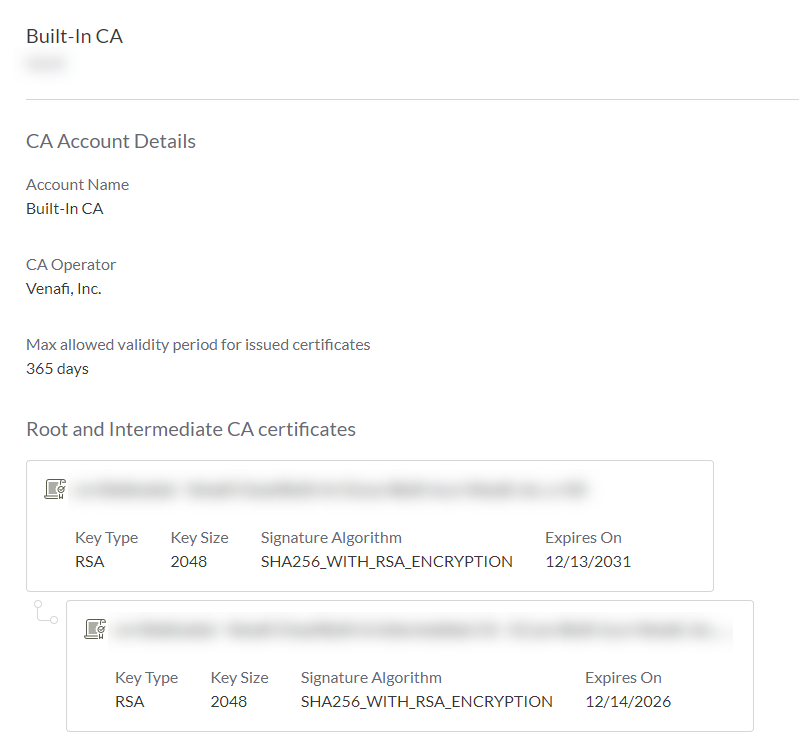
Working with the Built-in CA
In addition to integrations with various public certificate authorities (CA),
Next-Gen Trust Security provides a Built-In CA. The primary use case for the Built-in CA is to
rapidly issue certificates that are generally short-lived.
This is especially useful in development or DevOps environments where internal
machines, virtual machines, and applications need to trust each other, yet the
environment must remain flexible and responsive.
The Built-in CA certificate chain can be signed either by Next-Gen Trust Security or by a
public CA.
View Details about the Built-in CA Account
- Sign in to Next-Gen Trust Security.
- Click Configuration > Certificate Authorities.
- Click Built-In CA to see details.
Issue New Venafi Root and Intermediate Certificates
Performed by: Superuser
This option generates both a root and an intermediate certificate. The root
certificate is self-signed, and the intermediate certificate is then signed
by the root certificate.
- Click Configuration > Certificate Authorities.
- Click Built-in CA.
- In the Certificate Authorities local menu bar, click Change issuer > Venafi.
- Complete the fields for Root certificate based on your organization's requirements. Click Next.The values you entered for the Root certificate are copied to the Intermediate certificate form.
- Modify fields for Intermediate certificate as necessary.
- Click Done.
After a few moments, the new root and intermediate CA certificates appear on the Built-In CA page.
What's Next
Your Built-in CA is now ready to issue certificates. See What's Next below for next steps.
Issue a New CA-Signed Intermediate Certificate
Performed by: Superuser
This option creates a new Certificate Signing Request (CSR), which you'll then
submit to a CA. After the CA returns the certificate, you can upload the
certificate to Next-Gen Trust Security.
Generate CSR
- Click Configuration > Certificate Authorities.
- Click Built-in CA.
- In the Certificate Authorities local menu bar, click Change issuer > Custom.
- Complete the fields based on your organization's requirements. These values become part of the CSR. Click Next. The Sign & Upload section of the wizard opens.
Sign & Upload
The Sign & Upload screen contains a CSR. Copy this CSR, and submit it to
your CA. After your CA returns a certificate, you can upload it.
At this point, you have several certificate upload options:
| Upload Option | Description |
|---|---|
| Paste Base64 encoded text | If you have the base 64 encoded text certificate, click this option and then paste the certificate in the text box. |
| Upload file | If you have a file containing your certificate, click this option and then select the file. |
| Upload later | If you don't have either of the above available, select this option. Next-Gen Trust Security saves your state, and you can upload your certificate when you have it. See Uploading a certificate below. |
After you make your selection, click Done.
Uploading a Certificate
If you selected Upload later in the previous step and now have your
certificate, follow these steps:
- Click Configuration > Certificate Authorities.
- Click Built-in CA.
- Scroll to the bottom. Your previously-saved CSR shows, followed by the Paste Base64 encoded text and Upload file radio buttons. Select one, provide the necessary data, and then click Done.
Why do I see only one certificate in the Built-in CA summary?
The certificate that your CA provided is an intermediate certificate. It is
chained to the signing CA's own root certificate, even though the entire chain
isn't shown in Next-Gen Trust Security.
What's Next
Your built-in CA is now ready to issue certificates. See What's Next below for next steps.
Canceling a CSR
If you created a CSR and selected the Upload later option, that CSR is saved
in Next-Gen Trust Security. If you no longer need the CSR, and you don't plan to upload a
certificate based on the CSR, you can delete it.
- Click Configuration > Certificate Authorities.
- Click Built-in CA.
- In the local menu bar, click Discard changes. Confirm your selection by clicking Discard on the confirmation modal.
Download the Certificate Chain
After the certificate chain certificates have been issued, you can download them
from Next-Gen Trust Security. You can then install the chain in OS or application certificate
stores as necessary so that certificates issued by the Built-in CA are trusted.
- Click Configuration > Certificate Authorities.
- Click Built-in CA.
- In the local menu bar, click Download chain. Select whether you want the intermediate or the root listed first in the chain. The chain downloads in a .cer file.
What's Next
Issue new certificates
This CA is now ready to be added to one or more certificate issuing templates. To do this, select this CA when creating certificate issuing templates.
Download and install the certificate chain
The Built-in CA certificate chain will need to be installed on each machine or
application that must trust the certificates issued by the Built-in CA. You'll
first need to download the chain from Next-Gen Trust Security.
Installing the certificate chain varies by OS and application, so check your OS
or application vendor's documentation on how to install certificate chains.
