FedRAMP
Enable ADEM in Panorama Managed Prisma Access for Mobile Users
Table of Contents
Enable ADEM in Panorama Managed Prisma Access for Mobile Users
Learn how to enable Autonomous DEM for your Panorama
Managed Prisma Access users.
Autonomous
DEM is supported on GlobalProtect app version 5.2.11 with Content
Release version 8393-6628 or later running on Windows or macOS endpoints
only. Because you may not have licensed Autonomous DEM for all of
your mobile users, you might want to create a new app settings configuration
and restrict it to the supported operating systems and the specific
users for which you want to enable ADEM.
After the GlobalProtect
app receives the ADEM configuration, it uses the corresponding certificate
to authenticate to the ADEM service and register with the service.
After the agent registers, you will be able to assign app tests
to the user.
To enable Autonomous DEM for your GlobalProtect
users:
- Generate the certificate the agent will use to authenticate to the Autonomous DEM service.
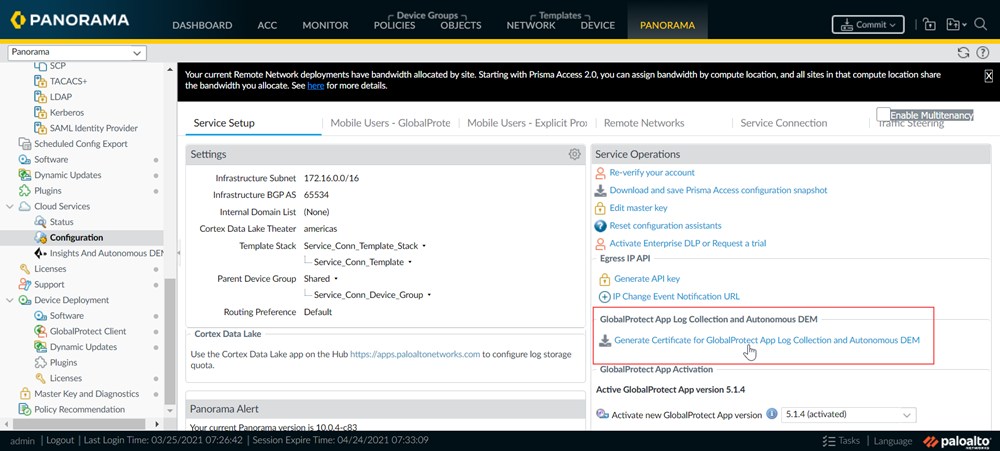
- From Panorama, select PanoramaCloud ServicesConfigurationService Setup.
- In the GlobalProtect App Log Collection section under Service Operators, click Generate Certificate for GlobalProtect App Collection and Autonomous DEM.
![]() A confirmation message indicates that the certificate was successfully generated in the Mobile_User_Template Shared location.
A confirmation message indicates that the certificate was successfully generated in the Mobile_User_Template Shared location.
Configure the portal to push the DEM settings to the GlobalProtect agent.- Select NetworkGlobalProtectPortalsGlobalProtect Portal.
- To create an agent configuration to push to your DEM users only, in the Mobile_User_Template, select the GlobalProtect Portal Configuration.
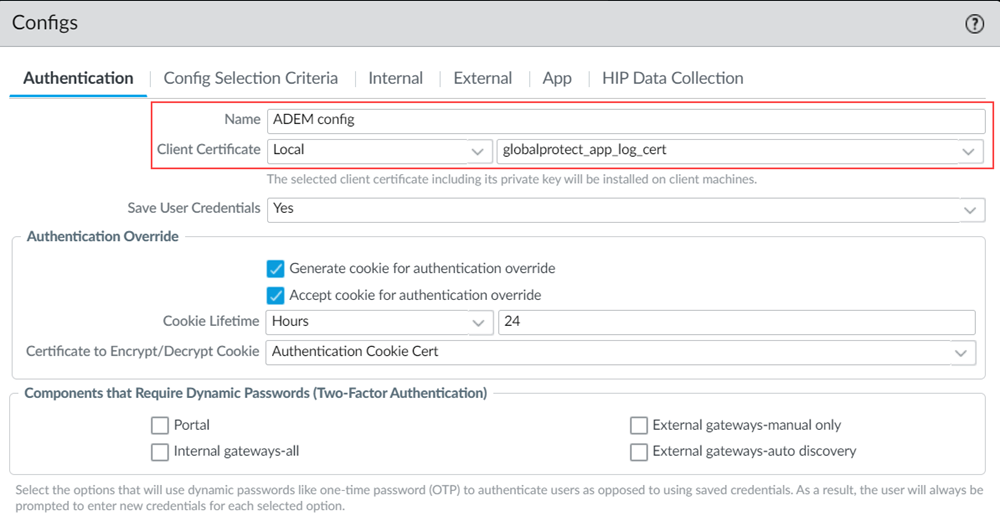
- On the Agent tab, select the DEFAULT agent configuration and Clone it and give it a new Name.
- To enable the portal to push the DEM authentication certificate you just generated to the end user systems, on the Authentication tab set Client Certificate to Local and then select the globalprotect_app_log_cert.
![]()
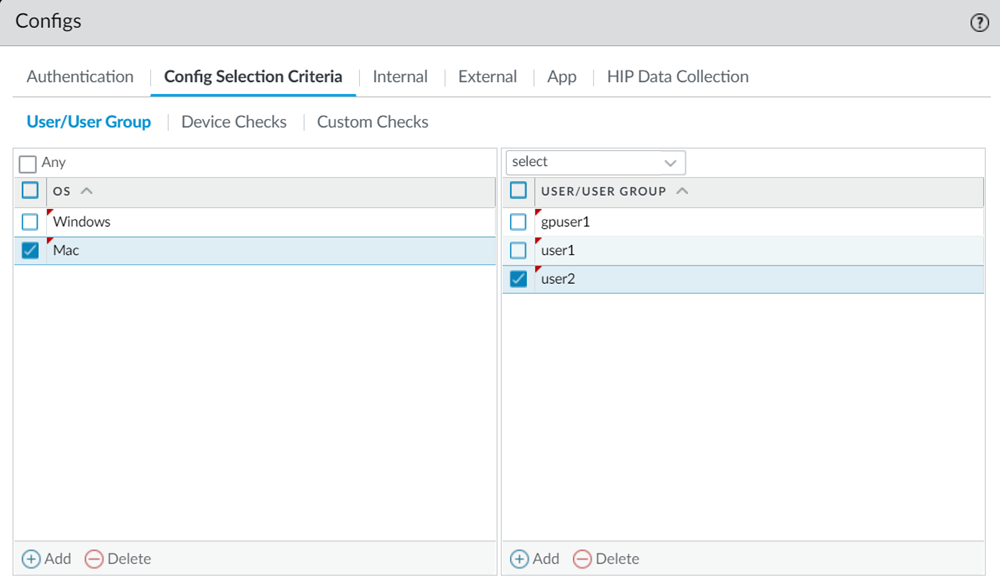
- To ensure that this agent configuration is only pushed to agents running on supported operating systems, on the Config Selection CriteriaUser/User Group tab, click Add in the OS column and select Mac and/or Windows only).
- If you only want to deploy the DEM configuration to a subset of your Mac and/or Windows users, in the User/User Group column Add the specific users or user groups to push this configuration to.
![]()
- To enable Autonomous DEM functionality for the selected users, on the App tab, enable Autonomous DEM endpoint agent for Prisma Access (Windows & Mac Only).Install and user can enable/disable agent from GlobalProtectADEM is enabled by default, however you can allow users to disable ADEM by selecting Install and user can enable/disable agent from GlobalProtect. End users can use this GlobalProtect configuration to pause/resume monitoring. If users disable the ADEM agent, they will continue to be online, but the agent will pause the monitoring and no synthetic tests will be conducted.Install and user cannot enable/disable agent from GlobalProtectADEM is enabled by default. Selecting Install and user cannot enable/disable agent from GlobalProtect will keep ADEM enabled. Users will not be able to disable ADEM.
- To enable Autonomous DEM functionality for the selected users, on the App tab, enable Autonomous DEM endpoint agent for Prisma Access (Windows & Mac Only). The available options depend on GlobalProtect release in your environment.
GlobalProtect Release Version Available Options Autonomous DEM endpoint agent for Prisma Access for GP version below 6.3 (Windows & MAC only) - Install and allow users to
enable/disableWith this option, ADEM is enabled by default and end users can enable or disable it. End users can use this GlobalProtect configuration to pause/resume monitoring. If users disable the ADEM agent, they will continue to be online, but the agent will pause the monitoring and no synthetic tests will be conducted.
- Install and do not allow users to
enable/disableWith this option, ADEM is enabled by default and end users will not be able to disable ADEM.
- Do not installEnd users will not be able to install ADEM. This is the default setting.
Autonomous DEM endpoint agent for Prisma Access for GP version 6.3 and above (Windows & MAC only) - Install
End users can install ADEM.
- UninstallEnd users can uninstall ADEM.
- No action
The previous ADEM state is retained. If ADEM was already installed, it will stay installed This is the default setting.
- Install and allow users to
enable/disable
- Also on the App tab, set Enable Autonomous DEM and GlobalProtect App Log Collection for Troubleshooting to Yes to enable the GlobalProtect app to use the certificate you just created to authenticate to the DEM service.
- Starting in GlobalProtect version 5.2.8, you have the option to suppress receiving all Autonomous DEM update notifications (pertaining to installing, uninstalling and upgrading an agent) on the endpoints. To suppress the notifications, set the Display Autonomous DEM Update Notifications to No. By default, the Display Autonomous DEM Update Notifications is set to Yes.
- Click OK to save the new app configuration settings and click OK again to save the portal configuration.
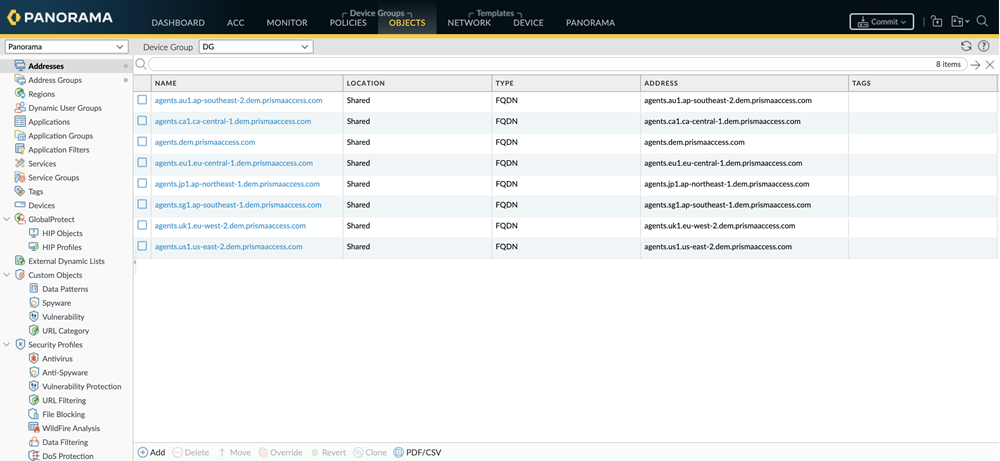
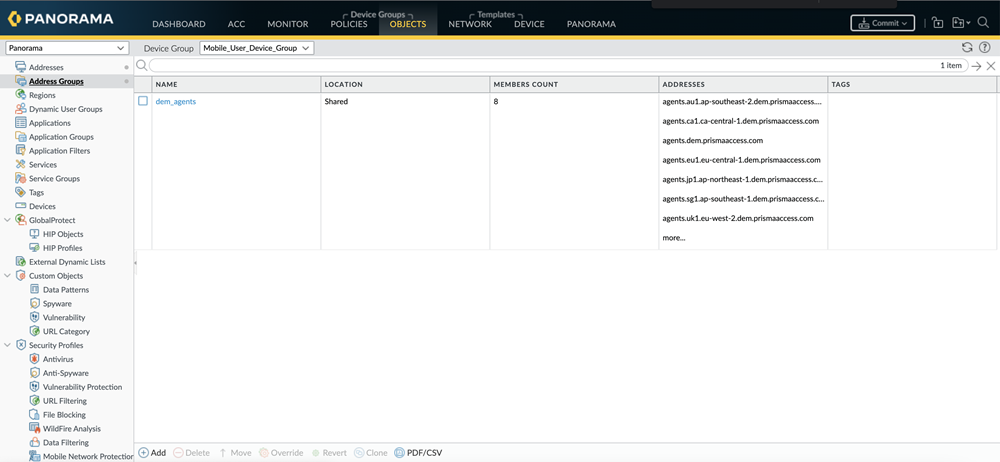
Make sure you have security policy rules required to allow the GlobalProtect app to connect to the ADEM service and run the synthetic tests.- In Panorama, go to Objectsaddresses. Click on Add and add the following ADEM Service Destination FQDNs.Do not decrypt the following servers. Also, make sure the profile allows untrusted issuers.
- FedRAMP High:
- updates.dem.prismasasegov.com
- agents.dem.prismasasegov.com
- features.dem.prismasasegov.com
- agents-il4-prod-us-central1.dem.prismasasegov.com
- FedRAMP Moderate:
- agents-fed-mod-prod-1-us-central1.dem.prismaaccess.com
- updates-fed-mod-prod-1-us-central1.dem.prismaaccess.com
- features-fed-mod-prod-1-us-central1.dem.prismaaccess.com
![]()
- Create an address group to contain the addresses above by going to ObjectsAddress Groups, clicking Add and providing a name for the address group.
![]()
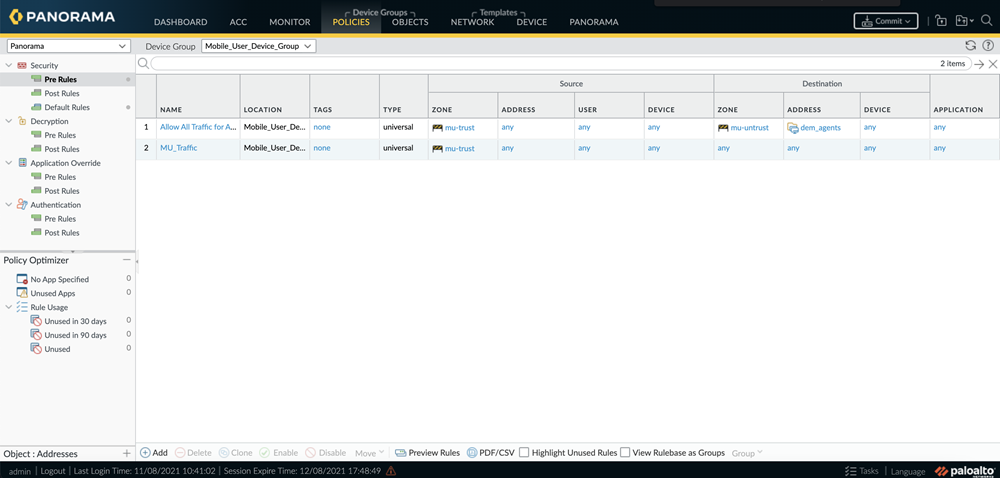
- Add the address group you just created into the security policy. Go to PoliciesSecurityPreRules. Click Add and add the address group to the policy.
![]()
- To enable the GlobalProtect users to connect to and register with the ADEM service and to run the synthetic application tests, make sure there is a security policy rule that allows traffic to HTTPS-based applications.
- To enable the app to run network monitoring tests, you must have a security policy rule to allow ICMP and TCP traffic.
- (Optional) If you plan to run synthetic tests that use HTTP, you must also have a security policy rule to allow the GlobalProtect users to access applications over HTTP.
Commit all your changes to Panorama and push the configuration changes to Prisma Access.- Click CommitCommit to Panorama.
- Click CommitPush to Devices and click Edit Selections.
- On the Prisma Access tab, make sure Prisma Access for users is selected and then click OK.
- Click Push.