Configure Explicit Proxy
Table of Contents
End-of-Life (EoL)
Configure Explicit Proxy
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
An explicit proxy is one of the types of web proxy that you can configure on your
firewalls. The web proxy enables you to leverage the same capabilities of a proxy
device while providing a simple, unified interface from which to manage the proxy.
The explicit proxy method in particular allows you to troubleshoot issues more
easily, since the client browser is aware of the existence of the proxy.
PAN-OS
- (VM Series only) If you have not already done so, activate the license for web proxy.You must activate the web proxy license for the PA-1400 Series, PA-3400 Series, and VM-Series. Learn how to activate your subscription licenses for the PA-1400 Series and PA-3400 Series or activate the web proxy license for the VM-Series in the following step.
- Log in to the Customer Service Portal (CSP).Edit the deployment profile.Select Web Proxy (Promotional Offer).
![]() Click Update Deployment Profile.On the firewall, retrieve the license keys from the server.If the license key retrieval is not successful, restart the firewall and repeat this step before proceeding.Set up the necessary interfaces and zones.As a best practice, use Layer 3 (L3) for the three interfaces the web proxy uses and configure a separate zone for each interface within the same virtual routers and the same virtual systems.
Click Update Deployment Profile.On the firewall, retrieve the license keys from the server.If the license key retrieval is not successful, restart the firewall and repeat this step before proceeding.Set up the necessary interfaces and zones.As a best practice, use Layer 3 (L3) for the three interfaces the web proxy uses and configure a separate zone for each interface within the same virtual routers and the same virtual systems.- Configure an interface for the client traffic.Be sure to carefully copy the IP address for this interface and save it in a secure location because you must enter it as the Proxy IP address when you configure the web proxy.Configure an interface for the outgoing traffic to the internet.Configure a loopback interface for the proxy.All incoming traffic is routed through this interface to the proxy.Set up the DNS proxy for Explicit Proxy.
- Configure a DNS proxy object for the proxy connection.Configure a DNS Server profile with both primary and secondary DNS servers.You must configure both a primary and a secondary DNS server for web proxy.Specify the interface for the proxy connection.Specify either the traffic ingress interface or a loopback interface.To enable decryption for MITM detection, create a self-signed root CA certificate or import a certificate signed by your enterprise certificate authority (CA). For more information, refer to the best practices for administrative access.Ensure you have completed the pre-deployment steps for the authentication method you want to configure.If you have a DNS security subscription, integrate the web proxy firewall with Explicit Proxy to sinkhole any requests that match the DNS security categories that you specify.
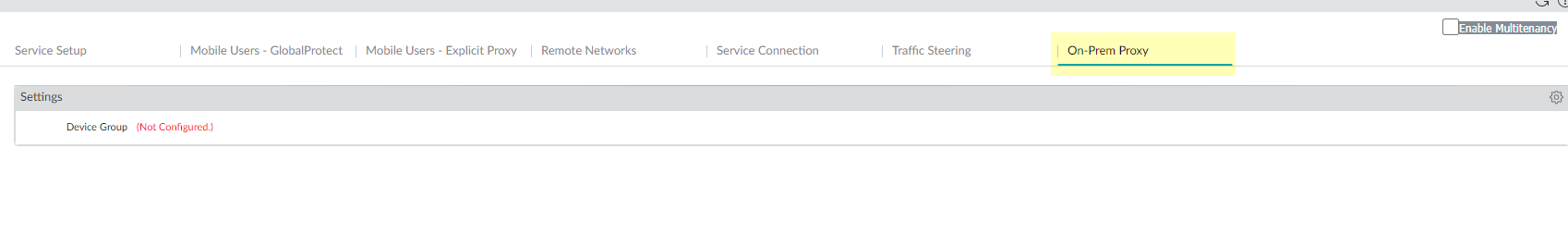
- Select PanoramaCloud ServicesConfigurationOn-Prem Proxy.Edit the settings then select the Device Group you want the web proxy firewall to use or Add a new device group.To integrate the web proxy firewall with Prisma Access, you must configure the web proxy firewall in a separate device group that contains no other firewalls or virtual systems. If the firewall is already a member of a device group, create a child device group as a sub-group and move the firewall to the child device group.
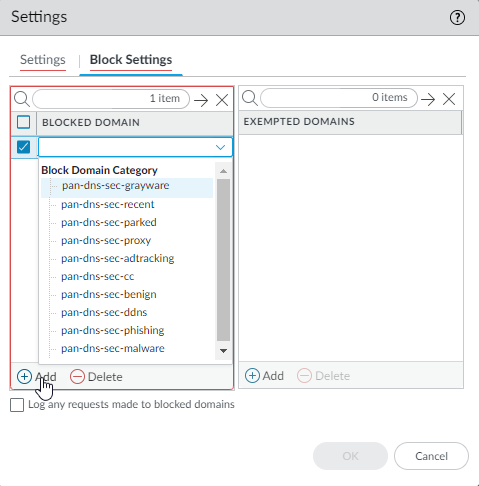
![]() (Optional) Select Block Settings to Add a Blocked Domain or any domains that are Exempted Domains because they are sinkholed due to matching one or more of the DNS Security categories.
(Optional) Select Block Settings to Add a Blocked Domain or any domains that are Exempted Domains because they are sinkholed due to matching one or more of the DNS Security categories.![]() (Optional) Select whether you want to Log any requests made to blocked domains.Click OK.Set up the Explicit Proxy.
(Optional) Select whether you want to Log any requests made to blocked domains.Click OK.Set up the Explicit Proxy.- On the firewall, select NetworkProxy then Edit the Proxy Enablement settings.Select Explicit Proxy as the Proxy Type then click OK to confirm the changes.If the only available option is None, verify that you have an active license for the web proxy feature.
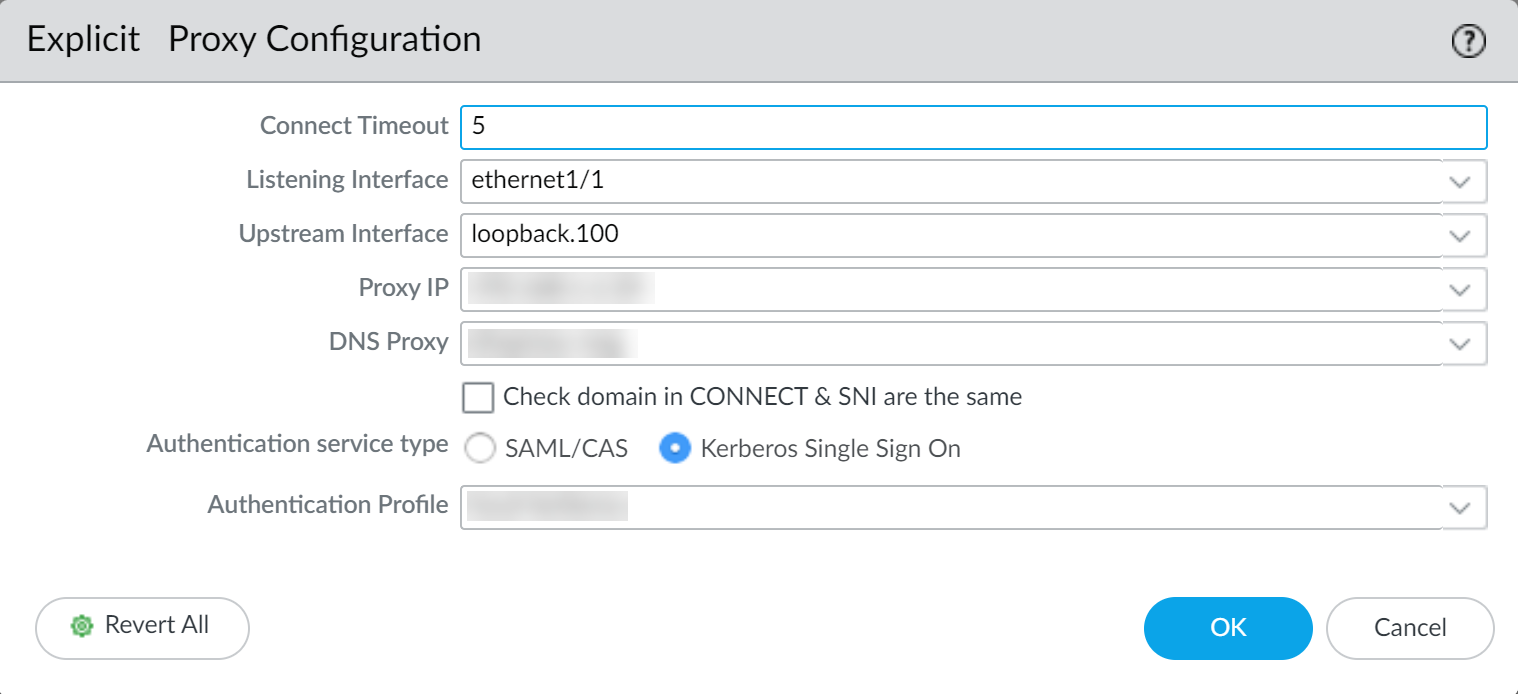
![]() Edit the Explicit Proxy Configuration.
Edit the Explicit Proxy Configuration.![]() Specify the Connect Timeout to define (in seconds) how long the proxy waits for a response from the web server. If there is no response after the specified amount of time has elapsed, the proxy closes the connection.Select the Listening Interface that contains the firewall where you want to enable the web proxy.Specify the ingress interface for the client traffic.Select the Upstream Interface that contains the interface with the web proxy that reroutes the traffic to the server.If you are using a loopback interface, specify that interface as the Upstream Interface.Specify the IP address of the listening interface as the Proxy IP.Enter the IP address of the interface you created in an earlier step.Specify the DNS Proxy object you created in an earlier step.Select Check domain in CONNECT & SNI are the same to prevent domain fronting attacks by specifying different domains between the CONNECT request and the Server Name Indication (SNI) field in the HTTP header.Select the Authentication service type you want to use (either SAML/CASor Kerberos Single Sign On).Be sure to complete all necessary pre-deployment and configuration steps for the authentication method you select. Select only one of the following authentication methods:Click OK to confirm the changes.Configure the necessary security policy rules to decrypt traffic and reroute applicable traffic to the proxy.You will need to create the following types of rules:
Specify the Connect Timeout to define (in seconds) how long the proxy waits for a response from the web server. If there is no response after the specified amount of time has elapsed, the proxy closes the connection.Select the Listening Interface that contains the firewall where you want to enable the web proxy.Specify the ingress interface for the client traffic.Select the Upstream Interface that contains the interface with the web proxy that reroutes the traffic to the server.If you are using a loopback interface, specify that interface as the Upstream Interface.Specify the IP address of the listening interface as the Proxy IP.Enter the IP address of the interface you created in an earlier step.Specify the DNS Proxy object you created in an earlier step.Select Check domain in CONNECT & SNI are the same to prevent domain fronting attacks by specifying different domains between the CONNECT request and the Server Name Indication (SNI) field in the HTTP header.Select the Authentication service type you want to use (either SAML/CASor Kerberos Single Sign On).Be sure to complete all necessary pre-deployment and configuration steps for the authentication method you select. Select only one of the following authentication methods:Click OK to confirm the changes.Configure the necessary security policy rules to decrypt traffic and reroute applicable traffic to the proxy.You will need to create the following types of rules:- Source NAT (if applicable)
- Decryption
- Security
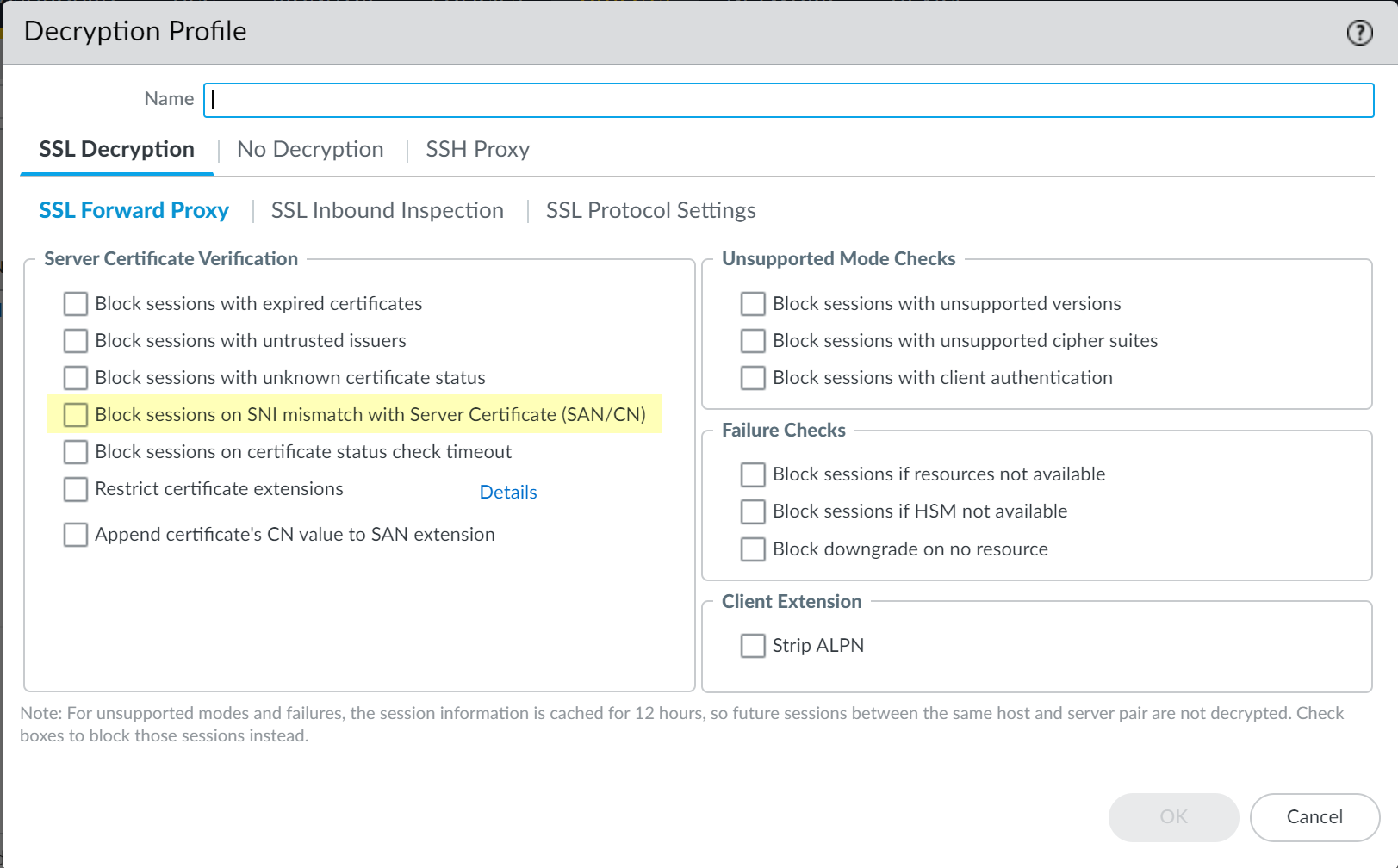
- Configure a decryption policy to decrypt the traffic so it can be rerouted if necessary.To avoid decrypting traffic twice, select the zone that contains the upstream interface as the source zone for the decryption policy.(Optional but recommended) Select ObjectsDecryption Profile and select Block sessions on SNI mismatch with Server Certificate (SAN/CN) to automatically deny any sessions where the Server Name Indication (SNI) does not match the server certificate.
![]() Configure the necessary security policy rules.
Configure the necessary security policy rules.- Create a security policy rule to allow traffic from the client to the interface you selected as the listening interface.
- Configure a security policy rule to allow traffic from the zone that contains the upstream interface to the internet.
- Configure a security policy rule to allow traffic from the DNS proxy zone to the internet.
Configure a security policy rule using the authentication profile you configured in an earlier step to route traffic to the proxy as appropriate.If this is your initial transparent web proxy configuration, make a change in your proxy configuration (Network DNS Proxy) and in your interface configuration (Network Interfaces), then Commit your changes to ensure the transparent web proxy configuration is correctly populated on the firewall.Strata Cloud Manager
Explicit Web Proxy for Strata Cloud Manager is supported only with the legacy router stack. If you'd like this enabled, please reach out to your account team.You can configure an explicit web proxy on cloud-managed firewalls using Strata Cloud Manager.- (VM Series only) If you have not already done so, activate the license for web proxy.You must activate the web proxy license for the PA-1400 Series, PA-3400 Series, and VM-Series. Learn how to activate your subscription licenses for the PA-1400 Series and PA-3400 Series or activate the web proxy license for the VM-Series in the following step.
- Log in to the Customer Service Portal (CSP).Edit the deployment profile.Select Web Proxy (Promotional Offer).
![]() Click Update Deployment Profile.On the firewall, retrieve the license keys from the server.If the license key retrieval is not successful, restart the firewall and repeat this step before proceeding.Set up the necessary interfaces and zones.As a best practice, use Layer 3 (L3) for the three interfaces the web proxy uses and configure a separate zone for each interface within the same virtual routers and the same virtual systems.
Click Update Deployment Profile.On the firewall, retrieve the license keys from the server.If the license key retrieval is not successful, restart the firewall and repeat this step before proceeding.Set up the necessary interfaces and zones.As a best practice, use Layer 3 (L3) for the three interfaces the web proxy uses and configure a separate zone for each interface within the same virtual routers and the same virtual systems.- Configure an interface for the client traffic.Be sure to carefully copy the IP address for this interface and save it in a secure location because you must enter it as the Proxy IP address when you configure the web proxy.Configure an interface for the outgoing traffic to the internet.(Optional) Configure a loopback interface for the proxy.Strata Cloud Manager automatically creates a loopback interface. Only configure one if you would like to use a different loopback interface.All incoming traffic is routed through this interface to the proxy.To enable decryption for MITM detection, create a self-signed root CA certificate or import a certificate signed by your enterprise certificate authority (CA). For more information, refer to the best practices for administrative access.Ensure you have completed the pre-deployment steps for the authentication method you want to configure.
- If you are using SAML, you must have configured Explicit Proxy for Mobile Users.
- If you are using Kerberos, you must have completed pre-deployment requirements for Kerberos.
If you have a DNS security subscription, integrate the web proxy firewall with Explicit Proxy to sinkhole any requests that match the DNS security categories that you specify.- In Strata Cloud Manager, select ManageConfigurationNGFW and Prisma AccessDevice SettingsProxyBlock DomainsCustomize.
![]() (Optional)Add Block Domain Categories, Block Domain Lists, or any domains that are Exception Domains because they are sinkholed due to matching one or more of the DNS Security categories.
(Optional)Add Block Domain Categories, Block Domain Lists, or any domains that are Exception Domains because they are sinkholed due to matching one or more of the DNS Security categories.![]() (Optional) Select whether you want to Log blocked domain requests.Save your selections.Set up the Explicit Proxy.
(Optional) Select whether you want to Log blocked domain requests.Save your selections.Set up the Explicit Proxy.- In Strata Cloud Manager, select ManageConfigurationNGFW and Prisma AccessDevice SettingsConfiguration Scope.Select the folder or snippet for which you want to configure Explicit Proxy.Select Device SettingsProxyProxy SettingsCustomize.
![]() Select Explicit Proxy as the Mode.
Select Explicit Proxy as the Mode.![]() Select the Authentication Method you want to use (either Kerberos Single Sign On or SAML/CAS).Be sure to complete all necessary pre-deployment and configuration steps for the authentication method you select.If you selected Kerberos Single Sign On, specify the Authentication Profile that you created when configuring Kerberos.
Select the Authentication Method you want to use (either Kerberos Single Sign On or SAML/CAS).Be sure to complete all necessary pre-deployment and configuration steps for the authentication method you select.If you selected Kerberos Single Sign On, specify the Authentication Profile that you created when configuring Kerberos.![]() Specify the Client Facing Interface.This is the interface for client traffic that you configured in an earlier step.Specify an Outbound Zone for outgoing traffic to the internet.You can Create New if you don't already have an outbound zone configured.Specify the IP addresses for the primary and secondary DNS servers that you want to connect to.Specify the interface for the DNS proxy connection.(Optional) Specify the Connect Timeout to define (in seconds) how long the proxy waits for a response from the web server. If there is no response after the specified amount of time has elapsed, the proxy closes the connection. The default is 5 seconds.(Optional) Specify the Web Traffic Service Port if you'd like web traffic to use special ports. The default ports are 80 and 443.(Optional) Specify the loopback interface for the proxy that you configured in an earlier step.(Optional) In case of legitimate business need, deselect Reset if SNI does not match HTTP CONNECT.It's recommended to leave this enabled to prevent domain fronting attacks by specifying different domains between the CONNECT request and the Server Name Indication (SNI) field in the HTTP header.Select Save to confirm the changes.If it applies to your deployment, create a Source NAT policy rule.Customize web access policies for any exceptions to the default policies you may need.If this is your initial explicit web proxy configuration, make a change to your proxy auto-configuration (PAC) file.
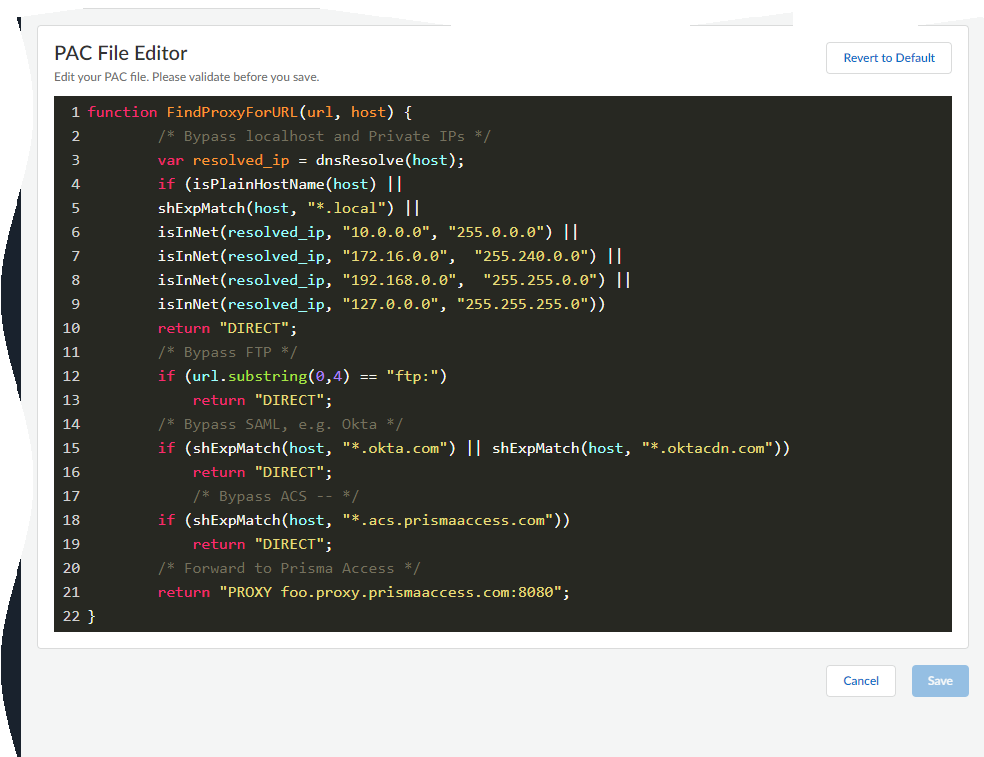
Specify the Client Facing Interface.This is the interface for client traffic that you configured in an earlier step.Specify an Outbound Zone for outgoing traffic to the internet.You can Create New if you don't already have an outbound zone configured.Specify the IP addresses for the primary and secondary DNS servers that you want to connect to.Specify the interface for the DNS proxy connection.(Optional) Specify the Connect Timeout to define (in seconds) how long the proxy waits for a response from the web server. If there is no response after the specified amount of time has elapsed, the proxy closes the connection. The default is 5 seconds.(Optional) Specify the Web Traffic Service Port if you'd like web traffic to use special ports. The default ports are 80 and 443.(Optional) Specify the loopback interface for the proxy that you configured in an earlier step.(Optional) In case of legitimate business need, deselect Reset if SNI does not match HTTP CONNECT.It's recommended to leave this enabled to prevent domain fronting attacks by specifying different domains between the CONNECT request and the Server Name Indication (SNI) field in the HTTP header.Select Save to confirm the changes.If it applies to your deployment, create a Source NAT policy rule.Customize web access policies for any exceptions to the default policies you may need.If this is your initial explicit web proxy configuration, make a change to your proxy auto-configuration (PAC) file.- Select ManageConfigurationNGFW and Prisma AccessDevice SettingsProxyProxy Auto Configuration
![]()
![]() Follow the PAC file guidelines to make the necessary changes to the PAC file.
Follow the PAC file guidelines to make the necessary changes to the PAC file.![]() When you're finished making changes, Save the file.The PAC file applies to all firewalls associated with your Strata Cloud Manager tenant. If you need different PAC files for different firewalls, you'll have to manually upload a different PAC file to those firewalls.
When you're finished making changes, Save the file.The PAC file applies to all firewalls associated with your Strata Cloud Manager tenant. If you need different PAC files for different firewalls, you'll have to manually upload a different PAC file to those firewalls.